Nikto is a web server assessment tool. It is designed to find various default and insecure files, configurations and programs on any type of web server. This tool is written in Perl language.
Open-source web server scanner that examines a website and reports back vulnerabilities. you can use with any web servers (Apache, Nginx, IHS, OHS, Litespeed, etc.)
https://github.com/sullo/nikto/tree/master/program
OSVDB prefix are vulnerabilities reported in the Open Source Vulnerability Database (a site that shut down in 2016). It’s similar to other vulnerability databases such as SecurityFocus, Microsoft’s Technet, and Common Vulnerabilities and Exposures, National Vulnerability Database.
You can recursively scan each page and virtual host as you discover them
How to use
1. Display basic menu
-H, -Help = help menu
- nikto -H

- nikto
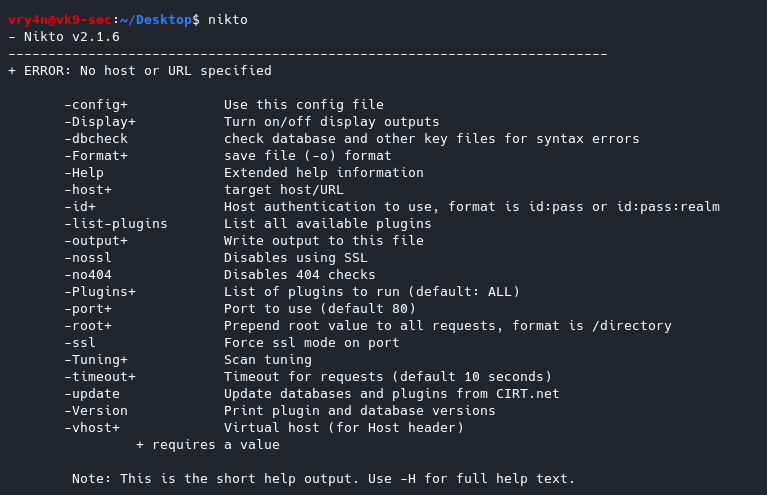
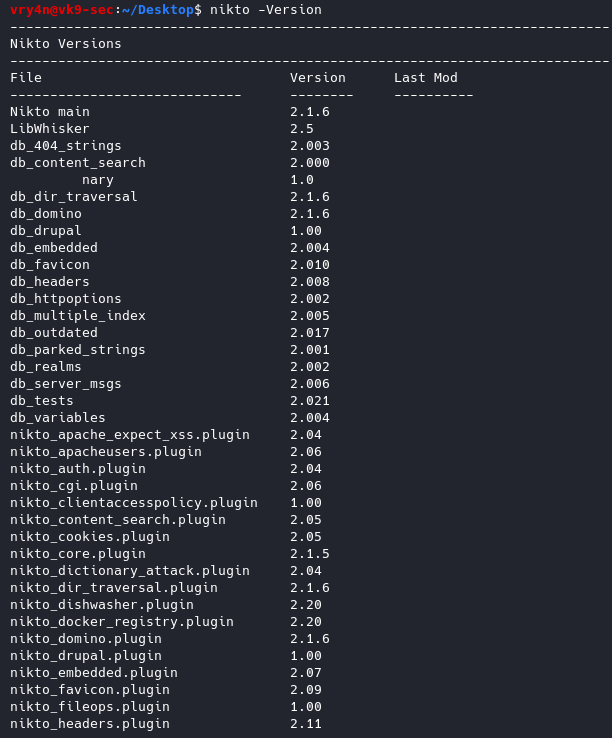
- nikto -Version
