Description
ROADtools (Rogue Office 365 and Azure (active) Directory tools)
ROADtools is a framework to interact with Azure AD. It consists of a library (roadlib) with common components, the ROADrecon Azure AD exploration tool and the ROADtools Token eXchange (roadtx) tool.
ROADlib
ROADlib is a library that can be used to authenticate with Azure AD or to build tools that integrate with a database containing ROADrecon data. The database model in ROADlib is automatically generated based on the metadata definition of the Azure AD internal API. ROADlib lives in the ROADtools namespace, so to import it in your scripts use
- from roadtools.roadlib import X
ROADrecon
ROADrecon is a tool for exploring information in Azure AD from both a Red Team and Blue Team perspective. In short, this is what it does:
- Uses an automatically generated metadata model to create an SQLAlchemy backed database on disk.
- Use asynchronous HTTP calls in Python to dump all available information in the Azure AD graph to this database.
- Provide plugins to query this database and output it to a useful format.
- Provide an extensive interface built in Angular that queries the offline database directly for its analysis.
- ROADrecon uses async Python features and is only compatible with Python 3.7 and newer (development is done with Python 3.8, tests are run with versions up to Python 3.11).
Requirements
Authenticated Account
Installation
There are multiple ways to install ROADrecon:
Using a published version on PyPi
Stable versions can be installed with pip install roadrecon. This will automatically add the roadrecon command to your PATH.
Using a version from GitHub
Every commit to master is automatically built into a release version with Azure Pipelines. This ensures that you can install the latest version of the GUI without having to install npm and all it’s dependencies. You