LDAP queries can be used to search for different objects (computers, users, groups) in the Active Directory LDAP database according to certain criteria.
This time, we will use LDAP to enumerate Active Directory users.
Search LDAP using ldapsearch
ldapsearch opens a connection to an LDAP server, binds, and performs a search using specified parameters. The filter should conform to the string representation for search filters as defined in RFC 4515. If not provided, the default filter, (objectClass=*), is used.
If ldapsearch finds one or more entries, the attributes specified by attrs are returned. If * is listed, all user attributes are returned. If + is listed, all operational attributes are returned. If no attrs are listed, all user attributes are returned. If only 1.1 is listed, no attributes will be returned.
By default, anonymous Lightweight Directory Access Protocol (LDAP) operations to Active Directory, other than rootDSE searches and binds, are not permitted.
This will only work if binding from the server is enabled.
ldapsearch how to (anonymous)
1. If your server is accepting anonymous authentication, you will be able to perform a LDAP search query without binding to the admin account. (the domain in this case is htb.local
- ldapsearch -x -h 10.10.10.161 -b “dc=htb,dc=local”

Note: This is the simplest form of output, so this will contain a whole to of information.
2. Finding all objects in the directory tree
- ldapsearch -x -b <search_base> -H <ldap_host> -D <bind_dn> -W “objectclass=*”
- ldapsearch -x -h 10.10.10.161 -b “dc=htb,dc=local” “objectclass=*”
3. Finding user accounts using ldapsearch
- ldapsearch -x -b <search_base> -H <ldap_host> -D <bind_dn> -W “objectclass=user”
- ldapsearch -x -h 10.10.10.161 -b “dc=htb,dc=local” “objectclass=user”
4. If you are only interested in some lines you can filter
- ldapsearch -x -b <search_base> -H <ldap_host> -D <bind_dn> -W “objectclass=account” cn uid homeDirectory
- ldapsearch -x -h 10.10.10.161 -b “dc=htb,dc=local” “objectclass=user” cn distinguishedName
5. Get possible usernames
- ldapsearch -x -h 10.10.10.161 -b “dc=htb,dc=local” “objectclass=user” sAMAccountName | grep sAMAccountName | awk -F “: ” ‘{print $2}’

ldapsearch how to (authenticated)
1. The easiest way to search LDAP is to use ldapsearch with the “-x” option for simple authentication and specify the search base with “-b”.
- ldapsearch -x -h 10.10.10.100 -p 389 -b “dc=active,dc=htb”

NOTE: If your server is accepting anonymous authentication, you will be able to perform a LDAP search query without binding to the admin account. In our case it needs authentication
2. Search LDAP with admin account (authenticated)
- ldapsearch -x -h 10.10.10.100 -p 389 -D SVC_TGS -w GPPstillStandingStrong2k18 -b “dc=active,dc=htb”

3. A number of UserAccountControl attributes have security relevance. The value of “2” corresponds to a disabled account status, and so the query below will return active users (by sAMAccountName / username) in the active.htb domain
- ldapsearch -x -h 10.10.10.100 -p 389 -D ‘SVC_TGS’ -w ‘GPPstillStandingStrong2k18’ -b “dc=active,dc=htb” -s sub “(&(objectCategory=person)(objectClass=user)(!(useraccountcontrol:1.2.840.113556.1.4.803:=2)))” samaccountname | grep sAMAccountName
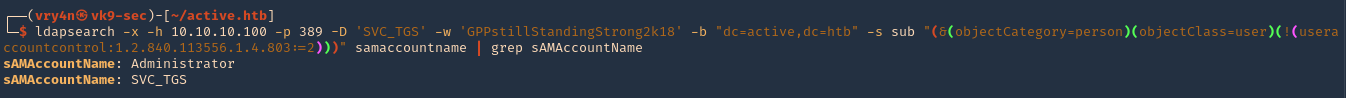
We got 2 users
- sAMAccountName: Administrator
- sAMAccountName: SVC_TGS
Enumerate Users Impacket
1. Locate the script within your machine
- find / -iname GetADUsers.py 2> /dev/null

2. (Optional) If you don’t have it installed run
- sudo git clone https://github.com/SecureAuthCorp/impacket.git
- cd impacket/
- sudo pip3 install .
- sudo python3 setup.py install
3. Application help
- python3 /usr/share/doc/python3-impacket/examples/GetADUsers.py

4. Knowing a username and a password you can run consults to enumerate
- python3 /usr/share/doc/python3-impacket/examples/GetADUsers.py -all active.htb/svc_tgs -dc-ip 10.10.10.100

We got 2 interesting users Administrator & SVC_TGS
Resources
https://devconnected.com/how-to-search-ldap-using-ldapsearch-examples/