by Vry4n_ | Mar 15, 2020 | Passive Gathering
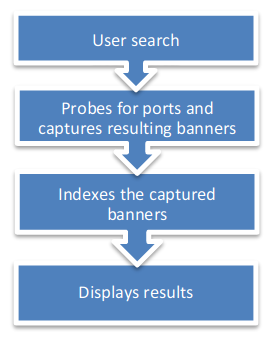
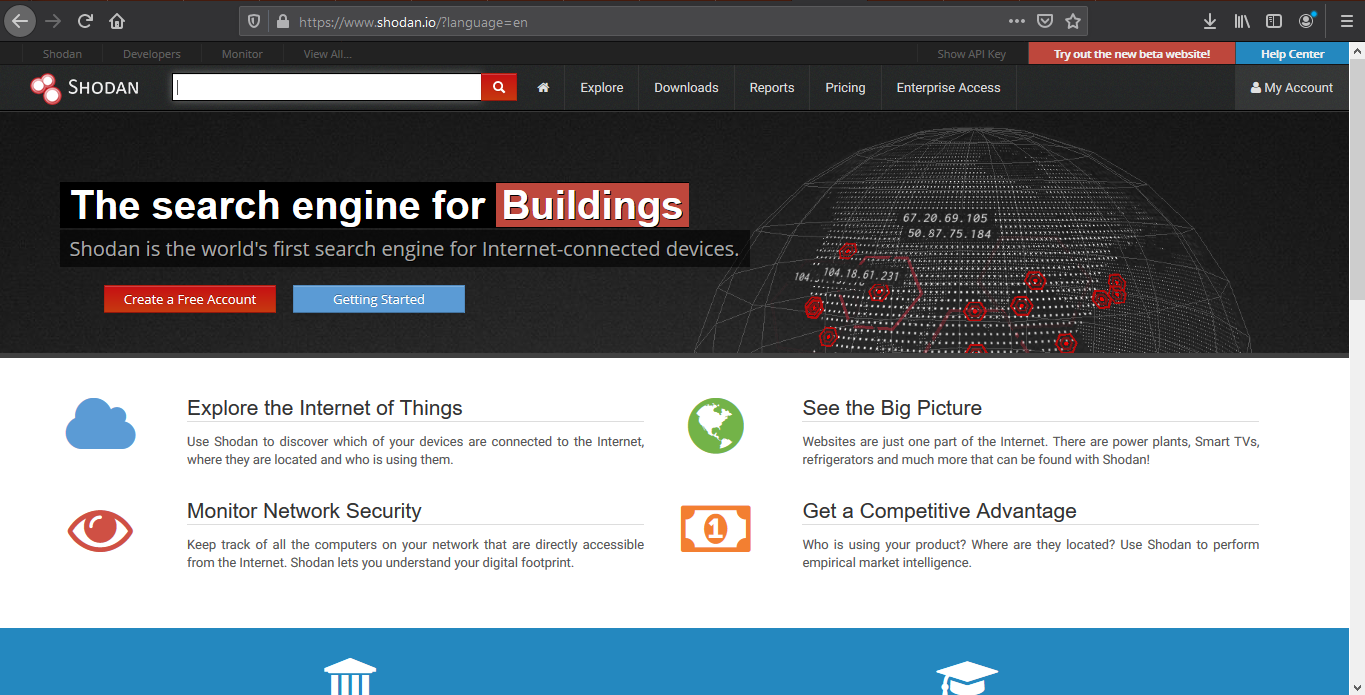
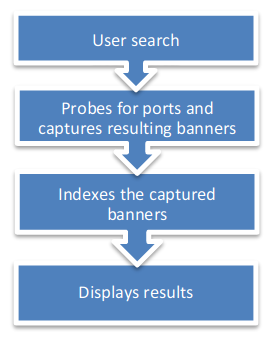
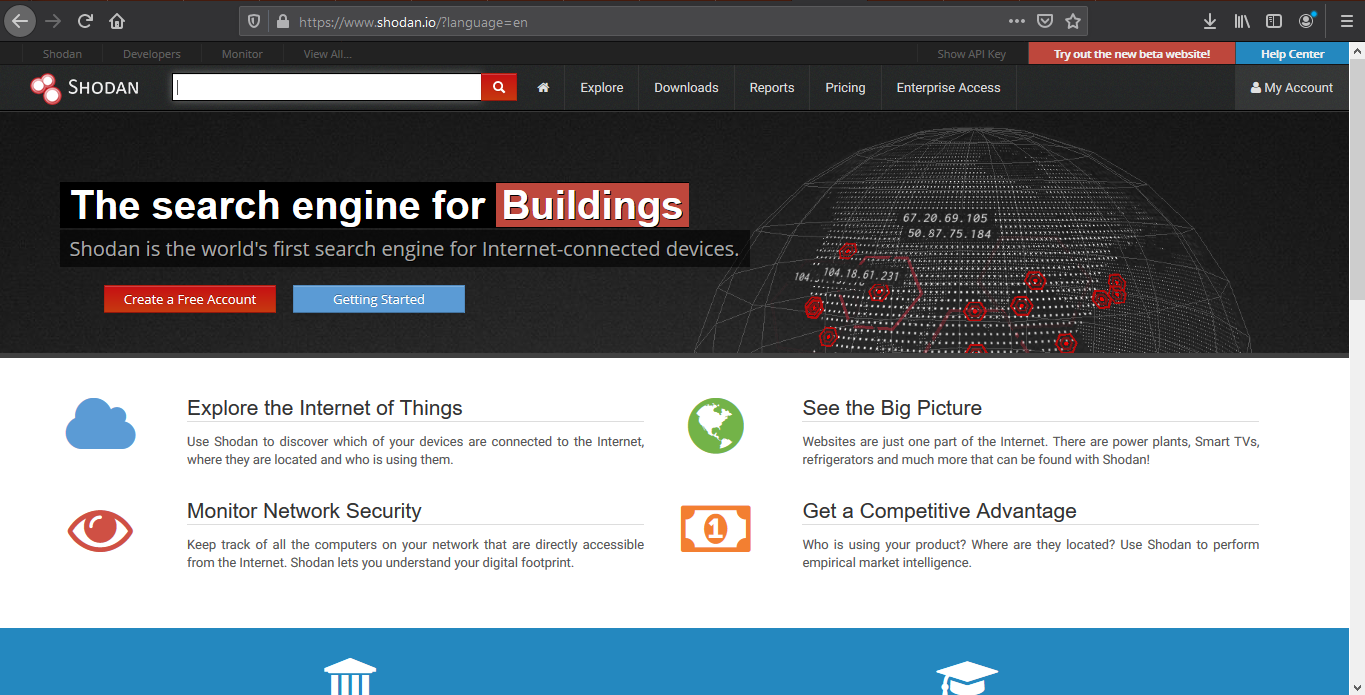
Shodan’s a search engine which helps find systems on the internet. It’s a great resource to provide passive reconnaissance.
Some have described Shodan as a search engine for hackers, and have even called it “the world’s most dangerous search engine”.
Devices that Shodan can find:
- Servers
- Routers
- Switches
- Printers on public ip
- Webcams
- Gas station pumps
- Voip phones
- Scada devices
- Etc
How to
1. visit https://shodan.io/