can download the roadlib and roadrecon build files from the Azure Pipelines artifacts (click on the button “1 Published”. The build output files are stored in ROADtools.zip. You can either install the .whl or .tar.gz files directly using pip or unzip both and install the folders in the correct order (roadlib first):
- pip install roadlib/
- pip install roadrecon/
You can also install them in development mode with pip install -e roadlib/.
Developing the front-end
If you want to make changes to the Angular front-end, you will need to have node and npm installed. Then install the components from git:
- git clone https://github.com/dirkjanm/roadtools.git
- pip install -e roadlib/
- pip install -e roadrecon/
- cd roadrecon/frontend/
- npm install
You can run the Angular frontend with npm start or ng serve using the Angular CLI from the roadrecon/frontend/ directory. To build the JavaScript files into ROADrecon’s dist_gui directory, run npm build
How to use
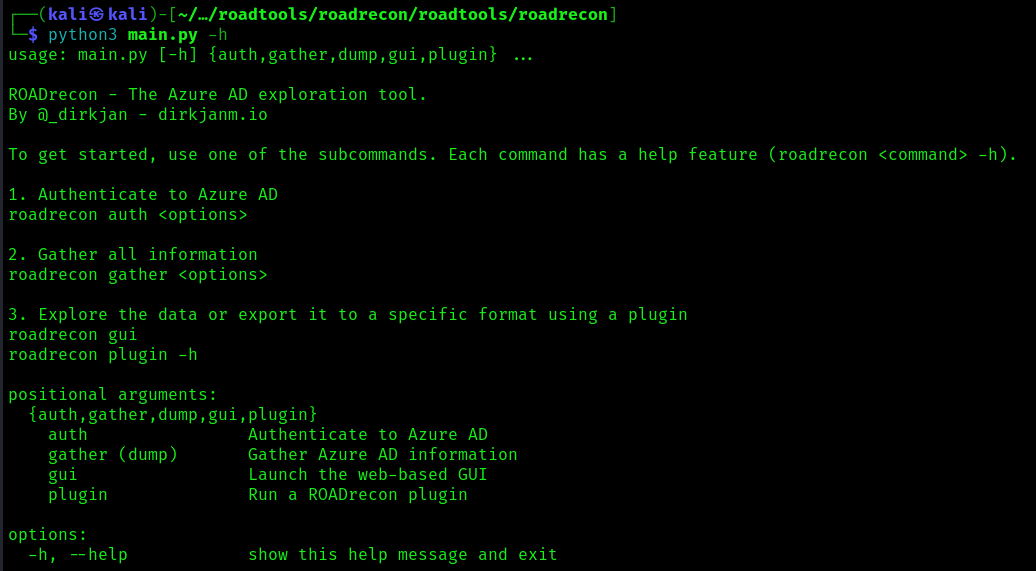
1. You can also run the main script to run reoad recon
- cd /roadtools/roadrecon/roadtools/roadrecon
- python3 main.py -h
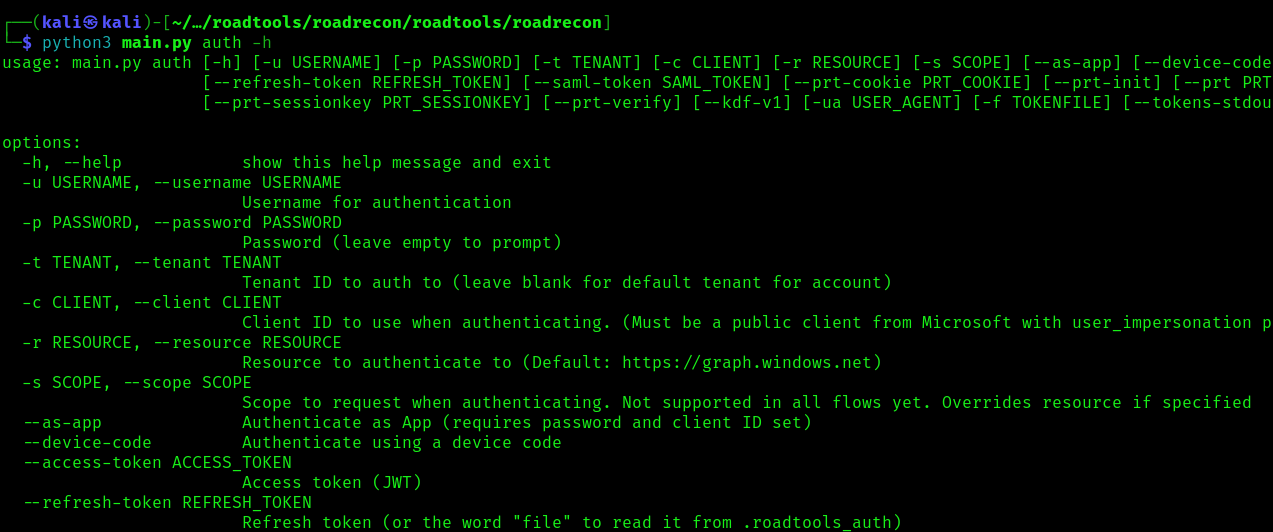
2. Display the argument options
- python3 main.py auth -h
Start enumeration
