It allows you to analyze the SSL/TLS configuration of a server by connecting to it, in order to detect various issues (bad certificate, weak cipher suites, Heartbleed, ROBOT, TLS 1.3 support, etc.).
It is a Python tool that can analyze the SSL configuration of a server by connecting to it. It is designed to be fast and comprehensive, and should help organizations and testers identify misconfigurations affecting their SSL servers.
Key features include:
- Multi-processed and multi-threaded scanning (it’s fast)
- SSL 2.0/3.0 and TLS 1.0/1.1/1.2 compatibility
- Performance testing: session resumption and TLS tickets support
- Security testing: weak cipher suites, insecure renegotiation, CRIME, Heartbleed and more
- Server certificate validation and revocation checking through OCSP stapling
- Support for StartTLS handshakes on SMTP, XMPP, LDAP, POP, IMAP, RDP and FTP
- Support for client certificates when scanning servers that perform mutual authentication
- XML output to further process the scan results
https://github.com/iSECPartners/sslyze
For this example, we will analyze a website certificate as well as a self-signed certificate. To create a certificate visit. https://vk9-sec.com/how-to-create-a-self-signed-certificate-openssl/
Basics
1. To download the tool (it already comes installed in most security distros)
- git clone https://github.com/iSECPartners/sslyze.git
- ls -ld sslyze

You could also run these commands if you face any issues running the script
- pip install –upgrade setuptools
- php install –upgrade sslyze
2. Run basic help
-h, –help = show this help message and exit
- sslyze -h

3. Check for the tool version
–version = show program’s version number and exit
- sslyze –version

4. Updade the trust stores
–update_trust_stores = Update the default trust stores used by SSLyze. The latest stores will be downloaded from https://github.com/nabla-c0d3/trust_stores_observatory.
- sudo sslyze –update_trust_stores

How run the application
1. Perform a basic scan on a website
–regular = Regular HTTPS scan; shortcut for –sslv2 –sslv3 –tlsv1 –tlsv1_1 –tlsv1_2 –tlsv1_3 –reneg –resum –certinfo –hide_rejected_ciphers –compression –heartbleed –openssl_ccs –fallback –robot
- sslyze –regular www.vk9-sec.com

2. To save the results to file run
- sslyze –regular www.vk9-sec.com –json_out=results.json
- cat results.json

To write the file and don’t print anything on the screen use –quet
–quiet = Do not output anything to stdout; useful when using –json_out
- sslyze –regular www.vk9-sec.com –json_out=results.json –quiet
3. To check for a list of targets
–targets_in=TARGETS_IN = Read the list of targets to scan from the file TARGETS_IN. It should contain one host:port per line.
- vi sites.txt
- cat sites.txt (vk9-sec.com:443)
- sslyze –regular –targets_in=sites.txt

4. Run a slow and less aggressive test, but more accurate
- sslyze –regular www.vk9-sec.com –slow_connection

5. Scanning for some protocols at the target
–starttls=STARTTLS = Perform a StartTLS handshake when connecting to the target server(s).
- sslyze www.vk9-sec.com –starttls=auto

Types of scan
1. Scan for TLS 1.1 support
–tlsv1_1 = Test a server for TLS 1.1 support.
- sslyze www.vk9-sec.com –tlsv1_1

2. Test a server for the OpenSSL CCS Injection
- sslyze www.vk9-sec.com –openssl_ccs

3. Test a server for the TLS_FALLBACK_SCSV mechanism to prevent downgrade attacks.
- sslyze www.vk9-sec.com –fallback

4. Test a server for SSL 3.0 support.
- sslyze www.vk9-sec.com –sslv3

5. Test a server for the OpenSSL Heartbleed vulnerability.
- sslyze www.vk9-sec.com –heartbleed

6. Test a server for the ROBOT vulnerability.
- sslyze www.vk9-sec.com –robot

7. Test a server for the presence of security-related HTTP headers.
- sslyze www.vk9-sec.com –http_headers

8. Test a server for TLS 1.3 early data support.
- sslyze www.vk9-sec.com –early_data

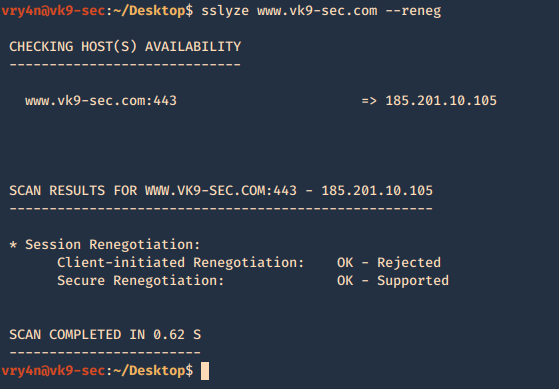
9. Test a server for for insecure TLS renegotiation and client-initiated renegotiation.
- sslyze www.vk9-sec.com –reneg
10. Test a server for TLS compression support, which can be leveraged to perform a CRIME attack.
- sslyze www.vk9-sec.com –compression

11. Test a server for session resumption support using session IDs and TLS tickets.
- sslyze www.vk9-sec.com –resum

12. Test a server for TLS 1.3 support.
- sslyze www.vk9-sec.com –tlsv1_3

13. Test a server for SSL 2.0 support.
- sslyze www.vk9-sec.com –sslv2

14. Retrieve and analyze a server’s certificate(s) to verify its validity.
- sslyze www.vk9-sec.com –certinfo