2. Click on “Login or Registration”. Create an account and log in
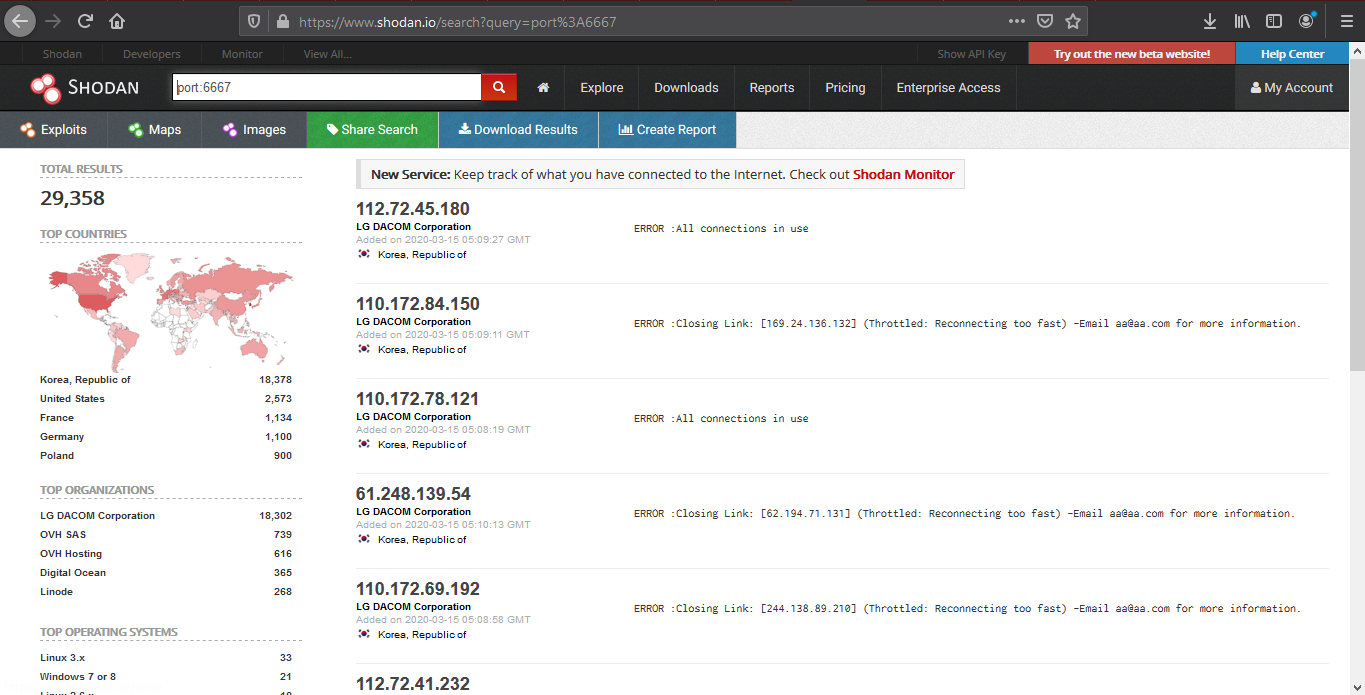
3. Once logged in, use the search bar to look for devices
Also, under “My account” you can do and find the following
- API information
- Change account password
Basic search Filters
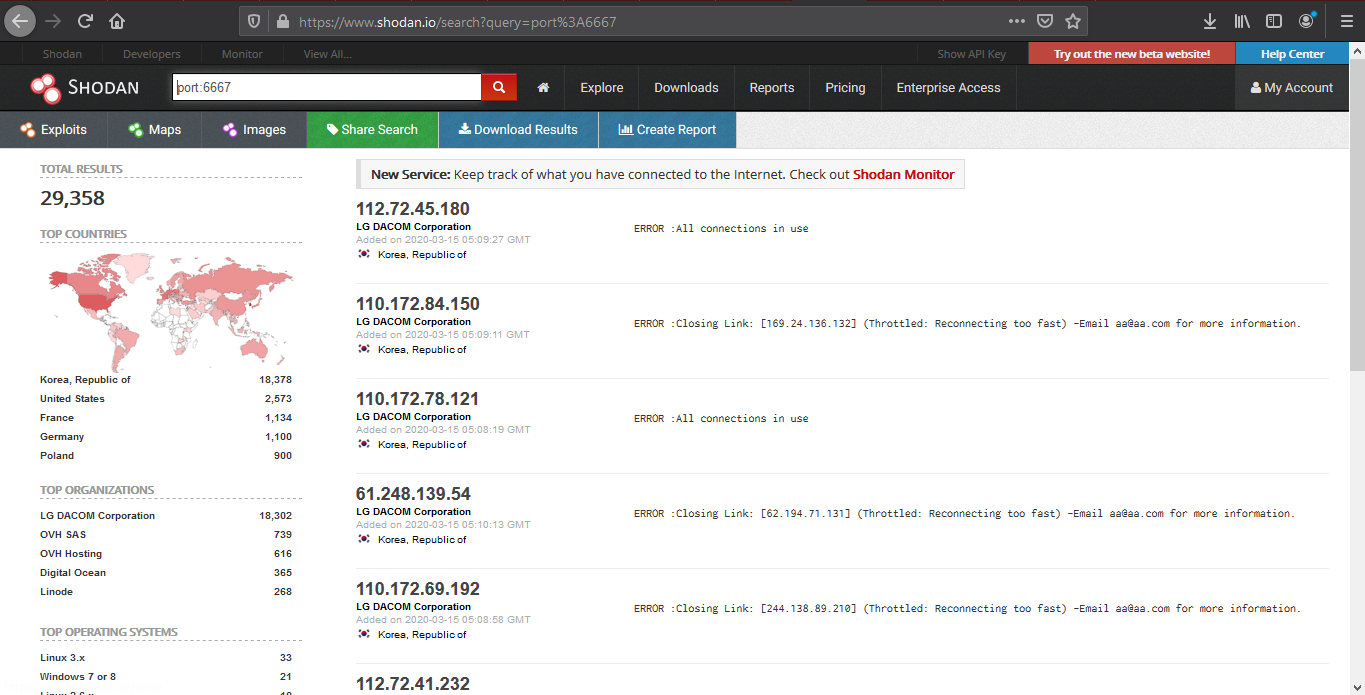
- Port: Search by specific port
- net: Search based on an IP/CIDR
- hostname: Locate devices by hostname
- os: Search by Operating System
- city: Locate devices by city
- country: Locate devices by country
- geo: Locate devices by coordinates
- org: Search by organization
- before/after: Timeframe delimiter
- hash: Search based on banner hash
- has_screenshot:true Filter search based on a screenshot being present
- title: Search based on text within the title
Searching
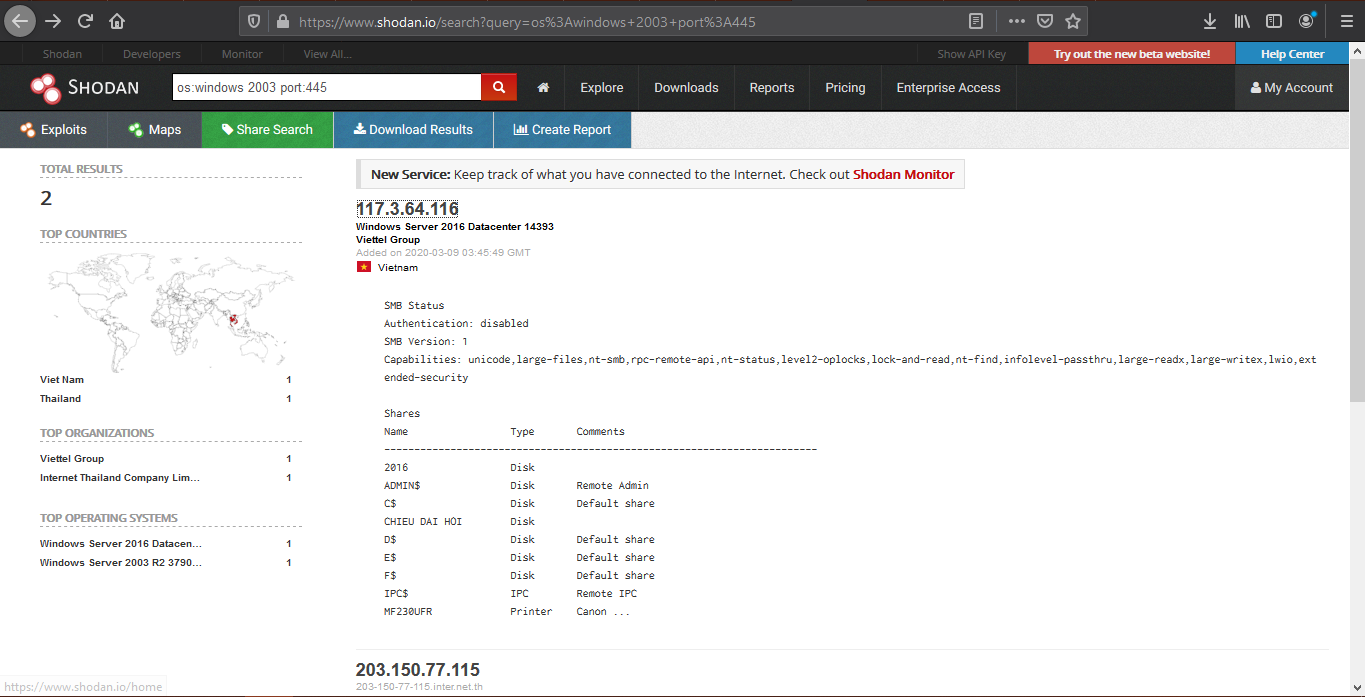
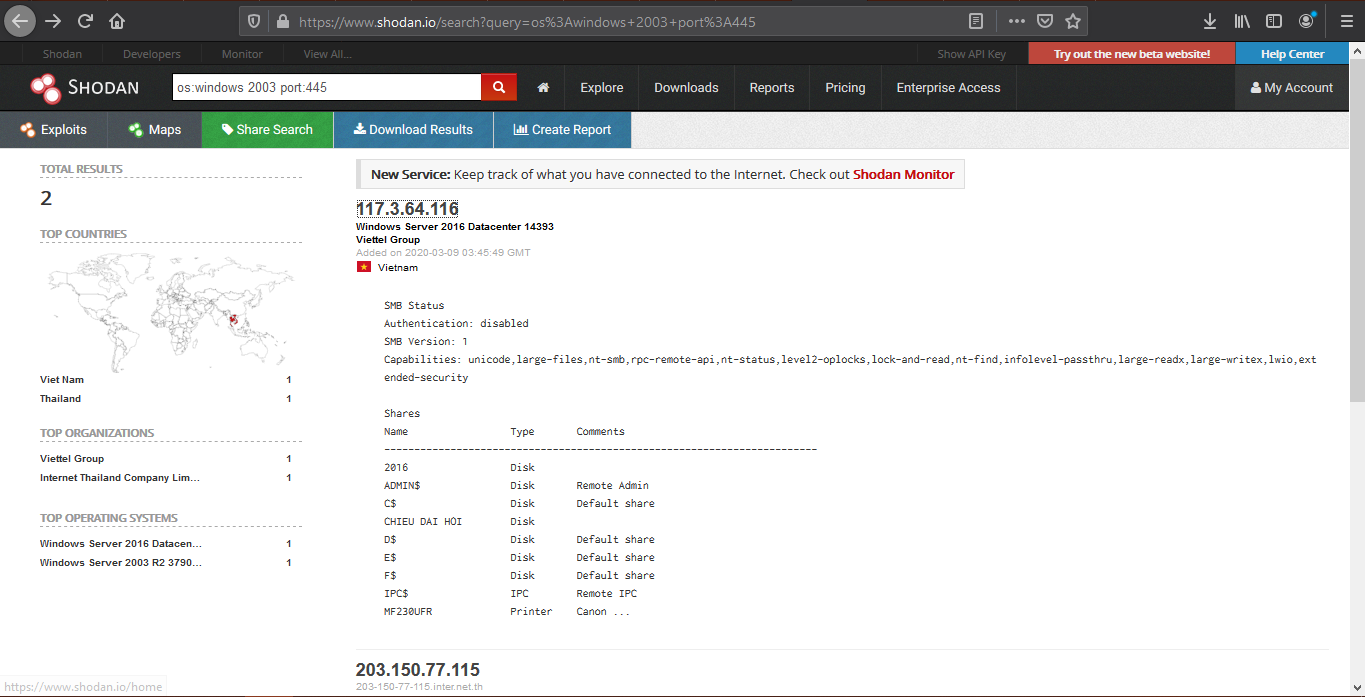
1. Find devices that run a specific port
2. Look for devices that have a specific OS and a port
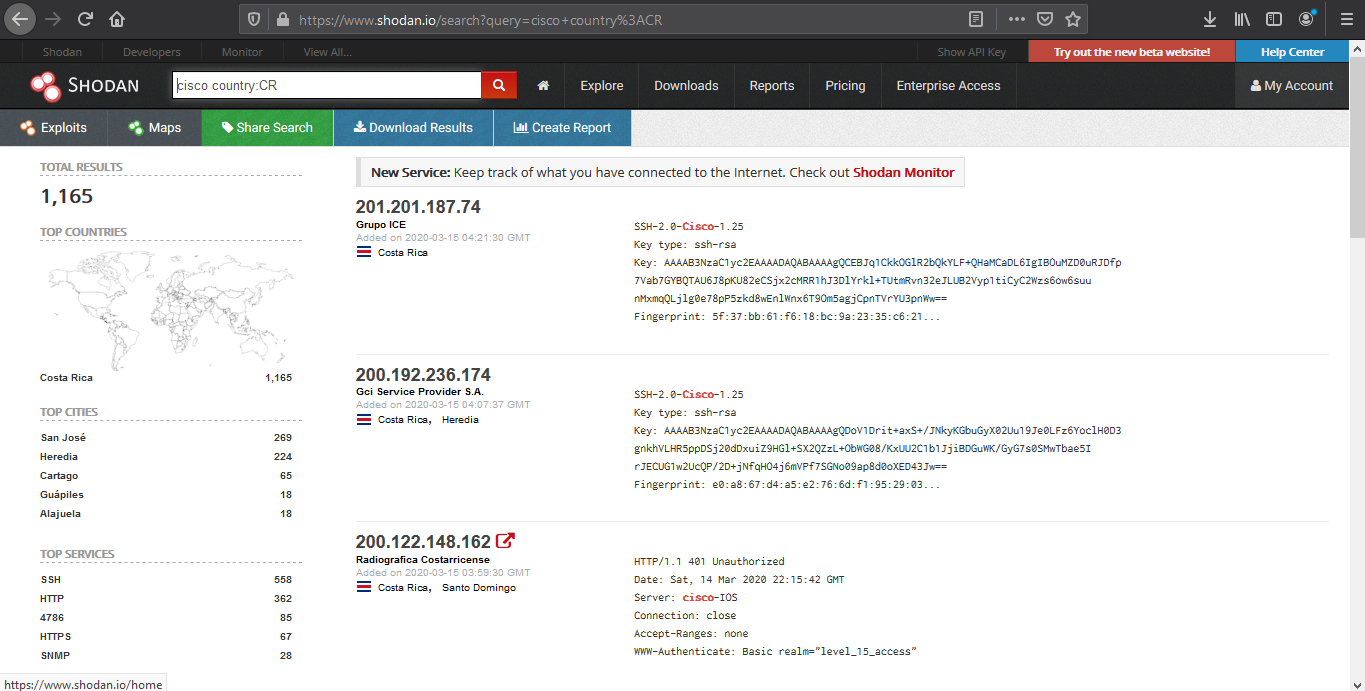
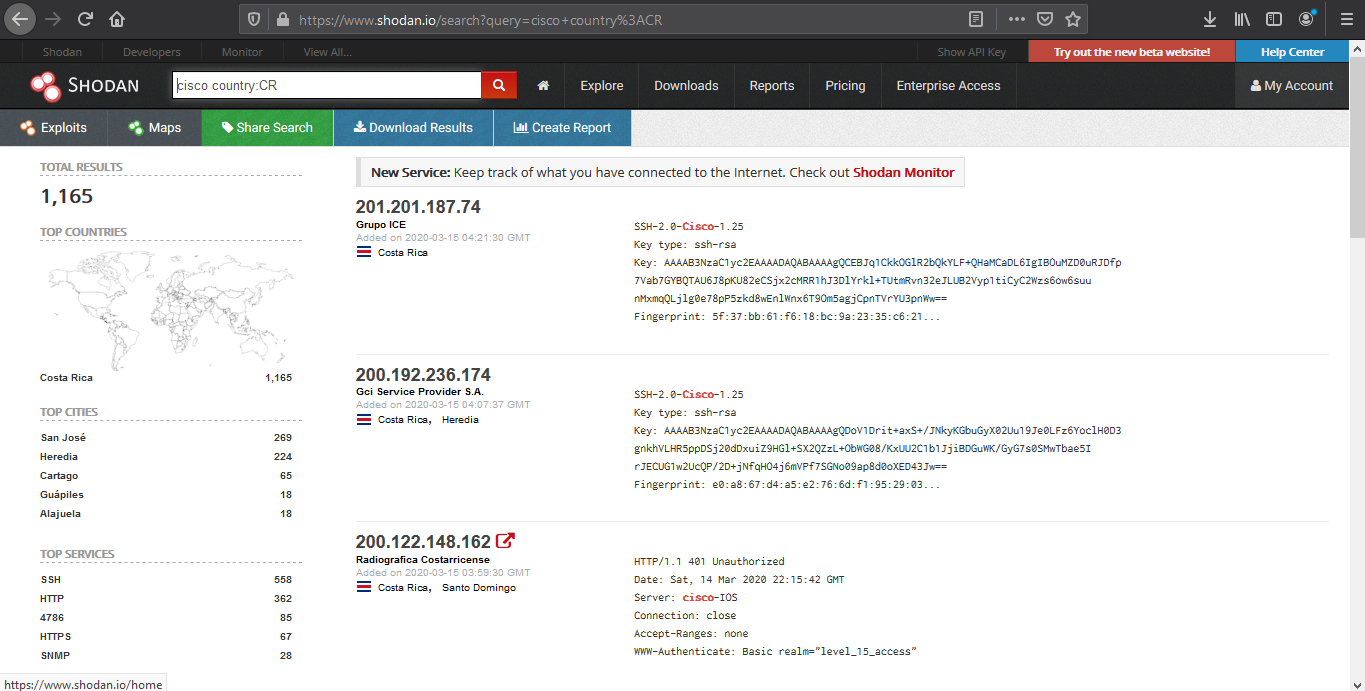
3. Look for device per country, and a keyword
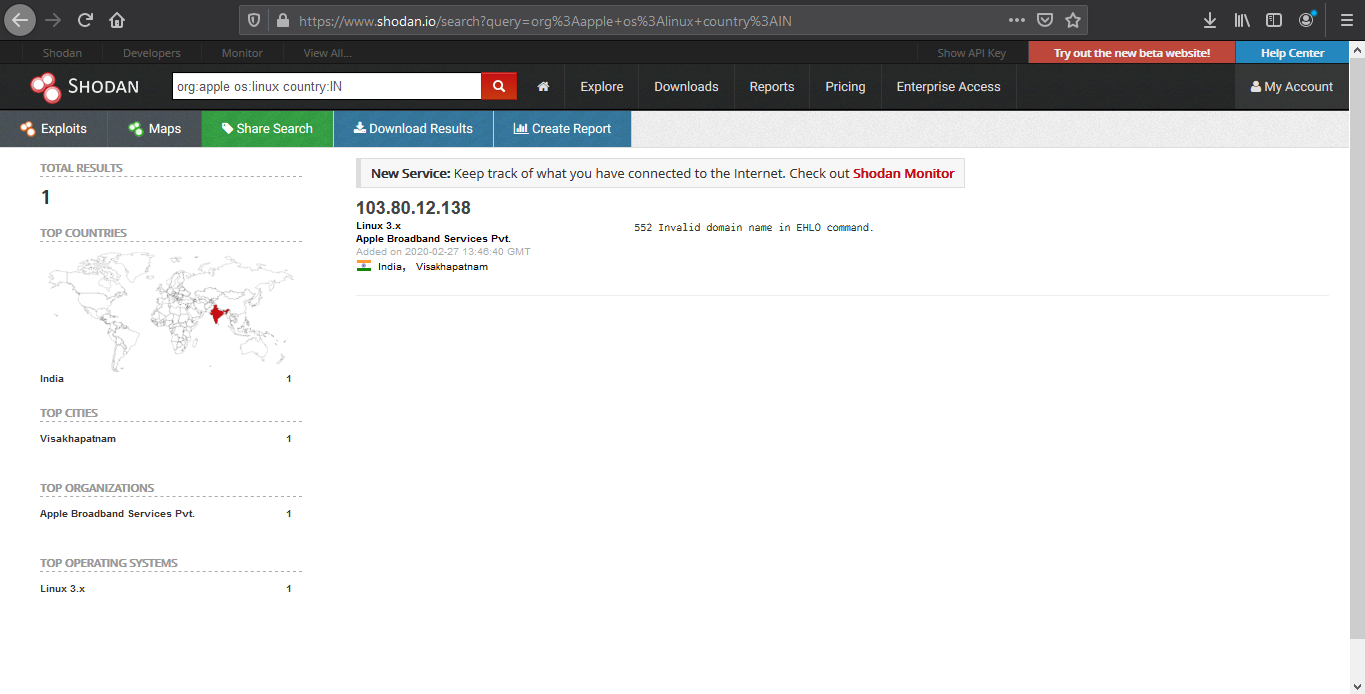
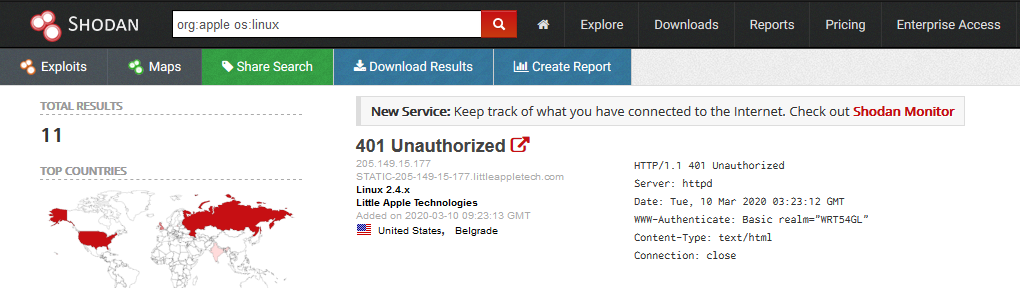
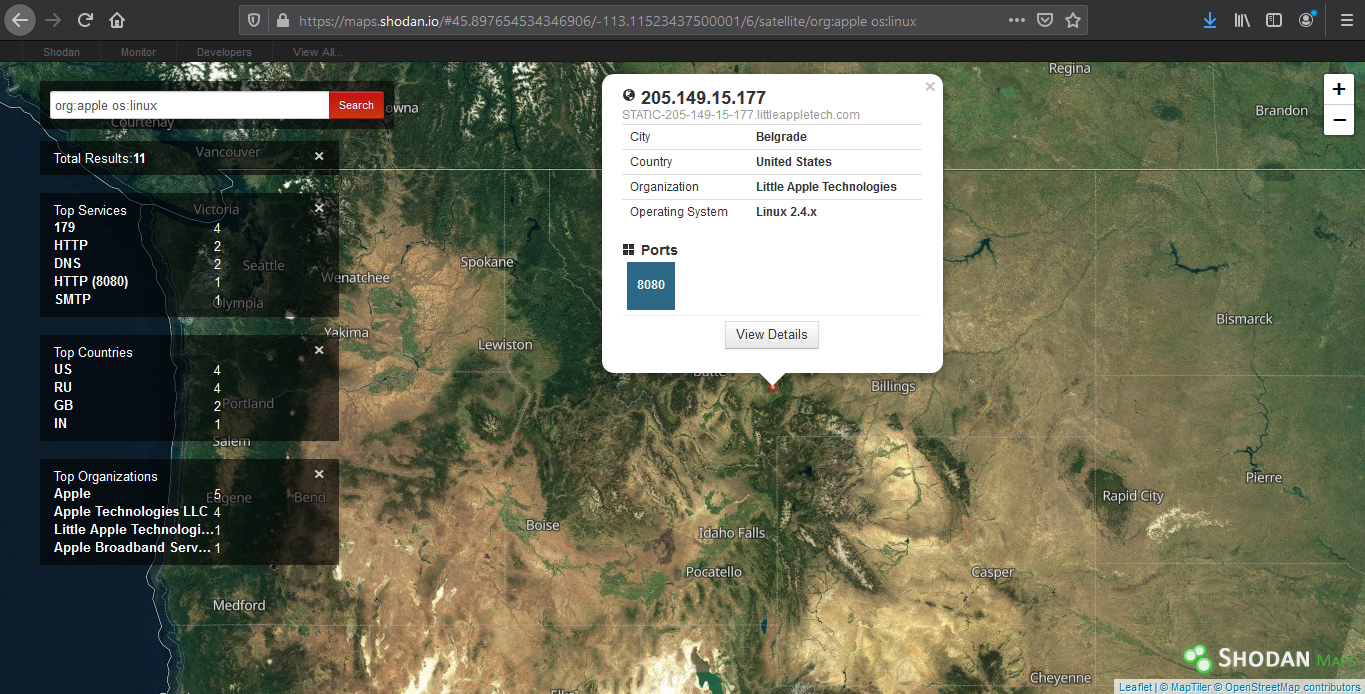
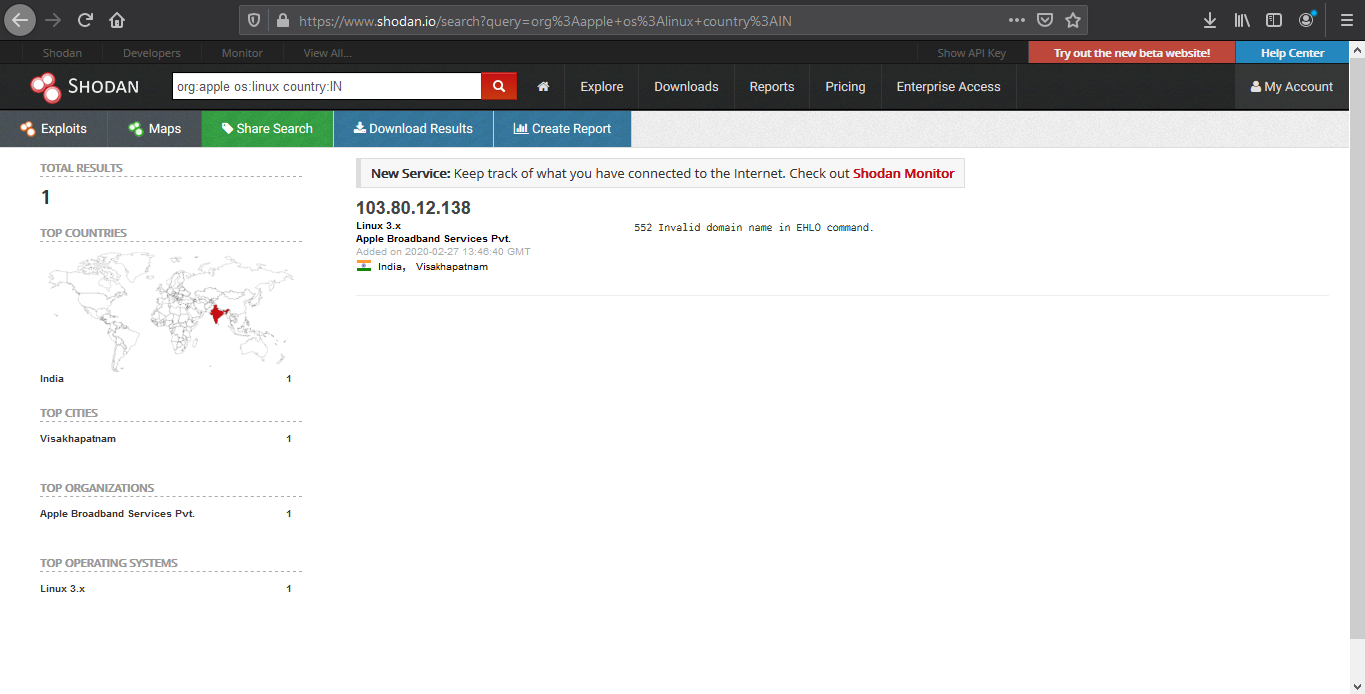
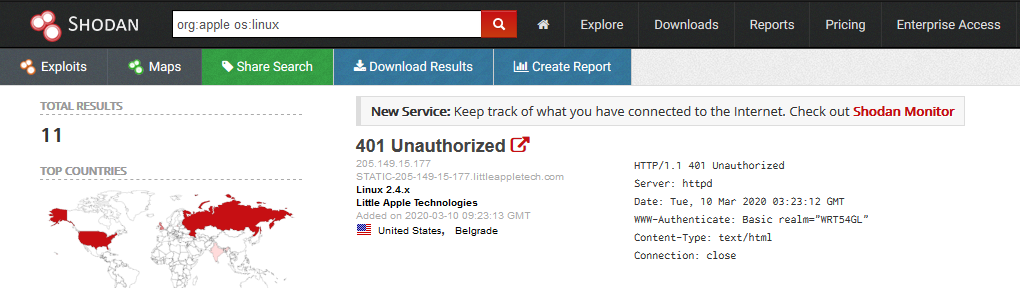
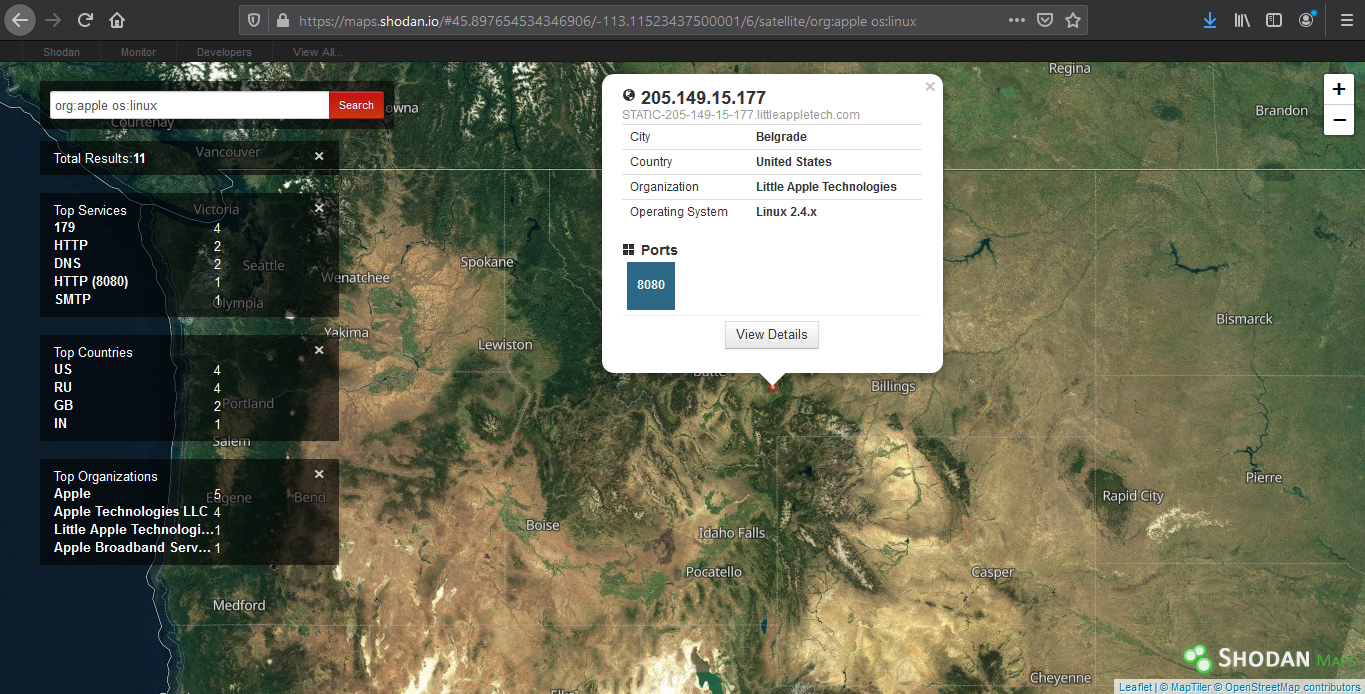
4. We can also search by company, OS type and their location
- org:apple os:linux country:IN
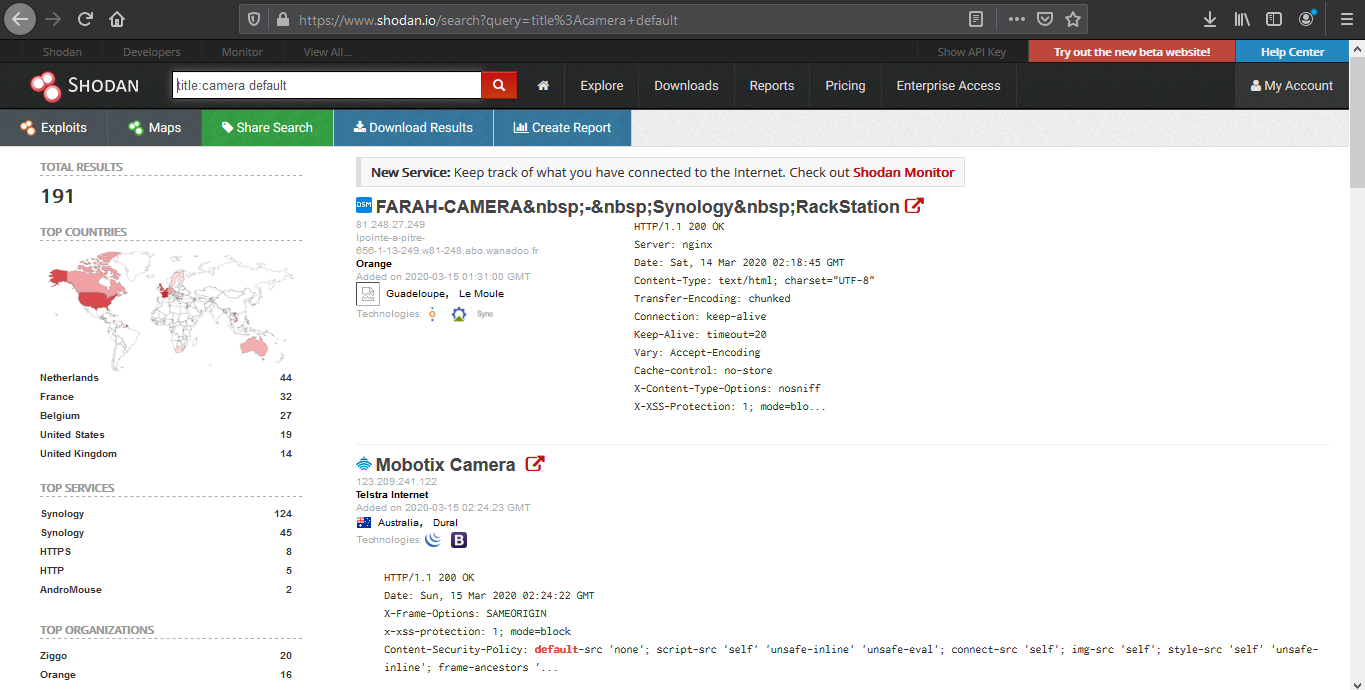
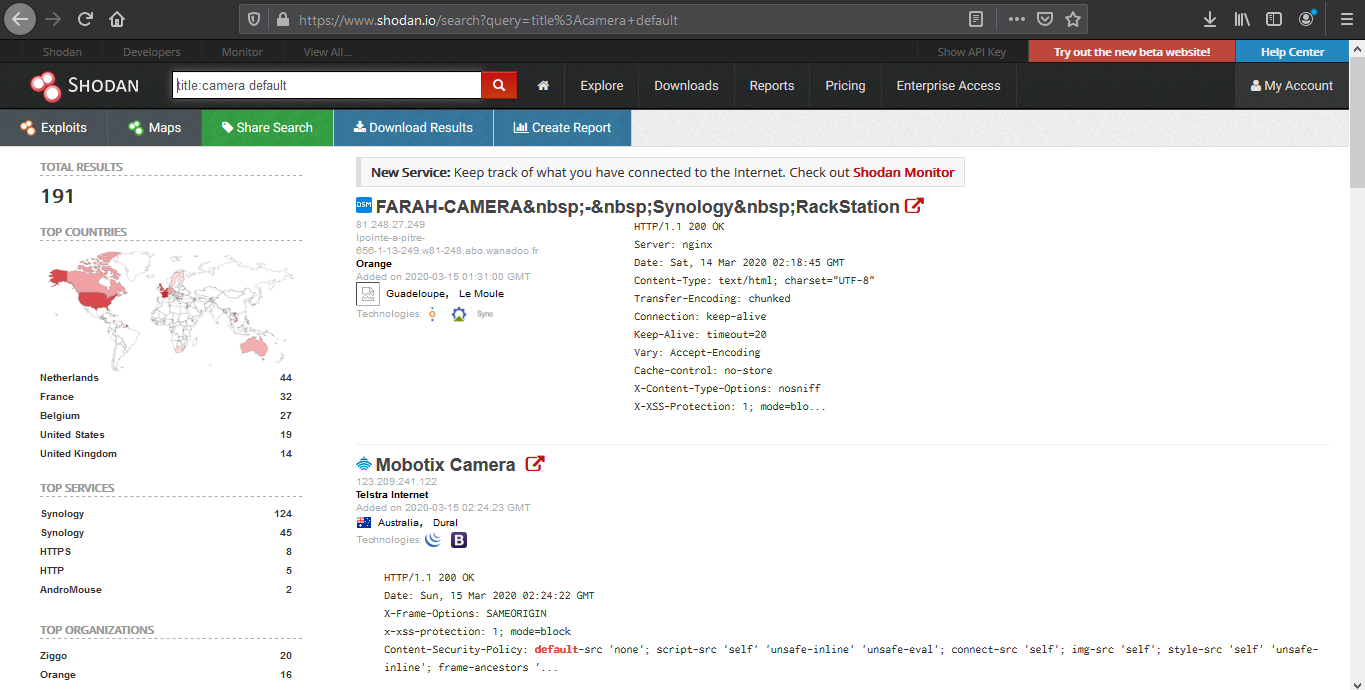