Authentication
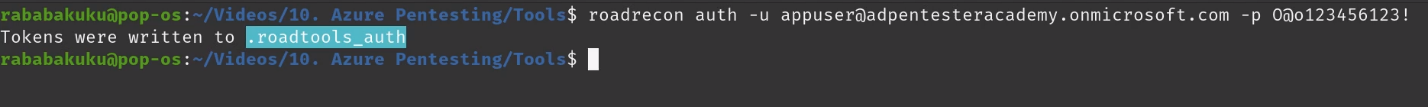
To authenticate use the auth module, this command will authenticate a create a token
- roadrecon auth -u <azure_username> -p <password>
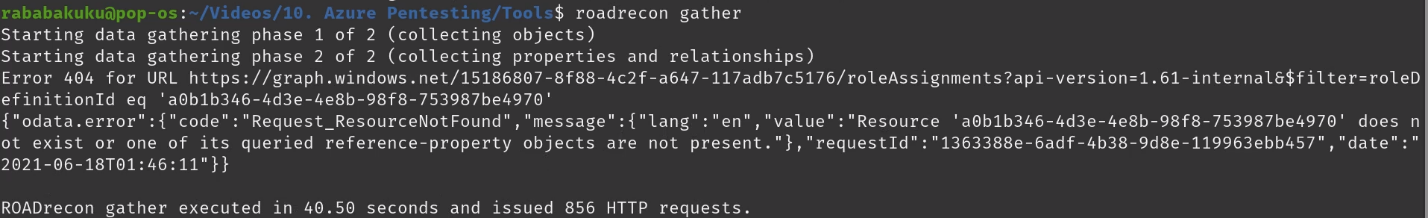
Gather information
Once authenticated we can proceed to gather information about Azure, it will save the results in a database
- roadrecon gather
Start GUI
1. After the information has been gather, we can start the GUI
- roadrecon gui
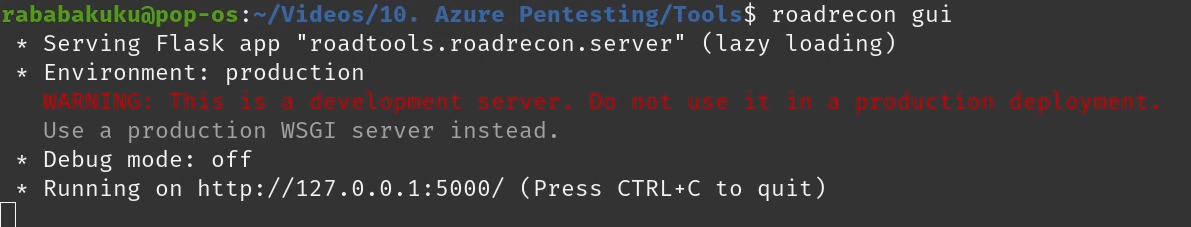
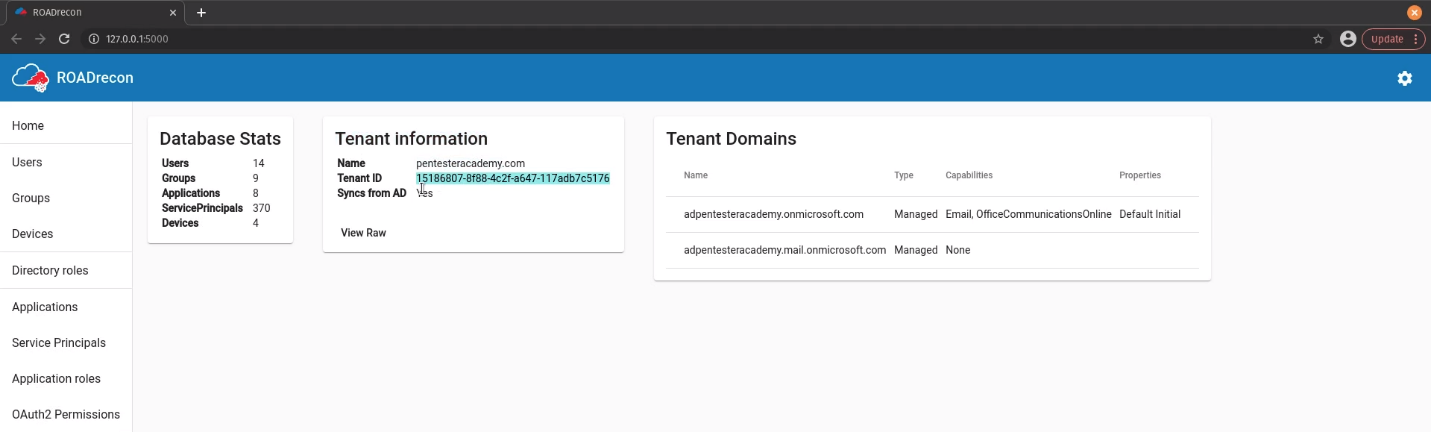
2. Connect to the GUI visiting http://127.0.0.1:5000/