-Version Print plugin and database versions
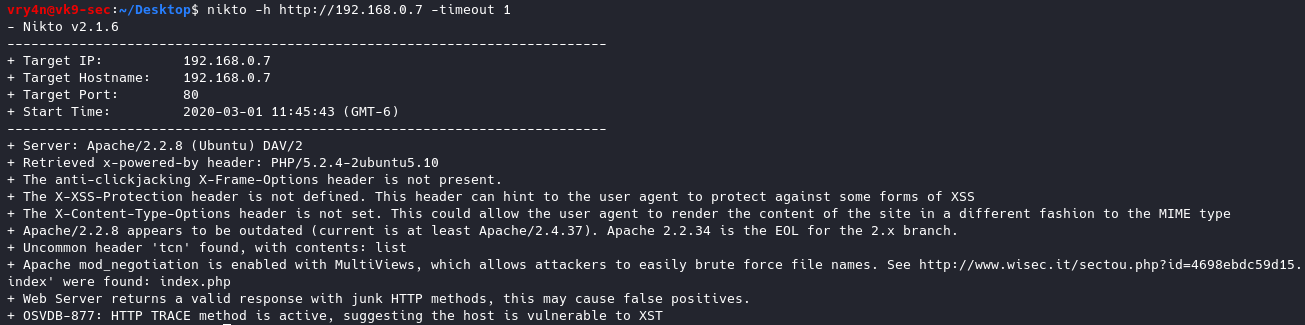
2. Basic Scan
-h = host
- nikto -h http://192.168.0.7

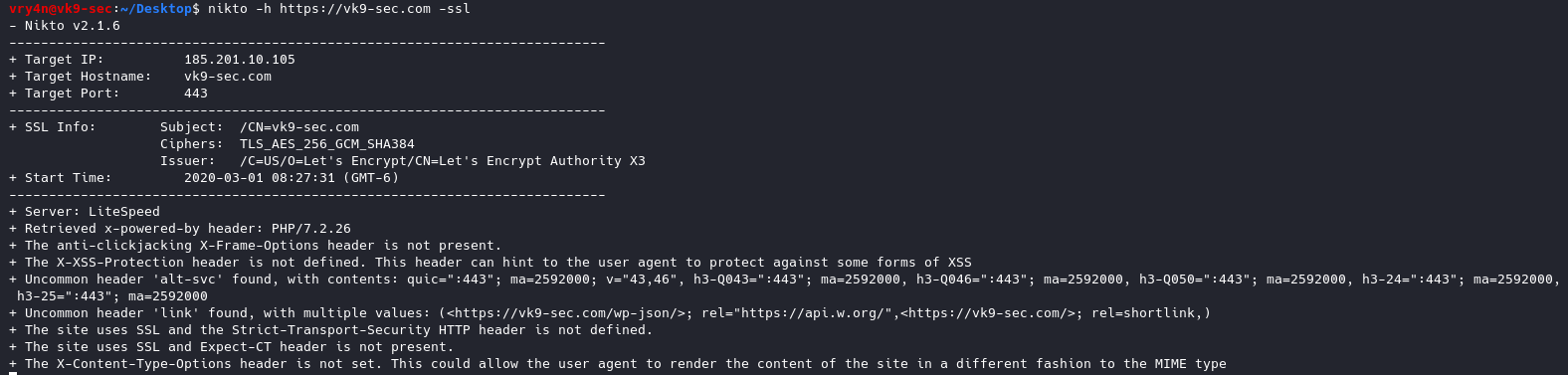
3. Scanning sites protected with SSL
-ssl
- nikto -h https://vk9-sec.com -ssl
4. Scan a list of IP addresses
- cat targets.txt
- nikto -h targets.txt

5. Output to integrate with Metasploit Framework.
-Format nbe = Format output for Nessus format
-o nessus.txt, – output = saves the output to a file named nessus.txt
csv Comma-separated-value
json JSON Format
htm HTML Format
nbe Nessus NBE format
sql Generic SQL (see docs for schema)
txt Plain text
xml XML Format
- nikto -h http://192.168.0.7 -Format nbe -o nessus.txt

- cat nessus.txt

6. Scan for any cgi directories
-Cgidirs all = Scan these CGI dirs: “none”, “all”, or values like “/cgi/ /cgi-a/”
- nikto -h http://192.168.0.7 -Cgidirs all
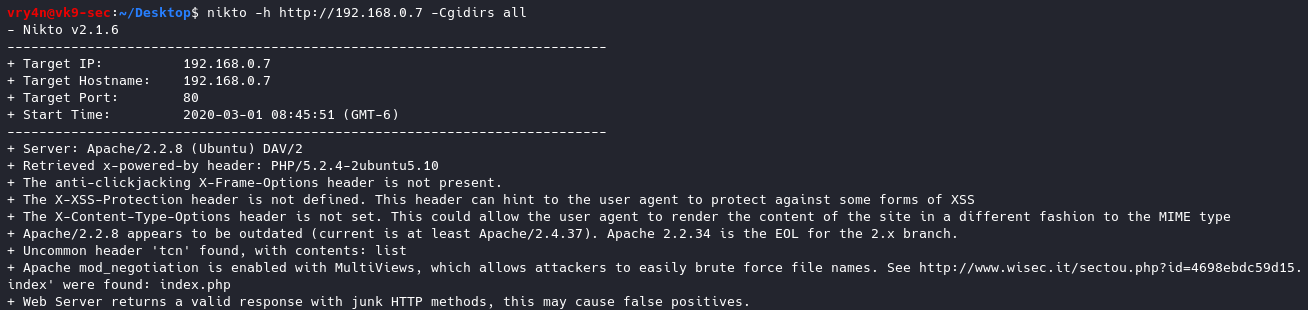
This time we got no results.