5. Search for title details and keywords
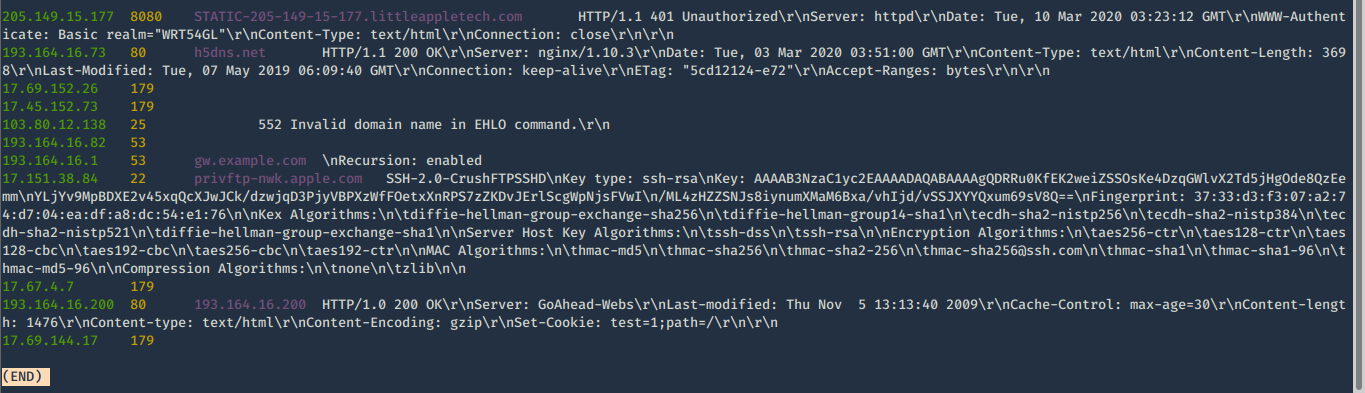
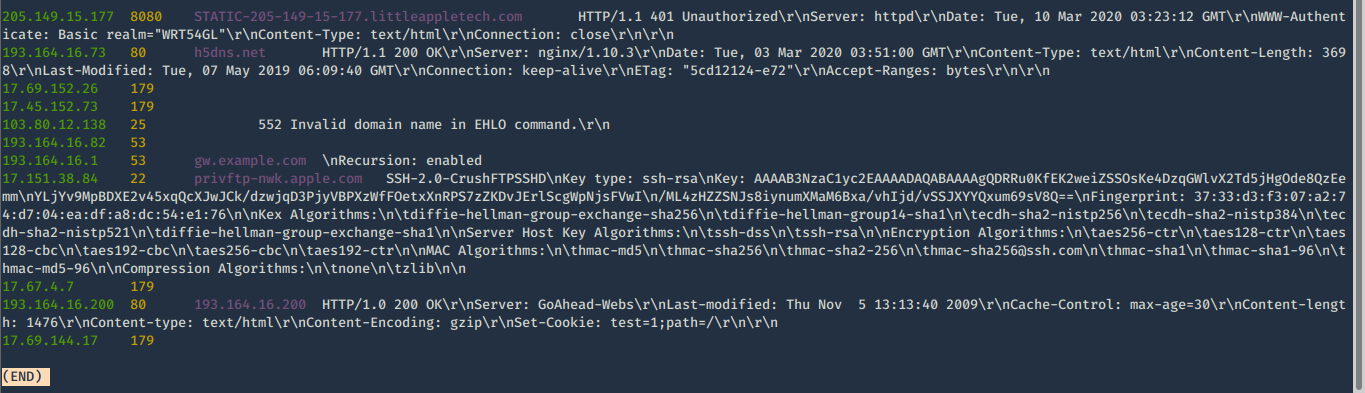
Analyzing the results
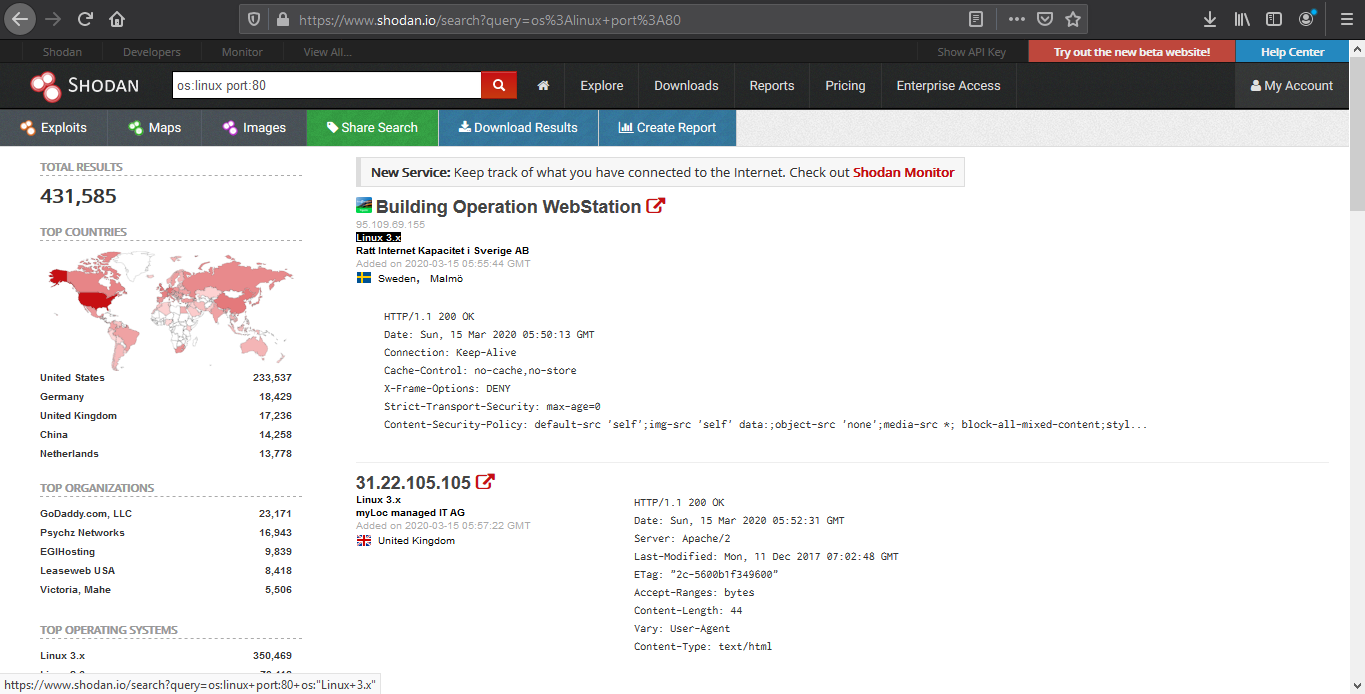
1. We are going to look for a Linux server with port 80 opened
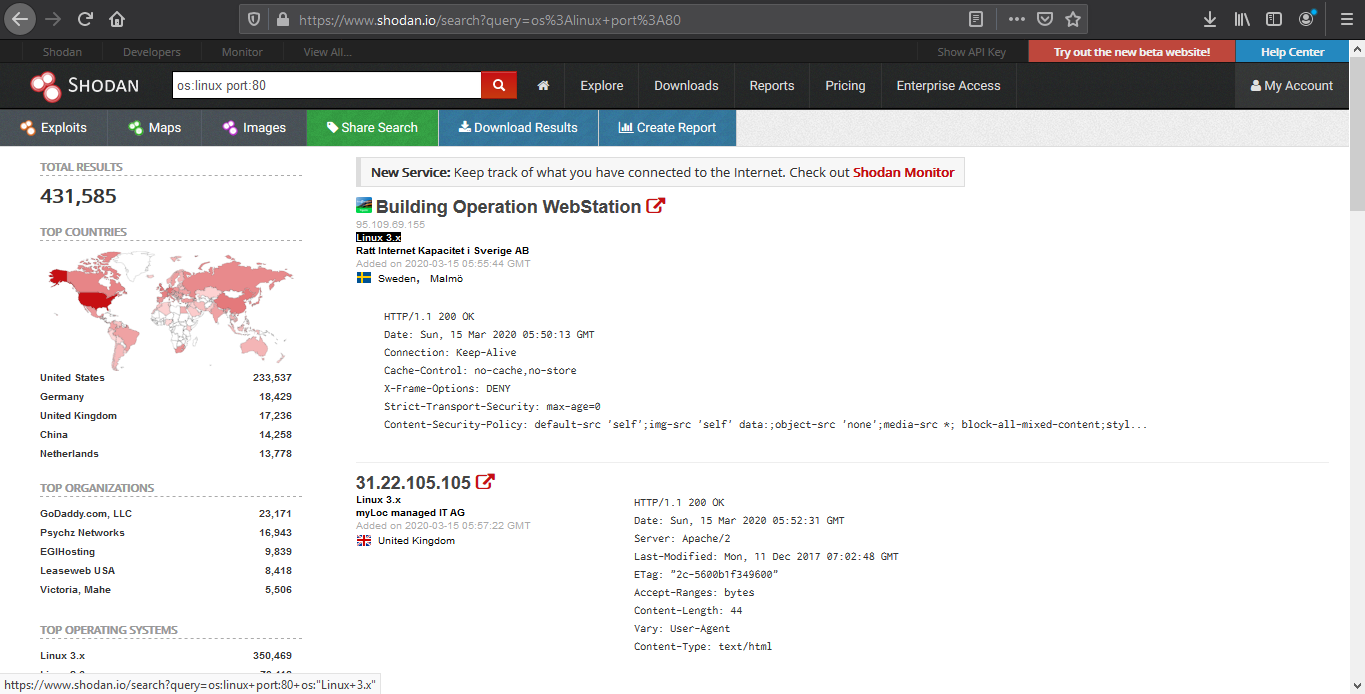
2. Opening the first result takes us to the details of that
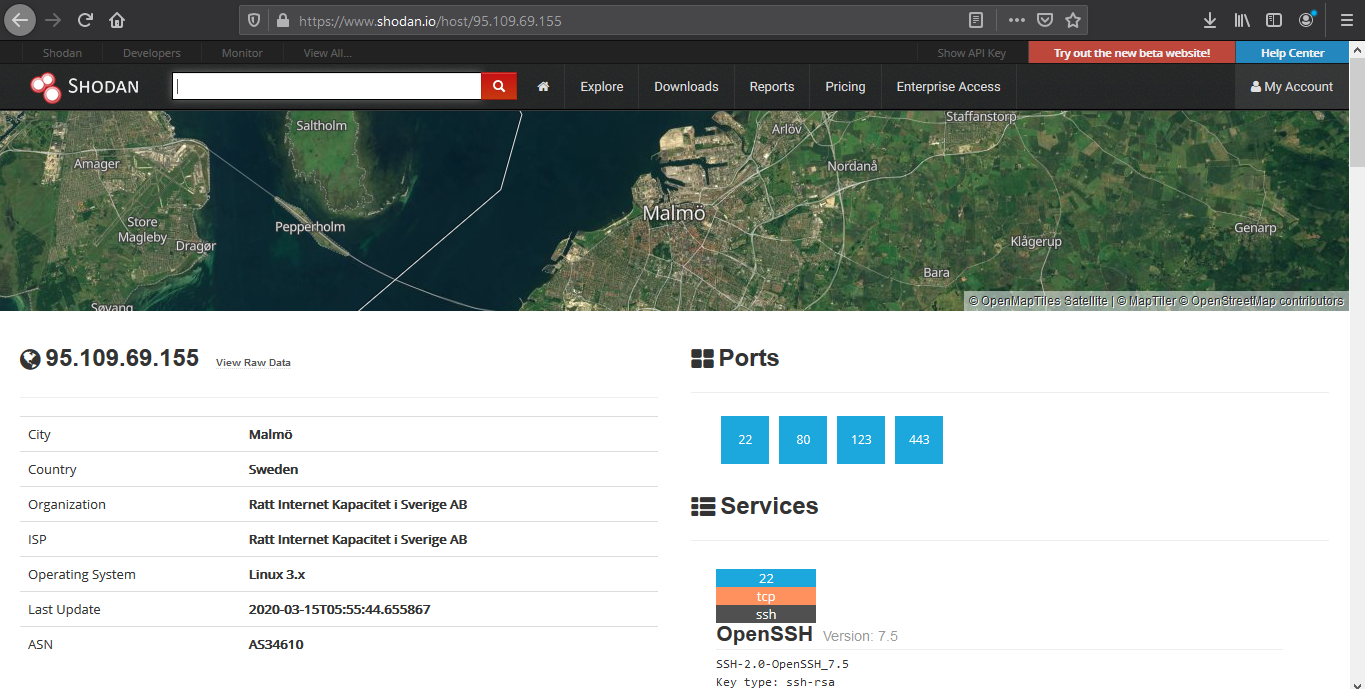
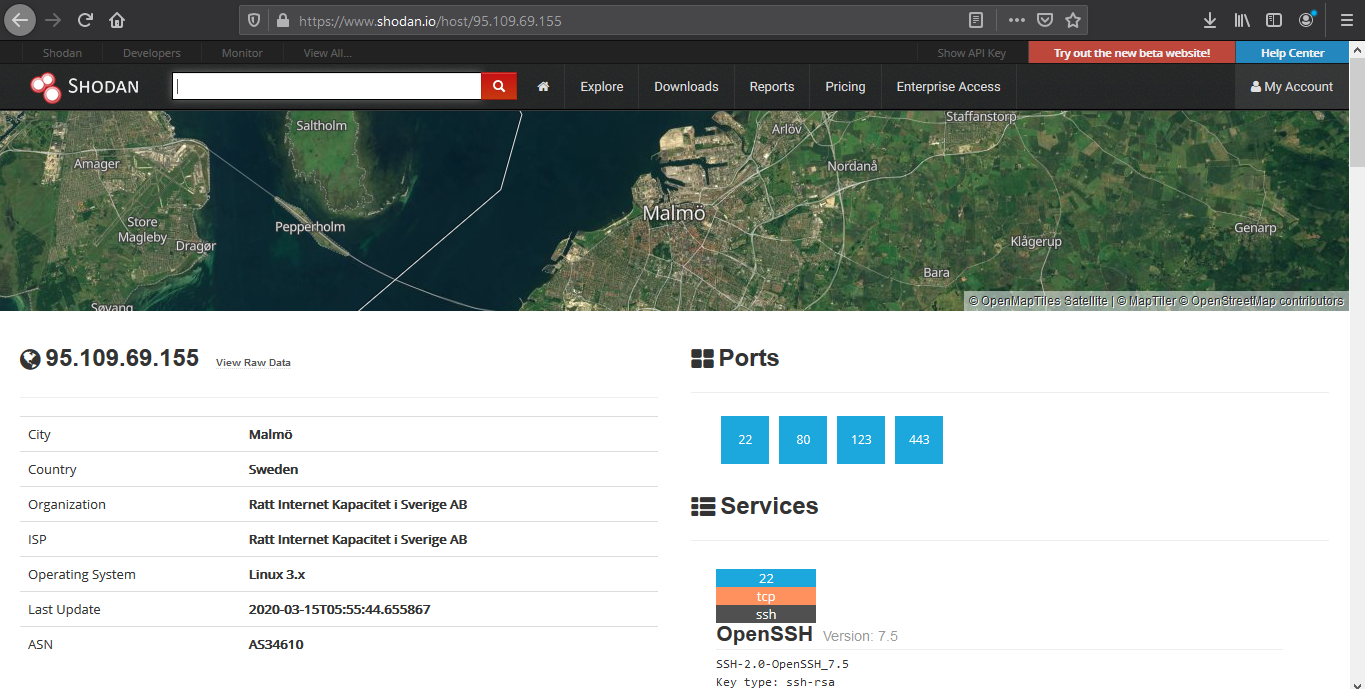
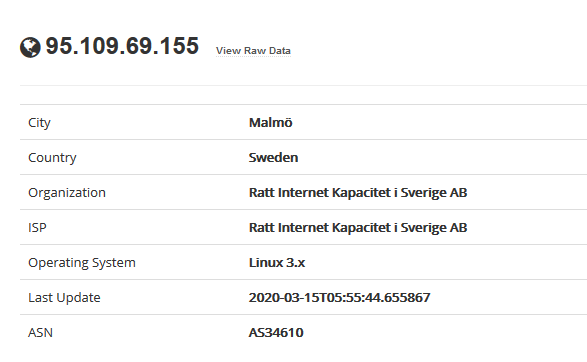
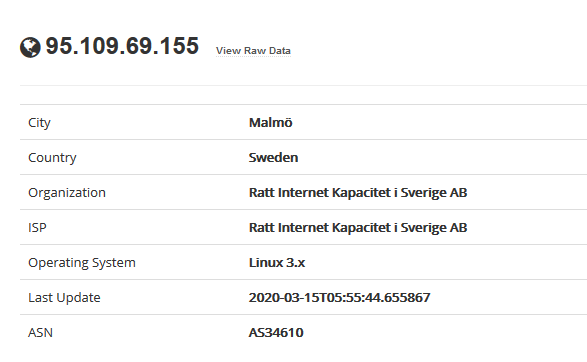
Device details displays basic information like the one below
- IP
- City
- Country
- Organization
- ISP
- Operating System
- Last Update
- ASN
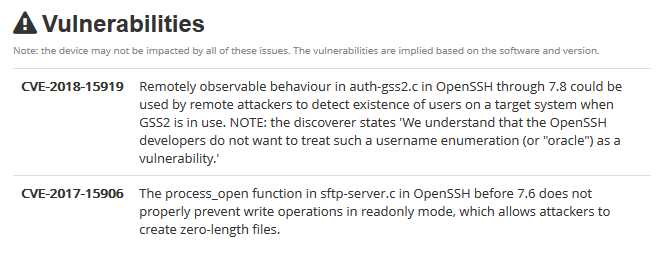
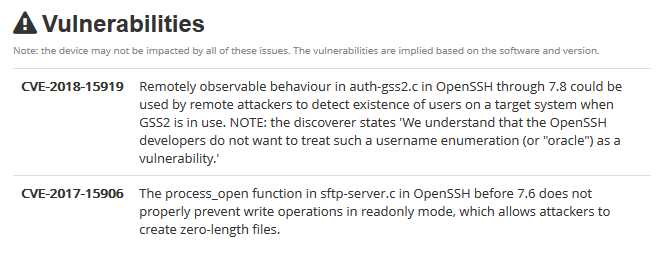
The results may sometimes show vulnerability scanning results.
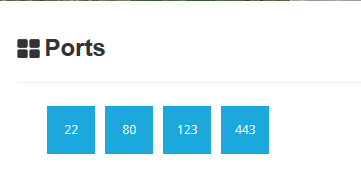
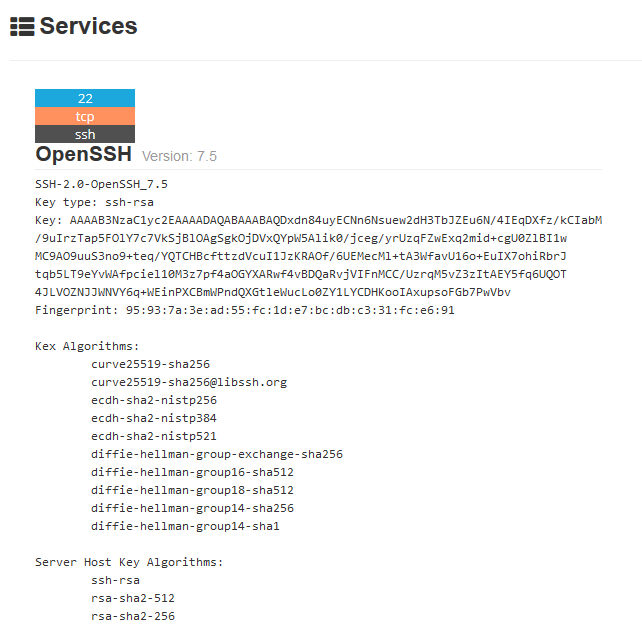
Opened port are also displayed
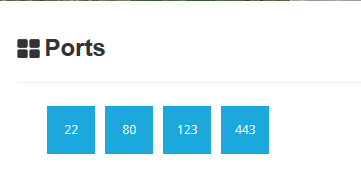
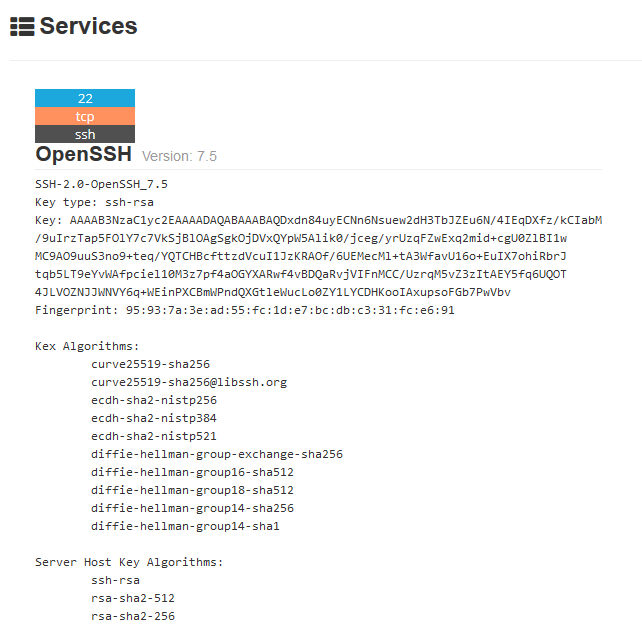
Each port discovered shows more info about the protocol. Sometimes useful configuration information can be displayed in there.
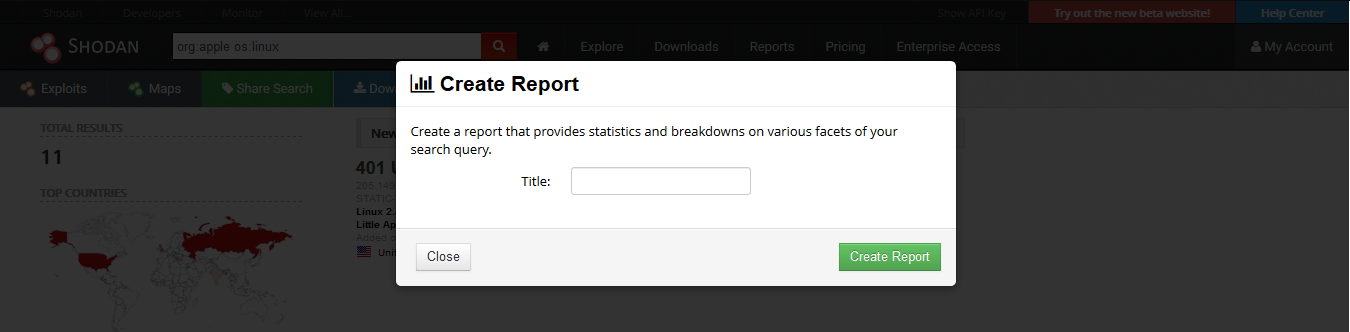
Reporting
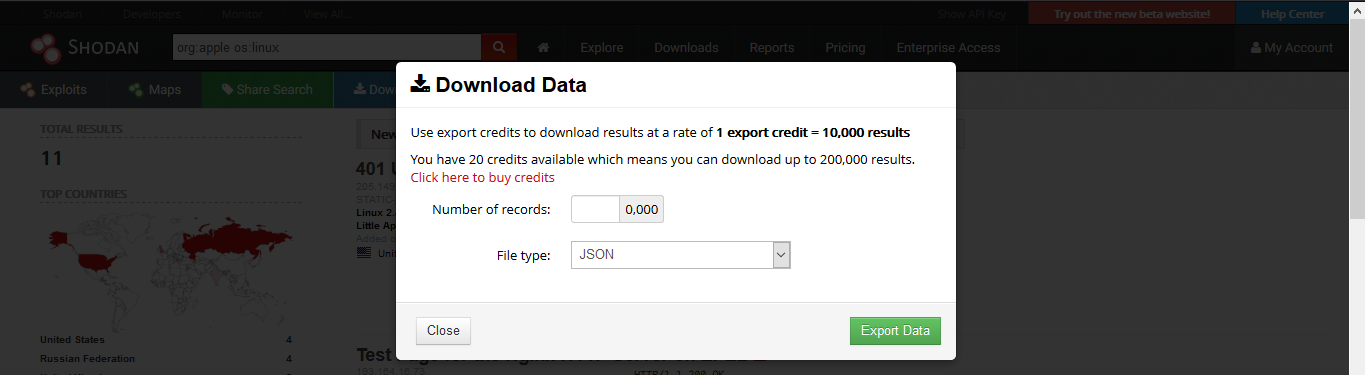
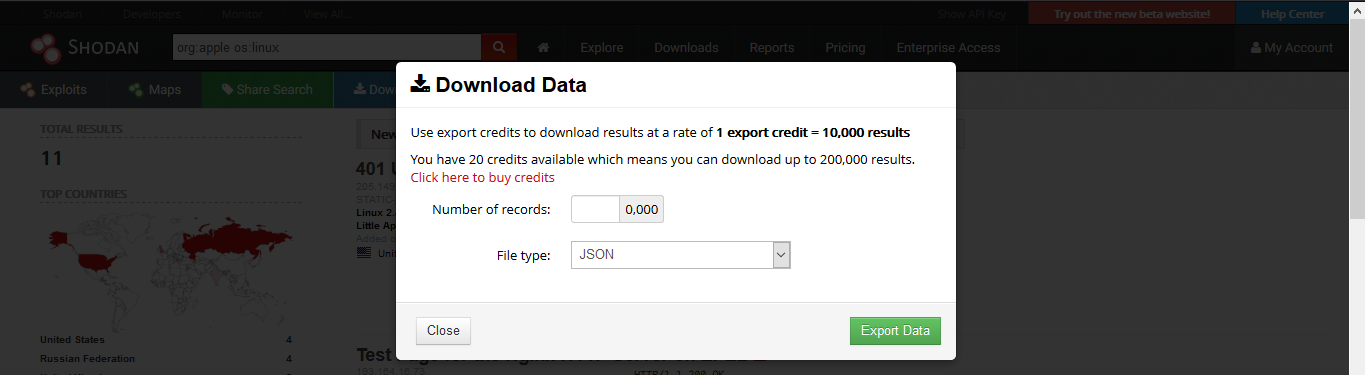
1. Download Data
Clicking on “Download Results” data lets you download the results, this requires credits, use them wisely
2. Creating a Report
Clicking on “Create Report” lets you download a report of results
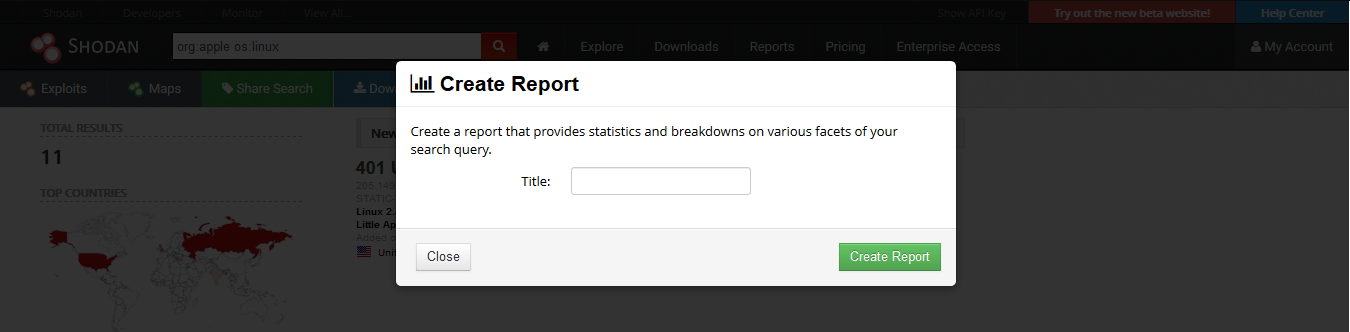
3. Going to “Reports” you can see generated file