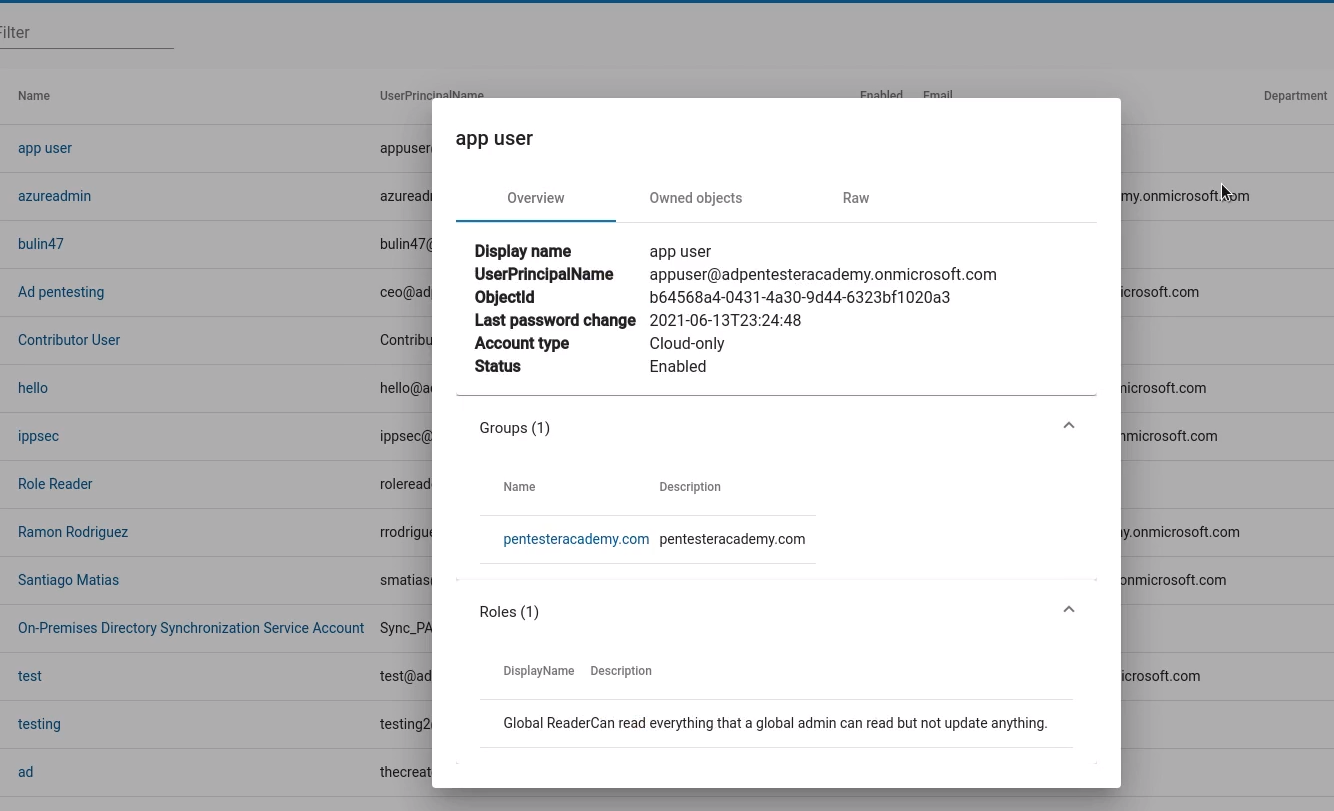
Users
1. Enumerate users’ information such as username, account type, email, last password change, etc
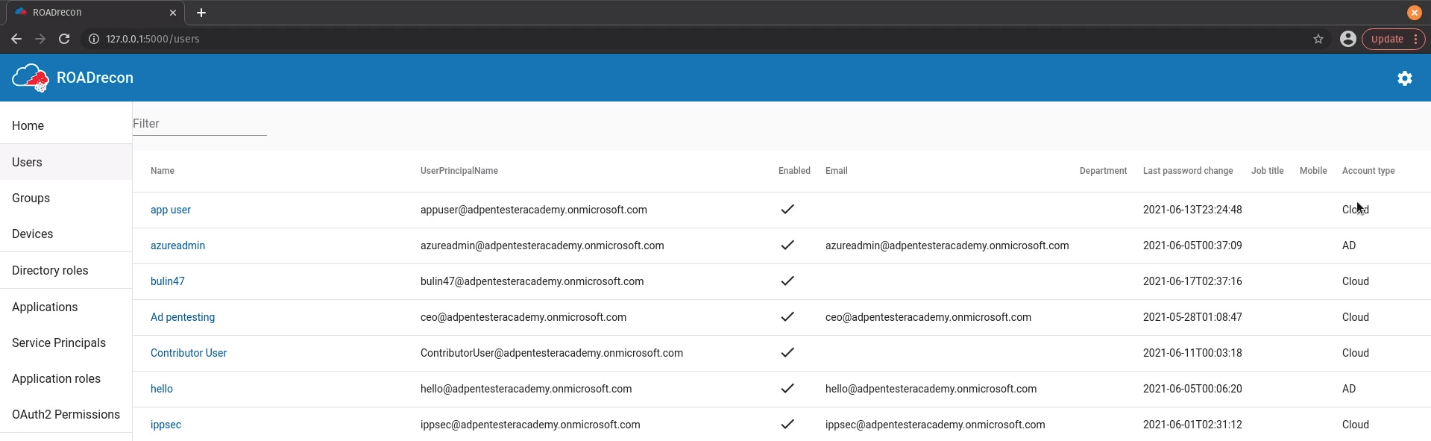
2. If you click on a user you can verify the Groups, Roles, Owned Objects, Raw data
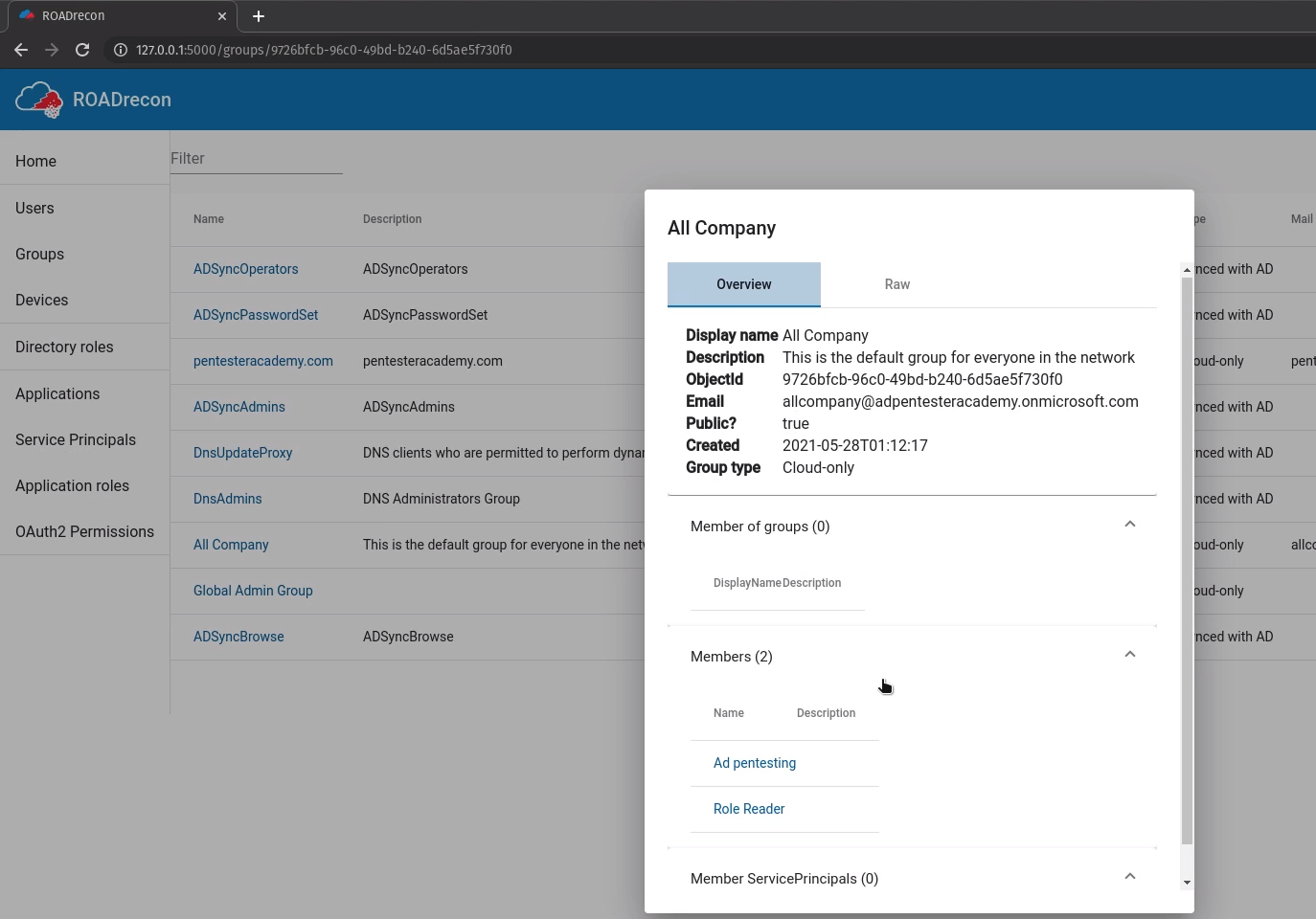
Groups
You can also enumerate groups and their details such as members and general information
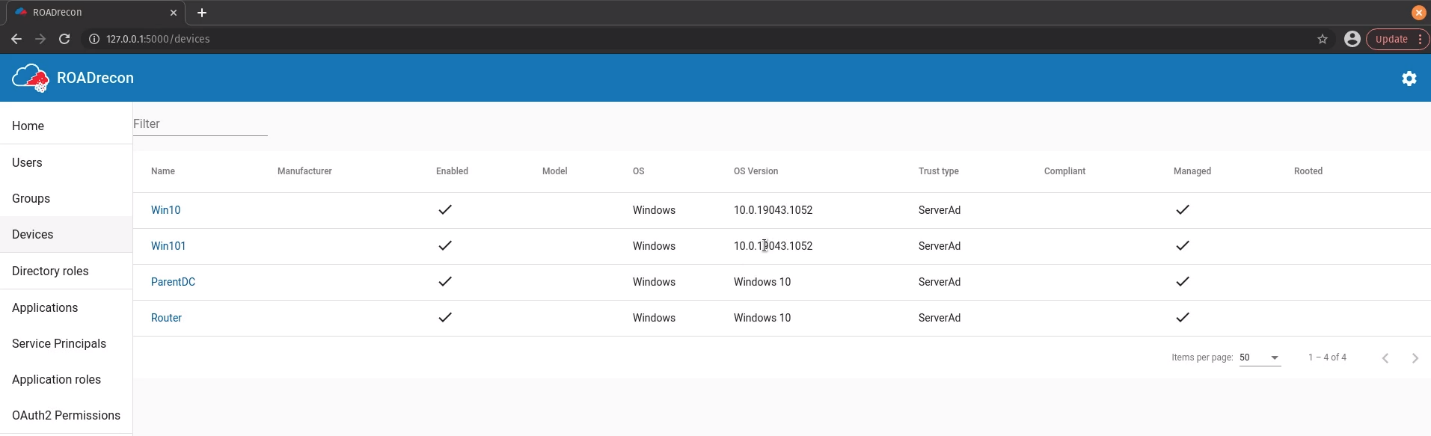
Devices
Enumerate the devices name, status, OS, trust type
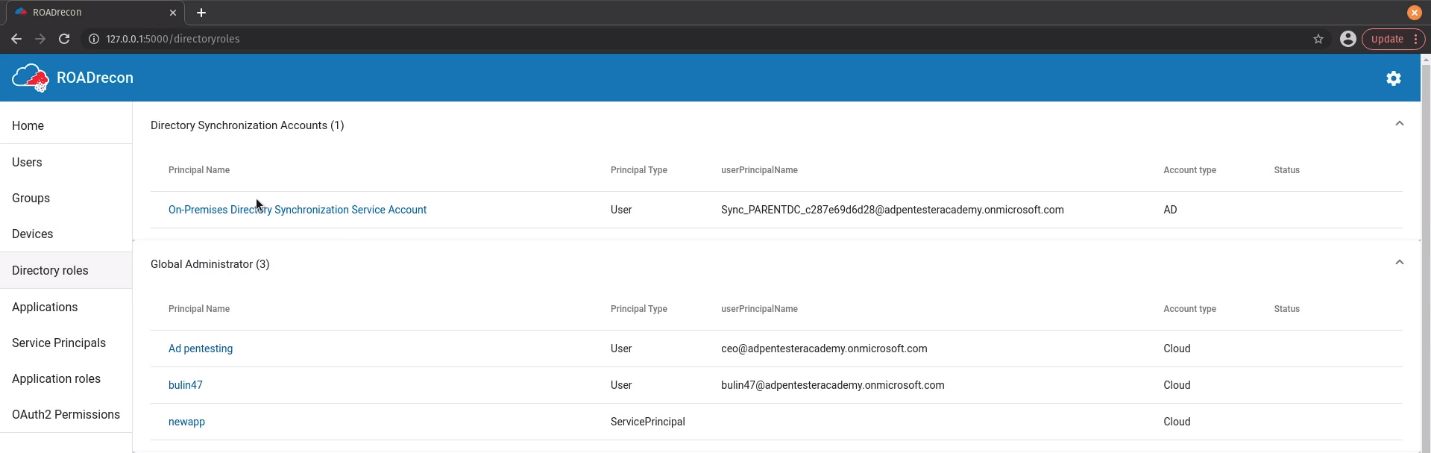
Roles
Enumerate rols Principal Name, type, userPrincipalName, status