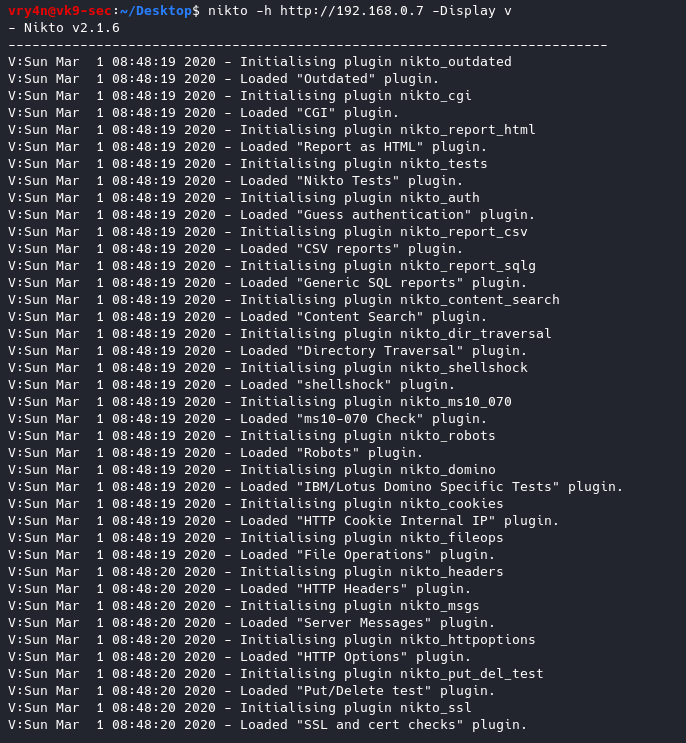
7. Display verbose, and, some results like 200 or 404 messages
-Display v = Turn on/off display outputs:
1 Show redirects
2 Show cookies received
3 Show all 200/OK responses
4 Show URLs which require authentication
D Debug output
E Display all HTTP errors
P Print progress to STDOUT
S Scrub output of IPs and hostnames
V Verbose output
- nikto -h http://192.168.0.7 -Display v
8. Check for database status and entries
-dbcheck = Check database and other key files for syntax errors
- nikto -dbcheck

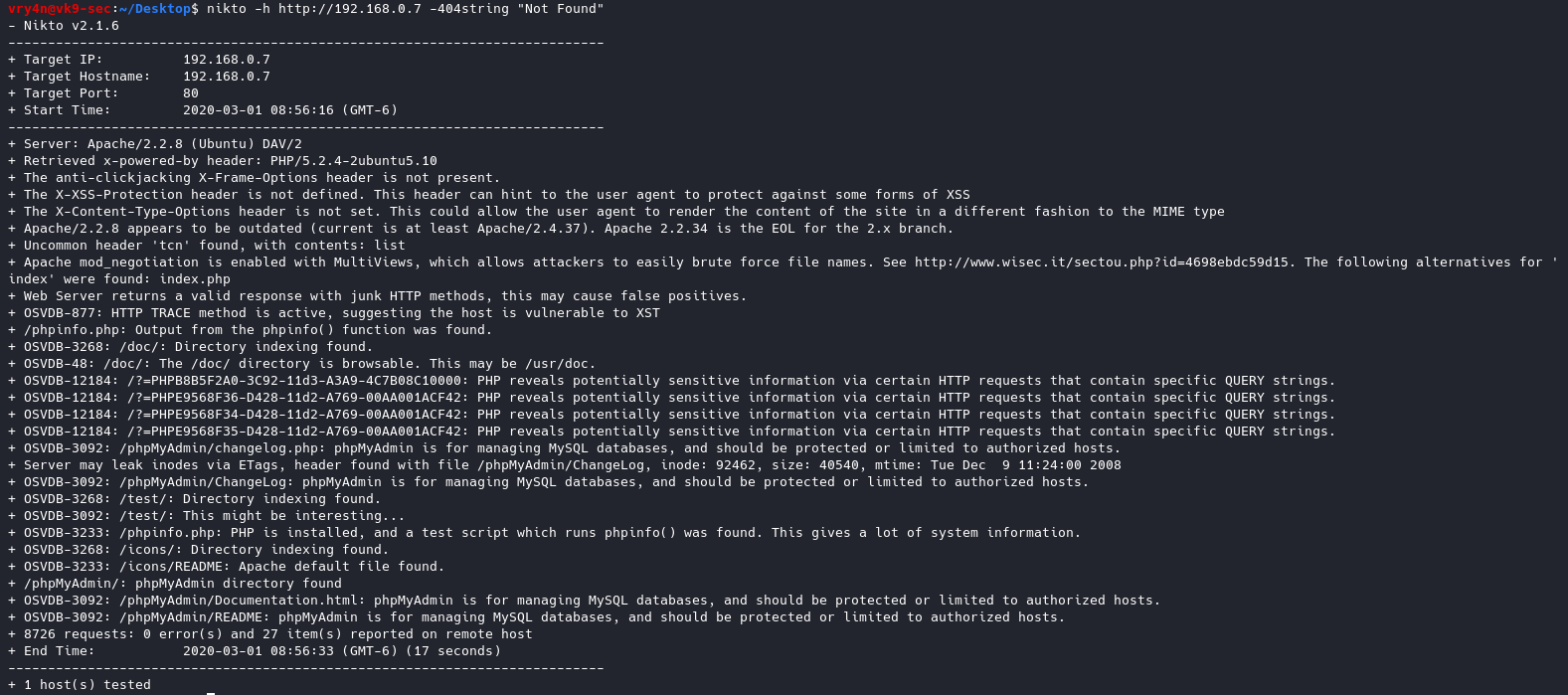
9. Ignore 404 code
-404code = Ignore these HTTP codes as negative responses (always). Format is “302,301”
- nikto -h http://192.168.0.7 -404code 404

10. Ignore string in the response body