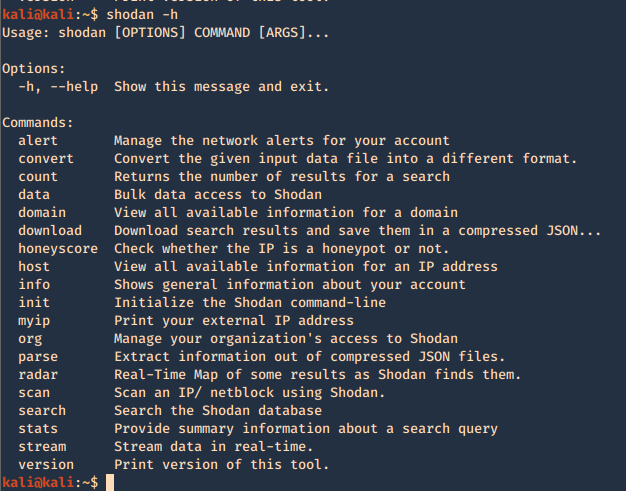
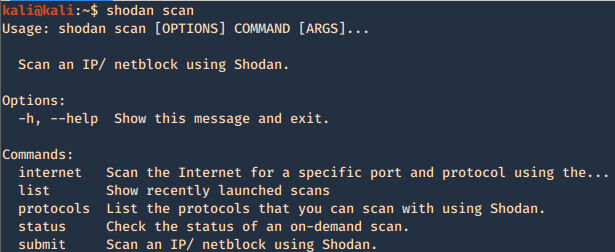
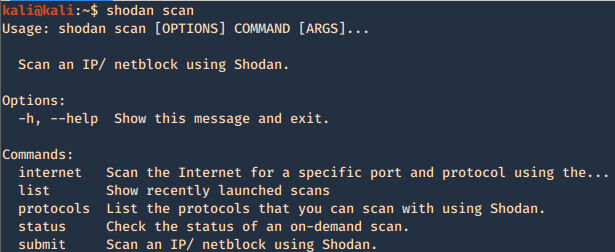
CLI
Shodan also provides an easy to use command line (https://cli.shodan.io/), it comes already install in kali, but, you can visit the official site to learn hot to install it.
1. Display help
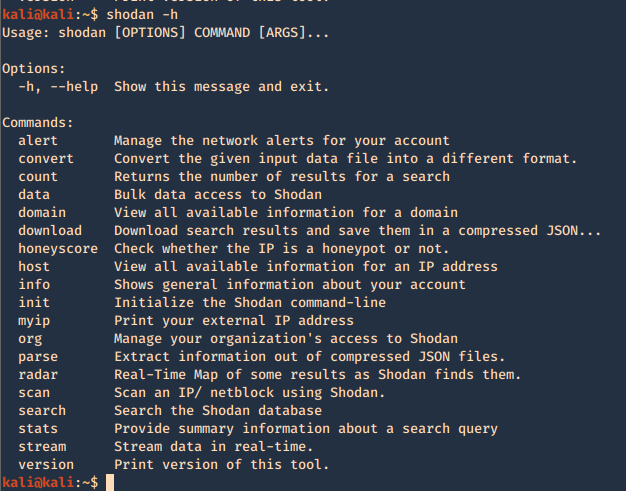
Using -h over the command will display further help
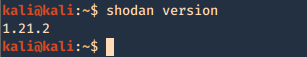
2. Show product version
3. Set up your API for starting the searches, API is found under account settings
4. First basic search
- shodan search org:apple os:linux
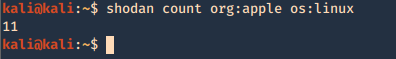
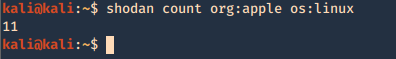
5. Show count of the searches
- shodan count org:apple os:linux
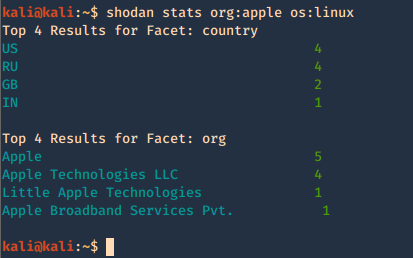
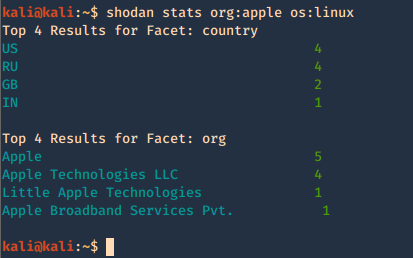
6. Show stats of the search
- shodan stats org:apple os:linux
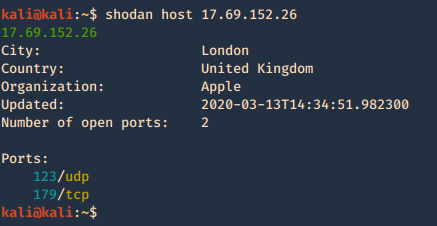
7. Check host info
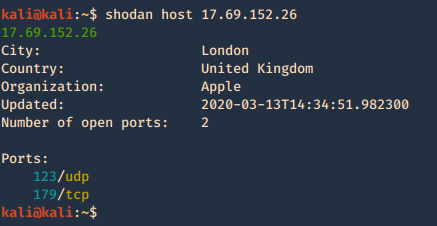
Shodan Maps
Shodan also provides a graphical map that helps you visualize the location of the result
(https://maps.shodan.io)
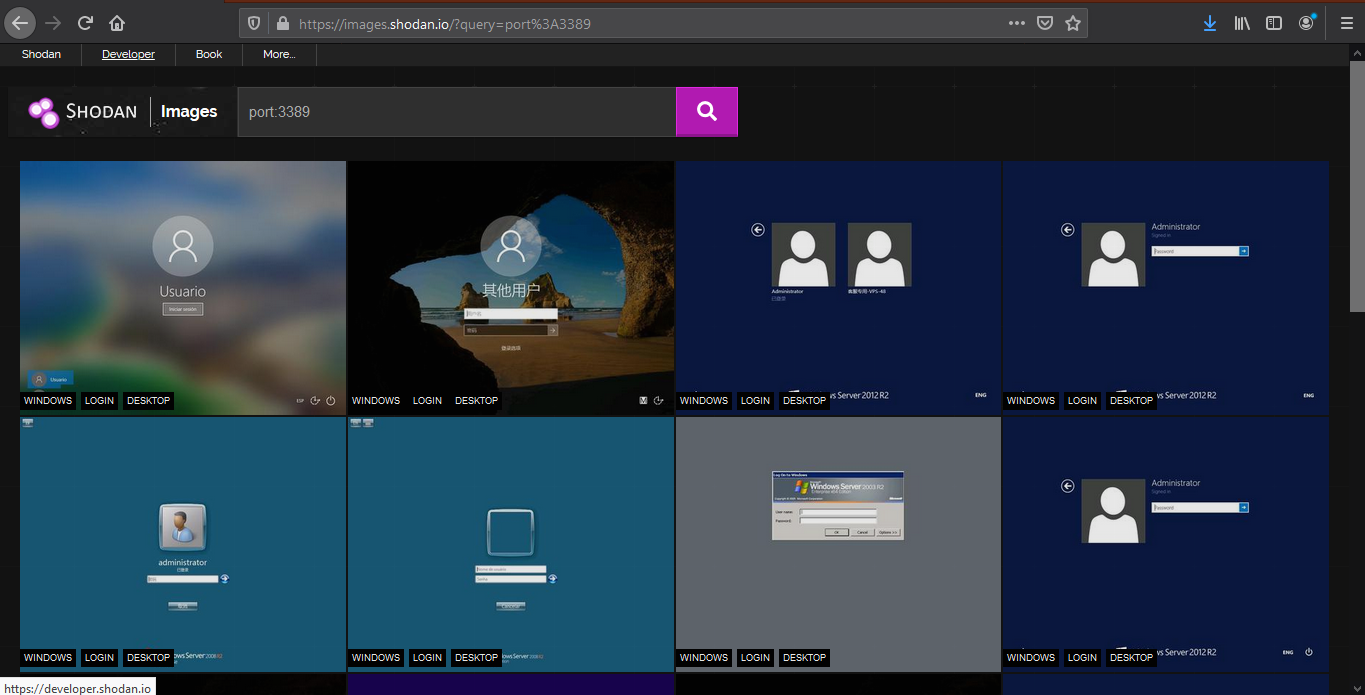
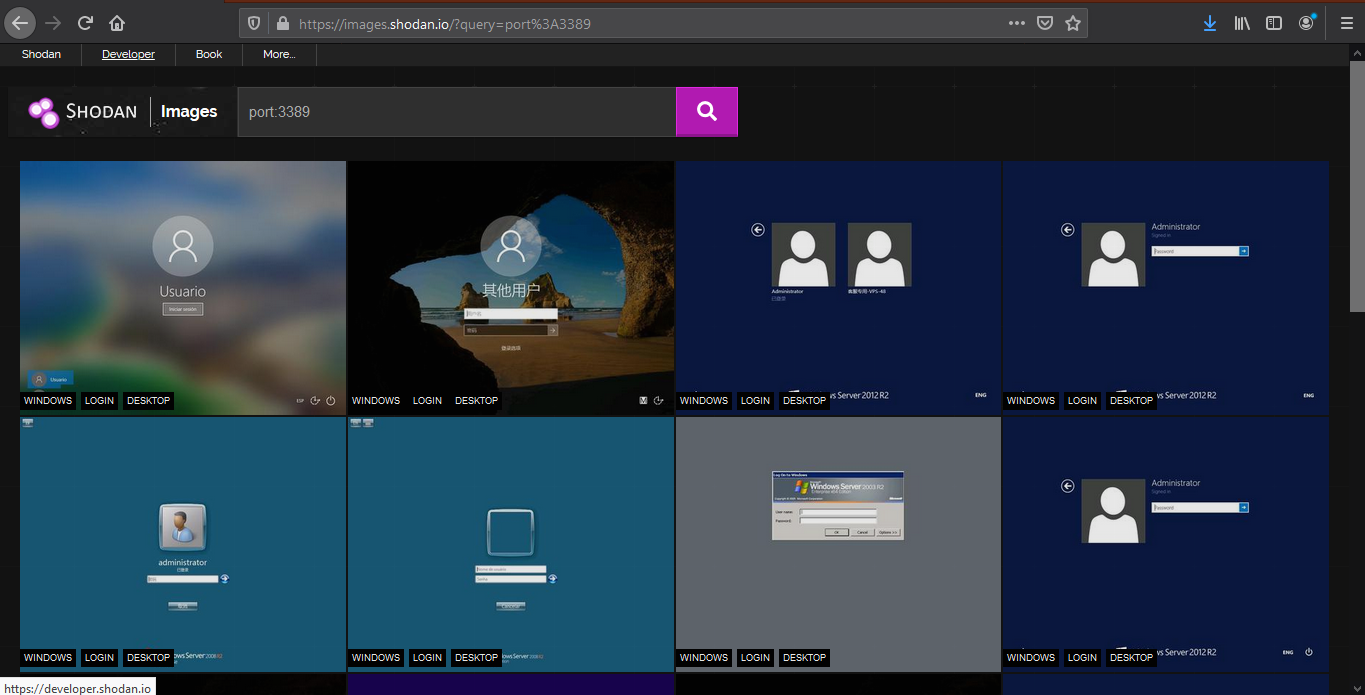
Shodan images
It helps display screenshot or images captured (https://images.shodan.io/). Image data is gathered from 5 different sources: VNC, Remote Desktop (RDP), RTSP, Webcams and X Windows.
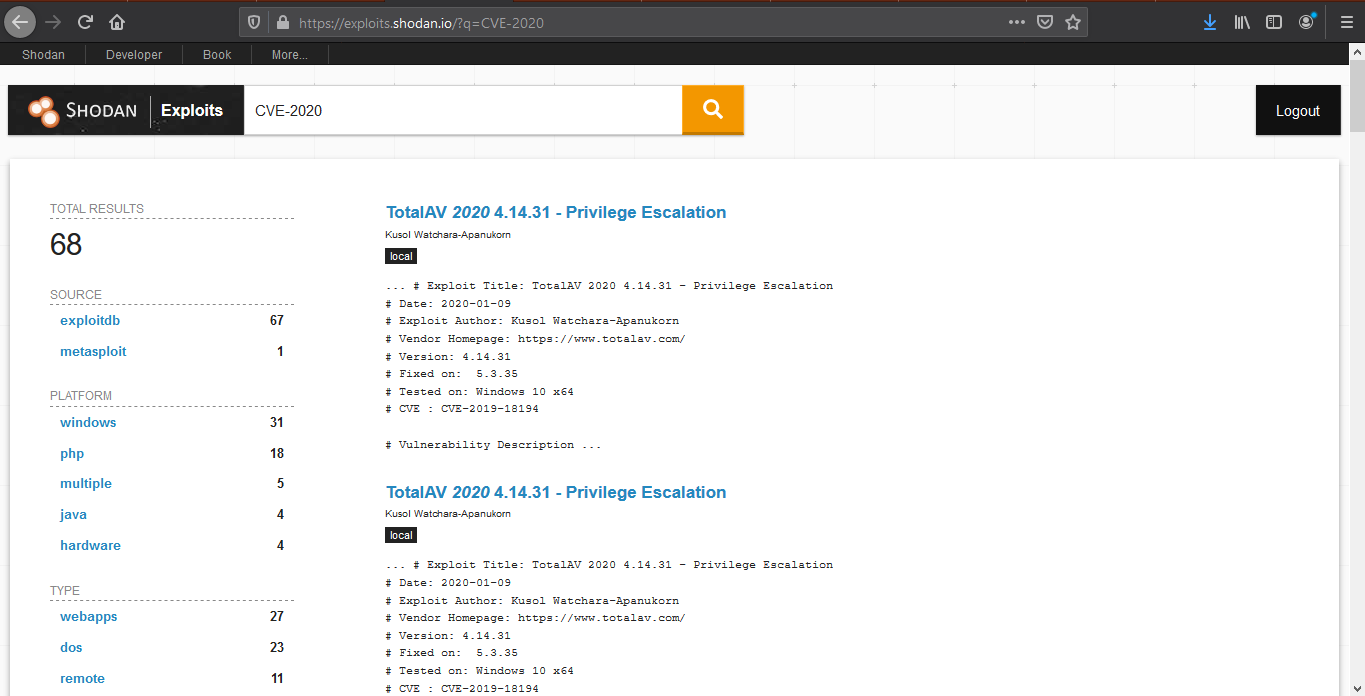
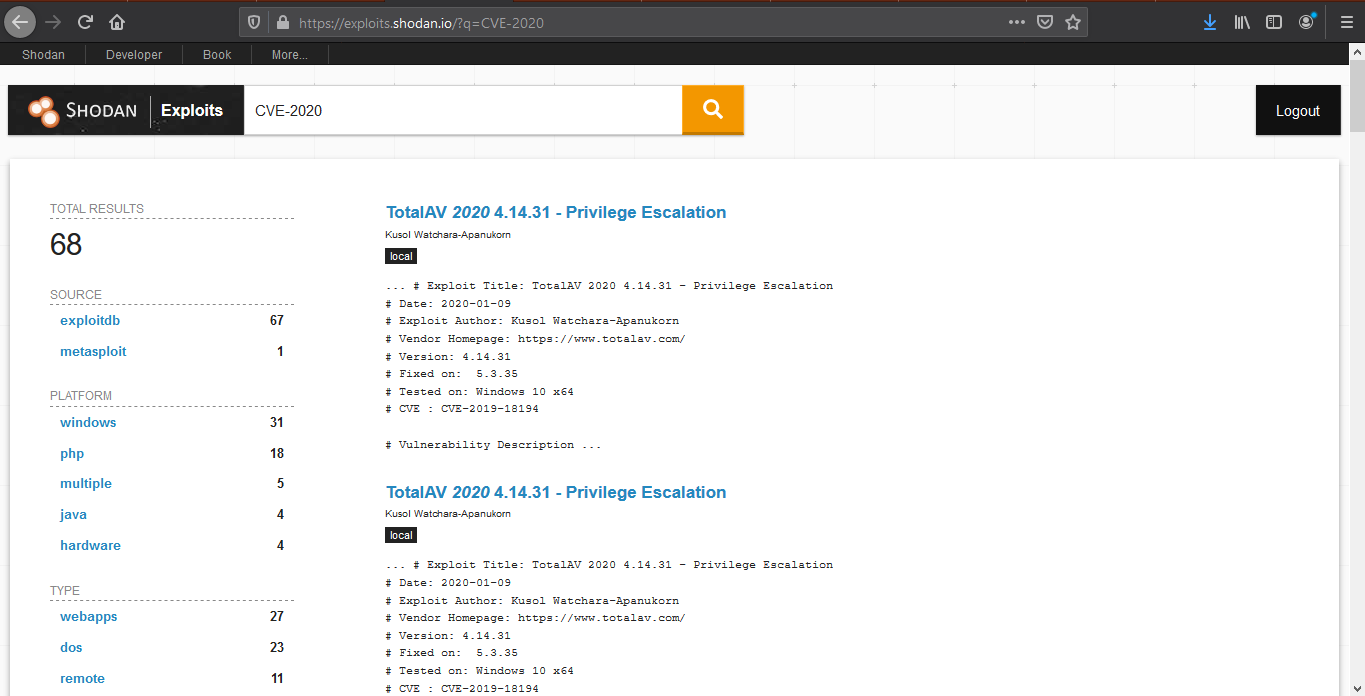
Exploit search
Basic exploit search within the database (https://exploits.shodan.io/)
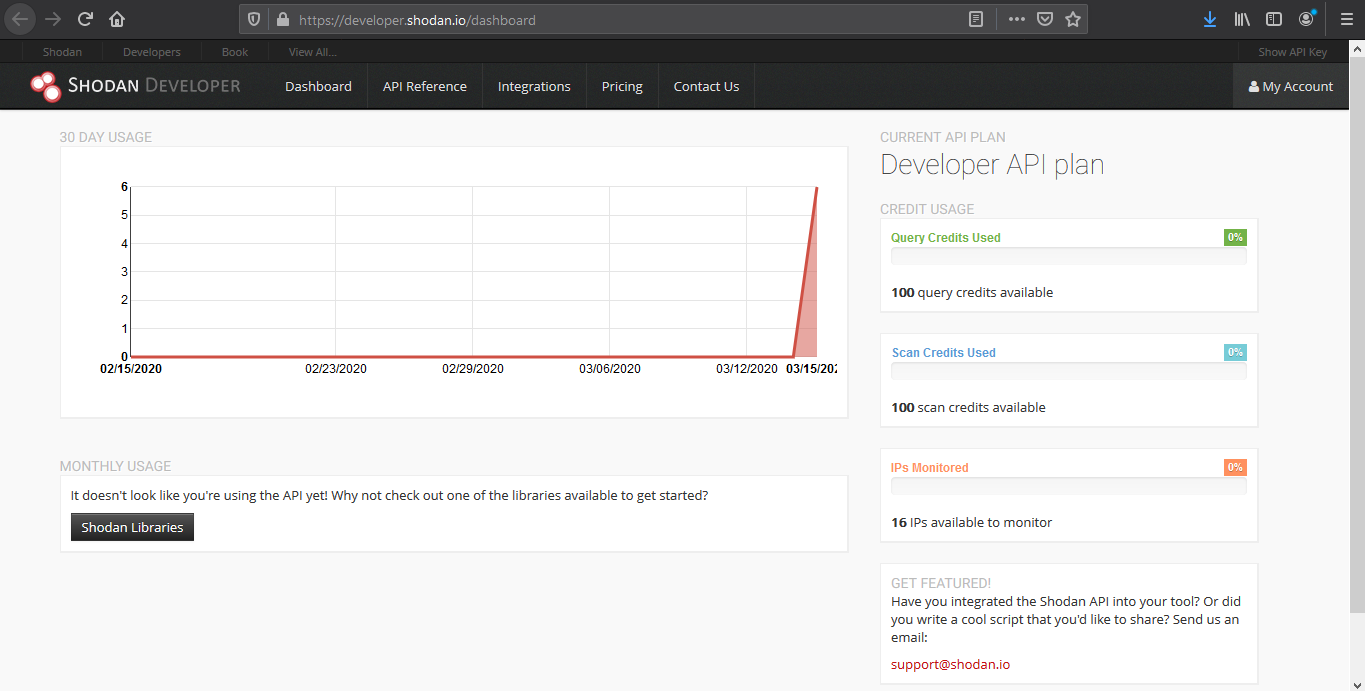
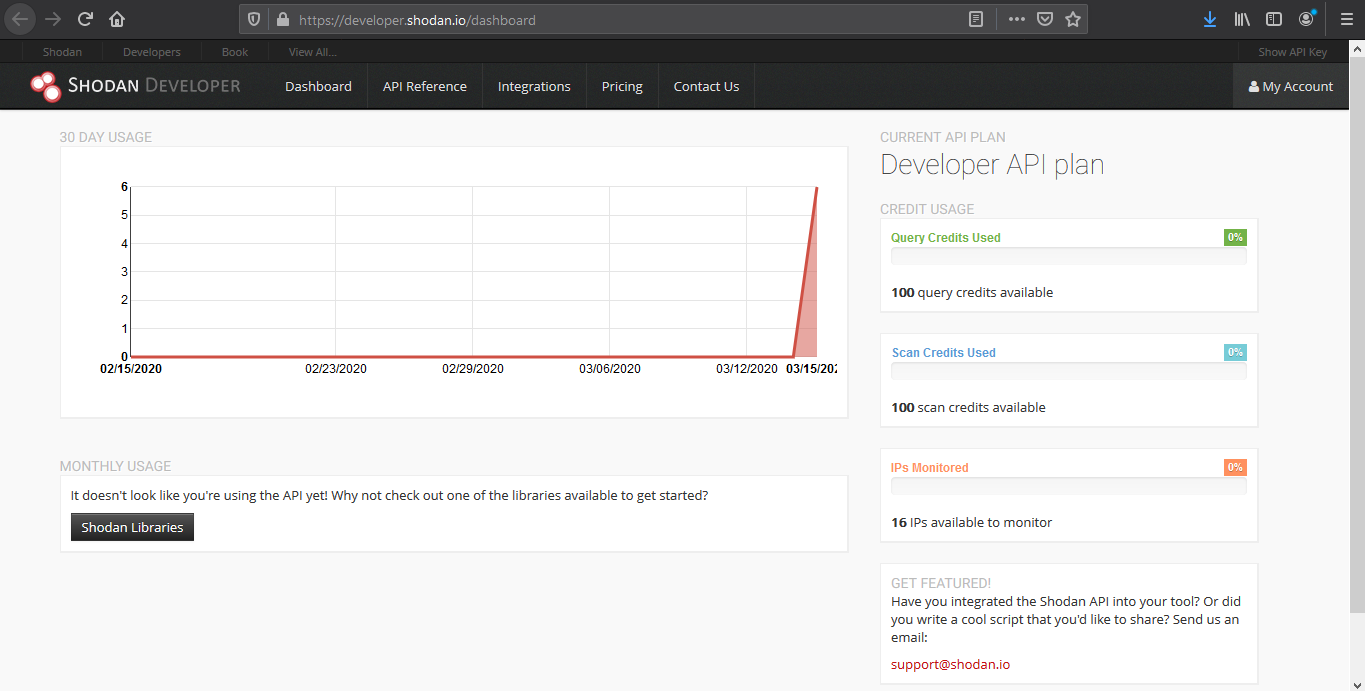
View API stats
This tool shows details about your API usage (https://developer.shodan.io/dashboard)
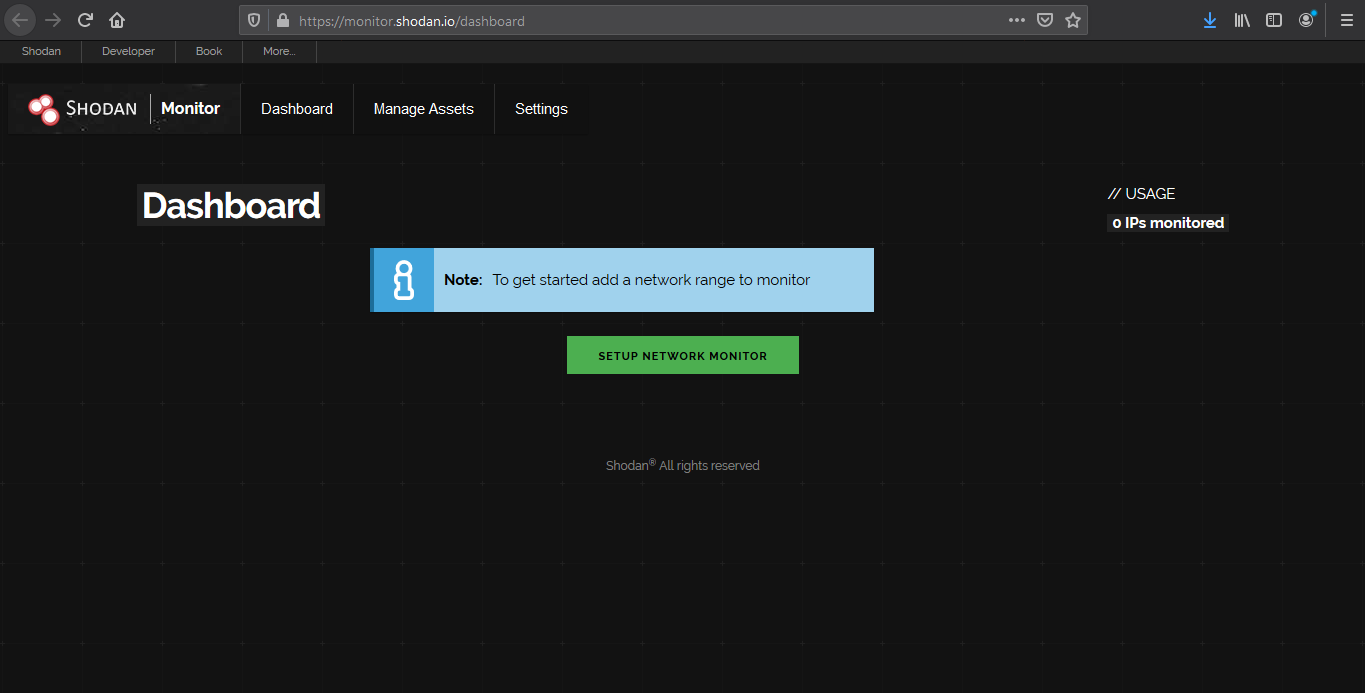
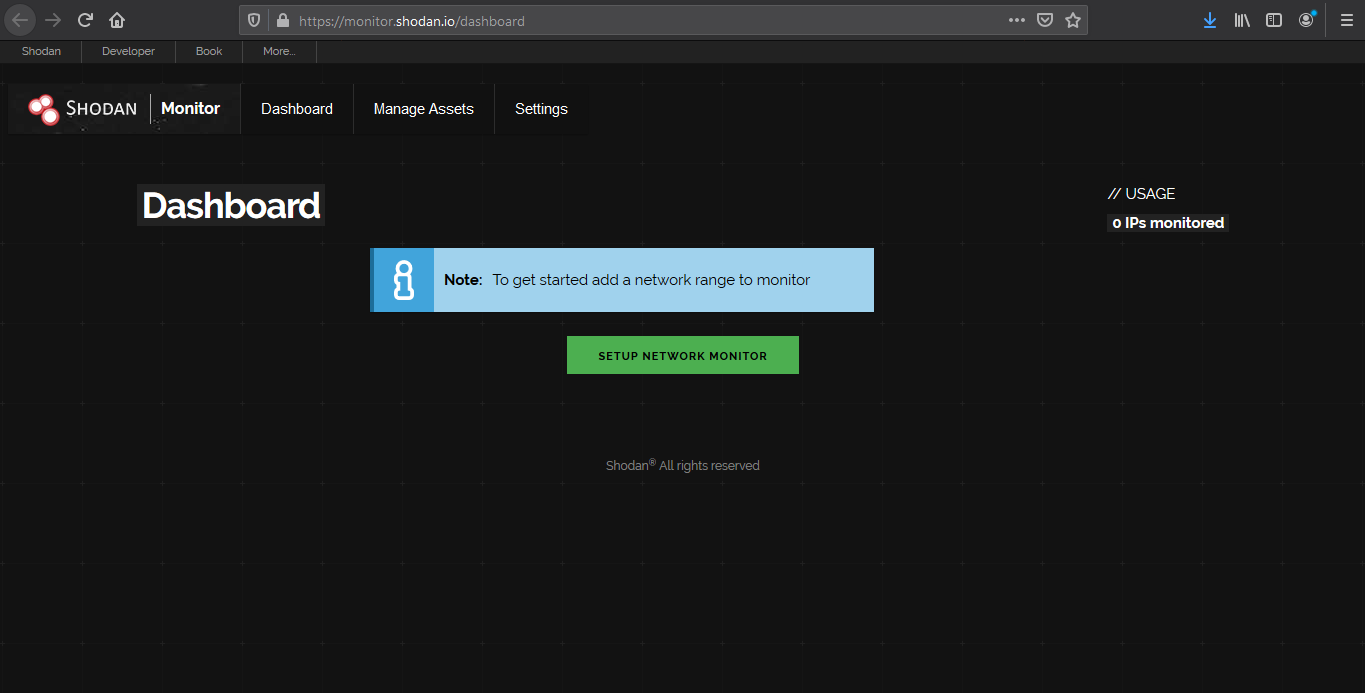
Network monitor
Keep track of the devices that you have exposed to the Internet. Setup notifications, launch scans and gain complete visibility into what you have connected. (https://monitor.shodan.io/dashboard)
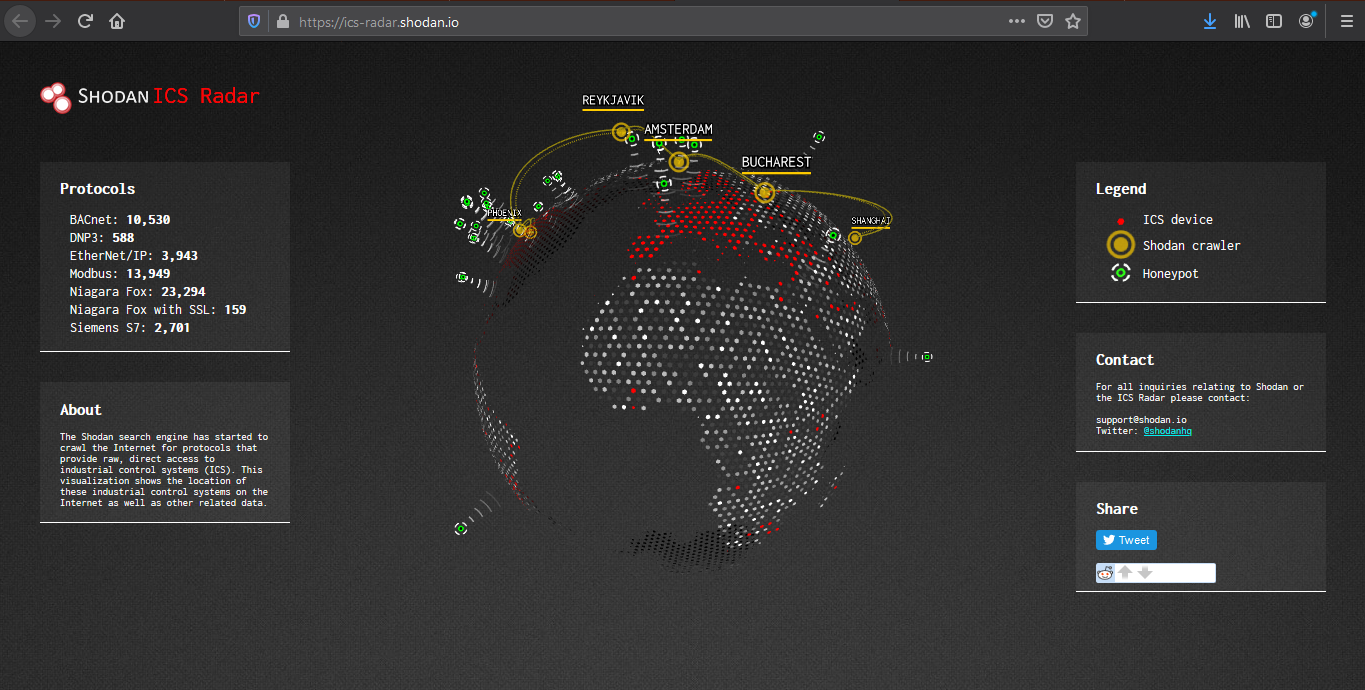
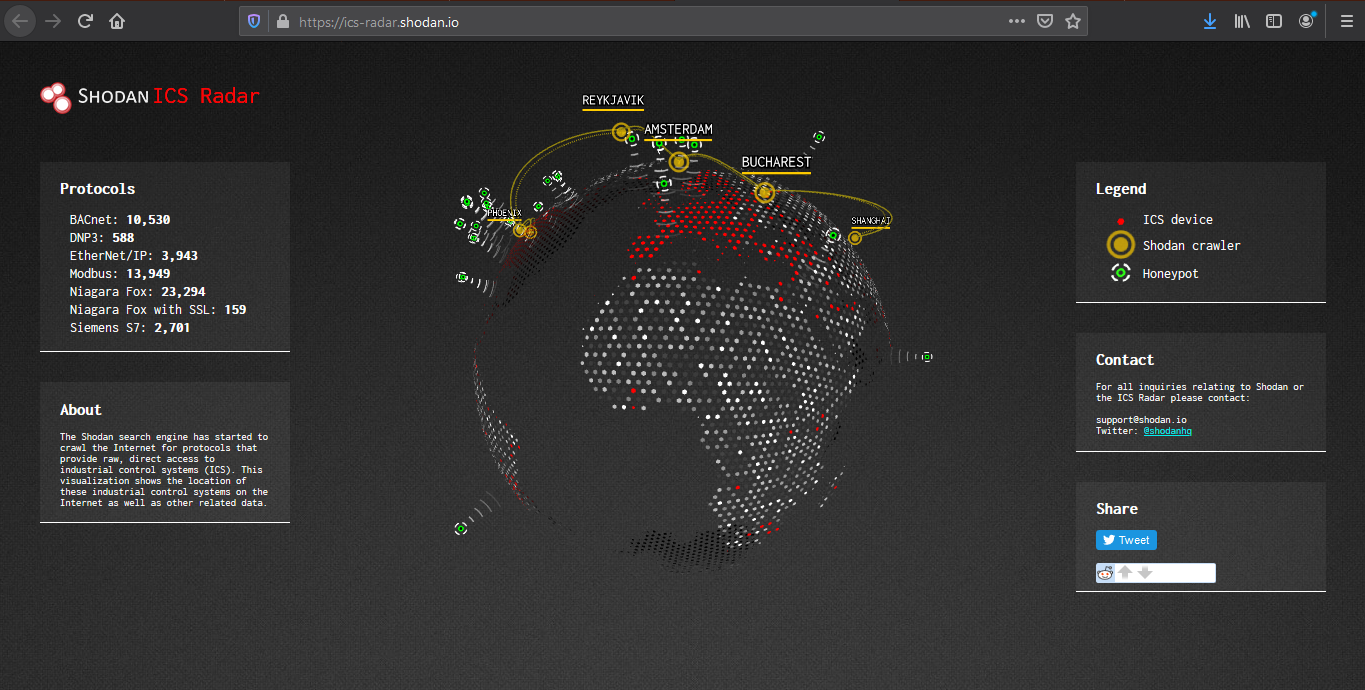
ICS radar
ICS Radar is a 3D map of Industrial Control Systems (ICS) devices found by Shodan crawlers. (https://ics-radar.shodan.io/)
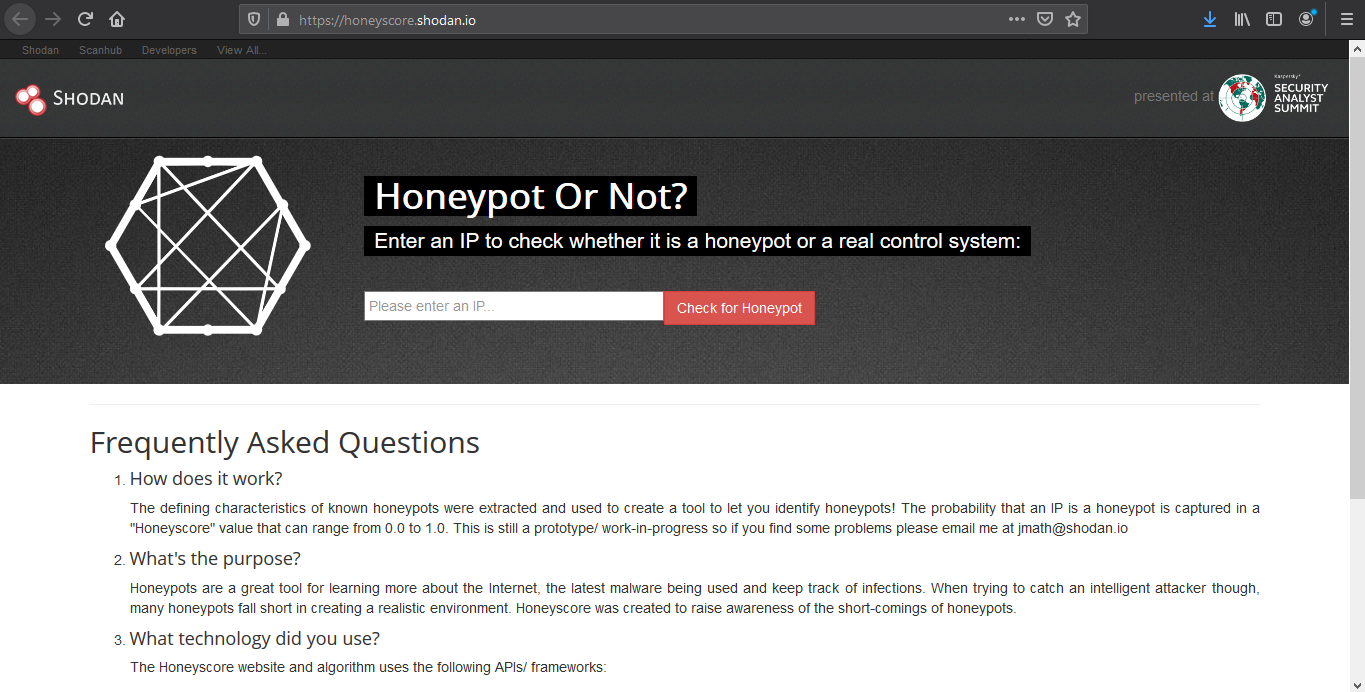
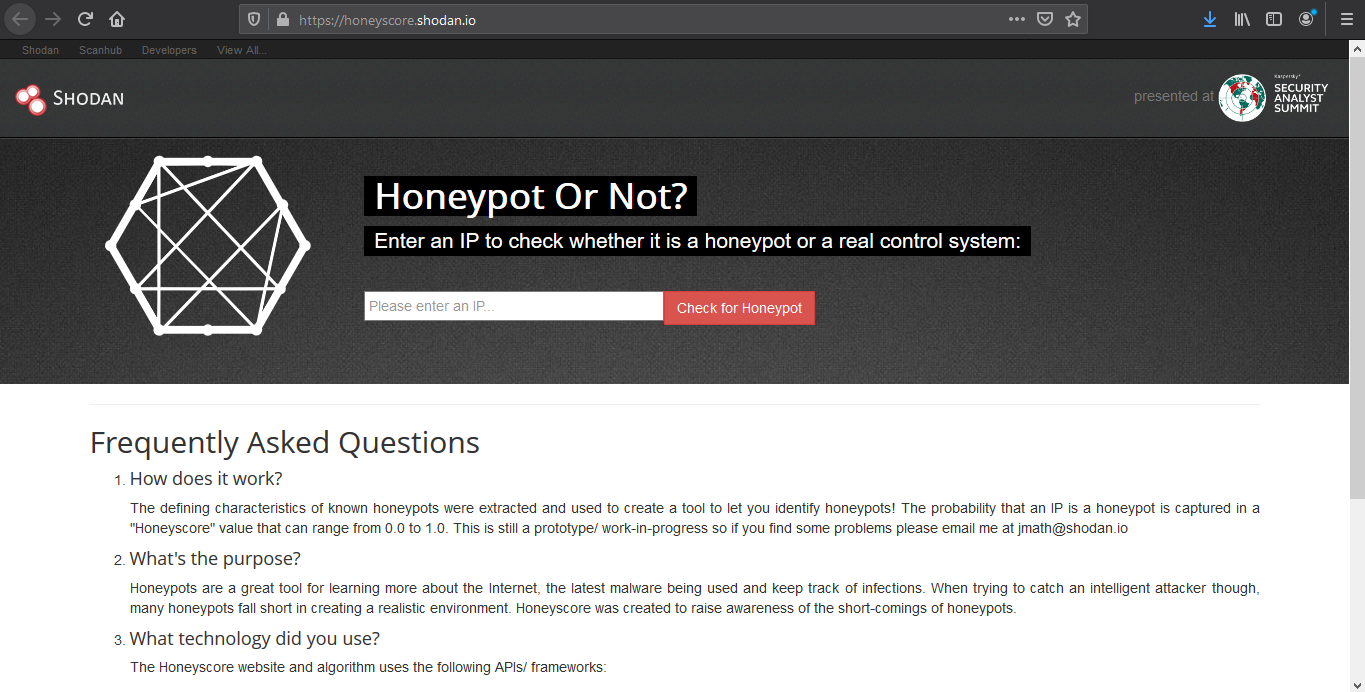
Honeypot score
The service called Honeypot or not? will attribute a Honeyscore to an IP address, a probability of being a honeypot. (https://honeyscore.shodan.io/)
Useful Shodan queries
https://github.com/jakejarvis/awesome-shodan-queries
https://beta.shodan.io/search/filters
Industrial Control Systems
Samsung Electronic Billboards
- “Server: Prismview Player”
Gas Station Pump Controllers
- “in-tank inventory” port:10001
Automatic License Plate Readers
Traffic Light Controllers / Red Light Cameras
Voting Machines in the United States
Telcos Running Cisco Lawful Intercept Wiretaps
- “Cisco IOS” “ADVIPSERVICESK9_LI-M”
Prison Pay Phones
- “[2J[H Encartele Confidential”
Tesla PowerPack Charging Status
- http.title:”Tesla PowerPack System” http.component:”d3″ -ga3ca4f2
Electric Vehicle Chargers
- “Server: gSOAP/2.8” “Content-Length: 583”
Maritime Satellites
- “Cobham SATCOM” OR (“Sailor” “VSAT”)
Submarine Mission Control Dashboards
- title:”Slocum Fleet Mission Control”
CAREL PlantVisor Refrigeration Units
- “Server: CarelDataServer” “200 Document follows”
Nordex Wind Turbine Farms
- http.title:”Nordex Control”
- “Jetty/3.1 (JSP 1.1; Servlet 2.2; java 1.6.0_14)”
C4 Max Commercial Vehicle GPS Trackers
- “[1m[35mWelcome on console”
DICOM Medical X-Ray Machines
- “DICOM Server Response” port:104
GaugeTech Electricity Meters
- “Server: EIG Embedded Web Server” “200 Document follows”
Siemens Industrial Automation
- “Siemens, SIMATIC” port:161
Siemens HVAC Controllers
- “Server: Microsoft-WinCE” “Content-Length: 12581”
Door / Lock Access Controllers
Railroad Management
- “log off” “select the appropriate”
Remote Desktop
Unprotected VNC
- “authentication disabled” “RFB 003.008”
Windows RDP
“\x03\x00\x00\x0b\x06\xd0\x00\x00\x124\x00”
Network Infrastructure
MongoDB
- “MongoDB Server Information” port:27017 -authentication
- “Set-Cookie: mongo-express=” “200 OK”
- “Home – Mongo Express”
- all:”mongodb server information” all:”metrics”
Jenkins CI
- “X-Jenkins” “Set-Cookie: JSESSIONID” http.title:”Dashboard”
Docker APIs
- “Docker Containers:” port:2375
Pi-hole Open DNS Servers
- “dnsmasq-pi-hole” “Recursion: enabled”
Already Logged-In as root via Telnet
- “root@” port:23 -login -password -name -Session
Android Root Bridges
- “Android Debug Bridge” “Device” port:5555
Lantronix Serial-to-Ethernet Adapter Leaking Telnet Passwords
- Lantronix password port:30718 -secured
Citrix Virtual Apps
- “Citrix Applications:” port:1604
Cisco Smart Install
- “smart install client active”
PBX IP Phone Gateways
- PBX “gateway console” -password port:23
Polycom Video Conferencing
- http.title:”- Polycom” “Server: lighttpd”
Telnet Configuration:
- “Polycom Command Shell” -failed port:23
Bomgar Help Desk Portal
- “Server: Bomgar” “200 OK”
Intel Active Management CVE-2017-5689
- “Intel(R) Active Management Technology” port:623,664,16992,16993,16994,16995
HP iLO 4 CVE-2017-12542
- HP-ILO-4 !”HP-ILO-4/2.53″ !”HP-ILO-4/2.54″ !”HP-ILO-4/2.55″ !”HP-ILO-4/2.60″ !”HP-ILO-4/2.61″ !”HP-ILO-4/2.62″ !”HP-iLO-4/2.70″ port:1900
Outlook Web Access
Exchange 2007
- “x-owa-version” “IE=EmulateIE7”
Exchange 2010
- “x-owa-version” “IE=EmulateIE7” http.favicon.hash:442749392
Exchange 2013 / 2016
- “X-AspNet-Version” http.title:”Outlook” -“x-owa-version”
Lync / Skype for Business
Network Attached Storage (NAS)
SMB (Samba) File Shares
- “Authentication: disabled” port:445
Specifically domain controllers:
- “Authentication: disabled” NETLOGON SYSVOL -unix port:445
FTP Servers with Anonymous Login
- “220” “230 Login successful.” port:21
Iomega / LenovoEMC NAS Drives
- “Set-Cookie: iomega=” -“manage/login.html” -http.title:”Log In”
Buffalo TeraStation NAS Drives
- Redirecting sencha port:9000
Logitech Media Servers
- “Server: Logitech Media Server” “200 OK”
Plex Media Servers
- “X-Plex-Protocol” “200 OK” port:32400
Tautulli / PlexPy Dashboards
FTP
- “230 login successful” port:”21″
- “Anonymous+access+allowed” connected
- Anonymous+access+allowed
Webcams
Yawcams
- “Server: yawcam” “Mime-Type: text/html”
webcamXP/webcam7
- (“webcam 7” OR “webcamXP”) http.component:”mootools” -401
SQWebcam
Android IP Webcam Server
- “Server: IP Webcam Server” “200 OK”
Canon
- title:”Network Camera VB-M600″ 200 ok server: vb
Security DVRs
d-link
- d-Link Internet Camera, 200 OK
- “Default Login” Authenticate
Printers & Copiers
HP Printers
- “Serial Number:” “Built:” “Server: HP HTTP”
- HP LaserJet 4250
Xerox Copiers/Printers
Epson Printers
- “SERVER: EPSON_Linux UPnP” “200 OK”
- “Server: EPSON-HTTP” “200 OK”
Canon Printers
- “Server: KS_HTTP” “200 OK”
- “Server: CANON HTTP Server”
Home Devices
Yamaha Stereos
- “Server: AV_Receiver” “HTTP/1.1 406”
Apple AirPlay Receivers, Apple TVs, HomePods, etc.
Chromecasts / Smart TVs
Crestron Smart Home Controllers
Random Stuff
OctoPrint 3D Printer Controllers
- title:”OctoPrint” -title:”Login” http.favicon.hash:1307375944
Etherium Miners
Apache Directory Listings
- http.title:”Index of /” http.html:”.pem”
Too Many Minecraft Servers
- “Minecraft Server” “protocol 340” port:25565
NetBotz (net monitoring tool)
- title:”netbotz appliance”
Scada
- EIG Embedded Web Server
- title:”RAKO Bridge Control Panel”
Vulnerabilities
OOB
- ”Active Management Technology”
by Vry4n_ | Feb 15, 2020 | Active Gathering
Finger is primarily used to enumerate user information on the target system. It can also find out detailed information (if exists) such as full name, email address, phone number etc. of all its users.
Nmap result