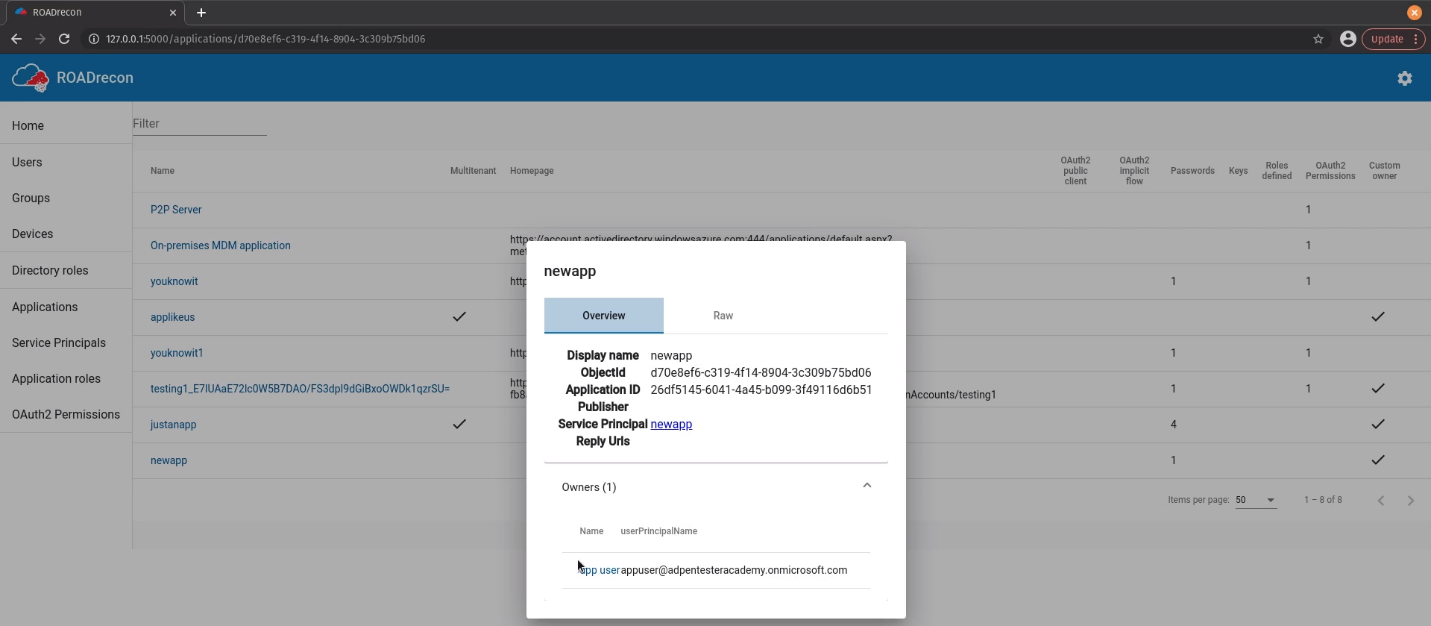
Applications
Enumerate applications name, multitenant status, home page, authentication, owners
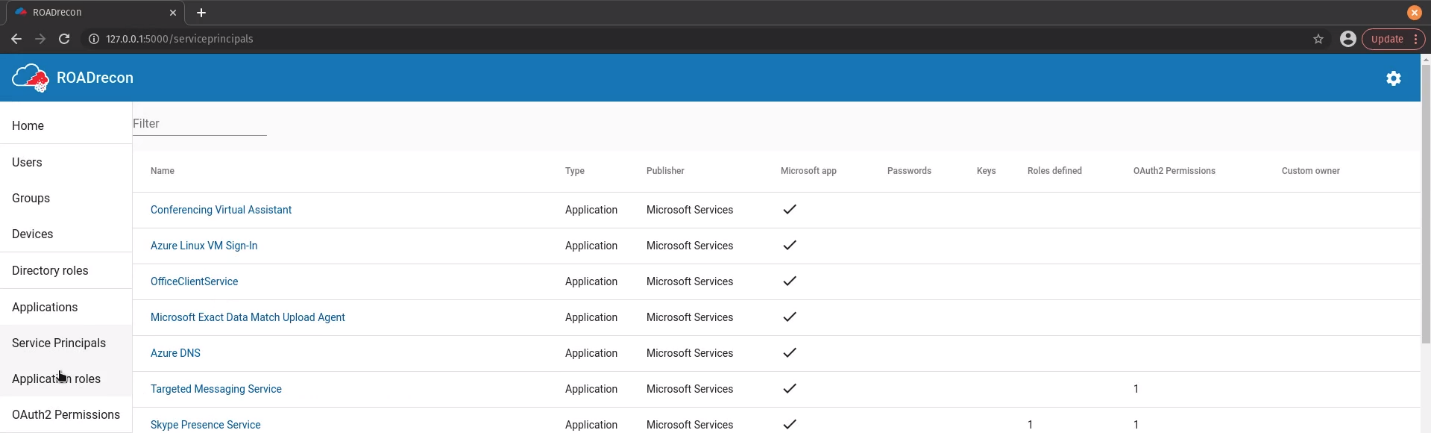
Service Principals
Enumerate Service principals name, type, publisher, status
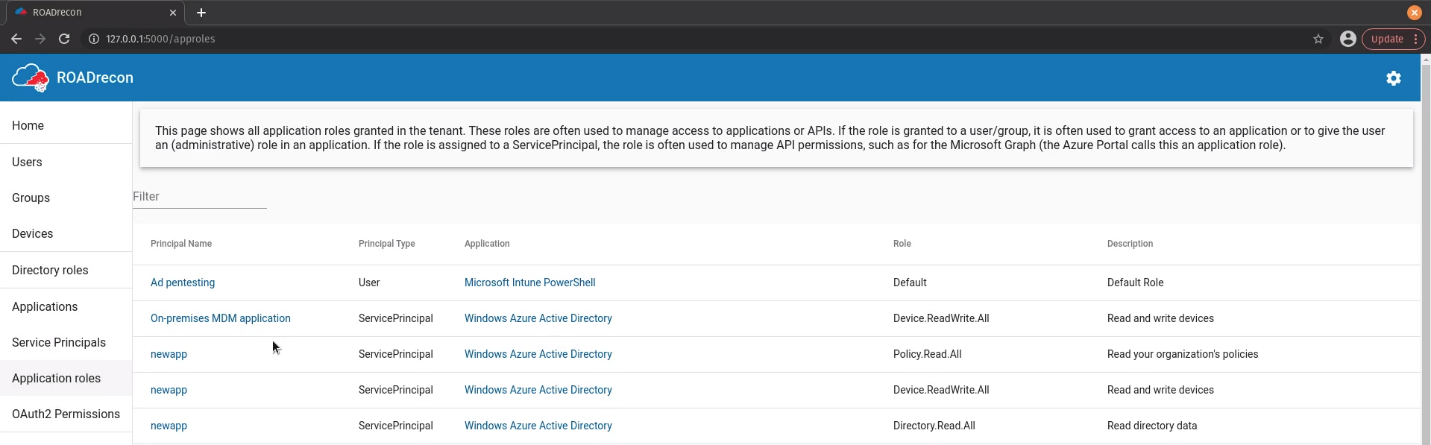
Applications Roles
Enumerate application roles name, type, application, role, description
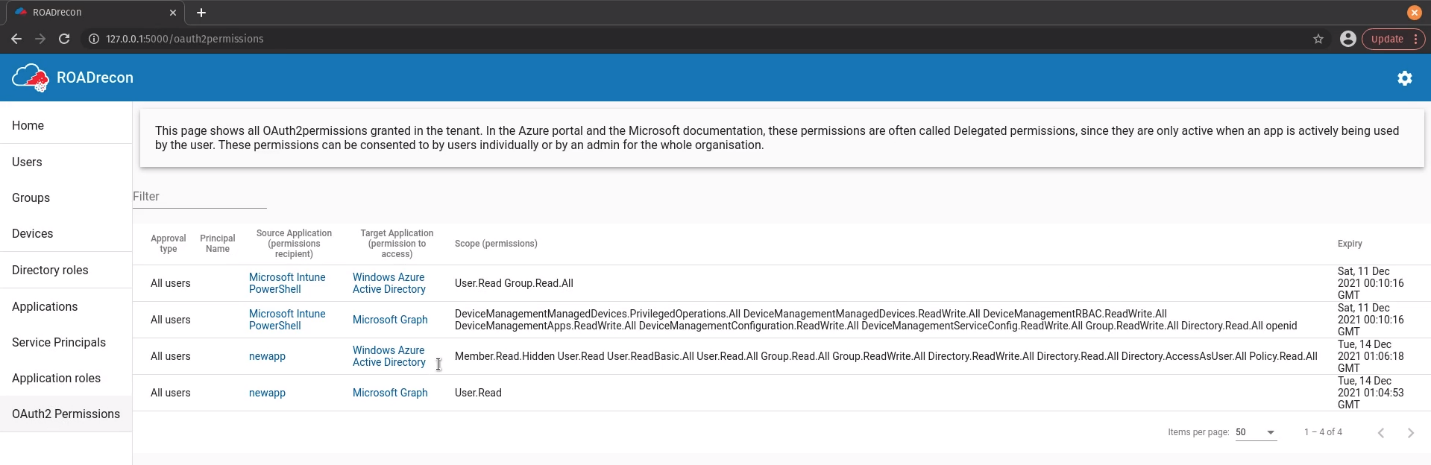
OAuth2
Enumerate OAuth2 Approval type, principal name, Source & target application, scope
References
https://github.com/dirkjanm/ROADtools
https://github.com/dirkjanm/ROADtools/wiki/Getting-started-with-ROADrecon