-404string = Ignore this string in response body content as negative response (always). Can be a regular expression.
- nikto -h http://192.168.0.7 -404string “Not Found”
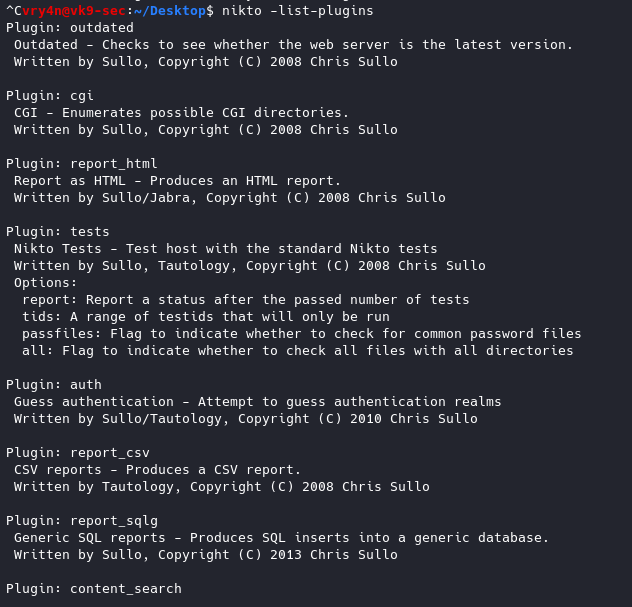
11. List of plug-ins and their status
-list-plugins = List all available plugins, perform no testing
- nikto -list-plugins
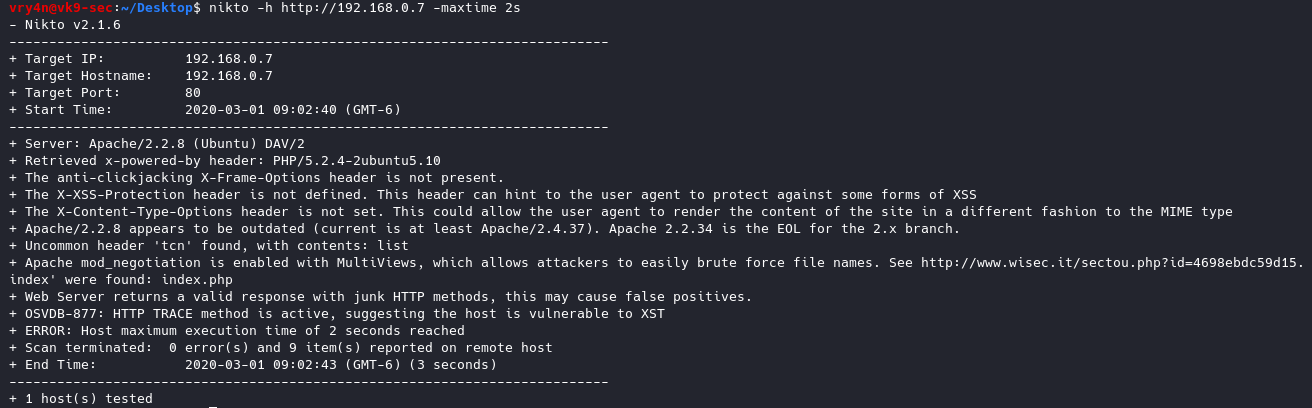
12. Specify how much time the scan should give per host
-maxtime+ = Maximum testing time per host (e.g., 1h, 60m, 3600s)
- nikto -h http://192.168.0.7 -maxtime 2s
13. Set a pause between tests
-Pause+ = Pause between tests (seconds, integer or float)
- nikto -h http://192.168.0.7 -Pause 2

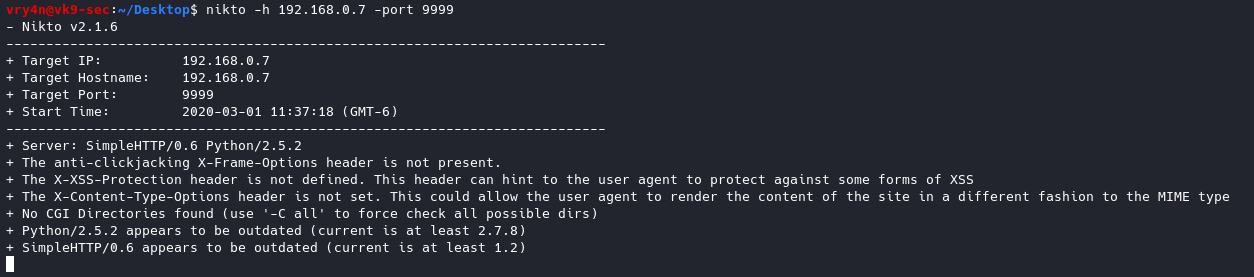
14. use a different port other than 80
-port+ = Port to use (default 80)
- nikto -h 192.168.0.7 -port 9999
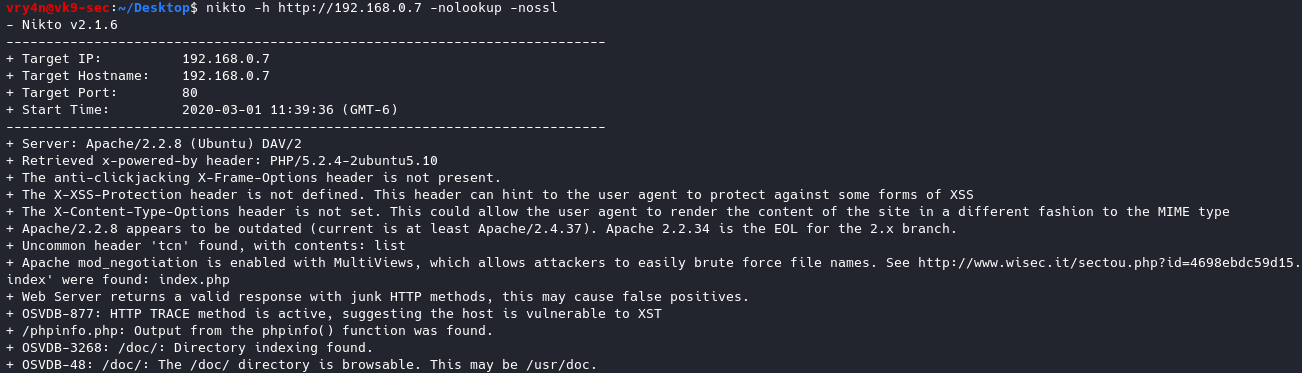