finger-user-enum
finger-user-enum is a script used to enumerate users
https://github.com/pentestmonkey/finger-user-enum
Username guessing tool primarily for use against the default Solaris finger service.
Installation
- git clone https://github.com/pentestmonkey/finger-user-enum.git
- ls -l finger-user-enum

Using finger-user-enum
1. Displaying help
- perl finger-user-enum.pl -h

2. enumerate a single user
-u = user
-t = host IP
- perl finger-user-enum.pl -u root -t 10.10.10.76

We can see output of root user, it means the user exists (1 result). On the other hand, the screenshot below would show (0 results).
- perl finger-user-enum.pl -u vry4n -t 10.10.10.76

3. Enumerate users using a list
- perl finger-user-enum.pl -U /usr/share/seclists/Usernames/Names/names.txt -t 10.10.10.76

4. Using a list of IPs
- perl finger-user-enum.pl -U /usr/share/seclists/Usernames/Names/names.txt -T IP_list.txt
5. Using another port than default 79
- perl finger-user-enum.pl -p 8000 -U /usr/share/seclists/Usernames/Names/names.txt -t 10.10.10.76
6. Showing detailed output
- perl finger-user-enum.pl -d -u root -t 10.10.10.76

Metasploit
1. Metasploit has a module for finger scan (auxiliary/scanner/finger/finger_users)
- use auxiliary/scanner/finger/finger_users
- show options
- set RHOSTS 10.10.10.76
- set USERS_FILE /usr/share/seclists/Usernames/Names/names.txt
- exploit

Using finger
Finger is a tool used to enumerate users using port 79. Finger may be used to look up users on a remote machine. The format is to specify a user as “user@host”, or “@host”
1. Display man page for help

2. enumerate a known user. In this case root
- finger -s root@10.10.10.76

3. Show the home directory of the user
- finger -sl root@10.10.10.76

4. Preventing the -l option from displaying the contents of the “.plan”, “.project” and “.pgpkey” files.
- finger -slp sammy@10.10.10.76

