In this article we will learn to enumerate users and groups manually.
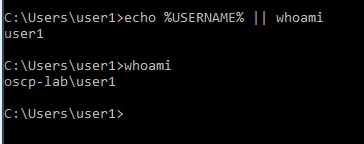
1. Check the current user
- echo %USERNAME% || whoami
- whoami
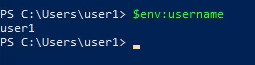
Powershell
- env:username
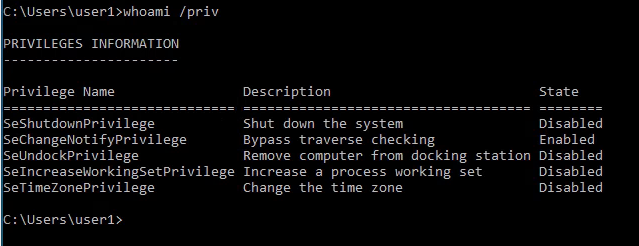
2. View the logged in user privileges
- whoami /priv
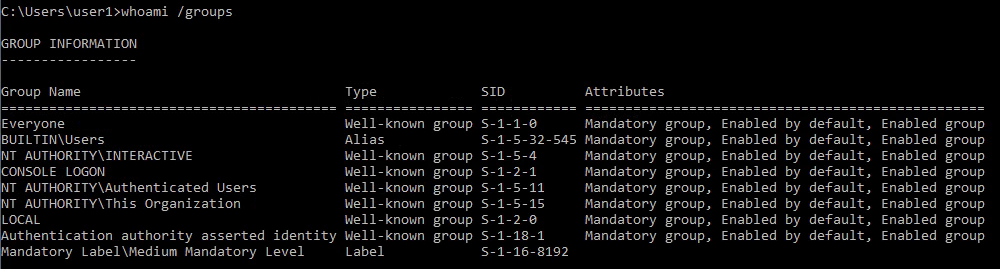
3. Display the user groups to which the current user belongs.
- whoami /groups
4. See the local users
- net user

Note: User1 is not listed as it is a Domain user
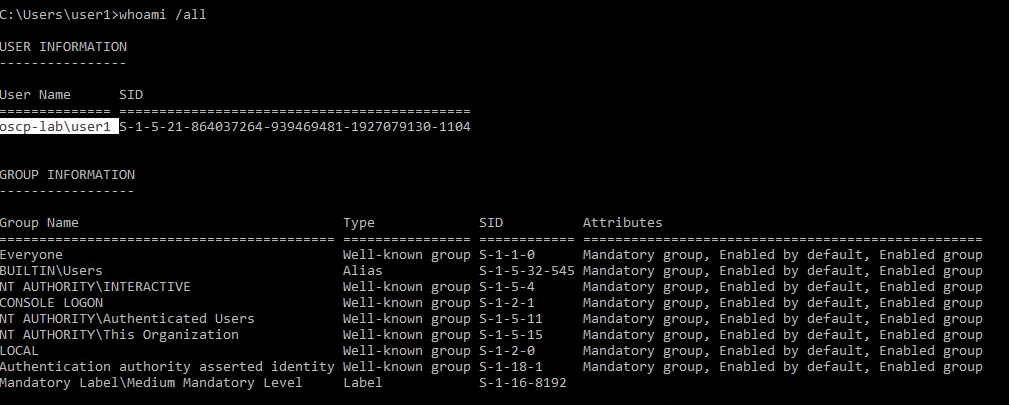
5. To view all users including local and domain users that have logged in to this machine
- whoami /all
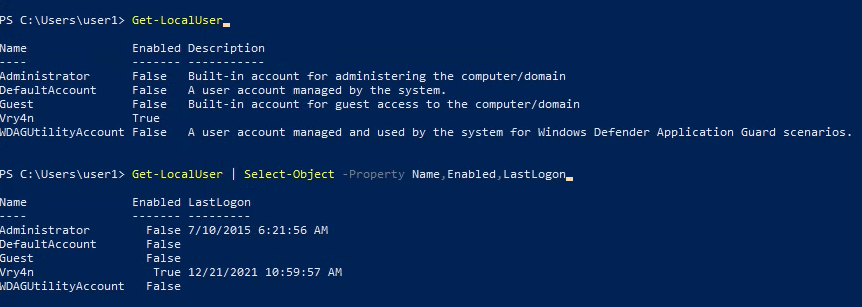
6. You can also see local users using powershell
- Get-LocalUser
- Get-LocalUser | Select-Object -Property Name,Enabled,LastLogon
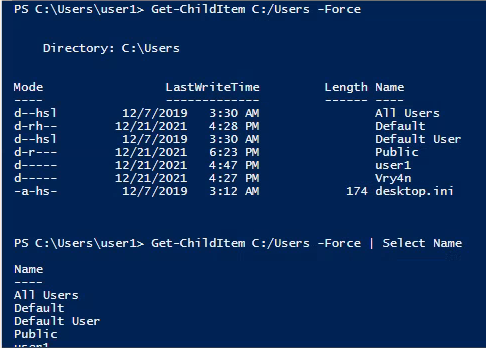
7. We could also get usernames by inspecting the users directory (C:/Users)
- Get-ChildItem C:/Users -Force