15. Disable SSL & DNS
-nolookup = Disables DNS lookups
-nossl = Disables the use of SSL
- nikto -h http://192.168.0.7 -nolookup -nossl
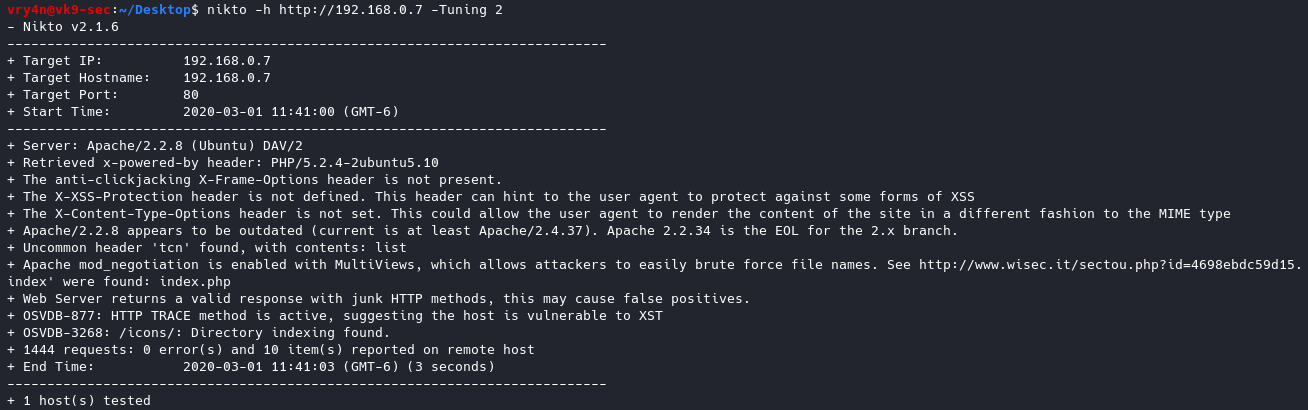
16. Test different types of attacks with Tuning option
-Tuning+
1 Interesting File / Seen in logs
2 Misconfiguration / Default File
3 Information Disclosure
4 Injection (XSS/Script/HTML)
5 Remote File Retrieval – Inside Web Root
6 Denial of Service
7 Remote File Retrieval – Server Wide
8 Command Execution / Remote Shell
9 SQL Injection
0 File Upload
a Authentication Bypass
b Software Identification
c Remote Source Inclusion
d WebService
e Administrative Console
x Reverse Tuning Options (i.e., include all except specified)
- nikto -h http://192.168.0.7 -Tuning 2
17. Set a timeout in case the request fails