by Vry4n_ | Dec 10, 2019 | Active Gathering
Dig stands for (Domain Information Groper). Dig is a network administration command-line tool for querying Domain Name System (DNS) name servers. It is useful for verifying and troubleshooting DNS problems and also to perform DNS lookups and displays the answers that are returned from the name server that were queried. dig is part of the BIND domain name server software suite. dig command replaces older tool such as nslookup and the host. dig tool is available in major Linux distributions.
Install Dig on Linux
Debian
CentOS 7
Dig Syntax
In its simplest form, the syntax of the dig utility will look like this:
- dig [server] [name] [type]
[server] – the IP address or hostname of the name server to query
If the server argument is the hostname then dig will resolve the hostname before proceeding with querying the name server.
It is optional and if you don’t provide a server argument then dig uses the name server listed in /etc/resolv.conf
[name] – the name of the resource record that is to be looked up
[type] – the type of query requested by dig. For example, it can be an A record, MX record, SOA record or any other types. By default dig performs a lookup for an A record if no type argument is specified.
Queries
Dig Commands Cheatsheet
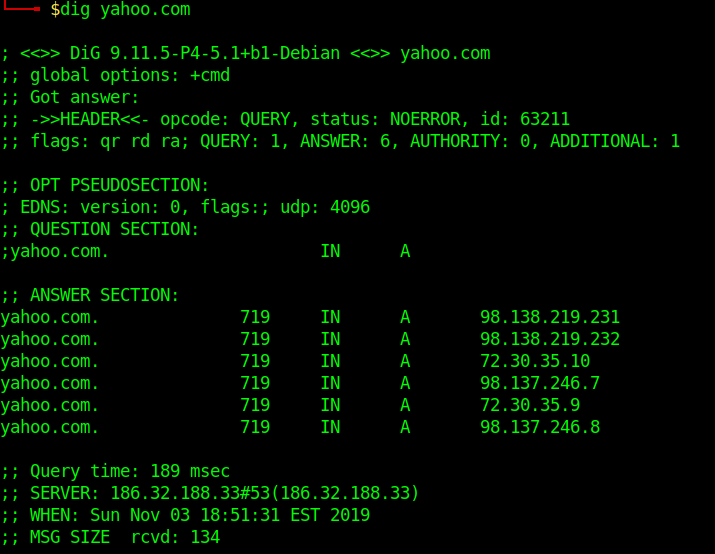
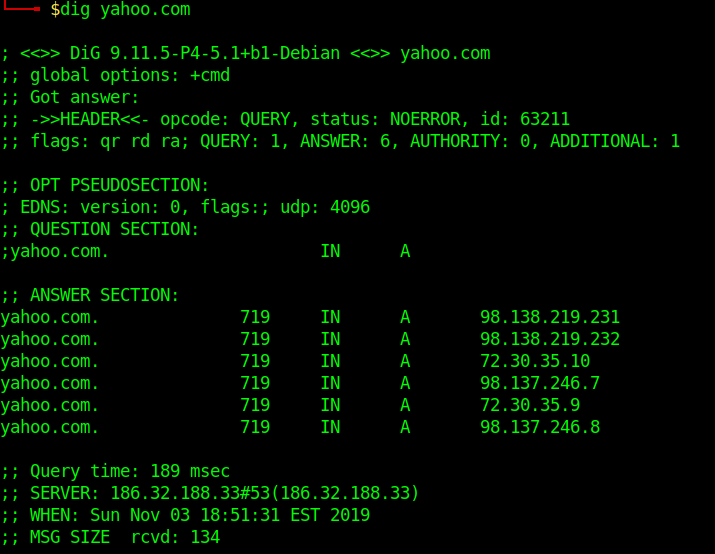
Dig a Domain Name
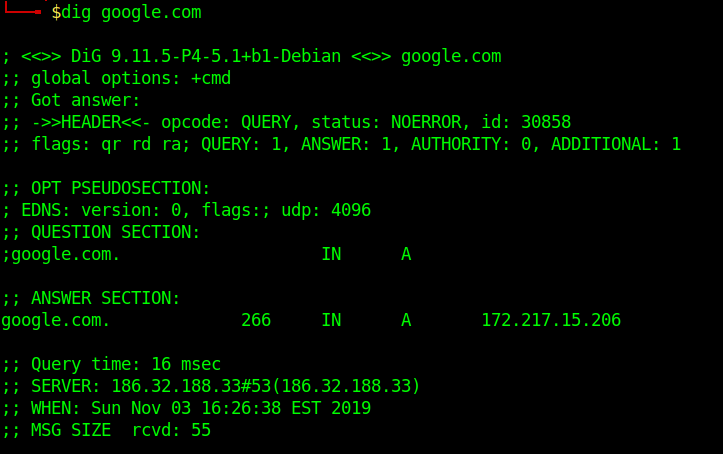
UNDERSTAND THE OUTPUT:
- Lines beginning with ; are comments not part of the information.
- The first line tell us the version of dig (9.11.5) command.
- Next, dig shows the header of the response it received from the DNS server
- Next comes the question section, which simply tells us the query, which in this case is a query for the “A” record of yahoo.com. The IN means this is an Internet lookup (in the Internet class).
- The answer section tells us that yahoo.com has the IP address 72.30.38.140
- Lastly there are some stats about the query. You can turn off these stats using the +nostats option.
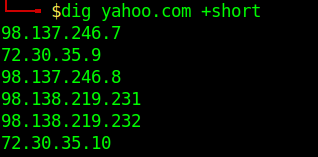
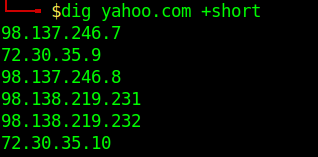
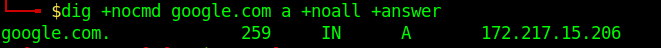
Short Answers
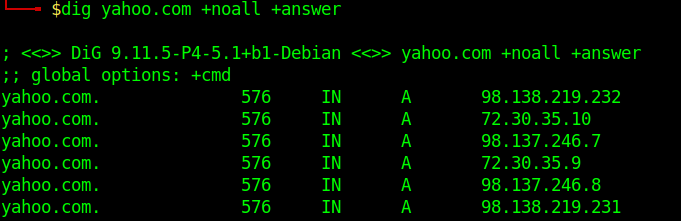
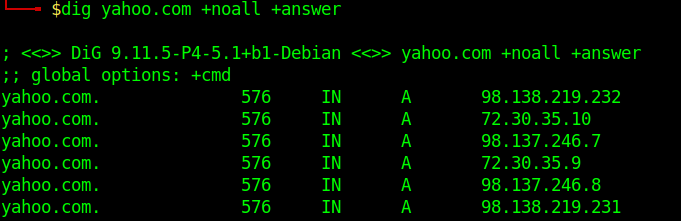
Detailed Answers
- dig yahoo.com +noall +answer
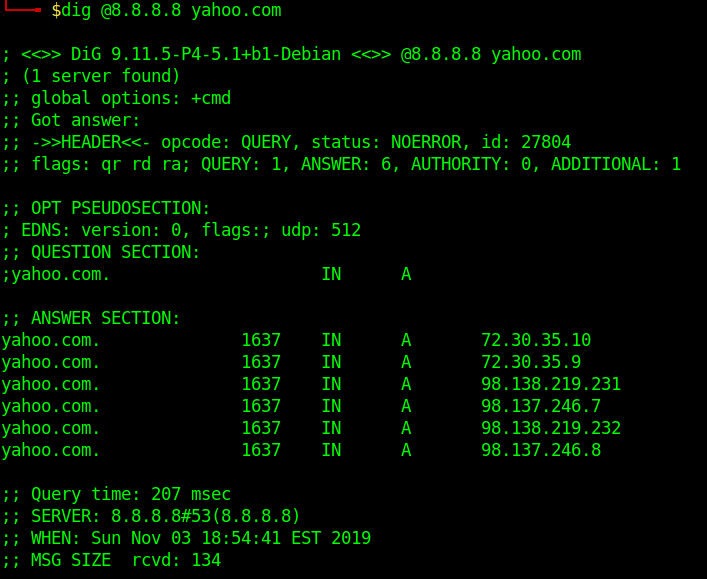
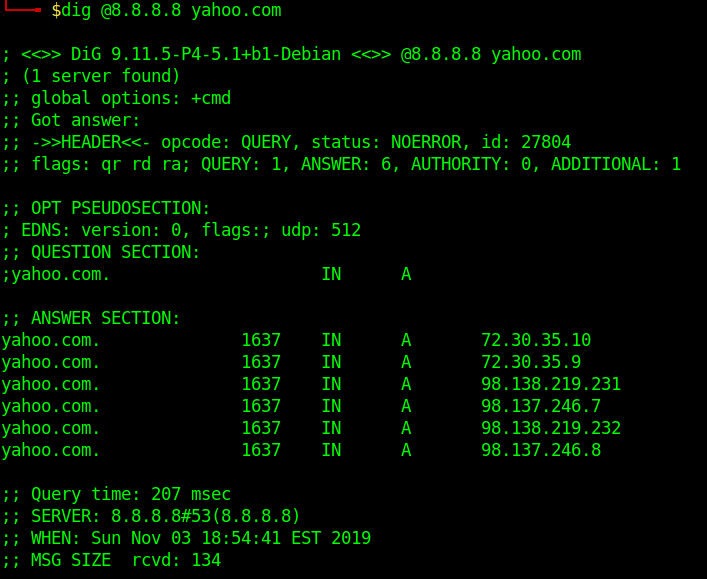
Specifying Nameservers
The following dig command sends the DNS query to Google’s name server(8.8.8.8) by using the @8.8.8.8 option
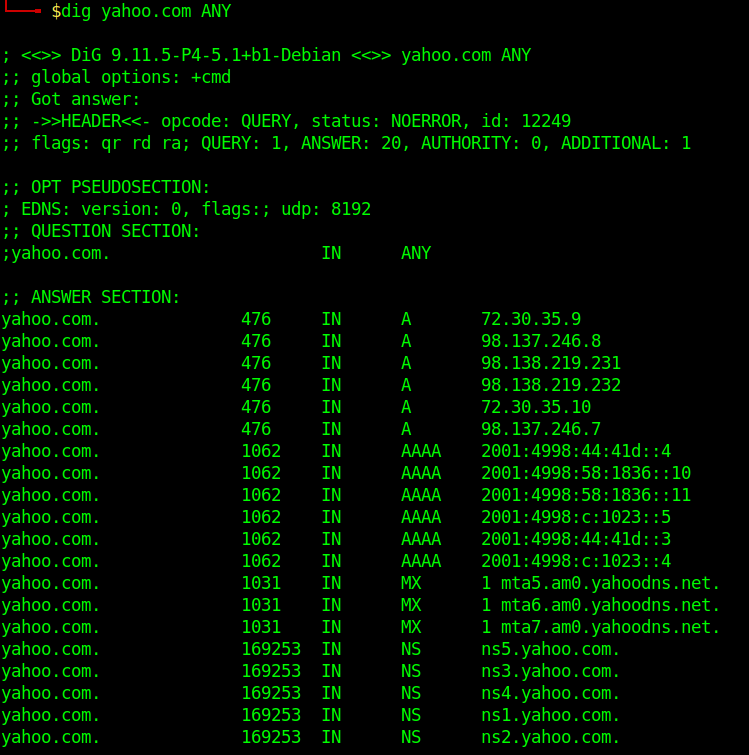
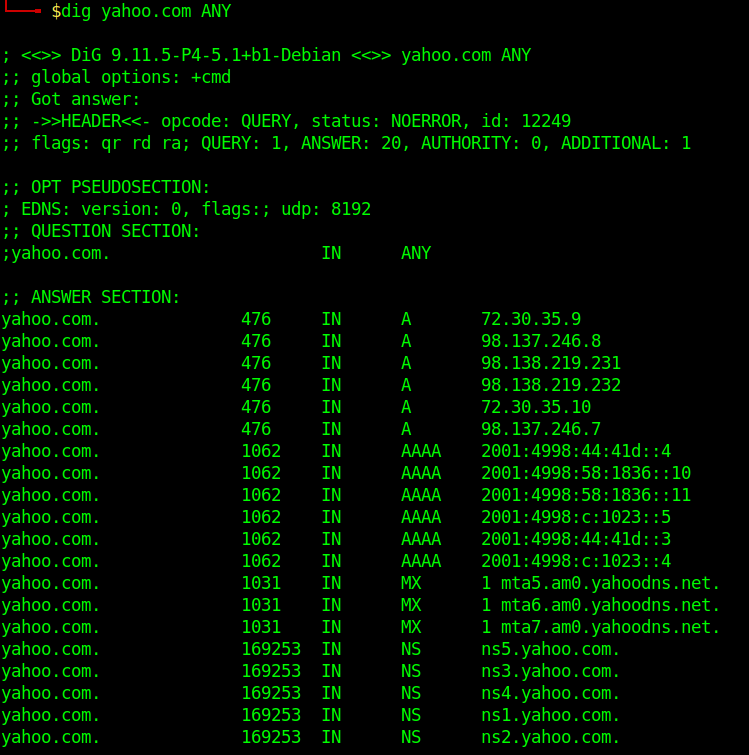
Query All DNS Record Types
Search For Record Type
- dig yahoo.com MX
- dig yahoo.com NS
- dig yahoo.com A
- dig yahoo.com SOA
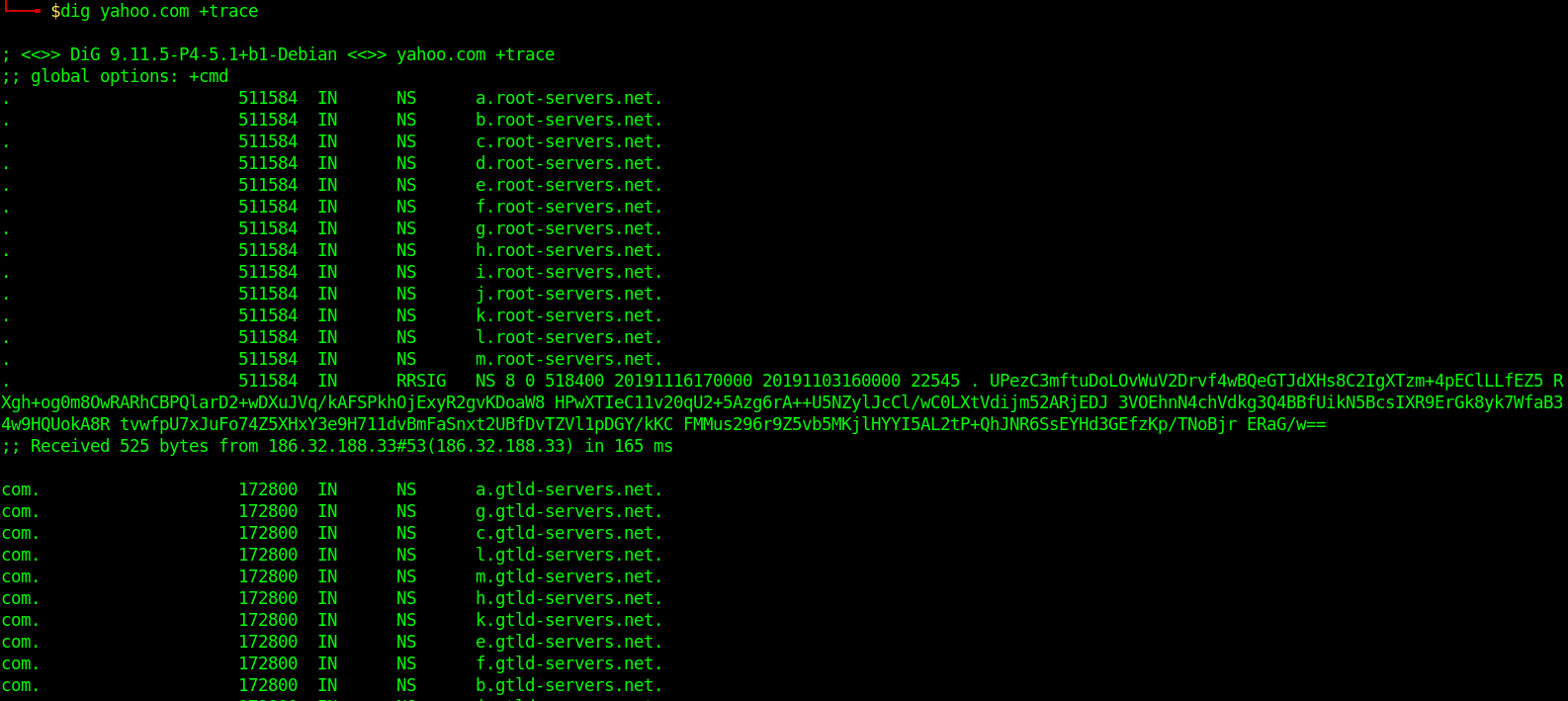
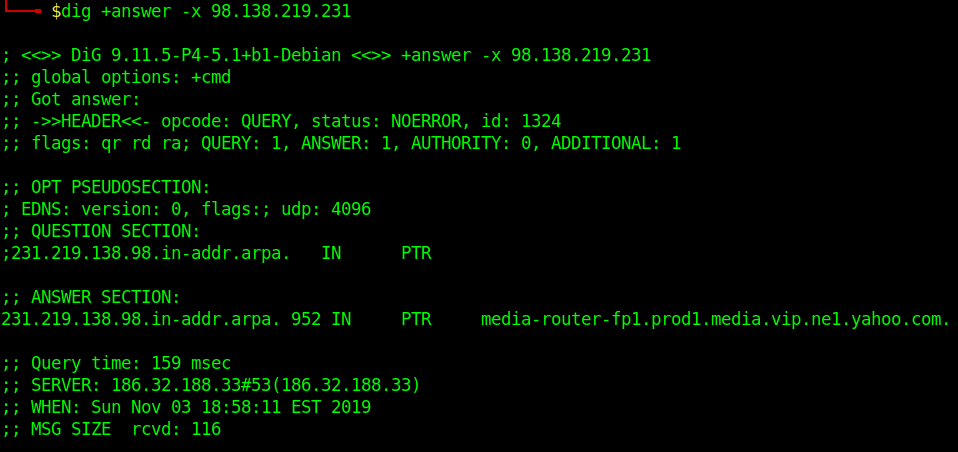
Trace DNS Path
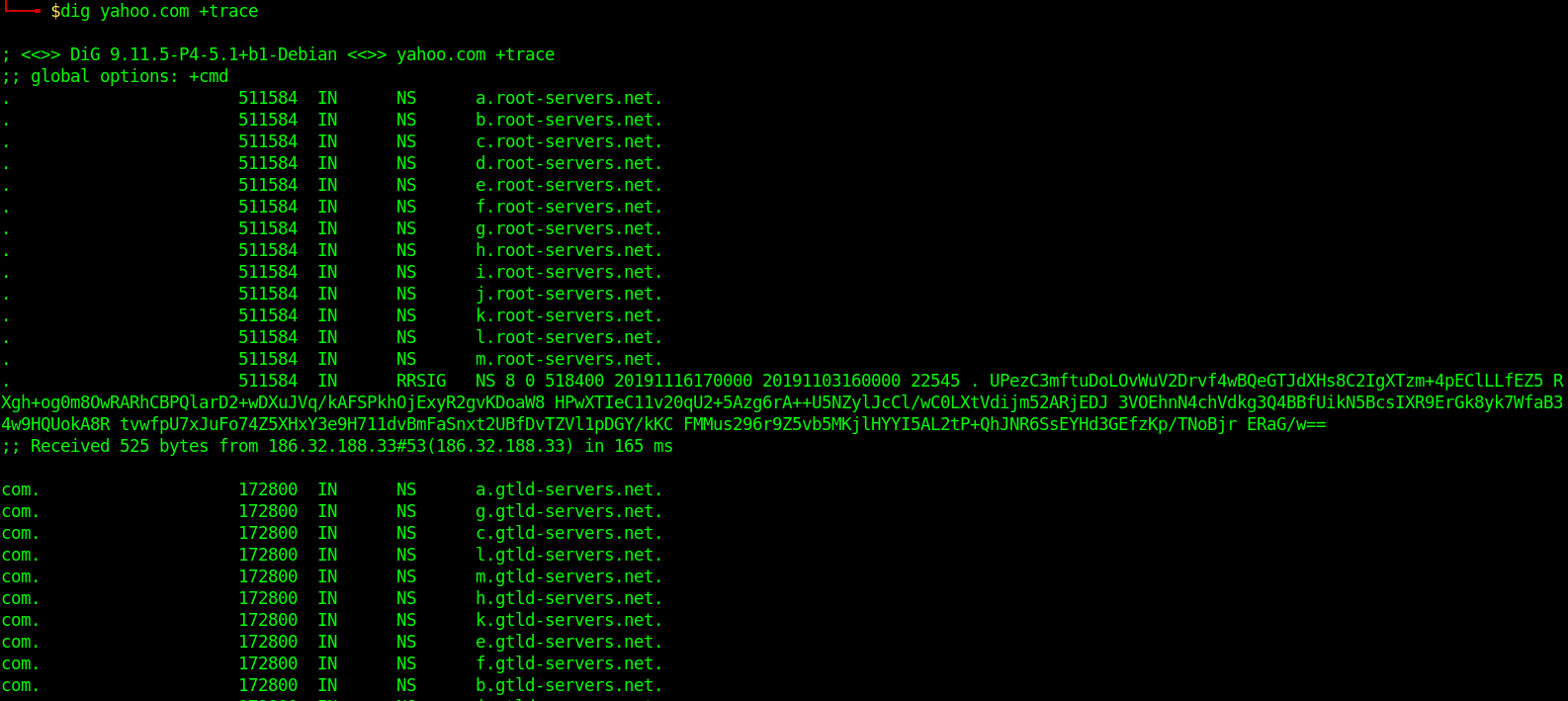
Reverse DNS Lookup
- dig +answer -x 98.138.219.231
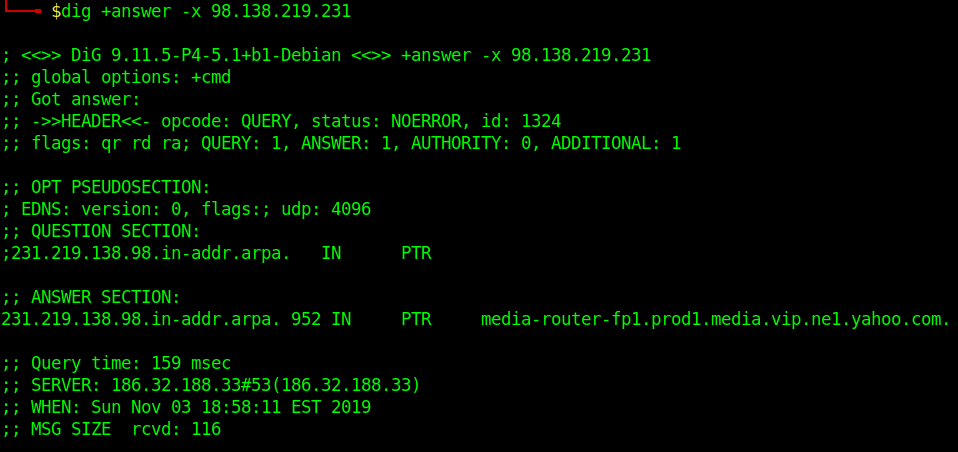
Reverse DNS lookup lets you look up the domain and hostname associated with an IP address.
Batch Queries
- dig -f domain_name.txt +short
provide dig with a list of domain names – one per line in a file
Custom Query
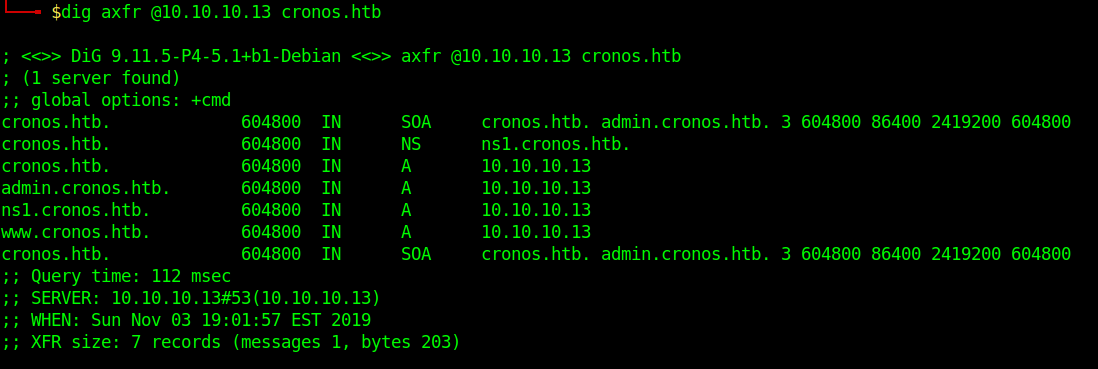
- dig axfr @10.10.10.13 cronos.htb
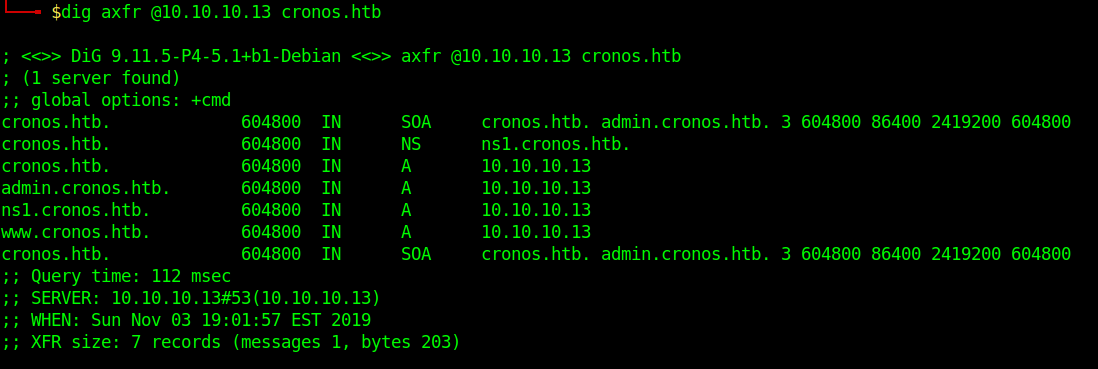
Those different domains in the output point to the same IP.
by Vry4n_ | Dec 2, 2019 | Active Gathering
Here you have a list of Linux Interesting files. They can be used to extract sensitive information leading to further exploitation.
It is always important to read the Administrator Guide of any application and appli the best security practices to configiguration file.
Any misconfiguration is a potential vector of attack.
• /etc/passwd
• /etc/shadow
• /etc/aliases
• /etc/anacrontab
• /etc/apache2/apache2.conf
• /etc/apache2/httpd.conf
• /etc/at.allow
• /etc/at.deny
• /etc/bashrc
• /etc/bootptab
• /etc/chrootUsers
• /etc/chttp.conf
• /etc/cron.allow
• /etc/cron.deny
• /etc/crontab
• /etc/cups/cupsd.conf
• /etc/exports
• /etc/fstab
• /etc/ftpaccess
• /etc/ftpchroot
• /etc/ftphosts
• /etc/groups
• /etc/grub.conf
• /etc/hosts
• /etc/hosts.allow
• /etc/hosts.deny
• /etc/httpd/access.conf
• /etc/httpd/conf/httpd.conf
• /etc/httpd/httpd.conf
• /etc/httpd/logs/access_log
• /etc/httpd/logs/access.log
• /etc/httpd/logs/error_log
• /etc/httpd/logs/error.log
• /etc/httpd/php.ini
• /etc/httpd/srm.conf
• /etc/inetd.conf
• /etc/inittab
• /etc/issue
• /etc/lighttpd.conf
• /etc/lilo.conf
• /etc/logrotate.d/ftp
• /etc/logrotate.d/proftpd
• /etc/logrotate.d/vsftpd.log
• /etc/lsb-release
• /etc/motd
• /etc/modules.conf
• /etc/motd
• /etc/mtab
• /etc/my.cnf
• /etc/my.conf
• /etc/mysql/my.cnf
• /etc/network/interfaces
• /etc/networks
• /etc/npasswd
• /etc/passwd
• /etc/php4.4/fcgi/php.ini
• /etc/php4/apache2/php.ini
• /etc/php4/apache/php.ini
• /etc/php4/cgi/php.ini
• /etc/php4/apache2/php.ini
• /etc/php5/apache2/php.ini
• /etc/php5/apache/php.ini
• /etc/php/apache2/php.ini
• /etc/php/apache/php.ini
• /etc/php/cgi/php.ini
• /etc/php.ini
• /etc/php/php4/php.ini
• /etc/php/php.ini
• /etc/printcap
• /etc/profile
• /etc/proftp.conf
• /etc/proftpd/proftpd.conf
• /etc/pure-ftpd.conf
• /etc/pureftpd.passwd
• /etc/pureftpd.pdb
• /etc/pure-ftpd/pure-ftpd.conf
• /etc/pure-ftpd/pure-ftpd.pdb
• /etc/pure-ftpd/putreftpd.pdb
• /etc/redhat-release
• /etc/resolv.conf
• /etc/samba/smb.conf
• /etc/snmpd.conf
• /etc/ssh/ssh_config
• /etc/ssh/sshd_config
• /etc/ssh/ssh_host_dsa_key
• /etc/ssh/ssh_host_dsa_key.pub
• /etc/ssh/ssh_host_key
• /etc/ssh/ssh_host_key.pub
• /etc/sysconfig/network
• /etc/syslog.conf
• /etc/termcap
• /etc/vhcs2/proftpd/proftpd.conf
• /etc/vsftpd.chroot_list
• /etc/vsftpd.conf
• /etc/vsftpd/vsftpd.conf
• /etc/wu-ftpd/ftpaccess
• /etc/wu-ftpd/ftphosts
• /etc/wu-ftpd/ftpusers
• /logs/pure-ftpd.log
• /logs/security_debug_log
• /logs/security_log
• /opt/lampp/etc/httpd.conf
• /opt/xampp/etc/php.ini
• /proc/cpuinfo
• /proc/filesystems
• /proc/interrupts
• /proc/ioports
• /proc/meminfo
• /proc/modules
• /proc/mounts
• /proc/stat
• /proc/swaps
• /proc/version
• /proc/self/net/arp
• /root/anaconda-ks.cfg
• /usr/etc/pure-ftpd.conf
• /usr/lib/php.ini
• /usr/lib/php/php.ini
• /usr/local/apache/conf/modsec.conf
• /usr/local/apache/conf/php.ini
• /usr/local/apache/log
• /usr/local/apache/logs
• /usr/local/apache/logs/access_log
• /usr/local/apache/logs/access.log
• /usr/local/apache/audit_log
• /usr/local/apache/error_log
• /usr/local/apache/error.log
• /usr/local/cpanel/logs
• /usr/local/cpanel/logs/access_log
• /usr/local/cpanel/logs/error_log
• /usr/local/cpanel/logs/license_log
• /usr/local/cpanel/logs/login_log
• /usr/local/cpanel/logs/stats_log
• /usr/local/etc/httpd/logs/access_log
• /usr/local/etc/httpd/logs/error_log
• /usr/local/etc/php.ini
• /usr/local/etc/pure-ftpd.conf
• /usr/local/etc/pureftpd.pdb
• /usr/local/lib/php.ini
• /usr/local/php4/httpd.conf
• /usr/local/php4/httpd.conf.php
• /usr/local/php4/lib/php.ini
• /usr/local/php5/httpd.conf
• /usr/local/php5/httpd.conf.php
• /usr/local/php5/lib/php.ini
• /usr/local/php/httpd.conf
• /usr/local/php/httpd.conf.ini
• /usr/local/php/lib/php.ini
• /usr/local/pureftpd/etc/pure-ftpd.conf
• /usr/local/pureftpd/etc/pureftpd.pdn
• /usr/local/pureftpd/sbin/pure-config.pl
• /usr/local/www/logs/httpd_log
• /usr/local/Zend/etc/php.ini
• /usr/sbin/pure-config.pl
• /var/adm/log/xferlog
• /var/apache2/config.inc
• /var/apache/logs/access_log
• /var/apache/logs/error_log
• /var/cpanel/cpanel.config
• /var/lib/mysql/my.cnf
• /var/lib/mysql/mysql/user.MYD
• /var/local/www/conf/php.ini
• /var/log/apache2/access_log
• /var/log/apache2/access.log
• /var/log/apache2/error_log
• /var/log/apache2/error.log
• /var/log/apache/access_log
• /var/log/apache/access.log
• /var/log/apache/error_log
• /var/log/apache/error.log
• /var/log/apache-ssl/access.log
• /var/log/apache-ssl/error.log
• /var/log/auth.log
• /var/log/boot
• /var/htmp
• /var/log/chttp.log
• /var/log/cups/error.log
• /var/log/daemon.log
• /var/log/debug
• /var/log/dmesg
• /var/log/dpkg.log
• /var/log/exim_mainlog
• /var/log/exim/mainlog
• /var/log/exim_paniclog
• /var/log/exim.paniclog
• /var/log/exim_rejectlog
• /var/log/exim/rejectlog
• /var/log/faillog
• /var/log/ftplog
• /var/log/ftp-proxy
• /var/log/ftp-proxy/ftp-proxy.log
• /var/log/httpd/access_log
• /var/log/httpd/access.log
• /var/log/httpd/error_log
• /var/log/httpd/error.log
• /var/log/httpsd/ssl.access_log
• /var/log/httpsd/ssl_log
• /var/log/kern.log
• /var/log/lastlog
• /var/log/lighttpd/access.log
• /var/log/lighttpd/error.log
• /var/log/lighttpd/lighttpd.access.log
• /var/log/lighttpd/lighttpd.error.log
• /var/log/mail.info
• /var/log/mail.log
• /var/log/maillog
• /var/log/mail.warn
• /var/log/message
• /var/log/messages
• /var/log/mysqlderror.log
• /var/log/mysql.log
• /var/log/mysql/mysql-bin.log
• /var/log/mysql/mysql.log
• /var/log/mysql/mysql-slow.log
• /var/log/proftpd
• /var/log/pureftpd.log
• /var/log/pure-ftpd/pure-ftpd.log
• /var/log/secure
• /var/log/vsftpd.log
• /var/log/wtmp
• /var/log/xferlog
• /var/log/yum.log
• /var/mysql.log
• /var/run/utmp
• /var/spool/cron/crontabs/root
• /var/webmin/miniserv.log
• /var/www/log/access_log
• /var/www/log/error_log
• /var/www/logs/access_log
• /var/www/logs/error_log
• /var/www/logs/access.log
• /var/www/logs/error.log
• ~/.atfp_history
• ~/.bash_history
• ~/.bash_logout
• ~/.bash_profile
• ~/.bashrc
• ~/.gtkrc
• ~/.login
• ~/.logout
• ~/.mysql_history
• ~/.nano_history
• ~/.php_history
• ~/.profile
• ~/.ssh/authorized_keys
• ~/.ssh/id_dsa
• ~/.ssh/id_dsa.pub
• ~/.ssh/id_rsa
• ~/.ssh/id_rsa.pub
• ~/.ssh/identity
• ~/.ssh/identity.pub
• ~/.viminfo
• ~/.wm_style
• ~/.Xdefaults
• ~/.xinitrc
• ~/.Xresources
• ~/.xsession
by Vry4n_ | Dec 2, 2019 | Active Gathering
Here you have a list of Windows Interesting files. They can be used to extract sensitive information leading to further exploitation.
It is always important to read the Administrator Guide of any application and appli the best security practices to configiguration file.
Any misconfiguration is a potential vector of attack.
• C:/Users/Administrator/NTUser.dat
• C:/Documents and Settings/Administrator/NTUser.dat
• C:/apache/logs/access.log
• C:/apache/logs/error.log
• C:/apache/php/php.ini
• C:/boot.ini
• C:/inetpub/wwwroot/global.asa
• C:/MySQL/data/hostname.err
• C:/MySQL/data/mysql.err
• C:/MySQL/data/mysql.log
• C:/MySQL/my.cnf
• C:/MySQL/my.ini
• C:/php4/php.ini
• C:/php5/php.ini
• C:/php/php.ini
• C:/Program Files/Apache Group/Apache2/conf/httpd.conf
• C:/Program Files/Apache Group/Apache/conf/httpd.conf