- Get-ChildItem C:/Users -Force | Select Name
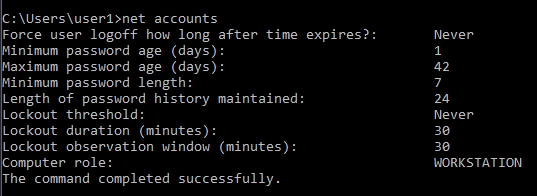
8. The “Net Accounts” command is used to set the policy settings on local computer, such as Account policies and password policies. This command can’t be used on domain controller. This command is only used on local computer.
- net accounts
9. Learn more about a specific local user
- net user administrator

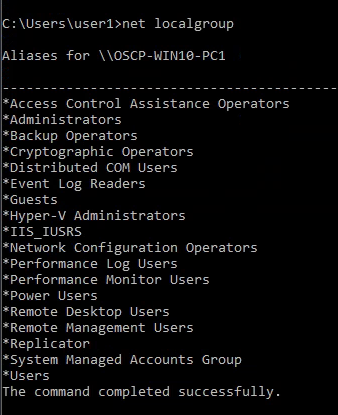
10. net localgroup displays the name of the server and the names of local groups on the computer.
- net localgroup
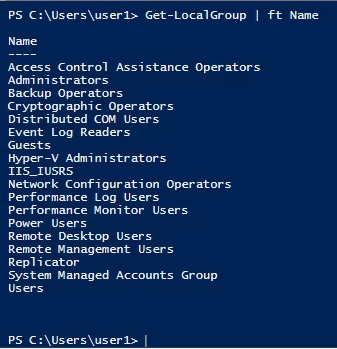
11. you can also get the local groups using Powershell
- Get-LocalGroup
- Get-LocalGroup | ft Name
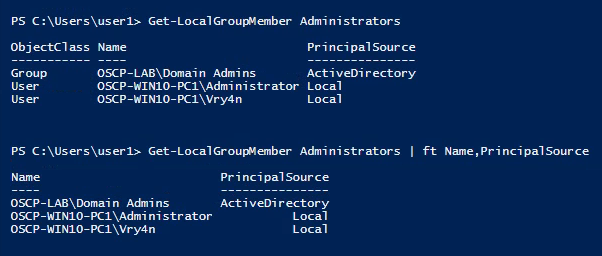
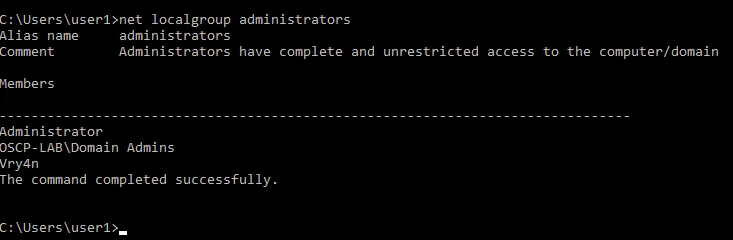
12. You can also see the users that belong to a group
- net localgroup administrators
13. You can also get user membership using powershell
- Get-LocalGroupMember Administrators
- Get-LocalGroupMember Administrators | ft Name,PrincipalSource