-timeout+ Timeout for requests (default 10 seconds)
- nikto -h http://192.168.0.7 -timeout 1
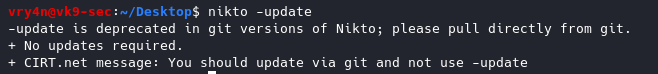
18.Update the databases and plugins. (out of date already)
-update = Update databases and plugins from CIRT.net
- nikto -update
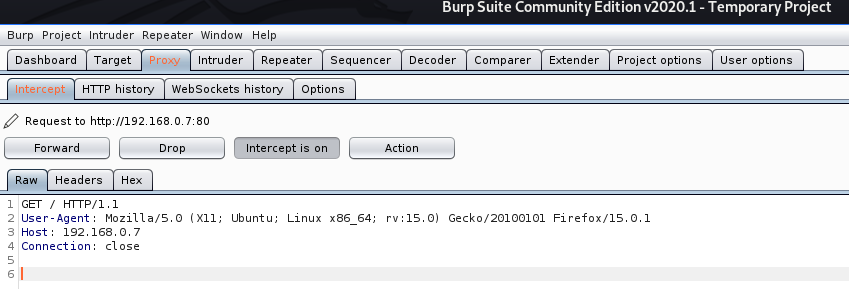
19. Send traffic through a Proxy
-useproxy = Use the proxy defined in nikto.conf, or argument http://server:port
- nikto -h http://192.168.0.7 -useproxy http://127.0.0.1:8080
In the proxy we can see
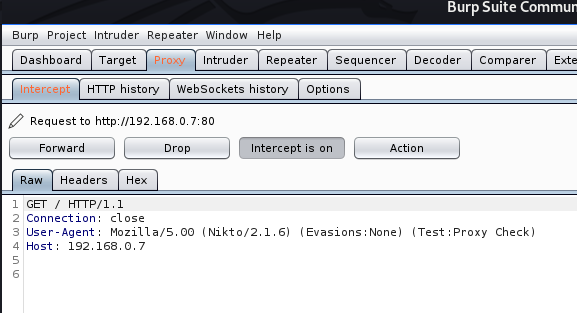
20. Spoof the User-Agent
-useragent = Over-rides the default useragent
- nikto -h http://192.168.0.7 -useragent “Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:15.0) Gecko/20100101 Firefox/15.0.1” -useproxy http://127.0.0.1:8080

In the proxy we see