• C:/Program Files/Apache Group/Apache/logs/access.log
• C:/Program Files/Apache Group/Apache/logs/error.log
• C:/Program Files/FileZilla Server/FileZilla Server.xml
• C:/Program Files/MySQL/data/hostname.err
• C:/Program Files/MySQL/data/mysql-bin.log
• C:/Program Files/MySQL/data/mysql.err
• C:/Program Files/MySQL/data/mysql.log
• C:/Program Files/MySQL/my.ini
• C:/Program Files/MySQL/my.cnf
• C:/Program Files/MySQL/MySQL Server 5.0/data/hostname.err
• C:/Program Files/MySQL/MySQL Server 5.0/data/mysql-bin.log
• C:/Program Files/MySQL/MySQL Server 5.0/data/mysql.err
• C:/Program Files/MySQL/MySQL Server 5.0/data/mysql.log
• C:/Program Files/MySQL/MySQL Server 5.0/my.cnf
• C:/Program Files/MySQL/MySQL Server 5.0/my.ini
• C:/Program Files (x86)/Apache Group/Apache2/conf/httpd.conf
• C:/Program Files (x86)/Apache Group/Apache/conf/httpd.conf
• C:/Program Files (x86)/Apache Group/Apache/conf/access.log
• C:/Program Files (x86)/Apache Group/Apache/conf/error.log
• C:/Program Files (x86)/FileZilla Server/FileZilla Server.xml
• C:/Program Files (x86)/xampp/apache/conf/httpd.conf
• C:/WINDOWS/php.ini
• C:/WINDOWS/Repair/SAM
• C:/Windows/repair/system
• C:/Windows/repair/software
• C:/Windows/repair/security
• C:/WINDOWS/System32/drivers/etc/hosts
• C:/Windows/win.ini
• C:/WINNT/php.ini
• C:/WINNT/win.ini
• C:/xampp/apache/bin/php.ini
• C:/xampp/apache/logs/access.log
• C:/xampp/apache/logs/error.log
• C:/Windows/Panther/Unattend/Unattended.xml
• C:/Windows/Panther/Unattended.xml
• C:/Windows/debug/NetSetup.log
• C:/Windows/system32/config/AppEvent.Evt
• C:/Windows/system32/config/SecEvent.Evt
• C:/Windows/system32/config/default.sav
• C:/Windows/system32/config/security.sav
• C:/Windows/system32/config/software.sav
• C:/Windows/system32/config/system.sav
• C:/Windows/system32/config/regback/default
• C:/Windows/system32/config/regback/sam
• C:/Windows/system32/config/regback/security
• C:/Windows/system32/config/regback/system
• C:/Windows/system32/config/regback/software
• C:/Program Files/MySQL/MySQL Server 5.1/my.ini
• C:/Windows/System32/inetsrv/config/schema/ASPNET_schema.xml
• C:/Windows/System32/inetsrv/config/applicationHost.config
• C:/inetpub/logs/LogFiles/W3SVC1/u_ex[YYMMDD].log
by Vry4n_ | Dec 1, 2019 | Active Gathering
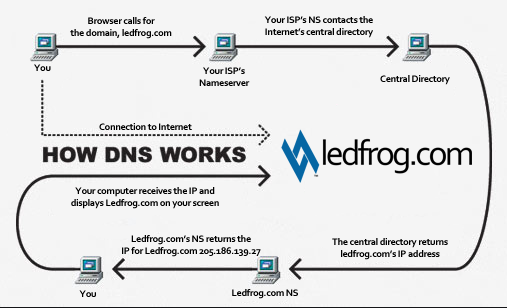
DNS is a naming system for computers that converts human readable domain names e.g. (infosecinstitute.com) into computer readable IP-addresses.
However, some security vulnerabilities exist due to misconfigured DNS name servers that can lead to information disclosure about the domain. This forms an important step of the Information Gathering stage during a Penetration test or Vulnerability assessment.
https://github.com/nixawk/pentest-wiki/blob/master/1.Information-Gathering/How-to-gather-dns-information.md
https://www.varonis.com/blog/what-is-dns/
DNS basics
Let’s say the user opens up the browser and types in infosecinstitute.com. It is now the responsibility of the DNS resolver in the user’s operating system to fetch the IP address. It first checks its local cache to see if it can find a record for the queried domain name. A cache usually contains a mapping of IP-addresses to hostnames which are saved during recent lookups so that the resolver does not have to fetch the IP address again and again. If it can’t find the IP address in its cache it queries the DNS server to see if it has a record for it. A DNS server is usually given to you by the ISP or you can manually set up a DNS server for yourself. If it still can’t find the IP Address then it goes through a process or recursive DNS query in which it queries different name servers to get the IP-address of the domain. As soon as it finds the IP-address it returns the IP-address back to the user and also caches it for its future use.
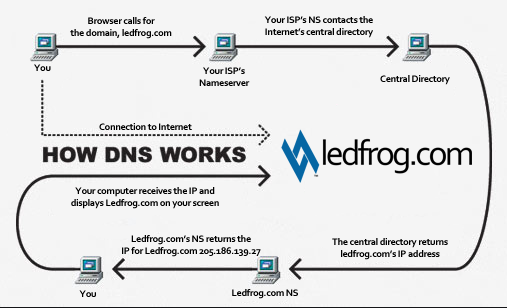
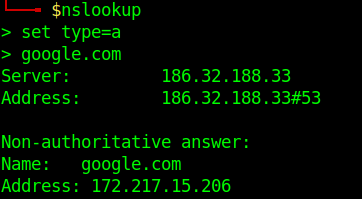
Basic DNS query
- nslookup
- set type=a
- google.com
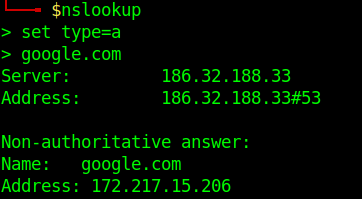
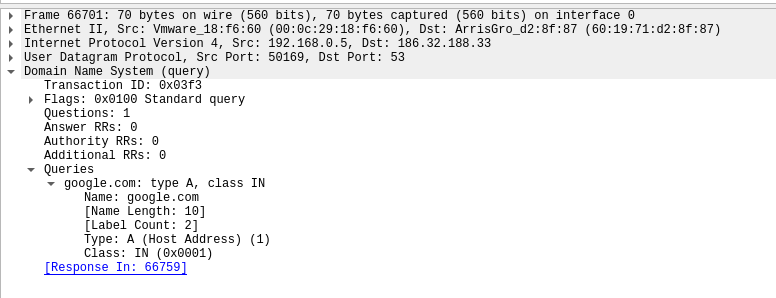
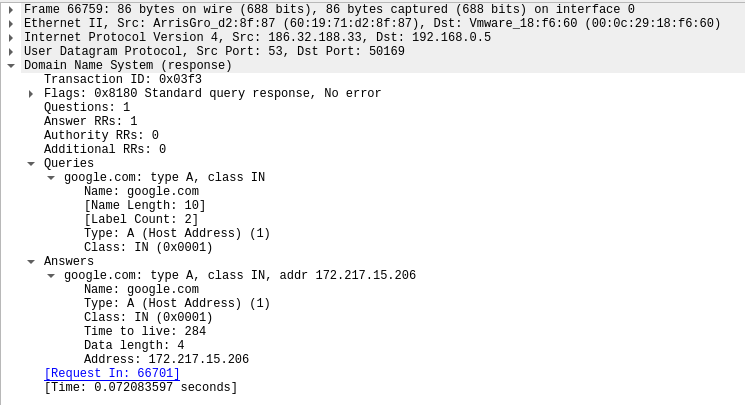
Network view of the request.
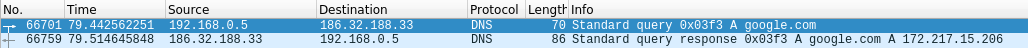
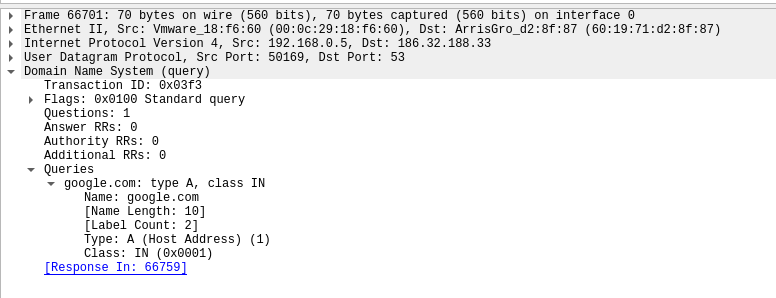
Request:
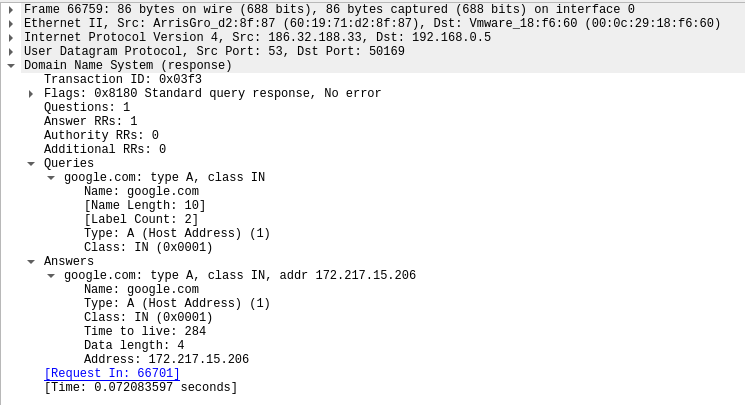
Response:
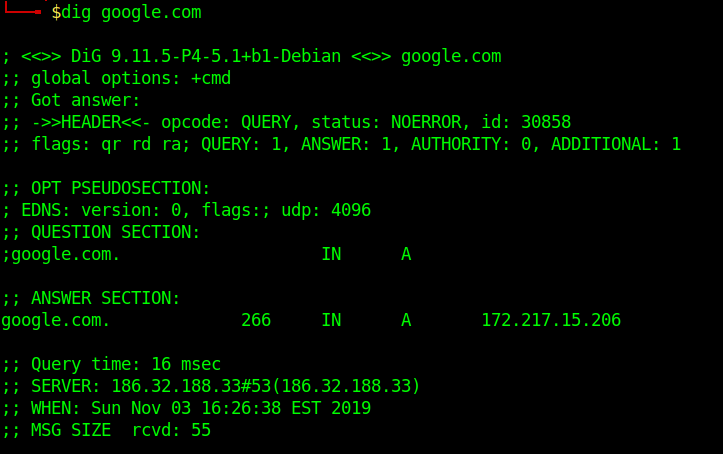
Running queries with dig
To simplify the output, we will be using those extra parameters on the following commands:
+nocmd – Removes the +cmd options output
+noall – Removes extra headers, flags, time information, message size, etc.
+answer – Tells dig to return the answer section (the “juicy” part of the output).
To specify the record we would like to query, we just have to add the record type right after the domain specification. Here is a basic syntax we will use:
- dig +nocmd google.com <record> +noall +answer
DNS Types: 10 Top DNS Record Types
DNS servers create a DNS record to provide important information about a domain or hostname, particularly its current IP address. The most common DNS record types are:
Address Mapping record (A Record)—also known as a DNS host record, stores a hostname and its corresponding IPv4 address.
IP Version 6 Address record (AAAA Record)—stores a hostname and its corresponding IPv6 address.
Canonical Name record (CNAME Record)—can be used to alias a hostname to another hostname. When a DNS client requests a record that contains a CNAME, which points to another hostname, the DNS resolution process is repeated with the new hostname.
Mail exchanger record (MX Record)—specifies an SMTP email server for the domain, used to route outgoing emails to an email server.
Name Server records (NS Record)—specifies that a DNS Zone, such as “example.com” is delegated to a specific Authoritative Name Server, and provides the address of the name server.
Reverse-lookup Pointer records (PTR Record)—allows a DNS resolver to provide an IP address and receive a hostname (reverse DNS lookup).
Certificate record (CERT Record)—stores encryption certificates—PKIX, SPKI, PGP, and so on.
Service Location (SRV Record)—a service location record, like MX but for other communication protocols.
Text Record (TXT Record)—typically carries machine-readable data such as opportunistic encryption, sender policy framework, DKIM, DMARC, etc.
Start of Authority (SOA Record)—this record appears at the beginning of a DNS zone file, and indicates the Authoritative Name Server for the current DNS zone, contact details for the domain administrator, domain serial number, and information on how frequently DNS information for this zone should be refreshed.
DNS Types: 3 DNS Query Types
There are three types of queries in the DNS system:
Recursive Query
In a recursive query, a DNS client provides a hostname, and the DNS Resolver “must” provide an answer—it responds with either a relevant resource record, or an error message if it can’t be found. The resolver starts a recursive query process, starting from the DNS Root Server, until it finds the Authoritative Name Server (for more on Authoritative Name Servers see DNS Server Types below) that holds the IP address and other information for the requested hostname.
Iterative Query
In an iterative query, a DNS client provides a hostname, and the DNS Resolver returns the best answer it can. If the DNS resolver has the relevant DNS records in its cache, it returns them. If not, it refers the DNS client to the Root Server, or another Authoritative Name Server which is nearest to the required DNS zone. The DNS client must then repeat the query directly against the DNS server it was referred to.
Non-Recursive Query
A non-recursive query is a query in which the DNS Resolver already knows the answer. It either immediately returns a DNS record because it already stores it in local cache, or queries a DNS Name Server which is authoritative for the record, meaning it definitely holds the correct IP for that hostname. In both cases, there is no need for additional rounds of queries (like in recursive or iterative queries). Rather, a response is immediately returned to the client.
Zone file
A Zone file is basically a text file present on the server hosting the domain that contains entries for different resource records. Each line is represented by a different record.
Each zone file must start with a Start of Authority (SOA) record containing an authoritative name server for the domain (for e.g. ns1.google.com for google.com) and an email address of someone responsible for the management of the name server.
Domains can be very large, so they are further organized into smaller books, called, “zones.” No single DNS server stores all the books – that would be impractical.
Different types of Resource Records exist within a Zone file. However we are going to discuss some of the important ones
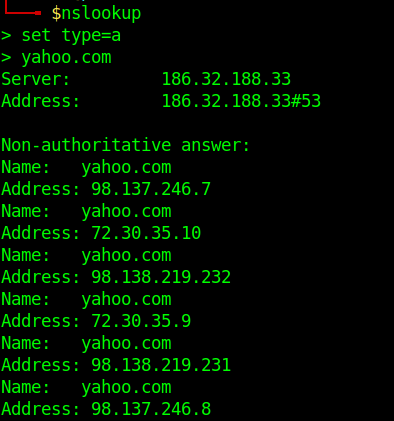
- A Records– Maps an IP Address to a hostname.For e.g. 74.125.236.80 for google.com.
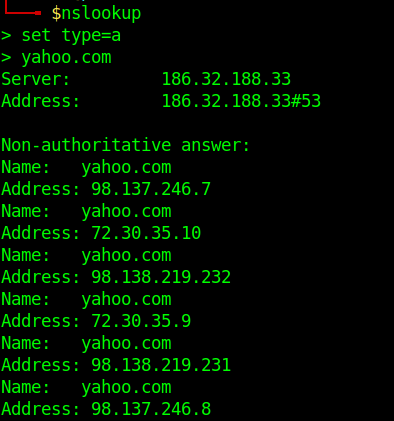
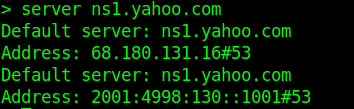
- nslookup
- set type=a
- yahoo.com
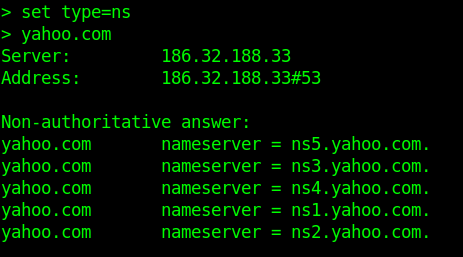
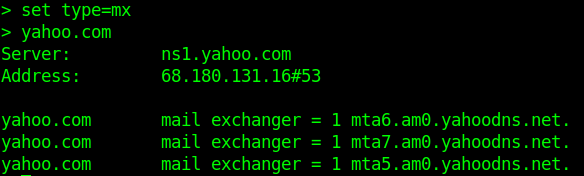
- NS Records-Delegates a given zone to use the given authoritative nameserver. For e.g. ns1.google.com is an authoritative nameserver for google.com
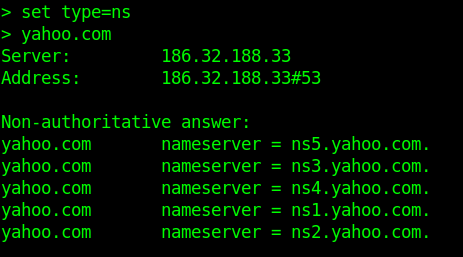
-
- server ns1.yahoo.com (set this as main server)
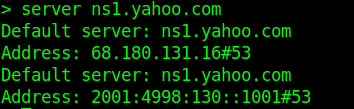
- MX Records-This basically tells us which server is responsible for receiving mails sent to that domain name.
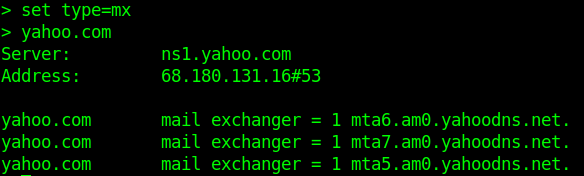
- TXT Records-This consists of arbitrarily human readable text in a record.
- CNAME Records– Gives an alias of one name to another.
Enumeration
Nmap
- nmap –script=broadcast-dns-service-discovery google.com
- nmap -T4 -p 53 –script dns-brute google.com
- nmap -Pn -sU -p 53 –script=dns-recursion google.com
DNSEnum
Multithreaded Perl script to enumerate DNS information of a domain and to discover non-contiguous IP blocks.
OPERATIONS:
- Get the host’s address (A record).
- Get the nameservers (threaded).
- Get the MX record (threaded).
- Perform axfr queries on nameservers and get BIND VERSION (threaded).
- Get extra names and subdomains via google scraping (google query = “allinurl: -www site:domain”).
- Brute force subdomains from a file can also perform recursion on a subdomain that has NS records (all threaded).
- Calculate C class domain network ranges and perform whois queries on them (threaded).
- Perform reverse lookups on netranges ( C class or/and whois netranges) (threaded).
- Write to domain_ips.txt file IP-blocks.
Execution
- dnsenum –noreverse google.com

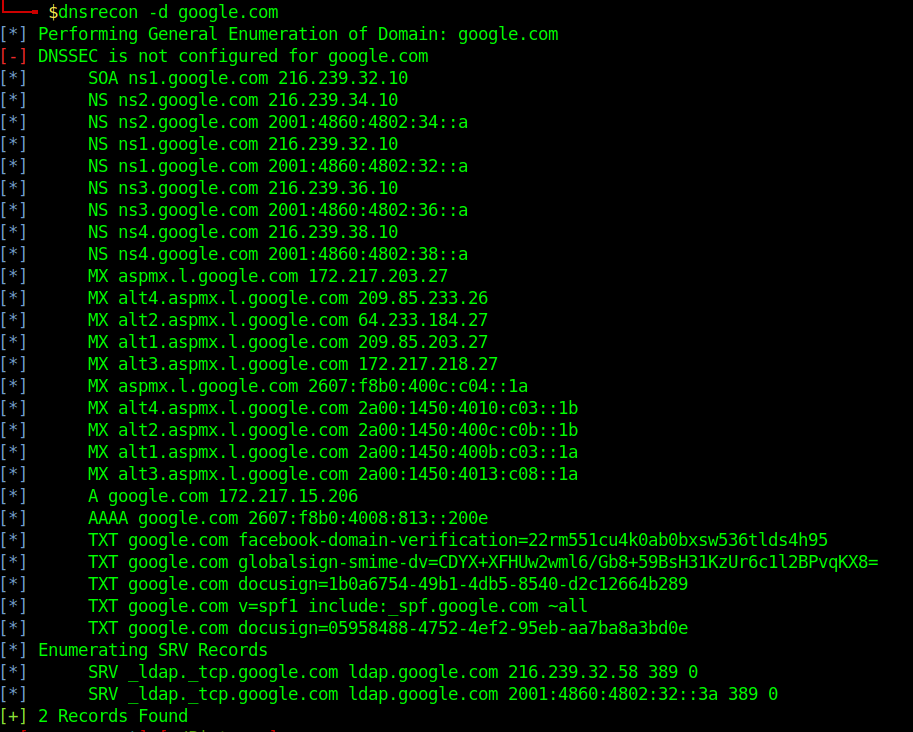
DNSRecon
DNSRecon provides the ability to perform:
- Check all NS Records for Zone Transfers
- Enumerate General DNS Records for a given Domain (MX, SOA, NS, A, AAAA, SPF and TXT)
- Perform common SRV Record Enumeration. Top Level Domain (TLD) Expansion
- Check for Wildcard Resolution
- Brute Force subdomain and host A and AAAA records are given a domain and a wordlist
- Perform a PTR Record lookup for a given IP Range or CIDR
- Check a DNS Server Cached records for A, AAAA and CNAME Records provided a list of host records in a text file to check
- Enumerate Common DNS records in the Local Network Enumerate Hosts and Subdomains using Google
Execution
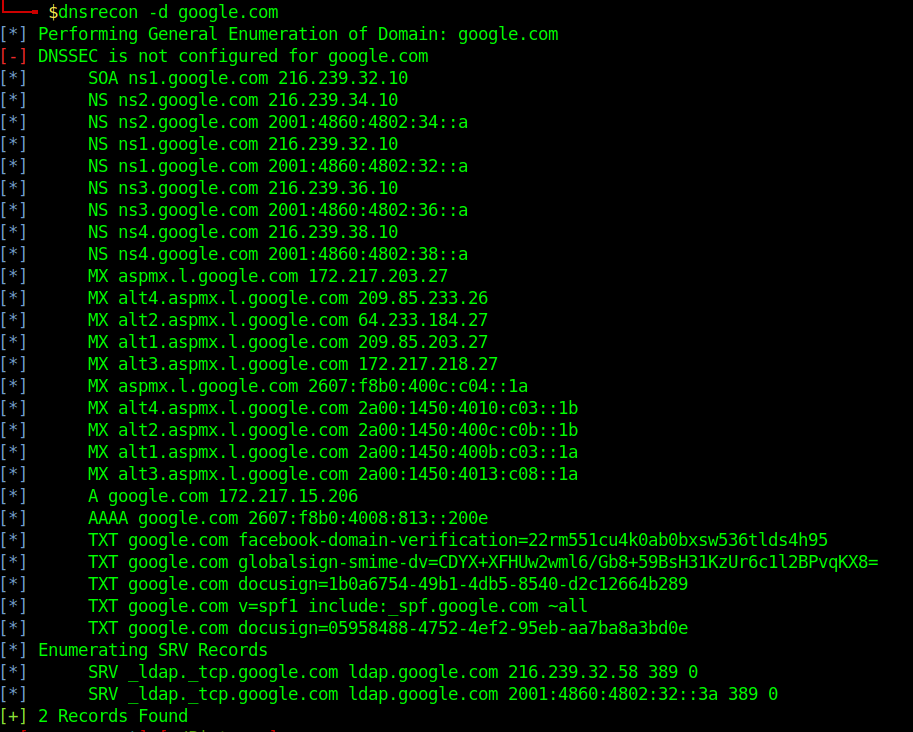
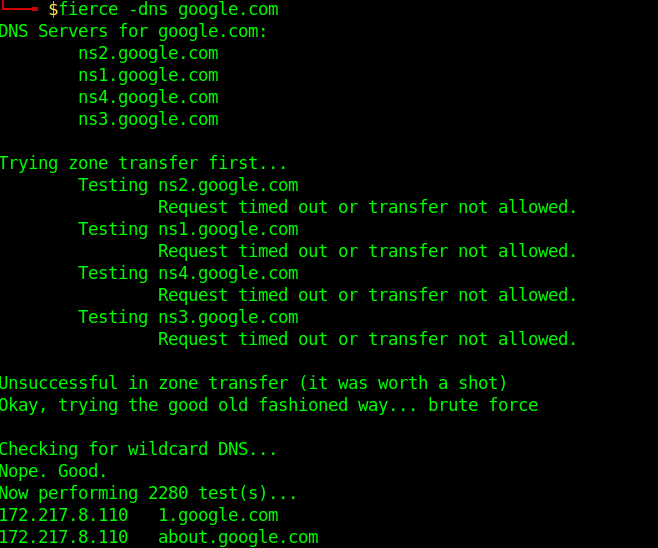
Fierce
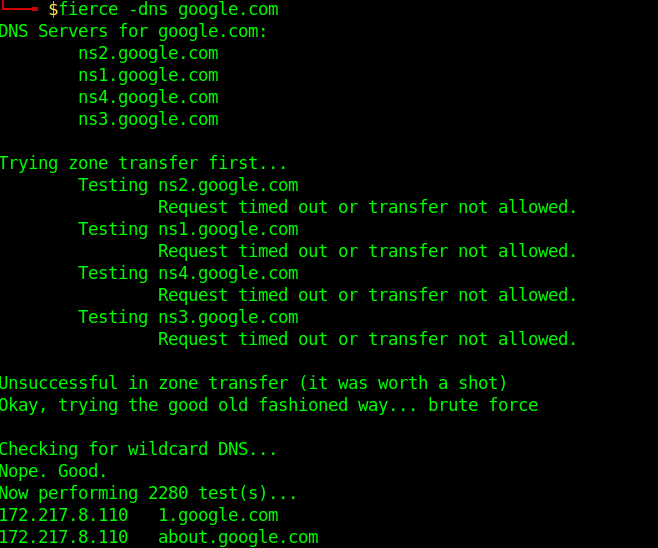
Fierce is a reconnaissance tool. Fierce is a PERL script that quickly scans domains (usually in just a few minutes, assuming no network lag) using several tactics
Execution
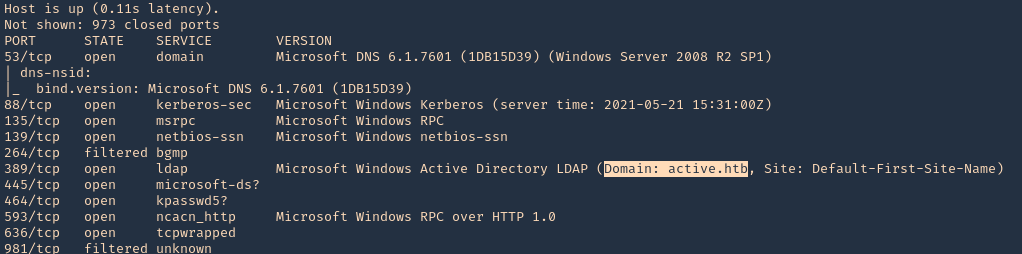
Know the DNS server name
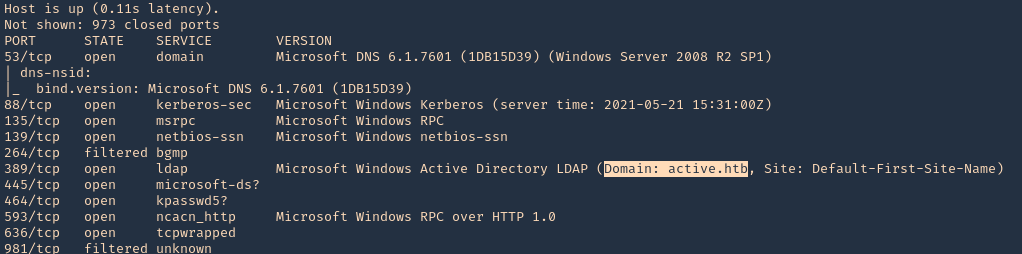
1. Scanning a host with nmap we can sometimes find a domain name, in this case LDAP
- nmap -sV -sC -A -T5 10.10.10.100
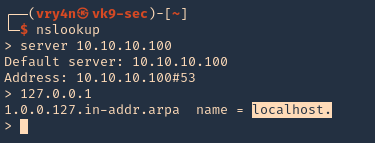
2. This server also has DNS (port 53) service opened. We can consult it
- nslookup
- server 10.10.10.100
- 127.0.0.1
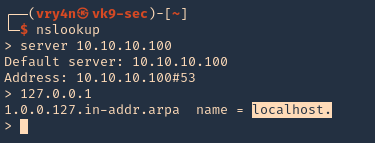
3. We now know this server is localhost, so, the FQDN would be localhost.active.htb